Ransomware with apparent links to a Dridex botnet affiliate has been spotted attempting to infect at least 450,000 computer users.
Brandon Levene, Micah Yates, and Rob Downs, all security researchers for Palo Alto Networks, have provided some backstory on the malware, nicknamed “Locky,” in a blog post published on Tuesday:
“Using Palo Alto Networks AutoFocus, Unit 42 observed over 400,000 individual sessions containing the Bartallex macro downloader, which in turned dropped Locky ransomware onto victim machines. Researchers suspect there is a link between the Dridex botnet affiliate 220 and Locky due to similar styles of distribution, overlapping filenames, and an absence of campaigns from this particularly aggressive affiliate coinciding with the initial emergence of Locky.”
A commonly-encountered banking trojan, Dridex was thought to have been at least partially taken out in October of last year. However, researchers spotted the malware earlier this year targeting several UK banks.
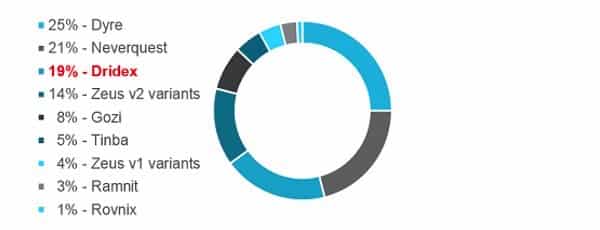
It would now appear those operating the Dridex botnet affiliate have decided that ransomware is a more lucrative payload than a regular trojan.
The Locky infection process begins with a fake financial spam email that comes with a malicious Microsoft Word document attached, such as this one described on Dynamoo’s blog:
From: June Rojas <[email-obfuscate email=”” linkable=”0″]>
Date: 16 February 2016 at 09:34
Subject: ATTN: Invoice J-06593788Dear nhardy,
Please see the attached invoice (Microsoft Word Document) and remit payment according to the terms listed at the bottom of the invoice.
Let us know if you have any questions.
We greatly appreciate your business!
June Rojas
Apache Corporation
www[dot]apachecorp[dot]com
If the user opens the attachment and enables macros, embedded code will execute the malware on the machine.
It is interesting to note that there is a chance to stop the encryption process. Unlike other ransomware, which generate a random encryption key locally, Locky performs a key exchange in memory via its command and control (C&C) infrastructure. If a user were therefore able to disrupt the C&C communication, such as by disconnecting from the web, they could stop the encryption process in its tracks.
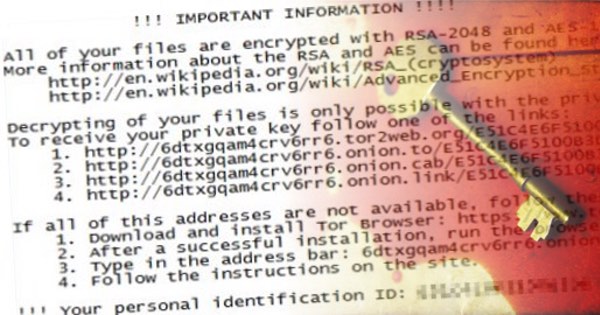
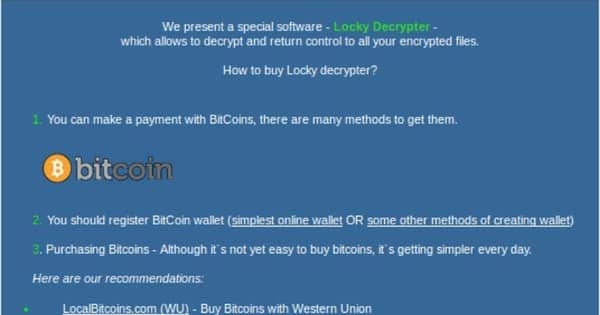
If the communication proceeds uninterrupted, however, a ransom screen loads on the computer and redirects the user to the payment portal page:
By this time, the ransomware has encrypted all documents, including those on connected network drives, as hash.locky files and has deleted all VSS snapshots.
