
Two new security threats, a malware-as-a-service (MaaS) platform and a ransomware-as-a-service (RaaS) program, are designed to specifically target machines running Apple macOS.
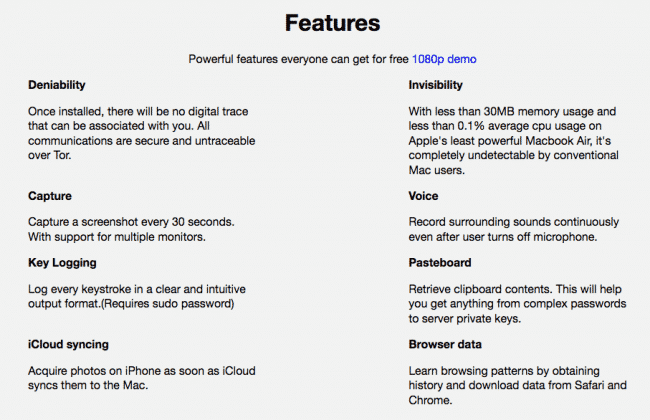
The MaaS platform, known as “MacSpy,” responds to what its authors feel is an ongoing lack of “sophisticated malware for Mac users”. Of course, that perception is not entirely accurate. We’ve seen numerous sophisticated malware strains developed for Macs over the past year or so.
It’s true, however, that MacSpy takes this budding proliferation to the next level by making macOS malware more accessible to users with low levels of technical expertise.
To get started with MacSpy, users sign up by emailing the author their preferred username and password. They then receive an email instructing them to download a ZIP archive using the Tor browser. Unzipping the archive launches the malware-as-a-service program.

When installed on a computer, the malware comes with numerous measures like anti-debugger checks in an attempt to avoid analysis. It also seeks to obtain persistence before executing. AlienVault researcher Peter Ewane explains what happens next:
“Upon execution, successfully passing the anti-analysis checks and setting persistence, the malware then copies itself and associated files from the original point of execution to ~/Library/.DS_Stores/ and deletes the original files in an attempt to stay hidden from the user. The malware then checks the functionality of its tor proxy by utilizing the curl command to contact the command and control server. After connecting to the CnC, the malware sends the data it had collected earlier, such as system information, by sending POST requests through the TOR proxy. This process repeats again for the various data the malware has collected. After exfiltration of the data, the malware deletes the temporary files containing the data it sent.”
The exfiltrated data, including screenshots, keystrokes, photos synced with iCloud, recorded audio files, retrieved clipboard content, and browser information, appears in directories that are accessible from the malware’s user web portal.
The “basic” MacSpy offering is free. But for an unspecified number of Bitcoins, users can gain even more functionality. These “advanced” features include the ability to access emails and social media accounts, retrieve any files/data, and encrypt the user directory within “in a few seconds.”

Its encryption capabilities aside, MacSpy is a quintessential spyware program.
Online criminals looking for a true ransomware package need to look elsewhere.
As it turns out, they don’t need to look too far; it appears the same authors are behind a ransomware-as-a-service platform known as MacRansom.


Like MacSpy, MacRansom also runs anti-debugging checks and tries to obtain persistence on the machine. It then encrypts the victim’s files using a TargetFileKey. According to Fortinet’s researchers, this encryption resource is fairly unique:
“A remarkable thing we observed when reverse-engineering the encryption/decryption algorithm is that the TargetFileKey is permuted with a random generated number. In other words, the encrypted files can no longer be decrypted once the malware has terminated – the TargetFileKey will be freed from program’s memory and hence it becomes more challenging to create a decryptor or recovery tool to restore the encrypted files. Moreover, it doesn’t have any function to communicate with any C&C server for the TargetFileKey meaning there is no readily available copy of the key to decrypt the files. However, it is still technically possible to recover the TargetFileKey. One of the known techniques is to use a brute-force attack. It should not take very long for a modern CPU to brute-force an 8-byte long key when the same key is used to encrypt known files with predictable file’s contents.”
Once the encryption routine has completed, this ransomware demands 0.25 Bitcoins (approximately US $700) from its victims. Its ransom message instructs users to send payment to a ProtonMail address.
It’s unclear how MacSpy and MacRansom are making their way onto unsuspecting users’ computers, but we can assume it’s through the usual distribution vectors of exploit kits and malspam campaigns. Under that assumption, users can protect themselves by exercising caution around suspicious links and attachments and by regularly updating their systems.
They should also back up their data on a regular basis.
Should they suffer an infection at the hands of MacRansom or another ransomware for OS X, users can follow these recovery tips.
