There’s a Bing ding dong, after Microsoft (over?) enthusiastically encourages Chrome users to stop using Google, and silence hits the British Library as it shares its story of a ransomware attack.
All this and more is discussed in the latest edition of the “Smashing Security” podcast by cybersecurity veterans Graham Cluley and Carole Theriault.
Plus: Don’t miss our featured interview with Kolide founder Jason Meller about his firm’s acquisition by 1Password.
Warning: This podcast may contain nuts, adult themes, and rude language.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
So some users thought Microsoft wouldn't be so tacky to use such a technique. Little did they know, and they assumed it was malware. So they thought this must be a scam. This must be something malicious going on. But it wasn't malware. It was just an intrusive, desperate ad. However, Microsoft don't it to be called an intrusive, desperate ad. They describe it as an opportunity.
An intrusive, desperate opportunity.
Yes, probably. Smashing Security, Episode 364: Bing Pop-up Wars and the British Library Ransomware Scandal with Carole Theriault and Graham Cluley. Hello, hello, and welcome to Smashing Security, Episode 364. My name's Graham Cluley.
And I'm Carole Theriault.
And Carole, I have a little secret to share with you.
A secret?
Last night I had a dream. About you.
What?
Yes.
I don't want to hear this.
More specifically, it was a dream about your podcast, Sticky Pickles.
About Sticky Pickles?
Because, yeah, because I heard that you had a special guest on Sticky Pickles, a celebrity guest, at least in my dream. You had Andy Garcia on the Sticky Pickles podcast.
How did you know I hang out with Andy Garcia?
Well, the funny thing was that you didn't know it was Andy Garcia. You thought it was—
Of course.
You thought it was Jerry Garcia from the Grateful Dead, leaving you in something of a sticky pickle.
Oh, well, you know, maybe you should come on the show sometime and regale all our listeners.
I'm here. I'm available. You have to say.
Oh, right. Okay. Okay.
Twiddling my thumbs, waiting for the invite.
You know what? I think it's time to kick the show off. First, let's thank this week's wonderful sponsors, Kolide, LastPass, Sophos, Sophos Networks, and Vanta. It's their support that helps us give you this show for free. Now, coming up on today's show, Graham, what do you got?
Oh, I'm going to be talking about being persistent.
Being persistent, giving nothing away there. And I'm going to talk about one of the worst cyber incidents in British history. Plus, we have an interview with Kolide's founder and CEO, Jason Meller, and he has some pretty exciting news to share. All this and much more coming up on this episode of Smashing Security.
Now, chums, chums, let's hear it one and all for the persistent. Yep, the people who never give up. Did you ever see that movie, the John Cusack movie Say Anything, where he holds the boombox over his head?
Yes.
And he plays the girl a Peter Gabriel song. You remember that? Don't Give Up.
Is it that one?
No, no, no. It was In Your Eyes. In your eyes.
Oh, yes.
So, yep. The people who never give up, those people you think you've dumped and they turn up on your doorstep at 3 o'clock in the morning with a boombox saying, let's get back together. The Mormons who ring your doorbell. They might find someone who's prepared to listen to them.
Yeah.
Or maybe you're more a dog with your head stuck inside a peanut butter jar, trying to lick out every last morsel. I don't know. What sort of persistence do you show?
I'm still here. On this show, week after week, I show up.
Episode 364. It's unbelievable, isn't it?
It is unbelievable.
Well, those are the people who never give up. They are wonderful. You know, they are the ancestors, I think, of the first monkeys who came down from the trees to walk on the land. You know, if we didn't have persistence, that would never have happened. We'd still be up in the trees. Maybe we'd still be in the primordial swamp. If one of us hadn't decided to crawl out and take the first brave gasp of air. So, you know, where would we be without them?
I thought you were going to say ancestors of Rik Astley.
Rik Astley?
Never gonna give you up. He's persistent.
Right. Yes. Very good.
Right.
So well done, Rik. Well done to the primordial gloop and the fish that resided in it. Well done to the monkeys. Well done to everything. Because without them, we wouldn't be here. It's down to their bravery, their persistence, and where, oh where, would we be without Microsoft? Let's be honest, the whole cybersecurity industry relies upon Microsoft, quite frankly, doesn't it?
I would mention Clippy. You wouldn't know what that meant.
Yes, yes, macroviruses wouldn't exist without Microsoft.
Nor would Solitaire, probably. It wouldn't have that much popularity.
Minesweeper as well.
Ah, the best.
Now, Microsoft, they have recently demonstrated their persistence in an act which rivals that of door-to-door encyclopedia salesmen. So they've never faltered in their quest to help us see the light, because Microsoft believes that our lives would be immeasurably improved if only we were to switch to Bing. Stop using Google as your search engine use Bing.
I think anybody that works at any company's job is that, isn't it? They're just trying to get everyone to sign on.
To promote Bing?
Well, no, to sign on to whatever they're schlepping, whatever they're selling.
I suppose, yeah, maybe.
When we worked at a particular company, we often would put out press releases saying this company is better than other companies, and, you know, was it really 100% true?