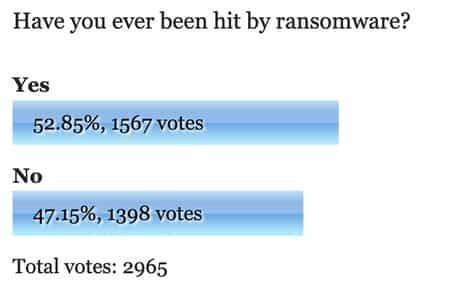
Most of the 446,000 individual infection sessions observed by Palo Alto Networks occurred in the United States.
Assuming a 50% infection rate and a one percent payment rate of 0.5 BTC, the attackers can expect to net several hundreds of thousands of dollars via the ransomware.

The research team at Palo Alto Networks believes that the developers of the Locky ransomware have lofty aspirations:
“Locky is aiming high in an effort to join the ranks of other big name ransomware families. Despite some weaknesses in its current implementation, we can expect to see further developments for this threat in the future. Ultimately, successes experienced by one attacker group embolden and inspire others. It goes without saying that cybercrime adversaries will continue to advance efforts to commoditize the already lucrative extortion of victims through encryption-based extortion.”
With this in mind, it is important that users back up their data frequently, do not enable macros on Word email attachments, and patch the software running on their computers as soon as possible.
For more advice on how you can stay protected against Locky and other forms of ransomware, read the report on Sophos’s Naked Security site.



Thanks for posting this. I received two suspicious emails which looked like these a few days ago (I'm in Mexico). The first one almost got me because it showed up right after receiving a legitimate invoice from a trusted retailer. I looked at the preloaded message in Thunderbird but didn't open it and deleted it right away. It happened again the same day. This time my virus protection software set off an alarm. Like the first message, I deleted it immediately without opening it. Thank God I didn't. As it is, I have CryptoBlock on my computer, but it might not have been enough.
'With this in mind, it is important that users back up their data frequently'
Daily (or if you can nightly). That's at minimum. But those who don't backup usually have a reason to do so and not much will change their mind – especially not by being told they should. Yet they definitely should (as everyone). I grant you that some might not have their computer on every day and I grant you that some uses might be so limited that you could get by without doing it on a daily basis but you better make 100% sure that you aren't missing something and while you're at it you should verify that your 100% is truly 100%. And something includes 'backup recovery' because a backup that doesn't work (corrupted backup and device failure included) isn't a backup, is it?
We were attacked tuesday by this ransomware. 150 Emails spoofed to our mailserver. 149 Mails were blocked by the Barracuda spamfilter. One slipped through and was initialised by a coworker from the saledepartment. In half an hour our fileserver, applicationserver and shared maps on local PC's was encrypted.
After locating the PC where it all started, we took that one from the network and started to restore everything from the backup. In one hour the fileserver and applicationserver was back working.
Except one local folder with lots of data in that wasn't on the fileserver was completely destroyed. We succeeded in fixing this as follows.
First we installed RECUVA on this PC and tried to recover the lost map.The fact that the user kept working on it, had as result that most files were'nt recoverable because they were overwritten by cookies and temporary internetfiles. (So when noticing the LOCKY files … stop working)
Windows 7 has shadow files. Too bad those files are corrupt because of the LOCKY virus … but … we were able to recover those files with RECUVA, restore them and start SHADOWEXPLORER and go back 6 days to recover a shadowcopy from the lost data folder. In the end we recovered about 99% of lost files !
But as someone said before …. nothing helps to prevent it so backup, backup and backup …..
Could you detail how you recovered the shadow copy ? As far as i know, Locky deletes all shadow copies after encryption.
Hi Peter pls help me it's urgent. all my files become .locky. I download RECUVA but i don't know which will be the name of befores shadows copies and SHADOWEXPLORER only show me today shadow copy. how i will recover shadow copy , which will be names of shadows copies?
