 As if it wasn’t bad enough that Sony Pictures found itself comprehensively hacked late last year and its emails and confidential data trawled through, WikiLeaks has now made things even more uncomfortable for the firm by creating a searchable online archive of the 30,287 documents and 173,132 emails.
As if it wasn’t bad enough that Sony Pictures found itself comprehensively hacked late last year and its emails and confidential data trawled through, WikiLeaks has now made things even more uncomfortable for the firm by creating a searchable online archive of the 30,287 documents and 173,132 emails.
From his small corner of the Ecuadorian Embassy in London, WikiLeaks founder and editor-in-chief Julian Assange attempted to justify the release of the documents:
Now published in a fully searchable format The Sony Archives offer a rare insight into the inner workings of a large, secretive multinational corporation. The work publicly known from Sony is to produce entertainment; however, The Sony Archives show that behind the scenes this is an influential corporation, with ties to the White House (there are almost 100 US government email addresses in the archive), with an ability to impact laws and policies, and with connections to the US military-industrial complex.
“This archive shows the inner workings of an influential multinational corporation. It is newsworthy and at the centre of a geo-political conflict. It belongs in the public domain. WikiLeaks will ensure it stays there.”
If Sony was furious at the media for publishing information stolen by the hackers before, they’re likely to be incandescent with rage at WikiLeaks for making everything available in a searchable archive now.

It’s a shame that Assange and his WikiLeaks colleagues didn’t go to greater effort to sift through the emails to find some smoking guns that might implicate Sony Pictures as being up to no good. As it is, it’s quite a lot to trawl through.
I had a quick look and found emails from Sony staff organising birthday parties, arranging cupcake deliveries, and talking about promotional plans for movies. I’m sure there may be something more damning there too, but I’ll leave it to others to uncover.
What I did find was a lot of evidence that Sony Pictures, and its staff, were pretty lousy at following best password practices.
Hopefully since their mega-hack they’ve learnt their lesson, and changed any passwords which may have been compromised, because judging by some of the things I saw they were making schoolboy errors.
Take the following, for instance, where Sony Pictures showed it wasn’t above using some very easy-to-guess admin passwords for systems on its servers (I added the highlight):
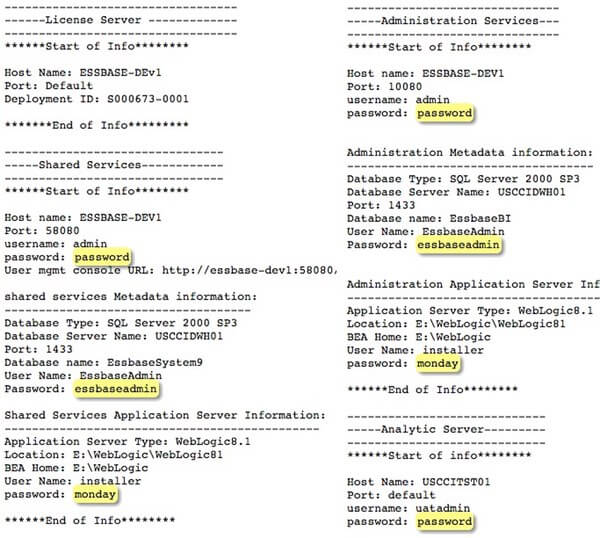
Passwords of “password”. Passwords which are identical as the username. Passwords which are just days of the week. It makes you want to hit your head against a brick wall.
