
Cat-themed ransomware for Android drops a payload that is capable of stealing victims’ SMS messages and encrypting their files.
McAfee Labs recently picked up a variant of the unnamed ransomware, which displayed an adorable picture.
But don’t be fooled by the cuteness.
McAfee mobile malware researcher Fernando Ruiz explains that the ransomware contacts its control server upon installation and requests a series of commands, all of which can ruin an Android user’s day:
“Some interesting features of this ransomware include the ability to encrypt specific files, steal SMS messages while forwarding them to the attacker and avoiding the victim’s message visualization, lock access to the device and the encryption using an AES algorithm with a hardcoded password.”
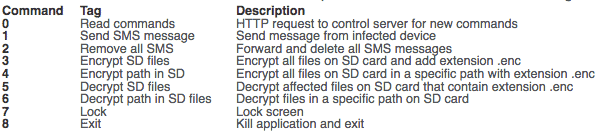
The ransomware also comes with a web-based control panel service with built-in botnet capabilities, including the ability to encrypt the SD card memory files, send SMS messages to the victim, and lock the screen with (you guessed it!) a cat image.
Fortunately, not all is lost for those who might fall victim to this ransomware. Users can decrypt files affected by the cat-themed crypto-malware using the hardcoded password (which unlike asymmetric encryption makes decryption “trivial”) or a method of decryption stored in the application code.
The fact that users can so easily decrypt their files has left Ruiz thinking the variant McAfee Labs came across is still a work-in-progress:
“This ransomware variant looks like a demo version used to commercialize malware kits for cybercriminals because the control server interface is not protected and includes in the code words such as MyDificultPassw. These kinds of threats are usually distributed by attackers who buy exploit kits on darknet markets and who want to attack a specific company or group of people. The attackers often use phishing campaigns, Trojanized apps, social media networks, or other social engineering techniques.”
Ransomware-as-a-service and other malware kits are a growing digital threat, as demonstrated by the recent launch of the Petya/Mischa plaform.
Users can protect themselves against those kits by backing up their data, avoiding suspicious links and email attachments, and keeping their software up-to-date.


