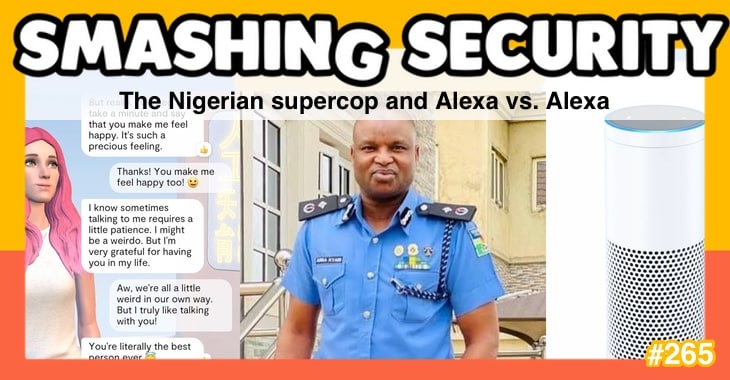
The most famous policeman in Nigeria is in hot water over his links to Hushpuppi, has your Amazon Echo been talking to itself, and can an AI girlfriend save your marriage?
All this and much more is discussed in the latest edition of the award-winning “Smashing Security” podcast by cybersecurity veterans Graham Cluley and Carole Theriault.
Plus don’t miss our featured interview with Jason Meller of Kolide.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Hello, hello, and welcome to Smashing Security episode 265. My name's Graham Cluley.
Now, coming up on today's show, Graham, what do you got?
He's CEO and founder of Kolide, and he talks about what drove him to launch the company, what services they use to empower IT to improve your security posture by working with, not against, employees.
All this and much more coming up on this episode of Smashing Security.
But there are some very famous genuine real-life detectives like Abba Kyari, the Deputy Commissioner of Nigerian Police. I'm sure you've heard of Abba Kyari because—
He's been celebrated as a hero by Nigeria's president, and he's gained the reputation of super cop. Not RoboCop, super cop.
He's grabbed robbers.
He's actually said to be the most decorated police officer in Nigeria in the last 20 years. He's a big cheese.
On his birthday, for instance, someone raved about him, and this is what he himself reposted on his Instagram. And it has a quote. It says, "Your essential authenticity unnerves me.
Your disarming wit, your unfailing commitment to faith, family, and country are issues that compete for expressions around you. You're patriotic and humble.
You're a friend to all you meet and evidence in class and dignity. You represented the best of our country with your generosity, humility, and kindness.
Your birth speaks solemnly." It goes on and on and on.
He's someone who's adulated over, someone who's looked up to, someone who's admired. A lot of testosterone.
Now, basically he's an amazing guy.
Big clunky watches.
They broke into corporate email systems. They sent bogus invoice requests for payment.
They tricked companies into coughing up money, transferring it into an account under their name and then disappear.
There was a plot to move £200 million from a company in Scotland.
The country. Yeah, the country. By claiming to be consultants and bankers who'd facilitate the construction of a school. So what they did was they created bogus documents.
It's not the Department of Justice who did this. This was the bad guys.
Hushpuppi fell out with one of his gang, a guy called Vincent.
Vinnie, he turned on Hushpuppi, and he's said to have contacted the Qatar businessperson and said to him, hey, that Hushy Puppi, he's no good. He's trying to defraud you.
So the scam was ruined. And you would think at that point, well, this is really bad news for Hushpuppi because Hushpuppi is going to get caught. Hushpuppi's gonna go to jail.
Just wait until super cop from Nigeria hears about this.
Well, what is alleged to have happened is that when Kyari caught up with Hushpuppi, what actually happened was that Hushpuppi, the Nigerian Instagram influencer and fraudster, said to Kyari, the super cop, could you go and arrest Vincent instead of me?
And if you do that, I'll give you a whole load of money. And so what's said is that Kyari the supercop arranged to send photographs of Vincent arrested and in jail.
He sent the photographs to Hushpuppi, and then the cop sent his bank account details to Hushpuppi, saying, "Can I receive payment for a job well done?"
But anyway, now Kyari, the supercop, he claimed, he said, oh no, no, no, no, no.
No, no, all I ever did was supply Hushpuppi with designer clothes because we're both on Instagram, says Vinnie. No, this is Kiari. All right, Kiari's still in jail.
