A new crypto-ransomware called “Bart” denies victims access to their files without the use of command-and-control (C&C) infrastructure or AES encryption.
Researchers at security firm ProofPoint explain that they first came across the ransomware at the end of last week:
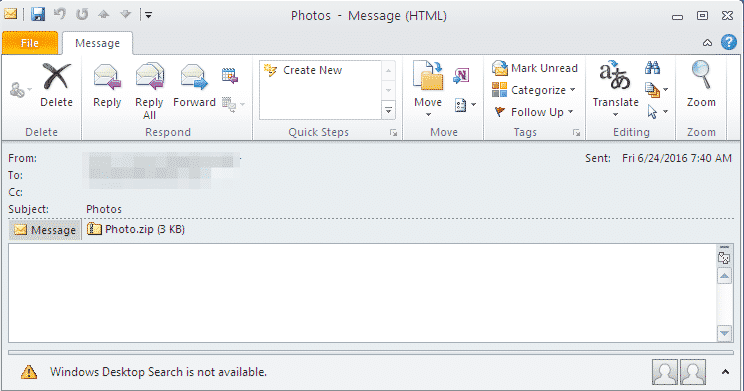
On June 24, Proofpoint researchers detected a large campaign with .zip attachments containing JavaScript code. If opened, these attachments download and install the intermediary loader RockLoader (previously discovered by Proofpoint and used with Locky), which in turn downloads the new ransomware called ‘Bart’.
The messages in this campaign had the subjects “Photos” with the attachment photos.zip, image.zip, Photos.zip, photo.zip, Photo.zip, or picture.zip. The zip files contained JavaScript file such as PDF_123456789.js.
The Locky ransomware has made quite a name for itself since it was discovered back in February.
Attackers used the Locky ransomware to target the Hollywood Presbyterian Medical Center in early spring 2016. Ultimately, the hospital conceded to the attackers’ demands and agreed to a ransom payment of 40 BTC (approximately US $17,000).
Since then, Locky impersonators and dark web marketplaces claiming to sell variants of this ransomware have been popping up online. Researchers have also been working hard to stem the tide of Locky infections.
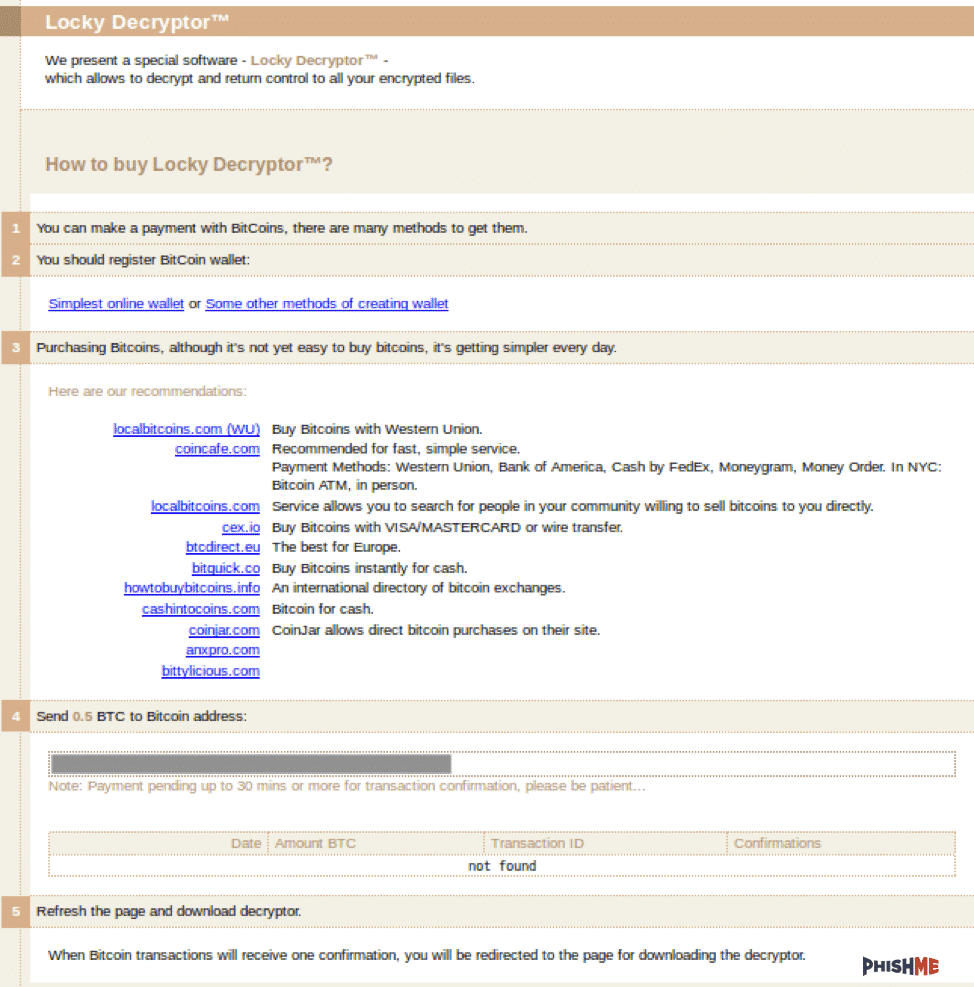
Locky appears to have had a profound impact on Bart. Take a look at this newest ransomware’s payment portal:
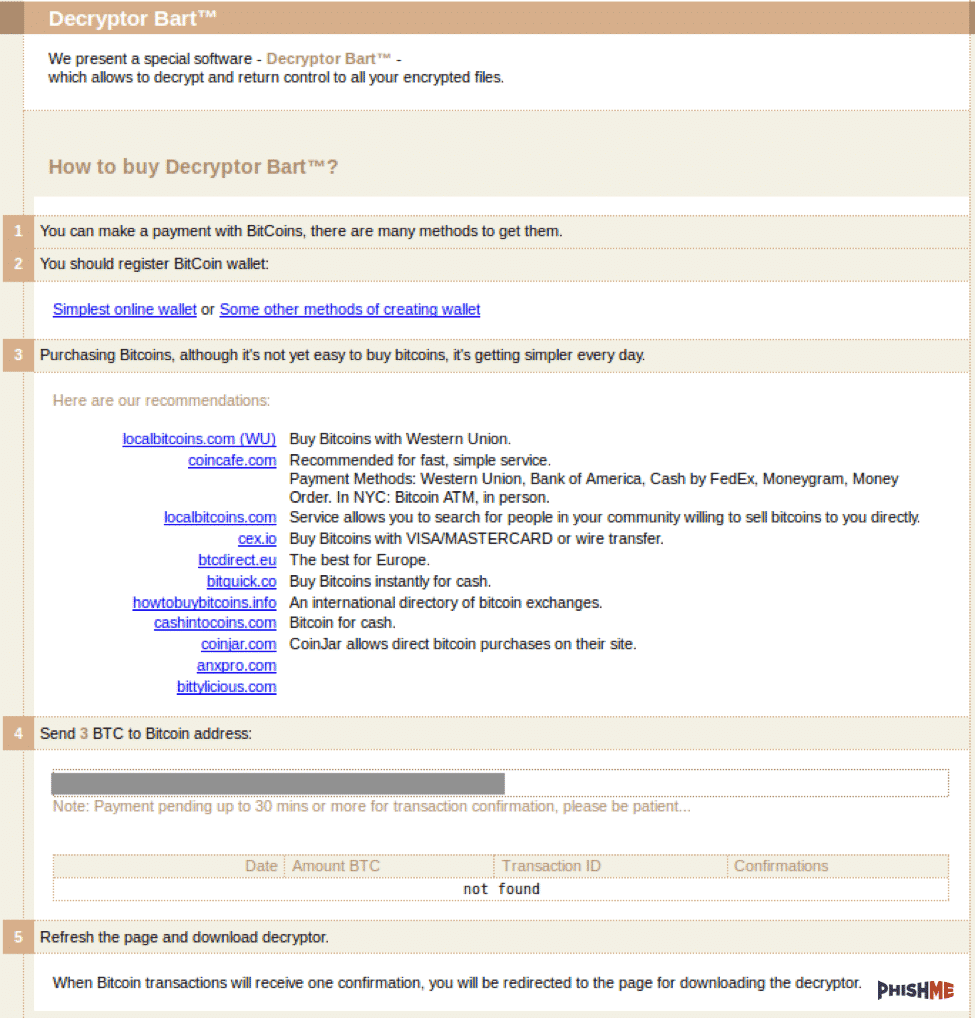
