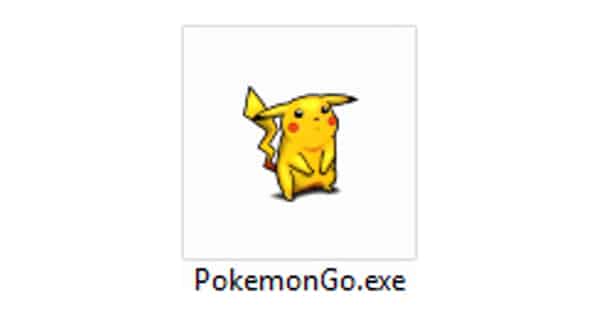
Originally spotted by Michael Gillespie, a security researcher who has identified and decrypted plenty of other locker programs, a new ransomware sample poses as a version of Pokémon Go for Windows.
This isn’t the first time researchers have run into fake copies of the popular smartphone virtual reality game.
At the time of Pokémon Go’s release back in early July, researchers came across an APK that claimed to be a copy of the game available on a non-Google URL. Not surprisingly, it turned out to be a malicious program that loaded the DroidJack remote access trojan (RAT) onto users’ Android devices.
A malicious take on “catch ’em all,” to be sure.
This is, however, the first documented case of ransomware that has taken on the hit smartphone game’s identity.
Based upon Hidden Tear, the now defunct open source ransomware project which spawned the likes of EduCrypt, the Pokémon Go ransomware doesn’t do anything remarkable… at least at first.
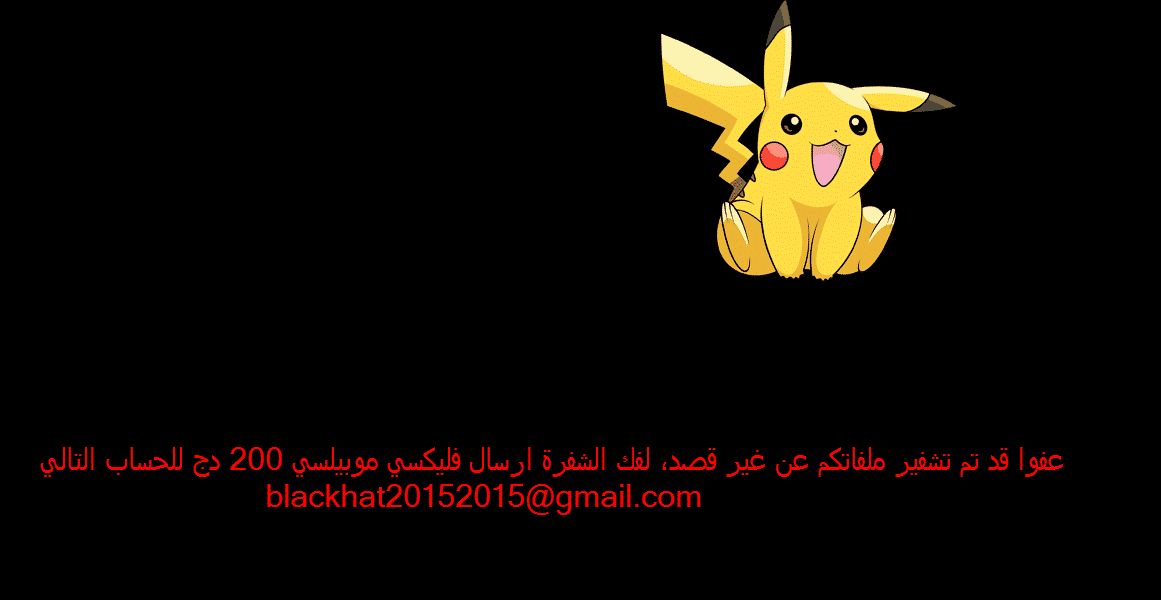
The ransomware targets a number of file extensions, appends .locked onto each infected file, and displays a ransom message written in Arabic that instructs the user to contact for payment instructions.
Most ransomware would be done at this point, right? Not this one!
Lawrence Abrams of Bleeping Computer analyzed the PokemonGo ransomware and found it takes things to the next level:
“Most ransomware infections encrypt your data, delete itself, and then display a ransom note. The malware developers are there to do one thing; encrypt your files so that you pay the ransom. With this said, most ransomware typically do not want to leave any traces behind other than the ransom notes. The PokemonGo ransomware acts a little differently as it creates a backdoor account in Windows so that the developer can gain access to a victim’s computer at a later date.”
Specifically, the crypto-malware creates the user account “Hack3r” and then deletes it from view by configuring a Windows registry key.
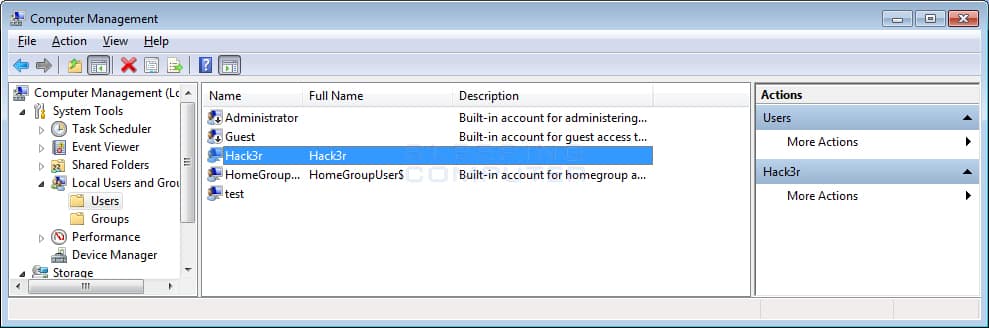
That’s not all. The ransomware also has the ability to create network shares and copy the executable onto all removable drives – just in case a user wants to carry the ransomware infection wherever they go!
The sample analyzed by Bleeping Computer used a static asymmetric encryption standard (AES) key, and its command-and-control server used a IP address registered for private use. Both of these observations suggest the ransomware is still in development but is ramping up to go live in the near future.
To protect yourself against this twisted Pokémon Go collector’s dream come true, avoid suspicious links and email attachments, keep your software up-to-date, and download applications from trusted sources.
The legitimate versions of Pokémon Go are available on Google Play Store and the Apple App Store for Android and iOS only. The game could potentially become available for Windows and OS X at some point, but it’s not there yet. As a result, any apps that claim to offer the game for a different operating system are most certainly malicious.
Watch out!