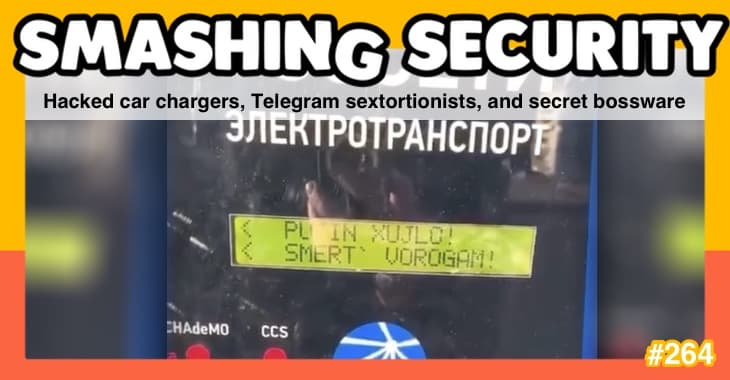
The cybercrime lovebirds who hijacked Washington DC’s CCTV cameras in the run-up to Donald Trump’s inauguration, the truffle-snuffling bankers at the centre of an insider-trading scandal, and the hackers that Uber paid hush money to hide a security breach.
All this and much more is discussed in the latest edition of the award-winning “Smashing Security” podcast by cybersecurity veterans Graham Cluley and Carole Theriault, joined this week by Lisa Forte.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Hello, hello, and welcome to Smashing Security episode 153. My name's Graham Cluley.
So I'm a partner at Red Goat Cybersecurity, and we specialize in security training and crisis simulations for crisis management teams and organizations where we simulate a cyberattack and then see how they handle it and the sorts of decisions they do or do not make.
And then I write a brutal report up on how well they did.
And just as I was setting up the company, I read this report in the New Scientist that was about some study done by UCL in London, and they'd recognized that goats can tell intruders to their herd just by hearing their voice.
And I thought, this is kind of exactly my thing for my company and what we're doing. So I thought, you know what, I'll do it.
And now when I go into some of my clients, they go, oh, the goat lady's here.
Now, on today's show, Graham tells us what happened to a Romanian couple who hijacked surveillance cameras in Washington, D.C.
Lisa visits the world of insider traders who are trading our secrets. And I'm revisiting the Uber hack of 2016, now that we have all the juicy details.
All this and loads more coming up on this episode of Smashing Security.
This beautiful romantic couple were walking the streets of Washington, D.C. Him, he was tall.
He was tanned, his blonde hair blown in the wind like a young Robert Redford, a long red tie dangling down his torso.
And next to him, a pouting former model from Slovenia, a picture of true love. I'm talking, of course, I think you can guess.
And we thought, oh, wonderful, a whole brand new era of civilization is about to begin. How fantastic, how optimistic.
Yes, those were happy times, and we knew everything was in safe, albeit quite small, hands. Well, Graham, let's not bring my hands into things. But we knew we had nothing to fear.
But Donald Trump's presidential inauguration could have gone horrifically wrong.
There's some people who think it did go horrifically wrong, of course, but you know, just days before the ceremony, just days beforehand, hackers managed to hijack 70%— 7-0%— of Washington, D.C.'s public surveillance cameras being used by the police.
And they demanded a ransom for their safe return of over $60,000.
Hackers targeted traffic and security cameras in the nation's capital just 8 days before President Trump was sworn in, and the attack happened while federal law enforcement officials were trying to ramp up security.
I mean, I know it can be hard getting those stations overseas, but you wouldn't necessarily go to this effort.
But what they did was they installed ransomware onto the computers controlling the cameras.
Nasty stuff. And the Secret Service, as you imagine, you know, they sprung into action because this was—
Oh yeah, they demanded a ransom.
They said this was a really high priority due to the impact on their mission, which was obviously to protect the First Lady and POTUS as he was given all the power.
I mean, that was a truly historic moment, needed to be recorded. We needed photographs of the crowds for posterity so that we could later count how many.
But to your point, if they were worried about any dissidents at the event, that is presumably how you would capture them.
It's fun to unravel the mystery and find out who did what and why. And that is what a recent article in the Wall Street Journal does rather spectacularly.
And I was reading this and I thought, oh, I would love to share this with listeners of Smashing Security.
So I'm gonna tell you what was happening because while Donald and Melania, let's not start a rumor that the First Lady's a man.
No, so Melania, while they were, you know, doing all those lovely things, there was another couple 5,000 miles away in Bucharest.