For more discussion of this topic be sure to listen to this recent episode of the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
They are holding the Secure Tour, and you can go and visit them in Manchester on the 6th of July at the Old Trafford football stadium, Manchester United's own stadium.
Secure Tour is where they get loads of experts like Paul Ducklin or Mustafa Al-Bassam, who used to be in the LulzSec hacking gang, as well as technology companies all speaking about their technology and cybercrime.
And if you're an IT security professional, you can register and attend.
Go to foursys.co.uk. That's foursys, F-O-U-R-S-Y-S, .co.uk, and get yourself a ticket for the Manchester Secure Tour.
Smashing Security, Episode 29: Exploits to Get Your English Teeth Into, with Carole Theriault and Graham Cluley. Hello, hello, and welcome to Episode 29 of Smashing Security.
My name is Graham Cluley, and I'm joined as ever by my co-host, Carole Theriault. Hi, Carole.
Don't put a number on them." And then it all got really confusing, because people ask us, "How many episodes have you done?" It's like, "Well, this is the 29th episode, but it's number 25." It's got too complicated.
So I think what we need to do is now jump straight from episode 25 to episode 29, which is this one.
And then the second season, they start at 200 and they do 12 shows.
He is the 3-time World Embassy snooker champion. He is security advocate at AlienVault. It is Javvad Malik. Hey, Javvad, welcome to the show.
What we're going to do is each of us is going to choose a story from the last week from the wonderful world of computer security, and we are going to explain why it piqued our interest and why we think we should have a little chat about it as well.
On the second Tuesday of every month, Microsoft releases to us, the great unwashed, its security patches, which is wonderful.
And we like them for doing that because it helps us protect against all the bad out there, but something rather unusual has happened this time.
Very unusually, Microsoft has issued patches for operating systems which it no longer supports.
The operating systems for which it said, "We will never, never ever release another patch for something like Windows XP and Vista again." So why are they doing this?
Well, they are warning of destructive cyberattacks, rather like those we saw involving another Microsoft exploit WannaCry a month or so ago.
So they've released a whole bunch of updates.
They've done their regular updates as well, of course, but they've now released security updates for XP, Vista, Server 2003 containing fixes for 3 NSA-developed exploits.
Hasn't been able to keep its exploits hoarded away quite as well as they should have done.
And unfortunately, because they've had these things and they've fallen into the bad guy's hands, in this case, the Shadow Brokers hacking gang, potentially they could be exploited by other online criminals or indeed nation states.
And that seems to be what Microsoft is worried about because Eric Doerr, I'm not sure, he's the general manager of Microsoft Security Response Center.
He has said, that the reason they've done this is to fix vulnerabilities that are at risk of exploitation by nation-state actors.
In short, they are worried of another WannaCry-style attack.
I mean, and I think many companies have switched away, but there are inevitably organizations which still have older computers running older operating systems, which maybe have been overlooked or for whatever reason haven't been patched, haven't been kept up to date.
We're going to keep on doing it.
Or it may be that that computer is powering a piece of medical equipment, for instance, which may have cost millions, and they simply cannot afford to upgrade the computer because they've only got drivers to drive that medical equipment which run on those older operating systems.
Yeah, so I think it's a good thing that they've done this. It's just how are they going to decide going forward whether they should release patches for these legacy systems or not?
And if they don't and it happens to get hit, are they going to get some negative press about that?
I've seen people saying they shouldn't have released these patches for these older versions of these operating systems because basically they sort of— These are people who believe in survival of the fittest.
It's they have to get rid of these older operating systems, let them die, let the malware infect them. That's what some people believe. Javvad, what do you think?
It's a bit rehab, isn't it?
Someone's trying to come off whatever substance they're addicted to, and you keep feeding them something when things get really bad, you're not really helping them necessarily.
So maybe the question is, do we need a different style or model of how software is licensed and spread and maintained?
Because they can act as a hub.
And I think Microsoft as a whole would really the whole of the internet to be safer because anything risky which is going on does damage to them and makes people want to switch away from their operating systems to something else.
It's not as simple as doing your regular Windows update. And interestingly, what's come out of this are the code names which the NSA gave these exploits.
So we have three exploits which Microsoft is patching against this week. There is Steam Audit, which exploits vulnerabilities in Windows Remote Desktop Protocol.
There is Exploding Can, which exploits flaws in IIS 6.0. And there is Englishman Dentist, which exploits a flaw in Exchange Servers.
Now, what we have is some intelligence agent, some hacker dude working for the NSA, right? Working on these exploits and he's thinking, oh, what am I gonna call this one?