Shocked. Shocked I am. I'm appalled by you, Carole. And I'm also appalled to discover that a staggering 91.62% of all search engine queries go through Google.
Yeah, it's a bit gross.
It is really, isn't it? Go through that advertising company. So Google's market share has not actually dipped below 90% for 10 years. However, what's that I see on the horizon, galloping fast towards the front line? Oh, it's Bing, hot on the heels of Microsoft at a blistering 3.31% of the market share. Wow. They must have much less malware that's targeting them though, right? I mean, you know, there must be some reason why people aren't using Bing as a search engine. Is it simply because it's easier to Google? Is Google a cooler name? Are people not bothered to change? I don't know what it is. I mean, there are certainly safer, more privacy-conscious search engines out there, like DuckDuckGo. DuckDuckGo has 0.53% of the market share. I'm surprised it's so small. I'm really, I mean, I knew that Google is the market leader by far. Yeah, there are some regional differences. If you were to travel over to Russia, you would find that Yandex has 71.5% of the market share in Russia. Yeah.
And what about China, right? They have their own search engine as well.
I think they want you searching the internet at all. I don't think they're kind of against that idea. Now, it probably wouldn't surprise you much to hear that this Google dominance of search engines, it rankles a little bit. It's sort of, it's got a little bit of sand in the crevice of Microsoft. You know, it's upset those guys in Redmond. They don't like it.
I'm not surprised. They're thinking, God, we had almost every computer on the planet was running Microsoft for a while.
Right.
And where are we now?
Why don't we own the search? They're asking themselves.
Well, they kind of own OpenAI, so they're not doing too badly, let's be honest. But anyway.
Well, yeah, they own a lot of stuff. Teams and Microsoft Office and Project, I don't know, PowerPoint. They could try to be a bit more proactive in promoting Bing, and they've spent millions over the years. I've been watching this morning some of the archive of past Bing search engine adverts, like TV adverts.
I've never seen one, I don't think.
Well, they're not very memorable.
Okay.
Even though there is one with Philomena Cunk in it, who we like.
Yes, very much.
So she's funny, but generally they're not that great. And it looks like the ads aren't working judging by the percentages. So what else could they do? Well, I'll tell you what they could do. As you've already alluded to, Carole, Microsoft does control what might be the world's largest number of advertising spaces because they own effectively the desktops of PCs running Windows, right? Which is the dominant operating system.
Right.
They could change everyone's wallpaper to say, go and run Bing instead of Google. They could have done that. It would be a bit like when Apple pushed out that U2 album to everyone's iPod.
You see, I seriously, I think the ad campaign should be just Bing it up. Bing it up. Bing it up. Bing it up.
TM it, Carole. Otherwise they'll rip you off. Don't you want the money?
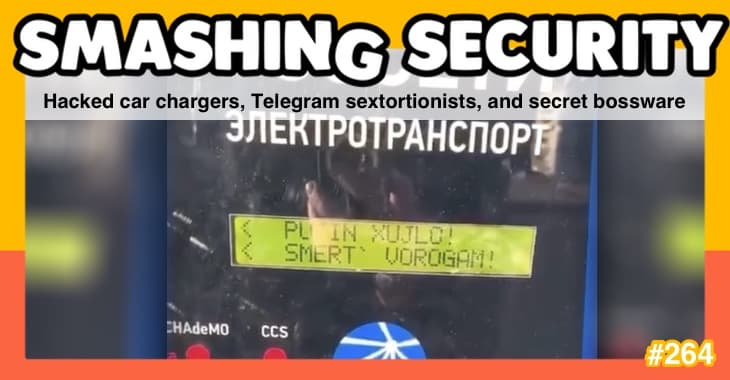
TM Carole Theriault.
Done. There you are. Very good. So, in recent days, there has been a bit of alarm caused by the display of a pop-up for users of the dominant Google Chrome browser. So, some of our listeners may have seen this. It's been popping up saying, "Hey, chat with GPT-4 for free on Chrome. Get hundreds of daily chat turns with Bing AI. Just try Bing as your default search. Easy to switch back. Install this service to improve the chat experience." So they are dangling a carrot.
I understand. Okay, good. They're enriching their experience. They're fighting back.
So, as Engadget describes, if you click "Yes, please," the pop-up will install the Bing Search Chrome extension, which makes Microsoft search engine the default. However, clicking yes to change the search engine will also prompt Google Chrome to pop up its own warning message asking you to confirm. Do you, did you really mean, hang on, did you really mean to change your search provider? Please, please stay with Google. Please stay with Google.
So they're politely jostling for our attention.
Well, it's more than that because Microsoft clearly anticipating that Chrome is going to display a warning, they pop up another notification saying, wait, don't change it back to Google. If you do, oh my God, you'll turn off Microsoft Bing search for Chrome and lose access to Bing AI with GPT-4 and DALL-E 3. And select keep it to stay with Microsoft Bing. So they're jostling for control of your search engine.
Wow.
Madness. Now, this kind of tactic isn't new for Microsoft.
Mm.