Alexandru Isvanca and Evelyn Cismaru, a guy and a girl, and they were set up in Bucharest and they were rather like Bonnie and Clyde.
They were a bit like cyber criminals of the 21st century. They actually liked to call themselves, their nicknames, their pet names for each other were Bobo and Eve.
So I think I might call them Bobo and Eve as well.
In fact, ever since around about a year after they first met, they had supported themselves in their relationship through computer crime and credit card fraud.
Fairly unsophisticated stuff. Yeah, romantic. Well, you know, who knows what they're buying. Committing small-scale online fraud with stolen credit card numbers, spamming out people.
And they largely got away with it, I think, because for the police, the cost to investigate the crime was just too high.
And sometimes that doesn't always mean everything gets investigated.
It all adds up to money, money, money, and lots of effort, which maybe could be being spent elsewhere.
And I think some financial institutions, if it's not tens of millions, are happy to take it on the chin. You know, and they think, well, consumers are gonna pay for this ultimately.
You know, through bank fees or whatever.
So Evelyn, also known as Eve, she was actually found guilty of some credit card fraud back in 2012, but she only got a suspended sentence and told to behave herself in future.
But surprise, surprise, that didn't stop her. And it didn't stop Bobo either.
And from their apartment in Bucharest, they had spammed out this ransomware attack to an email list they'd picked up.
And it just so happened that it infected all of these computers running Washington DC.
It's just that they were unprotected or the users on those computers had clicked on an email attachment, and bam, they got infected, and then it spread inside the organization.
And his mistake was to order food from a pizza shop called Andy's Pizza in Bucharest.
You know, you can buy things on Amazon which don't come directly from Amazon, but from other people who sort of set up online stores up there.
And what happened was whenever people ordered something from her, she'd get the alert saying, oh, you know, Frank has ordered a book or a DVD box set or something.
And then she would use a stolen credit card to go and buy it from a legitimate seller. So they would do all the shipments.
So she'd get the money and then she'd use a fake credit card to actually buy it and get it delivered. Well, it's astonishing this sort of thing goes on, but it does go on.
But she didn't use her own computer to do this because that would of course left too many clues lying around, right?
officials, when the Secret Service were running around fixing the hijacked cameras and panicking about that and resetting the computers, they went to one of these computers and they found on it this tracking number of an Amazon package being sent to the UK, right?
And interestingly, when they looked at the order of what was being sent to the UK, do you know what it described the item as?
Because that's sort of, you know, all the smoke and stuff, which I thought maybe it's something like that.
And according to the Amazon description, adds a lovely smoky flavor to food and drinks.
The UK cops were then told by the Americans, look, this is the house where this gun is being delivered, and we think it's associated with this hijack of the CCTV cameras.
So cops went round to this house in Streatham.
We're just into barbecues in quite a serious fashion.
She had created a Gmail account as a backup to some of her other online accounts, and she'd attached to that Gmail account her real name.
And you may not be surprised to discover that the police have it within their ability, if they have a name, to then possibly locate the person associated with that name.
And so they were able to identify that this was the same Evelyn in Bucharest.
Evelyn Chutsemaru, also known as Eve, was extradited to the States and has since pleaded guilty and agreed to testify against her former boyfriend.
The full story of how she was caught is quite fascinating. You can go and read it on the Wall Street Journal. It is quite interesting to read.
But anyway, she has since been released for time served. And she's now in London working as a fashion fitness entrepreneur.
He's facing trial in Romania on other credit card theft charges. And is currently facing extradition to the States where he could face up to 20 years in prison.
Can you imagine the arguments that they were going on in that car? No, it was you because you ordered that pizza. No, it was you because— I mean, it would have been beautiful.
Maybe not even commit the crime in the first place, but also as a backup for your future career, maybe set up an Instagram account because maybe you'll become an Instagram influencer.
They caught the attention of the FBI, who otherwise would never have looked their way because they were doing petty crime in Bucharest.
I think if you spam out a lot of email addresses, there's a danger that you might infect someone who you didn't want to infect, like the FBI, like Scotland Yard, like the NSA.
You know, you just want to stay well away from those kind of targets.
And they've been charged for insider trading, basically.
Yeah, so they've basically been taking loads of information from the companies they work for and selling it on to other traders through middlemen so that they can basically make— they reckon about tens of millions of dollars in profits have been made from this, and it's been going on for over 5 years.
So their OPSEC was a little bit better than— so they had pseudonyms for each other as well. They called each other Pops and Popsie in their emails.