I'm curious. Would running the email inside of Sandboxie, and the document reader, have prevented the infection? How about in a sandboxed virtual machine?
Hi Peter,
We are attacked by LOCKY virus on 25 th feb,,.,we are lost our data. How can i recover my data, i sea your post.,.,I need your help right now.,.please help me. As a human being i want help.,,.
Regards,
Raja Mohan Reddy
Strangely all files on my backup drive has a word _LAST (e.g read.txt_LAST, songname.mp3_LAST) What does this mean? Is this a virus or something else? I am using Western Digital passport to backup. Any help would be highly appreciated.
Sir, the "_LAST" extension is what the backup software uses to designate that whatever the file is, is the last (most recent) copy of the file. When it does it's backup procedure, it looks at the date and time of the files on your pc and compares them with the ones already in the backup file. If the file on your computer has the same time and date then it does not have to bother backing it up again and saves time and number of writes to the backup drive. It just means that it is a backup copy. If it has to be restored back to your pc, then the Western Digital software will strip away the "_LAST" from the file so it will be exactly as it was before it was backed up.
Ok, I am not computer literate at all. All of this is so confusing. I stupidly opened an e-mail attachment and have this virus. Now, if I ignore paying the ransom (which I will) is my computer unusable? Will I eventually have to just break down and buy another PC? Does this virus take my log in and cc info? Anybody know? Thanks.
Hi Tammi,
I highly advise against continuing to use a computer when you know there is malware installed on it. I have not seen anything about Locky coming with a keylogger functionality by which it can take your login and CC information, but malware is continuously evolving, so this could very well become a feature at some point in the future. If you have backups of your files, I would recommend you take your computer to an expert who can remove the malware for you, at which point in time you can restore your files without paying the ransom. If you don't have backups, there is unfortunately no way to regain access to your files without paying the fee.
Best,
David
Thanks David. I got my computer "fixed" but it's been 24 hours and the message popped up again a few moments ago. Should I just cut my losses and get an entirely new laptop? All of this stuff is like speaking Japanese to me. I don't know what's going on. I've been to two professionals and I still have this message popped on my screen. If I do get a new computer will I have to get another source of wifi connection? Sorry if this sounds stupid I just don't understand this stuff.
Hi Tammi, It's important to be mindful of what sites you visit to avoid re-infection. With that being said, the computer "professionals" who looked at your computer might have missed some of the malware's files, leaving the ransomware installed on your computer. I would therefore recommend that you follow this guide here: https://www.pcrisk.com/removal-guides/9807-locky-ransomware. For incomplete yet added protection, it's a good idea to keep an anti-virus solution such as MalwareBytes installed on your computer at all times. I hope that helps!
There's never a stupid question. The ransomware has infected only your computer. Your WiFi connection is fine. Just make sure you don't plug anything like a hard drive or USB into your computer. Doing so won't affect the WiFi connection, but it could very well spread the ransomware to those devices.
You're the best. Thank you so much.
Going to pay ransom but didn't even give me an amount there is just an error message. Went via tor still just say send bitcoin to the weird bitcoin address but the amount they want is "not found". So there is no hope of ever getting my files back.
You shouldn't pay to remove a Ransomware as that makes you a future target and it also promotes the business of hackers, try out removing the virus with MalwareFox and recover your files with a data restoration program.
As known recently most of users have been infected by TESLACRYPT Virus which changes all important documents like pdf,doc,xls,mp3,mp4,mpeg,avi,etc to .vvv, .ecc, .ezz, .exx, .xyz, .zzz, .aaa, .abc, .ccc, .xxx, .ttt, .micro, mp3 and "no extension change on last version" are encrypted and not usable/readable unfortunately. I can help infected users to decrypt their files, you can contact with me with below email address if you or one of your friend had been infected this kind of virus. Also there is paid solution for .encrypted extensions, please write me if you are interested.
Email: