
Ransomware ran amok in 2016.
Prominent crypto-malware strains like Jigsaw, Chimera, and Petya/Mischa had a field day encrypting unsuspecting users’ data (and made a lot of money in the process, too).
Given ransomware’s success, it’s no surprise some developers of non-encrypting malware modified their software to begin asking victims for a ransom. The creators of KillDisk did it, and no doubt other criminals will follow suit.
To a certain extent, end-users wised up to (or at least became aware of) the ransomware threat in 2016, though for whatever reason, many chose not to create a data backup strategy. Maybe the task seemed too daunting. Maybe they just didn’t have the time.
But 2016 is gone. The new year is the perfect time to get out of bad habits, and take that crucial step towards protecting your data. Here’s how you can create a robust data backup plan and make sure it works.
Developing a Data Backup Strategy
Once you’ve decided you’re going to take the plunge and back up your data, you’ll need to flesh out the what and how components of your backup strategy.
The what component refers to what devices you want to back up. Do you want to just focus on backing up your laptop, or do you have additional computers and maybe even a few mobile devices whose data you’d like to protect, as well?
Additionally, perhaps you don’t want to back up all of your saved data but instead only files contained in a certain folder or user profile. All of those factors shape the how component of your data backup strategy, that is, how you want to back up your data.
For instance, if you simply want to back up the files located in a folder, you can probably get away with copying that folder to both a USB drive and Dropbox and updating the files contained therein on a regular basis. By contrast, if you want to back up your hard drive, you might need to invest in hardware and software that come with adequate data storage capacity.
But here’s the thing: no matter how much data you want to back up, it doesn’t change the fact that you should maintain multiple copies of your information on different media.
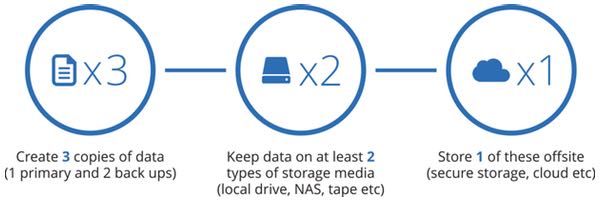
That’s the quintessence of a 3-2-1 backup strategy, where you keep at least three copies of your data on at least two different storage types with at least one copy located offsite.
Multiple copies in theory means at least one copy will work if the others fail. The same goes for the two different storage types; if you can’t use one, hopefully you can use the other. Finally, if you lose or someone steals a local copy of your data, you can always restore your data using the offsite copy.
For a basic 3-2-1 backup strategy of your laptop, I recommend that you purchase both an external hard drive and a subscription to an online backup service.
You should use the former to back up your critical data regularly but at least once a week.
 When you back up with the external hard drive, don’t do anything else with your computer. In fact, it might even be a good idea to temporarily disconnect from the internet so as to prevent web-based threats from pinpointing and infecting the external hard drive.
When you back up with the external hard drive, don’t do anything else with your computer. In fact, it might even be a good idea to temporarily disconnect from the internet so as to prevent web-based threats from pinpointing and infecting the external hard drive.
Once the device has finished backing up your data, make sure you store it in a secure location where no one else can find it. A locked drawer makes for a great storage place. If you really want to go all out, lock the external hard drive in a safe that’s fire- and water-resistant.
Of course, backing up with an external hard drive takes a lot of planning. That’s why it’s important you also have a solution that doesn’t take a lot of thought.
 An online real-time cloud backup service fulfills that need. All you need to do is install the software on your computer, log into your account, and let the program back up your files to the service’s cloud-based data center automatically.
An online real-time cloud backup service fulfills that need. All you need to do is install the software on your computer, log into your account, and let the program back up your files to the service’s cloud-based data center automatically.
Now don’t get me wrong. There’s some risk in backing up via the cloud, as a data breach at that company could potentially expose your personal information.
But that doesn’t mean you should run away from the cloud. Just make sure you do your homework and go with a reputable company that takes adequate steps to protect its customers’ information – such as encrypting your backups so the only person who can access the data is you.
Testing Your Data Backups
Congratulations! You’ve set up your backup strategy. But your work doesn’t end there. You don’t want to suffer a ransomware infection only to find out that none of your backups work. To protect against such a scenario, it’s important that you test your data backups regularly.
Here’s what I recommend:
1. On a quarterly basis, create a temporary folder on your computer. Then go to your data backup solution’s software and select a few files that have recently been updated for restoration. Save those files in the temporary folder and look them over.
Do their contents match those of the original copies? If not, try deleting the backup, backing up your computer again, and implementing the same test. Is there any improvement? If not, the backup software might be malfunctioning, in which case you might need to fix your external hard drive or call customer support for your online backup solution.