I know, it's beautiful, isn't it?
So they were sort of going through middlemen, sending these things, and one of the messages that has been sort of revealed in this court case is that he wrote, once upon a time, there was a pop searching for truffles in the forest.
And attached to said email was a highly confidential file relating to a pharmaceutical company that got sent to another trader. And they use these cryptic messages.
They were encrypting everything. They were using burner phones to pass information. And yeah, they cost a lot of people a lot of money and they're in a bit of trouble for it.
So it was a beautiful story of love and money.
But it's kind of interesting because one of the commentary pieces on it was that in some of the cases they released information like, okay, there's going to be a merger.
So the share price was going to go up.
So they get some sort of dirt on the company from these people and then they publish it and then the share price drops.
So interestingly, they were just at this for years and it seems to be that this is just the tip of the iceberg and they reckon that there could be 10, 15 other people around the world who've been involved in this ring of insider traders.
So it's really fascinating because obviously they were at a company that you'd have thought would have had a reasonable amount of security, but yet they were still managing to exfiltrate all this information and then use it to make millions.
It must just be, "How was your day?" "Fine." "Good." It's being married to a spy or something.
It reminds me a little about a hacking gang who a few years ago hacked into PR Newswire and some of the other press newswires, because of course that was somewhere where hundreds of companies were posting financial news or news about mergers and acquisitions.
And the hackers managed to get hold of these press releases before they were published and then sell them to dodgy people who were doing the trading. And they made a fortune.
This really is a more effective way, if you don't get caught, of making a large amount of money through cybercrime than just sending out ransomware, I reckon.
And I think the other thing, people always think that, 'cause we talk so much about PII and personal information and stuff, actually to an insider threat, that's pretty useless information because the stuff that's gonna make you big, big bucks is going to be trade secrets, it's going to be market information, it's going to be IP.
You know, that's the sort of stuff that you can steal and sell for a lot more money than any personal information of any employee or anything.
Because he stole trade secrets about the self-driving cars that Google were developing and he sort of took them with him when he left.
Rolled into Uber and was, "Hey, Uber, guess what?" This is such a big problem, isn't it?
I mean, with an Uber, you never really know what you're gonna get. You must have a crazy Uber story. I think everybody does.
And with the cleaning Febreze stuff. Oh no. Oh my God. Oh.
Well, the two guys behind the hack have recently pled guilty, and some pretty juicy details have come out since.
The upshot is Uber did not react the way you would want a respected company to behave, in my opinion.
So question one was, how did these two hackers get into Uber and steal that ginormous treasure trove of user information?
So in 2016, the two hackers, a Floridian named Brandon and a Torontonian named Vasily, used their custom—
These two guys used their custom-built GitHub account checker tool to test user credentials leaked from other sites against GitHub's own service, and they were particularly interested in targeting credentials of corporate employees because they wanted to get high-value GitHub accounts.
They weren't interested in little, you know, people like me with a few things there. They want to look for the motherlode.
They're looking for passwords, looking for keys, looking for anything that's gonna allow them to breach any associated Amazon Web Services.
So boom, they had the goods. This is the personal information of nearly 60 million users and drivers. Now, question 2, how do they extort the money but stay under the radar?
So with this data in possession, the two hackers created and used a ProtonMail email service.
Now they contacted the then chief security officer, Joe, the CSO.
Not the authorities, as the rules stipulate, not the affected users whose data had been stolen. Everything was kept deep, deep undercover.
I mean, certainly a few years ago, I know they've changed CEOs since then, but they were up to a lot of very dodgy things, which will make them very controversial.
And they did seem to, yeah, ride a bit rough shod over the rules.
So he carried on the charade.
You know, Joe the CSO paid via the company's HackerOne bug bounty program, which from a corporate standpoint is probably a very, very good way to hide if you're gonna pay off a ransom.
So this gets interesting here, right, for me. So we have responsible ethical hackers out there, right? And they find flaws and they contacted the affected company.
They provide proof that they were able to do something. And then often they look for payment for their hard work.
In exchange for that, they will not go public until the problem is sorted. That's effectively what we'd call responsible disclosure.
Now these guys, they're doing a similar thing, except they're holding data for ransom. They threaten to go public with that information unless Uber pays up.
You'd simply see that you had access to it.
So the other big question, how did Uber know that the hackers would not release the data after they made their payment? Right? That's the big question we always have.
How, you know, okay, I've paid off the ransom, but how do I know?