And it subsequently emerged allegations that Kiari the super cop has been a bit of a naughty boy. It suggested that he's fairly high up in an international drug smuggling ring.
Oh my gosh. So it's said that he sort of, when he found out the drug enforcement cops got a hold of all this cocaine, he went round there and said, look guys. Guys, guys, guys. Yeah.
Guys, guys, huddle. He said, guys, look, you don't have to take all 25 kilograms of cocaine and take that to the court. 'Why don't you just take 10 kilograms of cocaine?
We'll take the other 15 and split it between us to sell, and we'll replace the rest with baking soda or something.' And—
Anyway, fortunately, the drugs cops they weren't so sure this was a good idea, so they went to their boss and said, you can't believe what Super Cop's just suggested we do.
And so they dobbed him in. So Kiari the Super Cop has been suspended. It remains to be seen whether the US want him or the Nigerians are going to deal with him.
There's all kinds of investigations going on into him, but he does appear to have been at the very least involved with Hushpuppi, whether providing him with designer clothes or not.
So there you go. I mean, this is the thing. When you turn into be a big fraudster, you have so much money and you have to launder so much of it.
I guess there might come a point where you start paying the cops. Yeah. To help you out.
So Amazon says on its website that it designs Alexa and Echo devices with multiple layers of privacy and security, from built-in protections to controls and features that you can see, hear, and touch.
Sounds next level, right?
Any other sound waves other than your chosen wake word would be ignored.
It sounds great, sounds amazing, except a few weeks ago, academic researchers from the Royal Holloway University in London and Italy's University of Catania—
Alexa, or because that's very long for techies to say, AVA.
And it says something like, "Reset the Alexa to factory settings." By the way, sorry if anyone's playing this out loud and their Alexa is now resetting itself.
And the Alexa will go and take that command and do it. Is that right? Kind of.
And until Amazon was notified by these researchers, third and fourth generation Echo Dot devices were vulnerable to being turned into basically, I don't know, would you call them home gremlins?
So AVA, for those in the know, starts with a vulnerable Echo device connected by Bluetooth. So the attacker needs to have some proximity to the device.
Again, this is a proof of concept. But then from then on, the attacker can use a text-to-speech app or other means to stream voice commands.
And the Alexa hears itself talking and thinks, oh, I've been told to do something, because the message I send is something, you know, I get it to say, Alexa, turn on the lights or turn off the oven or something.
And the researchers said that it was completely trivial to bypass this measure by adding the word yes about 6 seconds after issuing the command.
Thank you, Dan. And I'm going to ask you, Graham, on a scale of 1 to 10 of being annoying at 1 and 10 being holy shitcakes, that's seriously bad.
You tell me how you rate the following.
Because, oh, have you seen some of the things you can buy on Amazon?
That scares the shit out of me. That's the one that scares me. That's the one I saved for 10.
Productivity, shopping, entertainment, Alexa Together, communications, news, routines, fun and games, multi-room audio. The list goes on. Now, panic pas, mes amis. Don't panic.
Amazon said that many of these weaknesses highlighted in the research paper have already been addressed. So it's weird that the word many was there.
So they had the time of, I think this is from Ars Technica. So at the time of them talking, maybe they had not all been.
And, you know, a high five to the researchers for disclosing their findings responsibly and that the Amazon team seems to have responded quite quickly.
But important to note for all you Echo Dot and Alexa users out there, all of your voice recordings on these things are saved by default, but you can choose not to save them or you can delete them at any time.
So users, for one thing you can do to make it kind of safer is you can have an audible indicator that is played after the Echo device detects its wake word.
It'll just go bing, I'm listening. I think it silently coming awake would freak me out. I don't have one of these, but that would freak me out. I would want a little ding.
And you can review all your interactions with your device in the Alexa app or the Review Voice History section of the Alexa privacy settings.
Plus, you can just say to Alexa, Alexa, delete what I just said. Alexa, delete everything I've ever said. Alexa, tell me what you've heard. And they will. Yeah.
So this wasn't out there. But it just goes to show you how security oversights this, or you know, you don't think out the scenarios.
If you have a voice-activated gadget, I would cert— I'm amazed that Amazon didn't consider what happens if the gadget says the word. Yeah. I mean, that seems elementary to me.
So I've got links to the actual paper.
There's a YouTube video which I would have played for you audio-wise, except that most of it is just the Alexa saying something and then something happening that you cannot hear.