They've used similar techniques in the past and tricks to get people to switch from the Google Chrome browser to Microsoft Edge. Well, that didn't work very well, did it? A few years ago, they even forced people to switch to Edge when they rolled out a Windows update. And earlier this year, Edge was caught automatically importing browsing data and tabs from Chrome without users' consent, which pissed off some people.
Uh-huh. Anyway, this new pop-up recommending you switch to Bing, this has caused a bit of drama. People have been complaining on Reddit. I mean, that's what you do, don't you? Uh-huh.
So they thought this must be a scam, this must be something malicious was going on, but it wasn't malware. It was just an intrusive, desperate ad. However, Microsoft don't like it to be called an intrusive, desperate ad. They describe it as an opportunity.
An intrusive, desperate opportunity.
Yes, probably. So they said, this is a one-time notification giving people the chance to set Bing as their default search engine on Chrome. This is one of their spokespeople. For those who choose to set Bing as their default search engine on Chrome, when signed in with their Microsoft account, they will also get more chat turns in Microsoft Copilot and chat history.
Sweetening the deal.
According to Windows Latest, who looked at this, that's an online blog, they say that the advert came as a server-side update. They speculate that it's linked to a couple of files. They saw something called the BingChatInstaller.exe, which apparently Microsoft started pushing out to people's Windows systems on March 13th. This is all speculation that's going on as to what's happening out there. I don't have a computer which has done this that I can look at to see if this is happening.
Right.
There's some talk that there's a program called BingChatInstaller.exe, which Microsoft may well have pushed out. I think there's a bit of subterfuge here. I think I don't really like this. I think if Bing was really that good, people would just choose to use it, wouldn't they? If it was good enough, you don't think?
No, well, no, because they may not have ever experienced it. I mean, Google does own all the space.
Why doesn't Microsoft buy some more Google search ads to promote Bing and tell people how fabulous Bing is?
Line Google's pockets even more.
They could use a stolen credit card.
They could. Yes, they could. Not endorsing that. Not endorsing that, obviously. Right. I would like to know if you know anything about The British Library.
Ah, well, I know they've been in the news.
Uh-huh. But do you know anything about the institution itself?
Isn't the British Library where they have a copy of every single book?
Yes, they have between 170 and 200 million items.
So they will have copies of all the Harry Potter novels.
Literary treasures like the Magna Carta, Shakespeare's First Folio, original manuscripts from renowned authors like Jane Austen and Charles Dickens.
Doctor Who and the Wheel in Space, which is quite hard to get your hands on, I know, because there was a fire at the distribution plant. So I never got to see that one.
Well, maybe you should go down to the British Library.
The British Library.
Yeah. Some items are as old as 1300 BC.
Oh my goodness.
There's even a railway system known as the Book Conveyor to transport materials efficiently between buildings.
Oh, isn't that lovely? I like the idea. It's cool. Yeah.
But late last year, on Saturday, 28th of October, to be exact, it became clear that the British Library had been hit by a significant ransomware cyberattack that compromised the majority of the library's online systems. A number of articles on this very topic were published at the time, but just late last week, the British Library issued its very own cyber investigative report. Which talks about the incident, the impact, the lessons learned. And it's a really interesting read, particularly for any CISO or infosecurity professional. So link in the show notes. So how did it all go down? Well, it turns out the library was alerted that there was a problem by JISC. I don't know how you call it, J-I-S-C. These are the folks that provide the library's internet access and monitor movement of data across their networks. And they had identified that an unusually high volume of data traffic, so 440 gigs had left the library's estate at 1:30 AM on the 28th of October. And this can be equated with the tranche of data illegally exfiltrated by the attackers later on. Turned out to be an attack which was subsequently claimed by the Rhysida ransomware gang.
Yes, not to be confused with Jack Recider from the Darknet Diaries podcast.
Yes, well.
Although I suspect they may have named themselves after him.
No.
Isn't a recider or a recida, isn't that some kind of caterpillar or cockroach or something? I think.
No idea.
I'm so educated. It's almost like I've been to a library.
You haven't proved it, so.
Okay. Right. Google.
Or Bing. So these guys, Rhysida Group, these guys had exfiltrated data, encrypted or destroyed substantial portions of the server estate, and forcibly locked out all users from the network. So based on the analysis from the British Library cybersecurity advisors, the belief is that the attackers used three methods of attack to identify and copy these documents. So they first copied records belonging to finance, technology, and people teams on a wholesale basis. So this made up 60% of the content copied during the attack. They think they also launched a keyword attack scanning the networks for any file or folder that used certain sensitive keywords in its naming convention, such as "passport" or "confidential." This is the other 40% of content snarfed during the attack. And third, they hijacked native utilities. So these are IT tools used to administer the network and use them to forcibly create backup copies of 22 of the databases, which were then subsequently exfiltrated from the network. And they currently believe that several of these databases contain some contact details of external users and customers, but they can't be sure until the database's infrastructure capabilities are restored.
Okay, this all sounds terribly, terribly serious. And by the way, giant centipede confirmed by the internet. But thank you very much. I was close enough. It all sounds very serious, but this is a library. I mean, what sensitive information they really going to have other than, oh, you know, you're a bit late returning your books. I mean, you know, is it that big a deal if a library gets hit? I mean, obviously it's inconvenient.
