Kirk ransomware comes with a Star Trek-themed decryptor as well as unusually demanding payment in a crypto-currency other than Bitcoin.
Originally spotted by Avast security researcher Jakub Kroustek, the encrypter masquerades as a tool called Low Orbital Ion Cannon (LOIC).
LOIC is often presented as a tool for stress-testing web applications to see how they will cope when swamped with a heavy load of traffic. Of course, although such a tool could be classified as legitimate, it can also be used in DDoS attacks.
Kirk dons the disguise of loic_win32.exe, an executable which creates an AES encryption key that’s responsible for encrypting a victim’s files. A RSA-4096 public encryption key then encrypts the AES key, which is then saved in a file called pwd.
Computer security expert Lawrence Abrams of Bleeping Computer says it’s very important for users without a data backup to hold onto pwd. As he explains in a blog post:
“If you plan on paying the ransom for the Kirk Ransomware, you must not delete the pwd file as it contains an encrypted version of your decryption key. Only the ransomware developer can decrypt this file and if a victim wishes to pay the ransom they will be required to send them this file.”
At that point, it will then display a dialog box with the title “Low Orbital Ion Cannon | When harpoons, air strikes and nukes fail”. The alert suggests that the Low Orbit Ion Cannon tool is initializing on a victim’s machine.

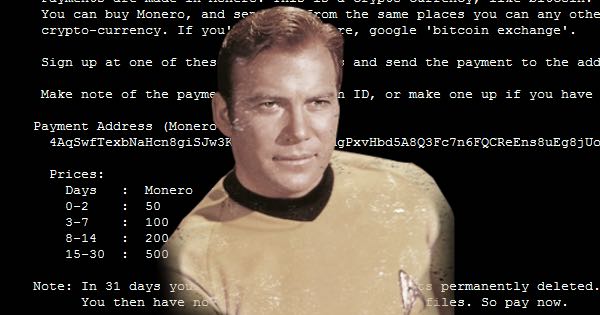
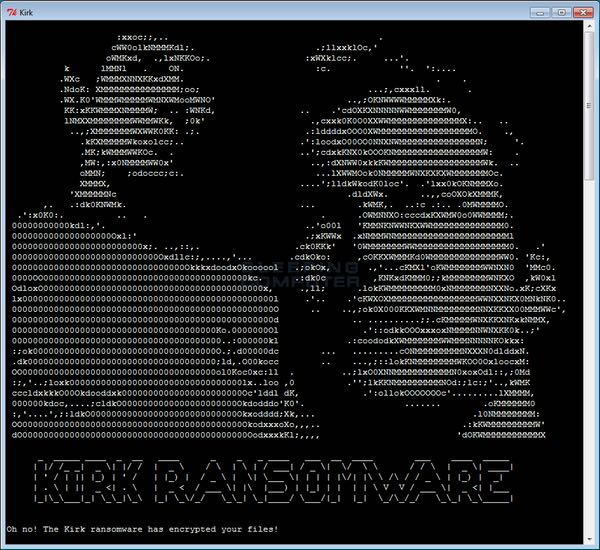
In actuality, Kirk is targeting 625 file types for encryption. For every file it encrypts, it appends the extension .kirked. Completion of its encryption routine causes the ransomware to display its ransom note, containing a neat ASCII art image of Captain Kirk and his faithful science officer Mr Spock.
Here’s where the crypto-malware gets interesting.
Whereas other ransomware demand ransom payments in Bitcoin, Kirk breaks from the pack by demanding 50 units of Monero (approximately $1,100). This crypto-currency has slowly been making its way onto underground forums, so it was only a matter of time before ransomware developers incorporated it into their software.
If the victim fails to pay that ransom within two days, the price goes up. The ransom ultimately maxes out at 500 Monero ($11,000) after two weeks; if the user doesn’t pay within a month, the ransomware authors delete the password decryption key, leaving some with no option to recover their data.
Those who agree to pay the ransom are met by “Spock”, a decryption tool that claims it will unlock all of a victim’s files.

The Star Trek motif is neat. But an overarching theme (which in other samples have ranged from cats to Pokémon Go) is no reason for users to pay the ransom. They should instead invest in a data backup strategy that includes regular testing.
If you do happen to suffer a ransomware infection, however, here’s what you should do.



There is a working removal guide for this type of ransomware already https://malwareless.com/kirk-ransomware-virus-remove/