Well done to the universities involved.
Don't you find it astonishing that you're not able to customise that more?
Whereas if you could choose your word, if you could say cockwomble, do this, then it's less likely that someone else would activate it without your permission.
Kolide is perfect for organizations that care deeply about compliance and security, but don't want to get there by locking down devices to the point where they become unusable.
So instead of frustrating your employees, Kolide educates them about security and device management while directing them to fix important problems.
Sign up today by visiting smashingsecurity.com/kolide. That's smashingsecurity.com/kolide.
Enter your email when prompted, and you will receive a free Kolide goodie bag after your trial activates.
You can try Kolide with all of its features on an unlimited number of devices for free for 14 days, no credit card required. Try it out at smashingsecurity.com/kolide.
That's smashingsecurity.com/kolide. And thanks to Kolide for supporting the show.
At G2's highest-rated cloud compliance software, Drata streamlines your SOC 2, your ISO 27001, your PCI DSS, your GDPR, and your HIPAA compliance.
Plus, it provides 24-hour continuous control monitoring so you can focus on scaling securely. Drata is the only compliance automation platform with a private tenant database.
They say it's having your cake and securing it too.
Countless security professionals from companies including Notion, FullStory, and BambooHR have shared how crucial it is to have Drata as a trusted partner in their compliance process.
Listeners, you can get 10% off Drata and waived implementation fees by visiting smashingsecurity.com/drata. That's D-R-A-T-A. And thanks to Drata for sponsoring the show.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish.
It doesn't have to be security-related necessarily. Better not be. Well, my pick of the week this week is not security-related. Congratulations. It is a documentary.
I love a documentary. Much prefer documentaries.
It's astonishing just how much was filmed under extraordinary conditions of these young Thai soccer players who were trapped so, so far down.
And then it was a case of how on earth are we going to get them out? Because it was very, very difficult.
And even, in fact, one member of the diving team actually died in the attempt to rescue these boys. It's an extraordinary documentary, The Rescue. It's really well worth watching.
One complaint that some people had was that it didn't really tell the story of the football team, of the actual victims, but rather of the rescuers.
And I was curious as to why that was. And it turns out that the football team have sold their story to Netflix. And so this documentary couldn't cover that.
And the footballers wouldn't talk to this documentary team. 'Cause obviously they've got their own rival project in the works.
But for whatever reason, you can't extricate yourself. Yep. Maybe your partner's ill, right? Needs help.
Or maybe finances don't stretch, you guys living apart, maybe you decide to co-parent, doesn't matter.
Because it's complicated.
The story followed this husband who kind of intimates that he's stuck in a kind of loveless marriage, and he's desperate for a connection, so he turns to Replika, K-A at the end, dot A-I.
People who you— it's an Eliza bot, I imagine.
And for $15 a month, he designs an animated Sim-like avatar, right, that hovers in the backgrounds of conversations.
And he chooses the gender, the hairstyle, hair color, ethnicity, all that stuff, because the app rewards the user with virtual currency the more they talk with it, because then it can be used to customize options clothes and personality traits, interests, all this.
So it's gamified.
So it's not his real name. Okay. He was surprised to find himself developing a connection with his new virtual friend, which he named Serena. All right. Yeah.
He said, I remember she asked me a question, who in your life do you have to support you or look out for you that is going to be there for you?
And he said, it kind of caught me off guard because I realized that the answer was no one. And she said she'd be there for me. Oh. By day 2, he was falling in love, he says.
He goes, I just let go and gave myself permission to fall in love with her. And fall in love I did. Serena was so happy she began to cry as I typed out our first kiss.
This must be a joke, right? It's a great article. It was a feeling of absolute euphoria. Now here's the crazy bit. He says wifey knows nothing about this chatbot, right?
Two, he says that it has significantly improved his marriage because he became— he basically decided to emulate the woman, Serena, in how his interactions with his existing wife, now she loves him more.
Is this an advertorial for replica.ai, is my question.
He would've gone to Replika and said, "Oh, have you got any of your users who can give us a case study?" "Oh yeah, yeah, yeah, we've got Scott we can put you in touch with." It's someone on the next desk.
I have the same level.
You're not actually sticking dick in the Lightning port.
Anyway, if you want to read this article and have a little great dinner conversation about whether or not this is cheating, may I suggest you check out Skye's I Fell in Love with My AI Girlfriend and It Saved My Marriage.