Oh, really? It's a national treasure, do you not think?
Well, I've never been to it, so I've never really benefited from it.
I can't believe you. Anyway, whatever. Now, this is a ransomware attack, right?
Yes.
Right. So the data thieves demanded a payoff to keep the data private, and they wanted a payout of 20 bitcoins, which is about £600,000, for privileged access to all the personal information. But the British Library refused to pay the ransom. Okay, so the hackers then decided to publish close to 500,000 files of what they called exclusive, unique, and impressive stolen data onto the dark web for anyone to download.
All right, okay. Did anyone care?
Yeah, no one gave a shit. No one gave a shit. No one cares about libraries. I'm shocked. I'm almost speechless. Normally I'm really good at attacks, but right now I'm just like, what? But that's not all, Graham.
That's not all.
As well as exfiltrating the data for ransomware, the attackers also encrypted the data and systems and even destroyed some servers to inhibit system recovery and to cover their tracks.
Okay, my crass comments, let's put those to one side because I'm just saying those trying to get a rise out of you. Obviously, this is terrible.
You know what, Cluley, I agree. So the destruction of these servers is what had the most damaging impact on the library, says the report. They explain that they have secure copies of all their digital collections, both born digital and digitised content, and they have the metadata that describes it, but they've been hampered by the lack of viable infrastructure on which to restore it because they had legacy systems.
And they were reliant on the little choo-choo train for moving things around, weren't they?
Right. And they now have to rebuild since this has happened, rebuild the infrastructure. And that has been underway since December and remains ongoing.
This has been months and months and months, hasn't it?
Yes. Well, yes, since October last year. So I can add them up if you want, but almost 6 months. So of course, readers, these are people who use library, the library and its services.
No, thank you for explaining what readers are.
So readers have been subjected to difficulties and delays as staff have been forced to locate books, manuscripts, and other items manually. And this is not just your typical library in your small town here. This has, what did we say, 200 million items?
That's a huge number, isn't it?
It's a massive number.
Yeah.
So, you know, the librarian, let's call her Debbie, she's going to have trouble finding some ancient archival Egyptian text for you without any computer help.
Poor old Debbie. Debbie does data breaches. What a calamity.
You make fun of this, but researchers and academics around the world, Graham, come to the library to see rare and ancient documents and artifacts for their dissertations, for their research. And they can't because there is no — how would anyone be able to find anything that they were supposed to look at? And there's some employees that have done absolutely nothing since the attack because the disruption has made their tasks impossible. They just can't do any of their job. And get this, about 20,000 published authors who get 13p, right, each time their books are borrowed from libraries. This is a system managed by the British Library. And they've had a lot of trouble getting their cheques.
You get 13 pence every time your book's taken out of a library.
I learned all about this looking into this, because it's a little rabbit hole. But there's actually conferences, library conferences, where authors go and basically tout their book.
Presumably quite quietly. They can't make too much noise.
The Financial Times estimated the attack will cost libraries up to £7 million. They conclude this report with actions the British Library is planning to take in order to withstand any future attack.
Ah, this will be useful to other people.
I think this whole report is really useful for other people. I really urge you guys all to read it. I really wish all companies that face some horror show would be able to put out a report to the public to teach and give all the learnings. We would be much better off.
I haven't read it, but I heard it was really good. So I've been meaning to read it.
By me? Or—
No, no, no, no, not— No, I just did just hear you say it. Yes. But I've heard other people other than Carole Theriault.
Oh, well, who cares?
I've had other people recommending it. To be honest, it's a bit going to the library. I've heard that going to the library is really good as well. And I've been meaning to do it. And I probably should. I think it would probably enhance my life considerably. But seriously, this report I heard was excellent and that they've done a sterling job. And isn't it great that they haven't actually paid their attackers?
Hallelujah, I agree. Now I just want to share a few of the actions 'cause there's 16 of them, so I'm obviously not gonna go through all of them.
Okay.
So number 1 on my little mini list here is fully implement multifactor authentication and not just at the endpoints, but even on certain supplier endpoints. So I just think that's very interesting 'cause they didn't have that there and that's, I think that was one of the reasons why their attackers got through. Eliminate legacy technology. Legacy systems are not just hard to maintain and secure, but they're extremely hard to restore, they say. Retain on-call external security expertise. And that's an important one for me to share on the show because they want a specialist external security advisor on retainer to help them improve speed of response. So, if any of you are looking for a job, you know, this would be the time to get in touch.
Was one of their recommendations sponsor a popular cybersecurity podcast?
No, but you should get in touch with them. You should get in touch with them.
Maybe we should. Maybe we should. Maybe we should do a podcast from the library. And I'll then go into a library, which will be fantastic.
Everyone will have to turn up their volume though. Shh.
Legacy managed file transfer tools are dated. They lack the security that today's remote workforce demands. Companies that continue relying on outdated technology put their sensitive data at risk. Well, this podcast is sponsored by KiteWorks, who enable organizations to effectively manage risk in every send, share, receive, and save of sensitive content. To do that, they've created a platform that delivers content governance, compliance, and protection to customers tracking, controlling, and securing sensitive content as it moves within, into, and out of organizations, all while ensuring regulatory compliance on all sensitive content communications. KiteWorks provides the industry's first private content network for protecting risky third-party communications with secure email, secure file sharing, secure mobile, secure web forms, managed file transfer, and governed SFTP servers. Visit KiteWorks.com to get started today. That's KiteWorks.com, and thanks to them for supporting the show.
Smashing Security is also sponsored by Vanta. Managing the requirements for modern security programs is increasingly challenging and time-consuming. Enter Vanta. Vanta gives you one place to centralize and scale your security program. Quickly access risk, streamline security reviews, and automate compliance for ISO 27001, SOC 2, and more. You can leverage Vanta's market-leading trust management platform to unify risk management and secure the trust of your customers. Plus, use Vanta AI to save time when completing security questionnaires. Smashing Security listeners, you get 20% off Vanta. All you lucky sausages have to do is visit vanta.com/smashing to claim your discount. That's V as in Victor, A-N-T-A.com/smashing. And thanks to Vanta for sponsoring the show.
You've probably heard us talk about Kolide before, but did you know Kolide was just acquired by 1Password? Well, that's pretty big news since these two companies are leading the industry in creating security solutions that put users first. For over a year, Kolide Device Trust has helped companies with Okta ensure that only known and secure devices can access their data, and that's what they're still doing but now as part of 1Password. So if you've got Okta and you've been meaning to check out Kolide, now's a great time. Kolide comes with a library of pre-built device posture checks, and you can write your own custom checks for just about anything you can think of. Plus, you can use Kolide on devices without MDM, your Linux fleet, contractor devices, and every BYOD phone and laptop in your company. Now that Kolide is part of 1Password, it's only going to get better. Check it out at kolide.com/smashing to learn more and watch the demo today. That's k-o-l-i-d-e.com/smashing. And thanks to them for supporting the show. And welcome back, and you join us at our favorite part of the show, the part of the show that we to call Pick of the Week.
Pick of the Week.
Pick of the Week. Pick of the Week is the part of the show where everyone chooses something they. Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they. It doesn't have to be security-related necessarily.
Better not be.
Well, my Pick of the Week this week is not security-related. In fact, it's not a Pick of the Week. It's a Nitpick of the Week. The thing I want to have a nitpick about this week I think is very, very simple. It's people. People specifically who use the word literally to emphasise something.
Literally, that bugs you?
My head literally explodes at the thought of people using the word literally incorrectly.
OK, I'm going to stay out of this. I'm beginning to worry about you seriously.
No, no, I'm interested in your point of view.
How can this bug you? And how come do they always go, "To be honest," at every beginning of every sentence?
What? You know what? Funny you should say that, Carole, because I've made a list of other phrases that annoy me. And one of them is, "To be honest," or "If I'm honest," "Basically." Oh, my son says "basically" all the time. And I always say to him, "No, tell me the complicated version." "Basically, Dad, basically." "At the end of the day." You sound like such a dad as well.
A grumpy dad.
I am a dad. At the end of the day? Why do people say that? Or, I turned around and said, and he turned around and said, and I turned around. Well, which way are you turning now? Which way are you pointing now? There's been so much turning around. It's unnecessary.
This is a pathetic, this is a pathetic Pick of the Week, and it says more about you than anybody else who has maybe verbal tics because they maybe feel anxious or uneasy, or maybe you make them nervous.
Well, my alarm is caused by the fact that a number of dictionaries are now apparently giving the definition of literally to mean not literally. So they've reversed the definition. So my head literally exploded apparently is fine.
You know, I've always had a problem with one word, which is completely unrelated, but much more interesting. Inflammable.
Inflammable and flammable.
Yeah. Inflammable and flammable.
Inflammable and flammable mean the same thing. So what is the word for something which is not flammable?
Non-flammable?
Correct. But why do we have flammable and inflammable?
Yeah.
Listeners, let us know. Anyway, if you're the sort of person who says literally and you want to go into the British Library, I'd be on your guard because it's the sort of thing they may test you for as you enter through the doors.
To be honest, Graham, I think this entire Pick of the Week is a bit lame.
I just saw you, what you did there. You inserted the word basically.
Took you a while. Doesn't bug you that much.
Carole, what's your pick of the week?
So we have a friend that is studying psychotherapy.
Yes, we do.
And when she started studying that stuff, I was, what is that? What kind of woo-woo is that? Tell me more because you're my friend. And over the years, she's been sharing some of the, you know, foundational thoughts behind it and different therapies and all kinds of things that sit in this tiny little world. And I was, this is kind of interesting. And so I go galloping through podcasts to see if I can find anything on the subject. And I land on this podcast called Good Morning Monster. Now, do you remember the movie Mommie Dearest with Joan Collins? Did you ever see that?
Joan Collins?
I think it's Joan Collins.
No, no, wasn't it?
Bing it, Bing it.
Okay, okay.
Sponsor us.
Hang on. Oh dear. Joan Crawford.
Joan Crawford. Damn it.
No, that's 1981. Is that the version? Is that what you want?
Is that the one? That must have been the one I saw, because when I saw it when I was a kid, and I was wow, that's a pretty shitty mom, right? Thank God Mariah doesn't do that. And Good Morning, Monster is a scripted drama based on one of 5 stories in a book by the same name. And the mom in this story makes Mommy Dearest look like Mary Poppins. So in the book that the podcast is based on, there's a therapist called Katherine Gildener, and she presents 5 of what she calls her most heroic and memorable patients. And among them is the story featured in this podcast. And it's basically about this glamorous workaholic who gets in touch with the therapist to deal with huge work anxieties that she has. But it turns out that the mom might have played a much bigger and more horrible role in how our workaholic deals with the world. So every morning, the mother would greet her daughter not with hi, or hello, beautiful, but good morning, monster. I hoovered up the 8-episode podcast. I wanted more, went to the library app, borrowed the audiobook to listen to the 4 other stories. One is of a successful first-generation Chinese immigrant musician who can't find love. Another is about a Canadian native who was officially ripped away from his family at age 5 to be re-educated. I mean, they make for harrowing reading, not for kids, and often heartbreaking. But the author has a light touch and doesn't hold back when she gets something wrong. And there's humor in it. It's humble, it's moving, it's very human. And I the podcast, but I love the book. And I learned new terms in therapy so I can impress our friend, right? So I got things, I'll be able to knock out words like transference and countertransference and ancestral trauma. And narcissism. You know, ever heard of that one, Graham? The last one? Narcissism. Ever heard of that? Anyway, if this sounds like your thing, listeners, the name of the podcast and the book is Good Morning, Monster. You find it at your library or at your local bookstore.
Fantastic. Now, Carole, you've been busy this week. You were chatting to Jason Meller at Kolide.
Yes, I was talking to Jason all about their next steps because they have some big news to share. Listen up. Listeners, today I am chatting about all things Kolide with the company's very own CEO and founder, Jason Meller. Welcome to Smashing Security, Jason.
Thank you so much for having me.
I know I should say welcome again. You've been here a few times.
I know, I'm getting the hang of this.
Since we last chatted, there has been a pretty huge announcement concerning Kolide, hasn't there?
Oh, just a little bit. Maybe a tiny tweak.
Tell us everything.
Yeah. So if you haven't heard the news, Kolide and 1Password are joining forces. More specifically, we've been acquired by 1Password. This is something that I've been working on with them for a while. Things have been going really well for Kolide since we launched our device trust offering last year, and we had started some talks the end of last year around working together in some form of partnership. And when we actually sat down and conveyed our visions, they were so close that we were why are we going to just go our separate ways and try to tackle the same problem as separate entities. Let's do this together. And to me, as a CEO who's very mission-focused, my job and my mission has always been how can we get end users to be a major part of the security remediation story? That's why I wrote Honest Security. That's why I built Kolide. I couldn't think of a better company to work with, and 1Password feels so similarly about end users. And feels so similarly about honesty. When we launched Honest Security, the manifesto I wrote, I know some of the 1Password founders, they actually had this chat internally why didn't we write this? This sounds like it's coming from our voice. So we're just very in alignment from a cultural perspective. And strategically, we just had a lot of things that we wanted to do that were similar. So it just made sense.
It's really great because I personally am a very huge fan and user of 1Password. I was reading your blog on your announcement, and I'd like to quote you back to you.
Sure.
You say, "It is my belief that every person in the world deserves to use computers with dignity and without fear of being taken advantage of by criminals and bad actors who seek to degrade, deny, or destroy the incredible things we all accomplish with the help of these magical devices." Now, I wanted to ask you, do you feel like this new— you joining 1Password underpins this belief?
100%. I don't think I could have agreed to any acquisition where I thought the parent company wasn't going to be in perfect alignment with how I feel. I have a very strong sense of right and wrong, and a lot of the things that I've done at Kolide were informed by experiences that I had when I was really young. You know, the first of those being just the excitement I had for computers during the dawn of the digital age and the World Wide Web. These are incredible machines. They allow us to extend the essence of ourselves far beyond what was ever possible. And they're incredible and everybody should feel good about using them. And then that is diametrically opposed to other experiences I had when I was starting university and I was doing IT tech support for students and just see these students that were so sad or so upset because their machines were just loaded with malware. Or I remember this one woman came in and she was crying because she thought this stalker put a Trojan horse on her computer and she thought that she was afraid of her computer because she thought it was being used against her own interests. And it just really pissed me off because on one hand, these things are incredible and on the other hand, no one's able to use these devices with any real dignity. And the direction that we're going as an industry, I just never sat well with me. It was always about, all right, we have to solve these problems as an organization. We have to solve the malware problem. We have to solve the compliance problem. So what is the way that we're going to do that? We're going to force the device to behave in a way that benefits the organization, but that wrenches control out of the hands of the end user who's supposed to be productive with it. It just never sat right with me. And it took me many years at Kolide to figure out what the answer was. And we found it. It was device trust. It's having a conversation with the user with some actual consequences if they don't listen to the security team's recommendation, but giving them the agency to sometimes break the rules and push back and to create a system in which that's possible. That is so much in the spirit of, if you think about 1Password, right? 1Password's a company that had to solve a very human problem. Passwords, they are not really a technology problem. They are a problem because human beings cannot remember long, complicated strings of text. We need to put them somewhere. And if you think about the state of passwords 10, 15 years ago, we had all of these experts telling us, hey, you got to use a separate password for all your different services. They need to be complicated. And they weren't providing any tools. So yeah, we heard everybody, but we didn't have the right capabilities to actually listen to the advice. And then 1Password comes along and all that whole category was created and now they're ubiquitous and we now can listen to the expert's recommendation. We can do it with ease because that's what the software does. And it makes us feel empowered, confident, and we can use our machines with dignity. That's what I've always wanted to do on the device compliance side and protecting devices. And so to me, it's just perfect alignment.