And his mind wanders and maybe he thinks of the Austin Powers movie and the general state of British dentistry.
And he calls it — now, I thought we were supposed to have a special relationship with the Americans. How can they go around criticising our teeth like this?
I mean, the malware doesn't always, and the vulnerabilities don't, but these exploits which are written by agencies do seem to have these funky code names.
And I have to say, sometimes I am a little bit impressed with them.
I don't know if they have a random word generator, you know, it's, oh, look, it's the Lumpy Trousers exploit, which we're going to release this week.
But it's, you know, I think it has a certain charm about it, doesn't it?
You may also want some layered protection to reduce the chances of you being exposed to some of the vulnerabilities here as well.
So you have to apply your normal patches just like you would any other Patch Tuesday, but you don't have to worry about these particular ones.
These particular ones seem to target particularly old operating systems.
Now why that is, whether someone is planning to launch an attack against older operating systems and why Microsoft's been driven to this, we don't know exactly what has driven them to do this.
Yeah, it's probably one of the first instances of malware as a service that we've seen on the macOS, and it just came to light about a month ago.
You just go online and you say, "Hey, Mr. Bad Guy, here's my credit card details," or, "Here are some bitcoins.
Can you launch the attack against here and give me an interface which I can then collect the data from?" So it's a very commoditized offering that allows non-technical criminals to—
I mean, Macs are all marketed on the premise that they're secure and they don't get viruses or malware. And it's really, I think it's just like they follow the money.
Wherever there's more proliferation of any operating system, you'll see more attacks being developed against it.
And we see Macs growing in popularity at home, but more than that in the enterprise now.
Or just a laptop.
And so they do become a target. I mean, it's never been the case that there hasn't been malware for Mac.
There's been a lot less malware for Mac, but this is really a sign that malware for Mac is growing up.
If I wanted to infect your Mac, presuming you had a Mac, I could go there, I could give them so many bitcoin and woof, off they go.
The fact that people that don't know how to do it can actually just go and ask someone to do it for them that has no basis in anything other than, "I've paid you money.
I want you to do this attack." That's a gun for hire, effectively.
But you know, they have a whole bunch of features and things that they list out, which, you know, you start going through and it's really quite impressive.
And then you think about the potential victims there. It's not just big enterprises, but you could see celebrities and PR agents and all those kind of things.
They're still reeling from their previous, you know, iPhotos sort of breaches. And this facilitates a lot of that kind of stuff as well.
So they're doing a ransomware version of this called MacRansom. So, you know, it looks pretty organized to me. And I think the message to Mac users is you can't be complacent.
There are far fewer threats for Mac, but it doesn't mean they don't exist at all. And malware for Mac I would argue, Carole, is growing up.
How are banks and other websites gonna stop people who have all the correct information from actually accessing the information you wanna protect from them?
We have this cool paper from this research team, Morano, Gambarini, and Sartoni. They published this last month, and it's a novel approach to detecting fake identities.
So the idea is this: so while truth tellers respond in one way to unexpected questions— and I'll get to what unexpected questions are in a second— liars have to build and verify their responses.
So they take actually longer to answer, and they take a more roundabout way, literally a roundabout way in selecting the correct answer.
So in this study that they've done, they had yes or no answers. And the expected questions were things like, were you born in 1991?
And Graham, you would certainly, if you're being honest, say no, right?
You would figure out all kinds of questions, including the star sign.
Actually, that was one of the things we were often asked, and that's the thing that would make me not get access because I wouldn't have researched that bit, which is why I asked you earlier, Javvad, did you know your zodiac sign?
Because that was one of the unexpected questions that they used in this as well. So one of them is, are you 21 years old? Right?
So rather than asking what year you're born in, it's asking what age you are right now.
Now, that's not something that you can't work out if you're faking an identity, but it takes you a bit longer, doesn't it?
Because I know right away what my age is, as opposed to if I was trying to pretend to be you, Graham, 55 or 56.
Because if you were faking it and you were maybe not from the same country, that may not be quickly available to you.
So it seems they find it difficult, liars find it difficult to respond to these unexpected questions quickly and without errors.
And what happens is it changes, this is the cool bit for me, it changes their mouse dynamics.
So if you imagine your mouse is hovering at place X on the screen and you draw a direct line to the answer you need, which let's assume is yes in this instance.
If you draw a straight line to that, you'll see that people who are truthfully answers will be very close to that straight line.
There'll be a little bit of an arc, but those that are lying, they have a lot bigger arc around.