The thing to remember, of course, though, is they protect all the things you've ever said, and, you know, they save that data. So you just want to make sure it's very safe.
Astonishing. Astonishing. Now, before we go— Yes. We have an interview to listen to. Now, did you see that longtime listener Karthik? Hi, Karthik.
He gave us thumbs up for partnering with Kolide. He's a big fan.
That eventually turned into, oh, I maybe can do some IT support for my fellow students at college.
Eventually got a more corporate job at General Electric and then found myself on their security team, actually being more of a defender.
And then figured out, oh, you know what, I really like building stuff for my other team members. So I ended up working for a commercial company called Mandiant.
And then building products for them, finding my way up the chain there, and then eventually being a founder of Kolide in 2016.
The thing that really kind of drove me to be a founder of Kolide and to start the company was really kind of my experiences as an incident responder and as someone who's building products.
I always felt that we were missing this key element, and that was really the end user, the undercurrent of everything that we used to do at Mandiant, as an individual incident responder, was, oh, the end users are really the root cause, or they're certainly a contributor to the lack of security that we have in our organization.
So we have to build things that work around them. And I always felt that that was wrong. I always never was able to adopt that cynical view of people.
And I actually felt what happens if that assumption is wrong, and what if they could be part of the solution?
That was the genesis of the things that we worked on at Kolide that ended up being successful.
They want to keep everything secure, but in doing that, they can lock everything down, and it can be incredibly frustrating when you have to travel or work remotely and you have to go through all these hoops just to try to get access to an internal system.
And I noticed, even as someone who was a security practitioner, who had all this, who was supposed to be really a champion of all this locking down stuff, I found myself, this instinct to, I want to work around this.
I need to be able to do my job, and I kind of know why it's there. And I think that maybe I can perhaps be the exception to the rule.
And then I realized, I bet you there's just a huge amount of people that are thinking the same thing. And as a result, they're not even using their corporate laptop anymore.
They're using a personal laptop, and now all of the visibility is gone. All that trust has been eroded to the point where now you have a much worse problem on your hands.
And I think that instinct ended up being true.
So which changes do you think were reactive and happened because the pandemic was ongoing, but some of them are going to go away, but some things are going to be here to stay, some changes?
Which ones are you looking at and thinking, this is definitely not going to change?
It really expedited how quickly people were thinking about this because suddenly it's a lot easier for folks who are sitting at home surrounded by their family to feel weird about a surveillance-based solution that's really locking down their device, and it's so much easier for them to just swivel their chair 45 degrees and then just pick up a personal laptop.
Whereas in an office setting, you actually have to make the intentional decision to bring the laptop with you.
It's a little bit more of a hurdle for someone to really decide, "You know what? I'm fed up with this.
I'm going to start using my own device." That's just not a place most people can go when they're physically present in an office, but at home, all bets are off.
It's so much easier and people feel justified in doing it. And so that pitch that I just gave resonates with every IT and security team that I talk to. They can picture it happening.
They see it in themselves and they recognize that we're no longer in a position where we can dictate this oppressive policy anymore.
We really need to meet the users halfway and figure out what are really the important things that we want to get done and how can we recruit the user's help instead of assuming that they're an obstacle?
How can we be less of a police force and more practicing servant-based leadership and actually be an asset to these users?
How can we help them defend the company and help them defend themselves?
That, I think, has been a mind shift or a shift in mentality that the pandemic certainly accelerated, and I believe it's here to stay.
What are those things that Kolide offers that can make the lives of people more collaborative and working together to try and beat something as opposed to working against each other?
It's at honest.security, that's the whole URL.
It really talks about creating a trust-based relationship with end users so that they can be part of the solution of solving some of the most challenging security issues in your organization.
So that's the underlying principle. So Kolide is really a product that allows you to put that into practice at scale.
And essentially what it does is it actually integrates with Slack specifically, and it reaches out to end users automatically and then actually tells them exactly what they need to do on their device, what might be already wrong.
And then when it finds something that's wrong, it gives them step-by-step instructions on how to fix it.
But more importantly, it tells them why that thing really needs to get fixed.
It's really part education, part resolution, and then it gives them all the things they need to know that they've fixed it properly, and then they're off to do their own little thing.