So speaking of device trust, as most of us know, our listeners know, Kolide is a huge advocate of the zero trust model. And you guys have been providing stellar support for auth provider Okta. Now, will you still be providing support for Kolide's device trust Okta integration now that you're a part of 1Password?
Of course, yeah. The goal here with this acquisition was to accelerate my goal, which is to get what we've built at Kolide into as many hands as possible. So we are in no way, it's not on the table for us to take what we've built and take it away from people who could have gotten it before. And actually, on the other hand, we want to continue to increase that investment with Okta. The way that I think about it is if you're looking to buy something like Kolide, you really are buying it because you want it to fit into an investment that you've already made. Okta's a major investment for you. When you roll out Okta, it's a huge project. It's really hard to roll back. It becomes part of your company. It's part of almost your authentication culture. So we want to make sure that we are being a good citizen within that ecosystem. So if Okta comes out with a new whizbang way to do device assurance and stuff, we want to be in perfect alignment with that, and that's going to require continuous R&D as they evolve their offering. So we want to be the best possible way to achieve this within Okta. So that's going to be on the table and it will always be on the table for as long as I'm here.
You know, I can just see listeners that are also customers of yours right now feeling so smug that they've made the decision to work with you because it's exactly what everyone wants to hear. Now, this is maybe tricky with this announcement. Will you maybe be considering other auth providers in the near future to integrate with?
Yes. Yes. So it is true that, you know, it's great to have focus, but I do have a goal here, and that goal is to get this in the hands of everybody. Yeah, the thing that we did when we launched Device Trust, we had to start with Okta because quite frankly, they were the only ones that really had the platform where we could build it to our vision. We didn't have to make many compromises in how it worked, and we needed to do that because we wanted to vet out the idea to see if it really was going to work in practice. And boy, did it ever. We understand what are the important pieces of it. And now we can hatch our plans to bring it to folks who have been just begging us. I don't have Okta. I don't have any plans to get Okta. We're a smaller company. We don't even need a really formalized IDP or SSO solution yet. I'm using Google Workspace or I'm using whatever Microsoft's calling it these days. I believe it's Microsoft Entra. We just want to get that rocking and rolling and get Kolide on top of it. So yes, we are moving forward with those plans. In fact, if you go to our website today and you try to sign up and you say that you don't have Okta, we'll actually kick you over to a form where we actually ask you some questions about what you are using. And those are now driving conversations that I'm having with prospects and existing customers on how we can build the version of this that's going to be best suited if you have any other SSO provider, including Microsoft Entra and Google Workspace. So if you are interested in being part of that beta, please reach out. This is something that we're going to be getting done in months, not quarters. So we're really excited to talk to folks who are passionate about device trust. They want what Kolide is offering, but they don't have any plans to get Okta. And we want to hear from them and understand what their needs are.
So where do they go again if they really— I'm sure there's listeners that would love to be part of that. Where would you recommend they go?
Yeah, just go to kolide.com/auth-beta. Provider-survey, or you can just go to kolide.com, K-O-L-I-D-E dot com, and then just click contact sales. Just fill out the form and just say that you don't have Okta. So either way, we'll find you and we'll get you into the right bucket.
Brilliant. Now, Kolide at the moment is an independent product, but with this new announcement, do you see it being packaged with 1Password?