2. Once you’ve restored a few files and verified their contents, try backing up an entire folder that comes with sub-folders. Successful restoration should preserve that folder’s entire folder directory, including all sub-folders and individual files. Check to make sure that’s the case.
3. On a bi-annual basis, completely restore all your data. Depending on space constraints, you might want to do this on another computer or on a virtual machine. Once the restoration is complete, review your critical files and folders. You should also look at the storage space and make sure it matches with the size of your data saved on your device.
Conclusion
There’s no need to go into 2017 with your data unprotected. By following the tips provided in this article, you’ll make sure a ransomware infection doesn’t get the better of you and your information. Sure, backing up your computer requires a little bit of thought, but it’ll save you a lot of time and effort in the long run if something happens where you lose access to your data.
Have I missed anything in this article? Do you adhere to certain data backup practices about which you’d like others to know? If so, please let me know in the comments!
To learn more about backups, make sure that you listen to this episode of the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Recorded Future arms threat analysts, security operators, and incident responders to rapidly connect the dots and reveal unknown threats.
Their patented technology automatically collects and analyzes threat intelligence from technical, open, and dark web sources.
Sign up to their Cyber Daily newsletter and get the latest insights from Recorded Future at recordedfuture.com/intel.
Smashing Security for the 21st of September, 2017. I'm here, my name's Graham Cluley, and I'm joined by my good chum and co-host, Carole Theriault. Hello, Carole.
We're not gonna look at enterprise backups as such, but it's more sort of how you're gonna deal with your personal computer and devices and keeping those backed up.
And my question for you, and by that I mean you two, have you got a backup?
I do it because I just think it's a jolly good idea to have a backup and to make sure that that backup is secure as well.
And that if I need it, I can get back up and running as quickly as possible.
So I think the first thing is backups are great, but in many cases people haven't done a backup recently enough.
So you'll come across someone who's maybe accidentally overwritten some of their data or they've had a hard disk failure or maybe they've been hit by something like ransomware and you say to them, have you got a backup?
And they go, well, I did one last October or something like that. And that's a backup which is older than six months or something.
Because if you're relying on yourself or somebody else to manually do the backup, it ain't going to happen. You're sitting in front of a computer device, right?
Which is really good at remembering to do things and doing things on a schedule. Okay, the computers screw up things all the time.
But if it's a boring, mundane task, which frankly doing a backup is a boring, mundane task, if it's something which will be easy to forget, then get your computer to do it on a schedule instead.
Because when you haven't got any previous backup, if you're backing up your entire hard drive or all the files in your user folder or something like that, then that may take a while to put onto a device or upload to the cloud or wherever it is.
And we'll get into the different places maybe you should back up.
Once you've done that, then you begin to get into incremental backups where the backup may only be a backup of what has changed since the last full backup instead.
So I used to be a computer programmer. I remember way, way back, you know, 25 years or whatever, when I was programming on a computer which didn't even have a hard drive.
I was saving my source code onto floppy disks.
So I would have piles and piles of floppy disks, and I'd be so paranoid I was going to lose my work that I'd save it on this floppy disk, but then I'd have another floppy disk, which was a different color or labeled with something else.
And I'd have all these different versions and archives of past versions of my source code.
But that was kind of what it was like because I had nowhere else to put these things. You didn't have USB drives. You didn't have anything else. So you had to use this kind of medium.
But I knew that a floppy disk on its own wasn't reliable, and so I'd have multiple floppy disks.
And that's one of the first things which I think you need to recognize is that there is this danger that you will have an accident.
You will accidentally maybe make a mistake, or you will delete a file, or you will change some code, and you want to move back in time.
And so this is my sort of second rule is that if you've got a backup, if the only backup you have is inside your house or another drive which is on your desk, that's not really a backup.
I mean, yes, it might recover, it might save you from those sort of accidental deletion of data or something like that.
So I can understand things like photos, email, you know, some files, but just sounds like you won't have to back up your entire system. Is that necessary?
Applications you can reinstall from the original media or you can download those from the net if you need to. It's the files which actually belong to you, which you created.
So it'd be the photographs. Yeah, it will be— you said the emails actually, but a lot of people will be using a web-based email system.
You may want to back up your contacts details, your calendar perhaps. You may have databases, you may have Word documents.
I think maybe for the typical home user though, the most critical thing which you want to back up are probably things which are completely irreplaceable, which would be things like, for instance, legal documents, things like—
The number of times when people will be going to data recovery firms saying, "Look, I've had a hard drive crash or something's gone wrong and I can no longer get the photos of my kid." Do you know what?