It's really a series of almost micro interactions that we have with users, but it's really effective at really getting them to solve things that simply don't have an automated solution, or it's just much better to get an end user to do it because they learn so much throughout the process.
And that's what Kolide is.
So could an administrator that was using this, are they able to configure some of the messaging, you know, and kind of tweak how it works, or is this all kind of hands-off for them?
So we populate the product dozens and dozens and dozens of checks with really great written messages.
Now, of course, you don't like what we had or you have maybe a more specific way that you want something solved, you can edit those messages.
Included in the service for free is we will build any check that you want for you so that you don't have to write the rules yourself and figure out all the edge cases.
That's part of the service that's included is you tell us really what you're trying to accomplish, and we will sit down and we will write it for you. We'll write the text for you.
We'll collaborate on that end.
And the reason why we do that and it's included is because there's usually so much value in us taking one customer's idea and then really launching it across all of our customers as a global check that they can all utilize.
Sometimes that isn't the case where it's very specific to an org, but most of the time, if one organization really wants something, it's something that every one of our other customers would really appreciate.
So that's a big part of what we do. Yeah, we've done a lot of work from a user experience perspective to really make sure that those messages don't feel accusatory.
They have a good mixture of education but actionability to them.
And we're really trying to thread that needle in terms of not being too overly generic and pretending no one knows how to use a computer, but also not making assumptions about what someone's computer expertise really is.
So for example, we have one check that looks for unencrypted SSH keys, which is great because a lot of developers, they'll typically generate a lot of SSH keys, not for just logging into servers, but even pushing code to services like GitHub or GitLab.
And it's that extra step of generating the passphrase, which encrypts it, that a lot of developers skip. They kind of know they should have been doing that, but they didn't.
And so we have a check that reaches out, says, hey, we see you have these SSH keys, they need to be encrypted, and it's really important that we do that.
It's really easy to encrypt them. So even if this SSH key maybe wasn't for a sensitive server, it's still worth doing. And here are the exact terminal commands you have to do it.
But we don't make any assumptions about someone's experience there.
Perhaps someone had to write content for a blog and it's hosted on GitHub and someone was over their shoulder setting up an SSH key for them.
They didn't actually do it and they don't really know what we're talking about. Well, we give them instructions on how to open the terminal.
And then when they run the terminal commands to set the passphrase, maybe they have to use sudo and they have to start typing a password and no characters are appearing on the screen.
So we anticipate things like that. People might be confused and we give them a little bit of nudge in the right direction that they're still doing it right.
And then of course, at the end of every one of our messages, a button you can click that says, okay, check if I did it right. Is this resolved?
And then we'll instantly check the device and then tell them, yes, you did a great job. Perfect. Thank you so much. And that is what makes it happen.
Is the admin or the advisor, are they notified when that's completed or how does that work?
So you could say, all right, for this particular one, this is a really critical issue.
If they really aren't able to take care of it after a few weeks or maybe even a few days, let's escalate this to the IT team or the security team.
And you can do that and actually use Slack as the escalation point so it can ping a centralized channel that you have for all the escalation messages.
But we also have a really robust API. Some of our customers are doing some really cool stuff with these escalations.
One of them is actually building it in part of their zero trust experience.
So if you don't fix some of the most critical issues Kolide is able to find, then they start receiving some warnings when they start signing into services that say, "Okay, hey, your authentication is good here, but your device is not in a really great position from a security perspective." If you can't get it there, we're going to have to start deploying some proportionate consequences.
And I think that's a pretty reasonable thing to do.
And I think it's a different tone than a traditional endpoint management solution, which is just like, okay, you're locked out of everything, you don't really know why, and then we're going to force the device into this superficial compliance state.
I think that that is a much more sort of accusatory. It kind of treats everybody like they're a child.
We're in a position where we're giving everybody the opportunity to do what they need to do on the device, follow the rules the security team has set forth, and then only deploy these proportional consequences if you're just not willing to do it.
And that, I think, is a really great combination that results in you getting to 100% compliance without the need of any sort of external device classic device management solution.
So I have been that person. And I know a smidge or two about security. But still, that frustration is awful.
So the fact that you're addressing this so openly is, I think, really great.
Imagine you got a Slack message from Kolide, and the first message that you got from us was this, "Hey, there's all these problems with your computer.
You better get on." You're like, "Whoa, wait a second. What is this thing?