Yes and no. So we want to remain— so here's my theory around this, and 1Password believes this too, is that when you have products, there are packages of emphasis. So you want to take the different parts of each product and you want to make sure that they can be what they're supposed to be. You don't want to create these arbitrary, let's just smash everything together and put it under one giant menu bar item. You want to have these things feel very separate and give customers options of buying them separately because we just have very different customers today, right? Today, Kolide only is sellable to people who have Okta and 1Password is, you know, even their enterprise password manager is best suited for folks who are still in that part of their journey within their organization. Or even they also have a consumer business, which is quite large. So what we want to focus on is what value can we bring to folks who have already deployed 1Password's Enterprise Password Manager, what they call internally EPM. So to me, my vision for this, and maybe I'm talking out of school a little bit, but here's sort of what I've started to work on. There's this thing in 1Password that I love. It's called Watchtower. And what Watchtower is all about is giving end users alerts that help them understand what is the security of their password. So for example, let's say you've created a password on a website and that website gets compromised and you've never changed your password. Well, it will have an alert for you to look at and say, hey, you need to go back to this website, go reset your password, change it, because that password probably now is in somebody's hands. So the challenge with this, and this is the same challenge we faced in the early days of Kolide, is you can tell users about these problems until the cows come home, and only some percentage of them is ever going to actually action them, which makes us sad. These are real problems. Those attackers really do have your password. Now, it may not be a really big deal because you hopefully are not reusing it anywhere, but maybe you are reusing it. So we want people to look at these things and fix them. Well, that's Kolide's entire job. We know how to do that now. So in my mind, if I'm a business owner, or I'm the IT owner, I can do something in Kolide say, hey, if this user is trying to sign into some of our sensitive apps and they have these intense alerts in Watchtower, let's have them just take a beat and go to 1Password and get some of those fixed. Then let's let them through to our most sensitive apps. Let's get them on the bus of fixing really important problems that are putting both them and the company at risk. That's what we've always been about, and that's a great way to get way more value out of Watchtower than it would have been previously possible.
Wow, I love that so much. We're coming to time already, which I hate. Is there anything else that you'd like to add, Jason?
Well, the thing that I'll say is we're going to be at RSA this year, and we're going to be jointly presenting, which is going to be really exciting. Now here's a little bit of an inside scoop. We're going to be talking about a really grand vision about how we see the zero trust space. So as you said earlier, Kolide has always been a big proponent of zero trust access in that model. But I've always felt that the vision— that it's always felt a little bit more of a principle or even a little bit of zealotry rather than a real category. So I'll tease this is that we have a really expansive vision on how to connect the dots between these unmanaged sort of shadow IT things and then getting those things managed and then putting device trust in front of them. So I'll just kind of put that in there as a teaser. We have a really strong vision here and you should come to RSA and learn more about it and we'll be talking about it a lot after May.
Fantastic. Jason Meller, CEO and founder of Kolide. Huge congratulations to you. I think your future is very bright. And thank you so much for chatting with us today.
Thank you.
Listeners, to learn more about the Kolide and 1Password acquisition and to check out Kolide's shadow IT report, go to, simply go to kolide.com/smashing. That's kolide.com/smashing.
Fantastic stuff. And that just about wraps up the show for this week. You can follow us on Twitter @SmashingSecurity, no G. Twitter allows to have a G. We also have a Mastodon account. And don't forget to ensure you never miss another episode. Follow Smashing Security in your favorite podcast apps, such as Spotify, Pocket Casts, and Apple Podcasts.
Huge, huge thank yous to our episode sponsors, KiteWorks, Fanta, and Kolide. And of course, to our wonderful Patreon community. It's thanks to them all that this show is free. For episode show notes, sponsorship info, guest list, and the entire back catalog of more than 363 episodes, check out smashingsecurity.com.
Until next time, cheerio. Bye-bye.
Bye.
Hosts:
Graham Cluley:
Carole Theriault:
Episode links:
- Search engine market share – Oberlo.
- A compilation of Bing ads – YouTube.
- With Edge, Microsoft’s forced Windows updates just sank to a new low – The Verge.
- Microsoft fixes Edge browser bug that was stealing Chrome tabs and data – The Verge.
- Is this Microsoft Bing Popup Malware? – Reddit.
- Microsoft confirms Bing pop-up ads in Chrome on Windows 11 & Windows 10 – Windows Latest.
- ‘A 22-carat disaster’: what next for British Library staff and users after data theft? – The Guardian.
- LEARNING LESSONS FROM THE CYBER-ATTACK British Library cyber incident review – British Library.
- The Disturbing Impact of the Cyberattack at the British Library – The New Yorker.
- Thanks to a shadowy hacker group, the British Library is still on its knees. Is there any way to stop them? – The Guardian.
- Have we literally broken the English language? – The Guardian.
- According to the dictionary, “literally” now also means “figuratively” – Salon.
- Good Morning, Monster: A Therapist Shares Five Heroic Stories of Emotional Recovery – Amazon.
- Good Morning, Monster – Apple Podcasts.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff)
Sponsored by:
- Kiteworks – Step into the future of secure managed file transfer with Kiteworks.
- Vanta – Expand the scope of your security program with market-leading compliance automation… while saving time and money. Smashing Security listeners get 10% off!
- Kolide – Kolide ensures that if your device isn’t secure it can’t access your cloud apps. It’s Device Trust for Okta. Watch the demo today!
Support the show:
You can help the podcast by telling your friends and colleagues about “Smashing Security”, and leaving us a review on Apple Podcasts or Podchaser.
Become a supporter via Patreon or Apple Podcasts for ad-free episodes and our early-release feed!
Follow us:
Follow the show on Bluesky at @smashingsecurity.com, or on Mastodon, on the Smashing Security subreddit, or visit our website for more episodes.
Thanks:
Theme tune: “Vinyl Memories” by Mikael Manvelyan.
Assorted sound effects: AudioBlocks.