Now, in order to ensure that the hackers stayed stum about their activities and their big treasure trove of data, Uber made the hackers sign NDAs.
This is a non-disclosure agreement, right, that holds parties accountable to keeping their trap shut. But how did they do that, right?
They didn't know the hackers' true identities, did they? Yes, they did.
And then two days later, another Uber rep meets up with the Canadian hacker in a Toronto restaurant and gets his John Hancock on the NDA form.
So they knew who hacked them, but never gave the identities to the cops. So to be fair though—
It's kind of a waste of time, really. I just think that in fairness, it does make logical sense.
It's not a very good strategy decision, and it clearly does not make you look very transparent, but you're not exactly going to go and publicize it after you've got them to sign NDAs.
The fact that they did this kind of ensures that they weren't going to go live with the data.
So in a way, it may have been a very responsible thing to do in terms of Uber customers whose data had been stolen.
They could have just whispered to him or left him a copy of it, or they may have been lazy with their own security, so someone else could have hacked the data.
And who knows, because those passwords were left on GitHub, someone else could have pinched it as well.
So they should have told all those Uber customers and drivers about the problem.
We really can't afford to have this huge, massive data breach that shows knows how incompetent we've handled our data to come out and then our share price will be zero and we won't, you know, that'll be that.
That was really the motivation.
What was he going to do, go live on the record and say, yeah, okay, so I paid them, I knew who they were, I made them sign NDAs to keep it all under quiet, and that would have been better for the company anyone.
And you know, it was only 10 months after this NDA signing, right, that Uber told riders and drivers— and that was under new management, you mentioned that earlier— so that's a long time now.
The current CEO, he said in a statement last week, "None of this should have happened and I will not make excuses for it." And he said, "While I can't erase the past, I can commit on behalf of every Uber employee that we will learn from our mistakes." Now, I was all cool with this apology till the word mistake.
Okay, mistake. I think that's a little bit rich, don't you think?
I mean, I'm not talking about the breach, the fact that they got, you know, their security wasn't on par and someone stole their data.
But how they responded to the breach is really abysmal.
I mean, we talk all the time about companies getting hacked and the mistakes they make, but this sort of deliberate cover-up, an attempt to avoid telling your breached customers about what's happened is scandalous.
And their comms messaging was on point, really transparent. And I truly think that honesty is your best policy if you know you've been breached.
When you— how you handle yourself in a crisis is a very good measure of something, someone you want to invest in.
And the Netherlands charged €600,000. And there was a $148 million fine for a class action lawsuit, right? So this was a settlement for that.
So all that together, still for a company reaching $3 billion in revenue is a tiny, tiny tap on the nose rather than a smart slap on the choppers.
If they— so if they get the money and you're, oh, well, you were an Uber user, you can get, you know, £140 off your— this year's taxes. That might encourage—
With central admin oversight, controlled shared access, automated user management, you help every employee become part of your security solution.
Find out more at lastpass.com/smashing.
Plus, I would like to extend a personal invitation to an upcoming LastPass event on Wednesday, November 27th, in the wonderful city of Manchester.
Occasional Smashing Security guest host Jessica Barker and yours truly are going to be talking about all things security related. We would love to see you there.
Check out the registration page on lastpass.com/smashing. On with the show.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish. Doesn't have to be security-related necessarily.
And oh, I see my wife has left the iPad. Within reach. I thought, I wonder what I could prop— I could prop that up somewhere and see if I can watch something.
Anyway, so I propped it up at the end of the bath and I went onto Amazon Prime and I went back in time once again, because I'm quite nostalgic.
I remembered being a 12-year-old boy watching a BBC TV show from the late 1970s, early 1980s. Called The Master Game.
On some of them you have to pay, but on this one you can watch the entire series for free. And it stars 15-year-old Deep Purple fan Nigel Short.
And if that isn't enough of a clue, Carole, as to what this TV show is about, it's about chess.
And as they were playing, you would actually get their internal commentary from the player themselves as though they were playing it. So they'd go, oh, what to do? Interesting.
That's a very sensible move he has made.
It was very innovative at this time because of course they didn't have computer graphics.
I have to say, when I was 12, Bill Hartston was a bit of a hero for me. Reminds me a bit of my dad—sort of softly spoken, sort of nice chap.
Gogglebox is a TV show where they basically film people sat on a sofa watching TV and responding to TV.
Fantastic, very exciting for me.
So I would recommend, if you have any interest in chess—I know I've probably lost you if you aren't interested at all—then go and check out The Master Game on Amazon Prime, and you can also see some clips on YouTube as well.