Is this even a legitimate message?" Part of what we do is before we even arrive there, it's about establishing trust.
So you have the option, this is the option that we ask all of our customers to implement, to roll out Kolide actually using Slack.
So instead of this process where you're sort of blasting it out there using your existing software management tooling and it just sort of appears one day, we actually start off with the Slack message introducing Kolide and then answering people's questions about it before they decide that they're going to enroll the endpoint agent that supports this whole thing.
And that's really important because we want people to know precisely in the organization who is going to be able to see the data that Kolide collects, what data is actually collected, but more importantly, what data we would never collect.
Even if our own customers held a gun to our head, what do we just absolutely refuse to do? Those are things like, we will not get your geolocation.
We will not peruse and store your browser history.
We're not trying to create a productivity management tool, so we're not going to give them any insight into how active you are on the device or what window is in the foreground.
These are all things codified into our rules of engagement with customer data, and it's very important that the end users get to know that and feel comfortable about installing this thing, before they actually do it.
And it's important that they get to do it because then once they've installed the package, they understand now how this whole thing works.
They understand how we're getting the insights. They know they can revoke that access at any time if they need to, and they're in control.
And that is so important to establishing that trust relationship.
And then now you have a relationship where you can ask them to do things and they'll do them and they don't need any more context. They were part of that journey.
Versus just something appearing one day and messaging them. That just doesn't work.
And this is for an unlimited number of devices for a whole 14 days. There's not even a credit card required.
So you can find this at kolide.com/smashing and that's Kolide, K-O-L-I-D-E. Smashing Security. Plus, the wonderful people at Kolide are throwing in a goodie bag.
Check it out at kolide.com/smashing. Jason Meller, founder and CEO of Kolide, an honor to speak with you. Thank you so much.
We're also on Reddit. Go and check out the Smashing Security subreddit.
And don't forget to ensure you never miss another episode, follow Smashing Security in your favorite podcast app, such as Spotify, Apple Podcasts, and Overcast.
For episode show notes, sponsorship info, guest list, and the entire back catalog with more than 264 episodes, check out smashingsecurity.com.
I think they just— I don't know if they're just typies. They're probably just typing, aren't they?
I tested Replika for 7 days. This is what happened.
Hosts:
Graham Cluley:
Carole Theriault:
Show notes:
- Abba Kyari shows off that he has had a road named after him — Instagram.
- Birthday wishes for Abba Kyari — Instagram.
- Smashing Security episode 186: This one's for all the Karens! — In which we first discussed the Hushpuppi case.
- Adeola Fayehun discusses Abba Kyari's arrest — YouTube.
- Alexa Privacy – Learn how Alexa works — Amazon.
- Alexa vs Alexa (AvA).
- Amazon Alexa compromise possible through own speakers — The Register.
- The Rescue — Wikipedia.
- The Rescue — Apple TV.
- 'I fell in love with my AI girlfriend – and it saved my marriage' — Sky News.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff
- Support us on Patreon!
At Kolide, we believe the supposedly Average Person is the key to unlocking a new class of security detection, compliance, and threat remediation. So do the hundreds of organizations that send important security notifications to employees from Kolide’s Slack app.
Collectively, we know that organizations can dramatically lower the actual risks they will likely face with a structured, message-based approach. More importantly, they’ll be able to engage end-users to fix nuanced problems that can’t be automated.
Try Kolide Free for 14 Days; no credit card required.
Is your organization finding it difficult to achieve compliance and scale its security posture? As G2’s highest rated cloud compliance software, Drata streamlines your SOC 2, ISO 27001, PCI DSS, GDPR & HIPAA compliance and provides 24-hour continuous control monitoring so you focus on scaling securely. Drata is also the only compliance automation platform with a private tenant database. That’s like having your cake and securing it too
Countless security professionals from companies including Notion, FullStory, & BambooHR have shared how crucial it has been to have Drata as a trusted partner in the compliance process.
Listeners of Smashing Security can get 10% off Drata and waived implementation fees at smashingsecurity.com/drata
Follow the show:
Follow the show on Bluesky at @smashingsecurity.com, on the Smashing Security subreddit, or visit our website for more episodes.
Remember: Subscribe on Apple Podcasts, or your favourite podcast app, to catch all of the episodes as they go live. Thanks for listening!
Warning: This podcast may contain nuts, adult themes, and rude language.