Here’s another example of a document created, I suspect, by a Sony employee. To save their embarrassment and reduce any potential risk I have obscured their username (not a measure that WikiLeaks has taken, of course):
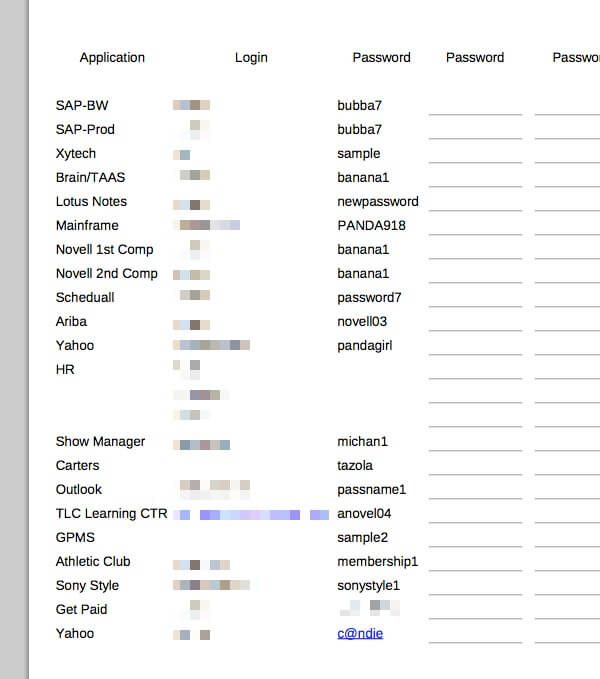
There are many many more examples.
In fact, over 1100 of the 30,287 Sony Pictures documents in the WikiLeaks haul contain the word “password”. No doubt even more evidence of sloppy password practices could be found in the email archive too.
Who needs sophisticated password-cracking software if passwords this poor are used by staff to secure their company’s systems and accounts?
Don’t feel too smug about Sony’s discomfort – ask yourself if you are taking enough steps to secure your passwords. Does your company use strong password management software to generate complex, unique, hard-to-guess passwords?


Who needs sophisticated password-cracking software if users store them in plaintext in Office documents, PDFs, emails etc? The people to blame are Sony infosec management, of course, not the end users. People will always do dumb things like that until it's explained to them (repeatedly :) ) putting passwords in email, for instance, is a very dumb thing to do.
And then they need to start issuing formal disciplinaries against people who do that sort of thing.
Yes, it is indeed problematic to have passwords in mail, and more generally credentials in plain text. Yes it generally comes down to a user at some point. But putting passwords in email is not always considered bad practise (this is somewhat conflicting; there is more to this). It depends on how, why and what service; there are definitely traps here, and likely they do occur.
Mailing lists comes to mind – they send reminders for membership (configurable; you don't have to have this). The problem isn't this by itself, the problem is when you're using it for anything else (users, as below). Unless the user creates the password – in which case it has a chance of being a previously used/shared password[1] – the only way they'll have the password is if it is emailed to them. More importantly, this isn't a password to log in to a service, but only for the list interface (and in many cases you don't even need to interact with the web interface; your mail client is sufficient). Of course, when that check fails, when someone uses a password they use somewhere else, that is definitely a very bad thing, and that it is sent in email is indeed very risky.
In short: yes, it is problematic; however, sometimes it is somewhat expected and/or the most acceptable IF it has to be done somehow. Any problems ultimately comes down to the security of the systems involved, which indirectly and directly comes down to the users (including their subscription lists, whether they specify a password that is already used or more critically used for something else like system accounts, and the devices they use that will see/use said passwords [and yes the security of the server as well])… as well as the decisions of the user (administrator included).
[1] Choosing your own – new, unshared, strong – password is of course the best choice, as well as disabling any reminders.
Hard to believe that (seemingly) intelligent people are still using Passwords this poor.
I understand if you have a large number of PCs and accounts such as Sony, that some may argue that it’s “inevitable” but this comes down to laziness doesn’t it?
But seriously using Password as your Password?
Love the Blog Graham
Sean Durrant
Well… if you find that difficult to believe, you have some catching up to do (see the tip below). But to make light of it, perhaps this would be more entertaining:
https://grahamcluley.com/dress-bad-passwords/
Tip: nothing should surprise you when it comes to security, or actually when it comes to people (which is, after all, the weakest link in the chain of computer security – it is so weak that it is just a very large hole). Of course, not being surprised about people unrelated to security also is valid. In any case, this mindset will take you a long way. If something seems too hard to believe, don't be surprised if it happens. Take the worst incidents in computer security history (which is decades old), and mark my words: we've seen nothing yet; it will get worse in some way or another, the most bizarre, unfathomable things will meet its match eventually.
Some might claim I'm just a cynic. They're right – I am (and I've yet to see enough reason why I shouldn't be), but when it comes to security, it so happens that I've just seen so much (above/under/middle ground) that nothing surprises me.