One of the things they took was my laptop with all our pictures on it. You know, we had just got married, da da da.
Just by absolute chance, the week before, my other half had backed up all the pictures.
I just cared about having those.
So I'm responsible not just for the files on my computer, but my mother's computer.
And I'm also the person that saves all the photos and the videos that we've had transferred and taken from film and upgraded onto digital.
And last year when my father passed away, it became another additional thing of oh my gosh, if we lose all this stuff, that's what's left of our memories of my dad that are, you know, in photos and video.
So I have to make sure that this stuff is backed up really, really well. Otherwise, you know, I'm responsible if something goes wrong.
Been my mission to figure out a better solution. And admittedly, I don't have a great one. So this is why this episode's really interesting.
It's a good idea, but I would argue that it's not a real backup because it is still at risk.
Although it probably will avoid the accidental deletion or something like that, there are still other risks involved. One of those will be fire or flood.
The other risk, however, is ransomware.
Its whole raison d'être is to attack your most precious files, to lock them up, to make them inaccessible to you.
And if you have an accessible drive, a backup drive accessible from your computer, which is infected with ransomware, that ransomware will seek it out and it will encrypt your backup as well.
For this reason, I think you begin to start thinking, well, for these really important files, we need an offsite backup. We should put our backups at a different physical location.
And some people say, oh yeah, that's great.
What I'll do is every week I will take my USB drive, I'll take it to the office or something like that, or I will take it to Auntie Jean's and I'll put it somewhere safe over there because even if I suffer a data disaster, it won't be affecting her house as well.
Which sounds like a great idea in principle. I know many people do that. However, I think that is just going to go wrong as well.
You were always in a rush because you got so many things to do in your life and it just falls by the wayside. You need offsite backups which are automated. That's my belief.
Anyway, some Eastern European kids from 1969 who were juggling tables on their feet.
So backing up onto another local device is a good idea. And in my personal scenario, what I do is my computers wake up at 2 or 3 o'clock in the morning.
Any file which has changed gets backed up onto the storage device.
So then you have to figure out when is a good time for you to schedule this. And it has to be time when you yourself are also active.
I'm sure there are programs out there which will detect, oh, you're not doing anything between these hours, therefore I'm going to slowly start backing up to the drive.
But that means I've always got something. In fact, the particular system which I use, it basically clones the drive so that I've got a bootable drive.
Because for me, the thing about backups is not just getting your data back, it's about getting up and running again as soon as possible because it's going to affect my business.
And just doing a very quick update of whatever has changed. Why not do it?
And what's your plan B if, you know, there's a fire or you have a cyberattack or whatever?
You could do it onto a USB stick if you really wanted to, and then you could take it with you.
You also want to consider things like encryption, obviously, and your hard drive should be encrypted, yadda yadda. That's a whole different debate.
If you do do a cloud service, especially if you're using a third party or you want to back up, you want, and you want to protect that data, encryption is the layer you need, right?
There are some cloud services which obviously are making a living, have made a business out of working out what information they can learn about you and the potential for them to sell marketing data and so forth and do things like that.
Some cloud services don't, aren't interested in that, but some are interested in that.
So my general rule is that if I'm putting anything sensitive into the cloud, it's going to be encrypted before it gets transmitted to the cloud.
I'm not saying it's a good idea, but I don't.
You know, you could set it off running, do a backup first, just in case, obviously, in case it screws up.
It's probably more important on laptops than it is on desktop computers, because a laptop, you're taking to a restaurant, you're taking out to other people's work.
You can shove the sensitive files if you wish. So even if you don't want, I can't imagine why you wouldn't want to encrypt your entire hard drive, but if you didn't for any reason.
And I really should, I should, this is my job, you know? I should be doing these things, but I don't because I'm lazy.
But I guess in my mind, if the more of these things that I set up, the harder it is for me to check my backups to make sure they're actually working.
So when I weigh those risks, I'm like, I just need accessibility to be number one. Not to try to justify my poor choices in life.
I think these are really, really big things that people ask themselves, and it's great to hear Graham go "you should do this and you should do that." But there's the reality of it here too, right.
I just don't think it's going to happen. I think probably for most people, some sort of cloud backup solution is a good idea.
There are some very consumer-friendly solutions which will do this, little programs which will run in the background and will only back up the files which have changed.
And then if you have any kind of disaster, it could be a hardware disaster, it could be that you've overwritten a file, I find myself using online backup restoration all the time.
Because I'll have been doing a little bit of coding on my website or something, or I've deleted a file which I then realized, "ah, damn, that file I had 6 weeks ago, I really need it now," and I've put it into the trash can.
