
Security researchers have released a free new tool that they claim can help protect users against known and possible future versions of the Locky, Teslacrypt, and CTB-Locker ransomware.
This announcement marks the expansion of a Windows tool that anti-malware firm Bitdefender first made available in the beginning of 2015. That utility protected only against CryptoWall, another infamous name from the world of crypto-ransomware.
As we have seen in recent weeks, however, new ransomware samples and campaigns are cropping up every day.
The Locky ransomware first appeared on the scene in February when it was identified as the malware that shuttered the computer systems of Hollywood Presbyterian Medical Center in southern California. The hospital ultimately paid a ransom fee of $17,000 to have its computer systems restored.

In the meantime, attackers continue to infect targets with other malicious samples, with some even going so far as to hack a hospital’s website in order to disseminate Tesclacrypt ransomware.
For those who are exposed to crypto-ransomware, there’s little hope that they will get their files back unless they have a secure backup of their data or are prepared to pay the ransom.
Sure, researchers sometimes leverage flaws in the malware code to publish decryption keys or to create a downloadable decryption tool. But that is not the case for all ransomware, especially those samples that have few coding and cryptographic errors.
That is where Bitdefender’s new tool comes in, according to the firm’s Chief Security Strategist Catalin Cosoi:
“The new tool is an outgrowth of the Cryptowall vaccine program, in a way. We had been looking at ways to prevent this ransomware from encrypting files even on computers that were not protected by Bitdefender antivirus and we realized we could extend the idea.”
This utility, which can be downloaded here, marks just one of several efforts to help protect users against crypto-ransomware infections before they happen.
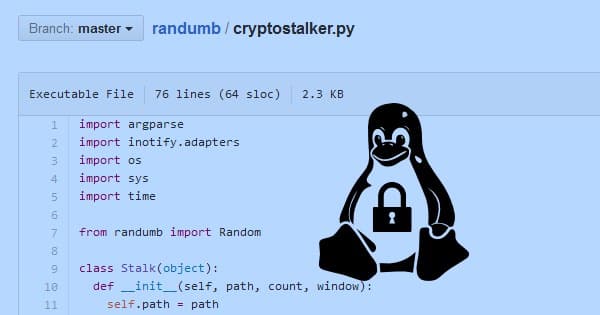
Earlier in March, the world first learned of Cryptostalker, a tool that might be able to help monitor a computer’s file system for newly written files as well as random data – a tell-tale sign of encryption – stored therein.
It’s important to note, however, that Cryptostalker and Bitdefender’s tool have their limits in that they should ideally complement, not replace, best security practices. Bogdan Botezatu, a senior threat analyst at Bitdefender, underlined that point in an interview with PC World:
“While extremely effective, the anti-ransomware vaccine was designed as a complementary layer of defense for end-users who don’t run a security solution or who would like to complement their security solution with an anti-ransomware feature.”
With that in mind, users should continue to avoid suspicious links, keep an up-to-date anti-virus solution installed on their machine, run regular backups, and implement software updates regardless of whether they choose to install Bitdefender’s utility.



There is tool out there that does this for years now
http://www.surfright.nl/en/alert
The Cryptoguard modules kicks all lockers signature less.
I believed Surfright/HitmanPro Alert was able to defend against all lockers until I viewed this video: https://www.youtube.com/watch?v=nsacrHzUYrY
No. It is a constant game of cat-and-mouse. Do not fool yourself into believing software (or hardware) will fix all your problems. It won't. Even layered defences (which is the best way) will not always succeed (depends on many things amongst them: your end, bugs in software, mistakes you make, other circumstances as well as the attacker [and how determined they are]). It might seem to at some points but you're playing a dangerous game (and if you believe you're 100% safe then how will you know when you've been proven wrong?).
you have hit center of the target .. safety begins at start up and where each connection is and what sites are visited and control of the cookies is helpful . never respond to spam . a mixture of free and paid for software along with a 47 character password .. running virtual machine and four forms of safe storage of back ups.two are off site
I think AntiRansom http://www.security-projects.com/?Anti_Ransom is much better and it's previous