With caveats, though. ID federations (single-sign-on services and password managers) create a single point of failure, not unlike putting all the eggs in a basket. It remembers all my passwords when un-hacked and loses all my passwords to criminals when hacked. It should be operated in a decentralized formation or should be considered mainly for low-security accounts, not for high-security business which should desirably be protected by all different strong passwords unique to each account.
It is too obvious, anyway, that the conventional alphanumeric password alone can no longer suffice and we urgently need a successor to it, which should be found from among the broader family of the passwords and the likes. At the root of the password headache is the cognitive phenomena called “interference of memory”, by which we cannot firmly remember more than 5 text passwords on average. What worries us is not the password, but the textual password. The textual memory is only a small part of what we remember. We could think of making use of the larger part of our memory that is less subject to interference of memory. More attention could be paid to the efforts of expanding the password system to include images, particularly KNOWN images, as well as conventional texts.
"ID federations (single-sign-on services and password managers) create a single point of failure"
Yes, if you rely only on passwords. But that's not the only possibility. Only good can come of password managers, if used properly. If someone finds passwords – or whatever else is implemented – is inconvenient, and there is a way to circumvent it, they will, and then it doesn't matter if it is passwords or something else.
"that the conventional alphanumeric password alone can no longer suffice and we urgently need a successor to it, "
Passwords have never been enough and I dare say they're stronger these days (there's also stronger encryption algorithms, password managers, fewer restrictions on length, characters, etc.). But even then, to rely only on them is a problem (or let's say it differently: it is less secure than if you had additional protections), and I'm afraid alphanumerical has always been weak; they never sufficed (this might be extended to say that the most determined attacker will succeed eventually, somehow). We don't need a successor. Passwords serve a purpose and to remove them in favour of something else is silly, when you can have multiple layers (doesn't matter what the layers are, so much as they exist and aren't the same defence; e.g. the same password at two different prompts isn't all that helpful).
"The textual memory is only a small part of what we remember."
… and in any case, if you can remember it, and you have multiple accounts, then it isn't as strong as it could be (e.g. passwords). Which means memory is less relevant. But as an aside, I can remember text far more than images or other things.
"More attention could be paid to the efforts of expanding the password system to include images, particularly KNOWN images, as well as conventional texts."
Key point: nothing is perfect, everything has flaws, and that is why there should be more[1]. Passwords are one example. I'm curious though. How are images going to help ? What do you mean ?
[1] If you have a very private document (whatever it is) you want to protect, and you put it in your safe, you definitely have a lock on the safe (and if not, why bother, at least for security?). Even then, you should also have the building the safe is in, locked/secured, too. You could suggest that the lock on the safe is an account password but in order to get a password prompt you have to reach the system itself (and there might be a different kind of lock protecting the system).
Apparently what some terrorists are now doing, is opening email accounts, drafting new emails with instructions for counterparts to follow or information they want relayed and then just leaving the email in the draft folder. Then the terrorist's counterpart logs in, sees the message in the draft folder and deletes it. There's never any sending of the message or significant log of the activity.
I wonder if using the same approach to store a few loose passwords might be better than actually sending them to yourself or others.
This is an old technique used by much more than crime. A more recent example: a certain US official did this and as a result, it was discovered he was having an affair (and they weren't exactly the first to use this technique; yes, some might call affairs criminal, but that's besides my point). The bottom line is it isn't all that special and it isn't all that safe. It isn't all that clever, either. In fact, by sharing passwords, you have a problem already. And if you're using this to also share other passwords, you're not better off: you're not only sharing passwords to obtain other passwords (MiTM attack ? Then you leak the more important passwords to another party; that's one example of many[1]), you're also sharing the passwords to the other accounts (whatever they might be). In the end, this is a terrible idea. The reason it is a terrible idea is it is still sharing passwords; sharing passwords is not a good idea no matter what reason. The more people logging in to the same account, the less you can keep track of who did what when (and the more people in the group, the more that are able to give too much information out, deliberately or accidentally, therefore exposing the entire operation), and that is a problem as well (there's a reason log files exist, after all).
[1] And you're also storing the passwords in a potentially unsafe manner, which is another problem as well.