It's almost it looks like a bow and arrow, like the bow, you know, with the— So, and apparently that it's 90% accurate that fraudsters will kind of be a lot looser in their direction and a lot slower in getting there.
Because he's a bit spooky if you haven't seen Derren Brown.
But he'll just look at you, ask you a question, and he knows if you're lying or he knows if you're thinking of a particular number.
And similarly, this tracking of the mouse might give clues to critical websites as to whether someone is who they claim. That's very interesting.
And I mean, we all know that polygraphs aren't considered scientific by most of the community anymore.
I mean, I don't think they're used anywhere privately, anywhere in the States, for instance. Oh, I think they still use it in governments, which is weird.
And I guess most of the security industry, really, most of the security technology kind of works a lot in that way. Look for patterns. So anyway, it's very interesting.
And it could open the door to new research.
They map your user journey as you enter the website, which URLs you tend to navigate through, the dwell time and all that kind of stuff to pick out whether you're a human or a script or that kind of thing.
So I don't think, you know, mouse is that much of an issue. I tell you what I think. I think that the biggest issue we have is websites are just too polite.
They're there to help facilitate and say, hey, welcome back, Graham. We think it's you. Please tell us it's you and buy some stuff.
I think they should just switch it around, be rude and have, you know, the American TSA kind of approach. What are you doing here? What do you want? We don't like the looks of you.
Turn around.
That's how he likes to be treated. Don't give him a usual login prompt. That'd be marvelous.
And thanks for sponsoring the show.
Carole, are you gonna do it or not?
And I'm going to go first because have you heard — do you remember the Atari video game console?
Specifically, they have developed an AI, an artificial intelligence, which can play Ms.
Pac-Man perfectly, and it has now scored a perfect score of 990,990, more than any human has ever achieved.
They clearly had a lot of time on their hands. But, you know, I think this is quite serious. We have to be careful about AI, don't we?
Because you remember, this is how Skynet started. I'm sure Terminator. It all started with Ms. Pac-Man. And before you know it, there were rising robots.
We'll put it in the show notes as to what Microsoft has been spending all that money we give them in Office 365 subscriptions is obviously being spent sensibly.
And they've written a program which can play Ms. Pac-Man really well. Fantastic. It's kind of cool, kind of crazy as well. And I imagine it has some use.
But anyway, he was a developer, and he felt that his life was too entrenched in routine and a steady pattern, so he made an app that eventually he expanded on it.
He started off with it just to do Uber, but basically it randomized his life. So he would, you know, click on the app and set a budget.
An Uber would pick him up and he'd have no idea where it would take him.
He would travel there, turn up with a bottle of bubbly and say, "Hey, I saw the invite online. I'm just here." And what's his—
So, you know, he ended up going around the world. He spent time at weird sort of festivals in random parts of the world that happens. He ended up there.
So he went around the world, he met people and strangers and all that kind of stuff. So I think it's good in a way that you kind of step outside of your own bubble.
So is he going to create an app and make this available to anyone who wants to just throw their wife into the dryer and see what happens?
And it sounds like he sort of reenacted that for the app generation. Can I ask a technical question about this fellow? Does he have a girlfriend?
You know, I have actually thrown my wireless mouse in the drawer about a year ago because I just got so annoyed with the frickin' battery usage and it going out of battery, not having batteries, and la la la la.
It's like you want the wire. The wire is a bonus. I would pay extra for a wire. Same with a mouse. I've got a cluttered desk. I need to find my mouse. You don't have to pay extra.
I will yank the wire.
So there are two Logitech mice for which this will be compatible, the G903 and the G703 for those who are interested. And there's the charging mat called the PowerPlay bundle.
So bundle is separate from the mice. So the mice are $100, $150. The power, the bundle, the mouse mat, the wireless charging base, which yes, you'd probably have to plug in.
Two mouse surfaces are in there, soft and hard. So you have a choice.
I was all excited by the idea that it's using cool, you know, magnetic resonance transmitters to, you know, because that's really hard to do.
You know how normally this whole wireless stuff works. You have to be right on top of each other. The transmitter and the receiver got to be very close for it to work.
But this is working across a whole mouse pad. So I don't know how they're doing it.
Ars Technica's Sebastian Anthony thinks there must be lots of antennas around built into the charging mouse pad. But I don't know.
Apparently it means more people get to learn about our podcast.
Go and check it out and you can contact us there and find our links to Twitter and all the other things. So until next time, thank you very much, Javvad Malik.
We appreciate you coming along.
And until next time, bye-bye! Bye! Ah, that was quite something, wasn't it?