I can go to my online backup and it will dig it out for me.
If I was doing a restoration of all of my data, then yes, I'd use the online offsite backup. I'll tell you, I've been using one for years called CrashPlan.
It just runs in the background and never bothers me, and it tells me that it last did a backup 2 minutes ago.
So CrashPlan, just a couple of weeks ago, put out this message to their home user customers saying they're no longer going to be selling the consumer version.
If you want to keep with them, you have to upgrade to the small business version at least, which does cost more money.
And they've suggested that you could switch to some alternatives, and the one which they've sort of partnered with is an alternative called Carbonite, which doesn't do exactly what CrashPlan did.
Personally, I've decided, you know what, I'm going to stick with CrashPlan because I know it works.
But the concern which you have obviously is that some of these solutions can get expensive, particularly when you end up being responsible for lots of different computers as well.
Now there is a solution which is — well, there's a few solutions which are less expensive.
There's the CloudBerry solution, which is just a one-time purchase of a piece of software, which then uses your other cloud drive services, your Google Drive, your OneDrive, your Dropbox, and can use that space to put a backup into.
I should just sync my hard drive or my documents with Dropbox, which isn't a bad thing to do, and then use that as a backup. I don't really believe that is a backup.
But I don't think that is a backup.
And the reason is that if you get ransomware on one of your computers and encrypts the documents in your Dropbox, then it is going to sync all your encrypted documents to those other devices as well.
But another solution, if you want a cheaper solution for cloud backup, is to use cold storage services. And they give you really cheap data buckets which you can stuff your data in.
Again, it has to be encrypted. It does require more nerdiness than maybe some of these consumer products you just turn on on your computer.
And the way they make the bulk of their money is if you want to access the data.
Because with something like Glacier and the cold storage, you shove data in, but it might take 3 or 5 hours if you want to request a piece of data back, or you may have to spend more money to restore your data.
So if you're simply archiving, if you're imagining, well, actually I'm very rarely going to need these backups, but it would be nice to know that they're there, then that could be an option which you want to take up.
But, it's, you know, for that kind of storage, it's perfect.
So do check that out, guys, if you want to kind of review any of the suggestions, recommendations that we've provided in the show.
I guess the last thing we should mention is that a backup isn't a real backup unless you've tested it.
You can buy swag at smashingsecurity.com/store or join us on Facebook at smashingsecurity.com/facebook as well. Thank you very much, Maria, for joining us today.
Always a pleasure to have you on.
Recorded Future is the real-time threat intelligence company whose patented machine learning technology continuously analyzes technical, open, and dark web sources to give organizations unmatched insight into emerging threats.
Sign up for free daily threat intelligence updates at recordedfuture.com/intel.




"There's some risk in backing up via the cloud, as a data breach at that company could potentially expose your personal information."
This is why I recommend people use a zero-knowledge encrypted cloud solution. There are a few out there but the best, in order, are:
1. Tresorit
2. SpiderOak
3. Tarsnap
4. Least Authority
But be warned: zero-knowledge means no access if you forget your password! Also be prepared to pay – these companies don't (and can't) make their money by selling your data unlike the big cloud providers. Therefore to make their money you've got to pay a subscription.
David I think you're a bit over the top on this but better to be that way than "under funded"! anyhow here's what I do. I have 2 SSD 500 GB how swappable that are normally unplugged. I start with linux which right there makes it mighty tough to break in around here. Secondly I do your thing. I run a script that backs up /home and it runs automatically at 01:00 every Saturday morning. I also backup a few other things like bookmarks and some directories related to personal data under firefoxes database. If pics or videos directories have changed they get backed too (but I first check to make sure they're assessable)… now my backup plan is first thing disable the entire LAN. nobody talks to nobody else, see? I do this first on the router and then on the NIC. I then run the backup script manually. but just in case its also in my startup.
now because this is hot swappable I need to MANUALLY plug in the SSD. but not until everything has been disconnected, see? I then run the script. now when I do this manually the drive is automatically mounted by the OS when I first plug it in (however it tries that at the beginning of the script anyway). at the end of the script I send a umount command to both SDx's thus they become invisible to the sytem once the script completes.
I then remove one of the SSD's and actually carry it around with me! yep wherever I go it goes! the next week I do it all over again but remove the alternate SSD (to become my clossest "buddy" for that week!). btw the SSD's are installed into a prior 3.45" floppy bay.
result of all this? no right to criticize you I'm probably even worse! AND I RUN LINUX whereby a ransomware (or anything else obscene) is just about impossible.) sure you may know where the data on most people's machine resides… /home. but HOW are you gonna access the thing? wipe out the MBR(s), perhaps? too bad I make copies so better find plan "B" somewhere. you could try to upgrade privileges but guess what? I have that directory ENCRYPTED! I also use a 25 alphanumeric character PW. so basically mr RANSOMEWARE you are TOTALLY SCREWED!