It’s exactly the same as Locky’s except for the fact that it asks for 3 Bitcoin (approximately US $1,800) instead of the 0.5 BTC demanded by Locky:
Rest assured, however, that Bart isn’t a Locky copy. This new ransomware distinguishes itself from most other ransomware in two ways when it comes to its encryption algorithm.
First, the ransomware doesn’t have any C&C infrastructure. Instead it uses a victim identifier to tell the threat actor what decryption key they should use to create a decryption application.
Second, Bart doesn’t deny victims access to their files in the same way as other crypto-ransomware. Researchers at PhishMe explain:
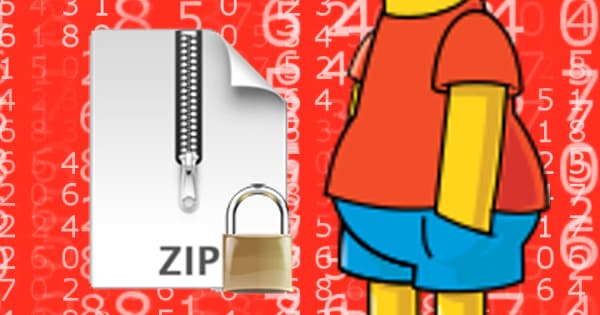
“Most encryption ransomware has traditionally relied upon a sophisticated asymmetric, public-private key pair or the creation of a distinct symmetric encryption key for encryption. This key is generally passed to the threat actor’s infrastructure at the time of encryption for later use. However, Bart simply places its targeted files in individual zip archives and applies password protection to these archives.”
#Bart #ransomware encrypts files by packing in password protected ZIP archive pic.twitter.com/odg8KhXgpD
— hasherezade (@hasherezade) June 25, 2016
At this time, there is no decryptor available for victims affected by Bart. That means users need to follow best ransomware prevention practices, such as by exercising caution around suspicious links and email attachments. They should also back up their files just in case.
In addition, organizations could block Bart at the email gateway by setting rules that automatically filter out emails with zipped executables.