And that is why it is my pick of the week. Lisa?
So mine is an app, it's a game that I've recently become addicted to and it's called Plague. Yeah, it's gonna—it's just gonna get worse from this point.
And basically it's a bit weird, but it's a game where you have to design a bioweapon, a virus, a bacteria that's gonna infect and kill off every single member of the human race.
And it's really, really difficult because the damn humans keep working on cures or isolating.
They close airports, they close shipping ports, and you have to get around it, and it's really difficult.
I waste so many hours traveling, playing, killing humans, basically, is what I do.
Looks like it's—oh, there's even a board game version of it.
Not at all what I had in mind. It's really frustrating and I don't want to do it anymore. And in those times, I have taken to watching old art documentaries on the YouTube.
And there are a few wonderful compilations, which I will share in the show notes on the Smashing Security webpage.
We're talking hundreds of hours of intelligent thought-provoking, insightful, interesting things into artists or art movements or techniques or scandals.
I was recently watching one called The Great Contemporary Art Bubble.
It's a BBC documentary from 2017, and this is on Damien Hirst and how he was at the center of the art bubble because there was this gallery called The White Cube in London and they would occasionally come, "We've got a brand new Damien Hirst and it's valued at 500 million," you know, and have an auction around that.
But it turned out that someone had leaked their inventory and price list and they had hundreds or even thousands of Hirsts in the back room and they had all the prices written down.
So in other words, they were controlling the supply and demand of the artworks to keep by keeping them scarce. And what does Damien Hirst end up doing?
He decides to hold his own auction of the works he still owns, right? So this could undercut the gallery, but what are the galleries supposed to do?
If they don't support him, then his work might get undervalued because he might sell them for a few thousand.
But if they do support him, they don't get to see any of the money returned because he owns the whole auction. Fascinating. Check it out.
I will have a bunch of show notes of different YouTube compilations and a few shows that I found fantastic. And if you're into art or artists or Francis Bacon— crazy, crazy.
What's the best way for folks to do that?
Just look for the Smashing Security subreddit.
Special Patreon supporters, you have mail, or you'll be getting some soon. I stuffed the envelopes myself along with a little "You rock" note.
So check out smashingsecurity.com for past episodes, sponsors, details, and info on how to get in touch with us.
Everyone with a 4-year-old knows exactly what I'm saying.
Hosts:
Graham Cluley:
Carole Theriault:
Guest:
Lisa Forte – @LisaForteUK
Show notes:
- Ransomware attack impacted 70% of Washington DC police surveillance cameras — Graham Cluley.
- The Hapless Shakedown Crew That Hacked Trump’s Inauguration — Wall Street Journal.
- Eveline Cismaru's Instagram account.
- London Investment Bankers Charged in Insider-Trading Ring — Bloomberg.
- Trade-Secrets Case Linked to Google Seen as Warning to Silicon Valley — Wall Street Journal.
- Uber concealed massive hack that exposed data of 57m users and drivers — The Guardian.
- Uber's statement about its 2016 "Data Security Incident"
- Hackers who extorted Uber and LinkedIn plead guilty — ZDNet.
- Maersk: Springing back from a catastrophic cyber-attack — I-CIO.
- The Master Game — Wikipedia.
- BBC's The Master Game — The Kenilworthian.
- Gogglebox — Channel 4.
- Ndemic Creations, makers of Plague Inc.
- Plague Inc. trailer — YouTube.
- Plague Inc. — iOS App Store.
- Plague Inc. — Google Play.
- The great contemporary art bubble. BBC documentary – YouTube — YouTube.
- BBC art documentaries playlist — YouTube.
- Painters and artists documentaries — YouTube.
- Art documentaries playlist — YouTube.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff)
- Support us on Patreon!
LastPass Enterprise makes password security effortless for your organization.
LastPass Enterprise simplifies password management for companies of every size, with the right tools to secure your business with centralized control of employee passwords and apps.
But, LastPass isn’t just for enterprises, it’s an equally great solution for business teams, families and single users.
Go to lastpass.com/smashing to see why LastPass is the trusted enterprise password manager of over 33 thousand businesses.
Follow the show:
Follow the show on Bluesky at @smashingsecurity.com, on the Smashing Security subreddit, or visit our website for more episodes.
Remember: Subscribe on Apple Podcasts, Spotify, or your favourite podcast app, to catch all of the episodes as they go live. Thanks for listening!
Warning: This podcast may contain nuts, adult themes, and rude language.