I'm no Windows apologist but your comments couldn't be more wrong about Linux.
The security of Firefox is abysmal compared to modern browsers, so much so that a well respected security contest doesn't even bother attacking it any more:
"Pwn2Own 2016 Won't Attack Firefox (Because It's Too Easy)"
http://bit.ly/2kaC6Vx
Disabling "the entire LAN" will make no difference whatsoever if your Linux distro has been or gets infected by ransomware. Therefore disconnecting the SSD, making the drive invisible and so forth won't have much/if any effect if one of your files is surreptitiously infected.
Contrary to your belief ransomware is NOT "just about impossible"; it's out there and is ACTIVELY infecting Linux servers and desktops!
http://bit.ly/2ktOUSU
http://tcrn.ch/2ktNPul
KillDisk is also affecting Linux users as of January 2017 rendering machines unbootable:
http://bit.ly/2il6KXp
I could give many more examples but I won't for the sake of keeping this reply short.
In terms of "upgrade privileges" this is a piece of cake on Linux for an attacker. Their own chief developer Linus Torvalds has continually criticised distro programmers for not making this secure enough. It's easy to remotely elevate privileges in Linux by a malicious entity.
A good explanation of why Linux is not more secure than Windows can be found here:
http://bit.ly/2lvJMh5
http://bit.ly/2lyfxXL
Just five days ago (05/02/17) did a Gentoo Developer harshly criticise Linux for being way behind Windows in terms of security. He gave a dozen examples (there are many more) where Linux has simply not kept up.
http://bit.ly/2kWi9Bi
He's also uploaded some slides showing just a handful of the most appalling problems with Linux insecurity … they're not been fixed for many years:
http://bit.ly/2la02sd
Advanced security features in Windows have been around since 7… which is quite a while ago (7 -> 8 -> 8.1 -> 10) and Linux hasn't implemented a single one. We're now on anniversary editions of Windows 10 and security is constantly improving.
The problem with Linux is that it's maintained predominantly by volunteer developers. Each time a new update gets pushed out, sometimes several times daily, something breaks. They rely upon people sending them details of security fixes and, even when they do, there aren't enough developers with enough time to fix everything.
Even Linus Torvalds recognises how insecure Linux has become:
http://bit.ly/2kazyqv
At least with Windows it's maintained by Microsoft who are paid to keep it updated. Mission critical organisations like hospitals, government departments, military organisations (Department of Defense) and civil authorities use it. Problems are fixed quickly and regular patches are pushed out. There's proper support for legacy versions and regular non-security upgrades.
Not everything Microsoft is good but taking into account the vast disarray of Linux distributions, many of which are not properly updated, and major security flaws in Open Source software being left undiscovered and/or unfixed you CANNOT sensibly suggest that Linux is more secure than Windows.
Here's a perfect example of a developer not updating their encryption software and leaving a master password of "p", believe it or not, which opens any file encrypted by it. Yet people still use the software in the false belief that anything Linux is more secure.
http://bit.ly/2l0CuFj
I used to upload all my files to a cloudshare/dropbox type facility until I realised that they included a spreadsheet file of all my passwords and personal data! I now keep it zipped under password and in fact should just transfer it all to LastPass.
Years ago, when my Dell desktop BSOD'd I discovered the beauty of having a second internal drive to back up to. I used to use a free backup programme but realised that it was missing files out, so stopped using it. I tried Acronis for a while but it slowed my machine down so much I quit using it, even after I'd paid for it.
I used to burn a CD of my critical files every Friday and put it in a metal container in my car glove box! I figured that, if my house burnt down, my car would be ok on the street. I suppose that I might do that with a memory stick nowadays.
I do something very similar – I use the Windows Backup feature to back up my files to a Virtual Hard Drive (VHD) on the same drive *but* I then regularly copy that one file (which has all of my automatically backed up files within it) to a USB. The VHD is encrypted for security and my backup consists of dragging and dropping one file to a USB 3 – it's done within a couple of minutes.
My important data is also replicated in real-time to my encrypted, zero-knowledge cloud provider.
One word of advice SlipperyJim: if you're using ZIP files make sure you're using AES and NOT the old ZipCrypto. If you're making your ZIPs in Windows then they're not secure – they use ZipCrypto which can be easily cracked. 7-Zip provides AES encryption which, assuming you use a strong password, is uncrackable.