
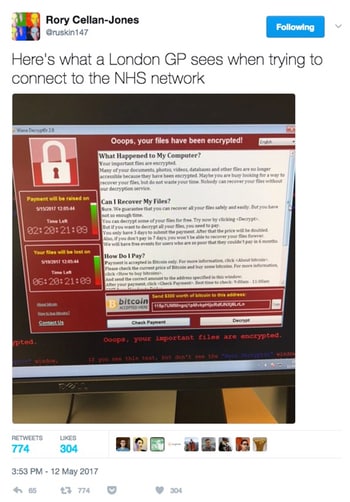
The WannaCry ransomware (also known as WCry or WCrypt or Wana Decryptor) burst onto the scene spectacularly today after NHS hospitals across the UK ground to a standstill, as the ransomware encrypted files and caused staff to cancel operations.
I can only imagine the chaos.
As you can imagine it’s “been a bit busy” here too. Every time I try to write something the media grab me for an interview, and I spent an hour or so in a BBC studio in Oxford while they tried to work out why they couldn’t beam me live down the wire to their studios in London.
(They never did find out what the gremlins were, but thought it “probably” wasn’t the WannaCry ransomware.)
The NHS wasn’t targeted. They’re just a huge organisation which has had insufficient investment in computer security over the years. In short, it has a lot of computers and at least some of them weren’t able to withstand an attack like this.
The state of the NHS’s cybersecurity becomes obvious when you consider that it still relies heavily on computers running Windows XP, which Microsoft started to tell people to dump way back in 2007, and finally stopped patching in April 2014.
If you were still running Windows XP after that date – well, you had something bad coming to you.
The UK Government did end up paying Microsoft over £5.5 million of taxpayers’ money to receive support and security updates for a further 12 months after April 2014 (did they not pay any attention to Microsoft’s warnings since 2007?) but that really was the last chance saloon.
But it would be wrong to think that the NHS was targeted. They weren’t. This is extortion – 21st century style. The bad guys release ransomware (in this carried by a worm which exploits a vulnerability), and their intention is to infect as many PCs as possible to make as much cash as possible.
Hitting the NHS wasn’t necessarily their intention, but it is a soft target due to its poor defences. And, of course, the implications of a widespread NHS infection is felt by many people.
Meanwhile, other organisations in other countries were also impacted. For instance, Telefonica in Spain, and FedEx.
WannaCry appears to have spread at an astonishing pace because it has been spread by a worm exploiting a Microsoft vulnerability – MS17-010. Once one computer in your organisation is hit, the worm hunts for other vulnerable computers to attack.
Before you know it, you’ve got a big problem.
You probably don’t care about this if you’ve had your computers hit by WannaCry, but the story behind the MS17-010 vulnerability is an interesting one.
The vulnerability was first found by the NSA. However, they chose not to tell Microsoft about it. (Which is a shame, because that would have meant computers would have been patched earlier).
Instead, the intelligence agencies kept the details of the exploitable vulnerability to themselves, so they could use it to infiltrate computers and spy upon them. They dubbed the exploit “ETERNALBLUE”.
However, a group of hackers called the Shadow Brokers stole details of this and other exploits used by US intelligence agencies, put them up for sale, openingthe door for other criminals to exploit the vulnerabilities.
Microsoft responded with a patch, but wouldn’t it have been better if the NSA had done the decent thing for all of us on the internet and told Microsoft about the flaw as soon as they discovered it?
Sometimes you protect your country best not by spying on others, but by ensuring that everyone in the world (including the people you may want to snoop on) is better defended.
I’ll update this page with more on WannaCry as it becomes available, but for now you can either follow me on Twitter at @gcluley or (perhaps most importantly) ensure that you have applied Microsoft’s vulnerability patch MS17-010 from earlier this year.
Stay safe folks. And remember to make sure that you have a secure backup regime.
For more discussion on the issue, make sure to listen to this episode of the “Smashing Security” podcast.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Recorded Future arms threat analysts, security operators, and incident responders to rapidly connect the dots and reveal unknown threats.
Their patented technology automatically collects and analyzes threat intelligence from technical, open, and darkweb sources. Why?
To provide invaluable context for faster human analysis and real-time integration with your existing security systems.
Sign up to their Cyber Daily newsletter and get the latest insights from Recorded Future at recordedfuture.com/intel.
Hello, hello everybody, and welcome to another episode of Smashing Security, number 21 for the 18th of May, 2017. And I'm joined as always by my buddy Carole.
Pob isn't just here to say hi to Jason Isaacs from the Harry Potter movies. He's also here because we brought him in to talk about the big story of the last week.
Actually, did anything happen in the last week? Has anyone noticed?
Everyone on Twitter was saying, "I wonder what Smashing Security is going to speak about this week." Yes, we are going to talk about WannaCry, but we're going to do it a little bit later in the show, if that's all right with you.
In fact, I was talking to the BBC about this particular issue and then WannaCry happened. So I think they never actually published their story about this.
It's about HP laptops and a bunch of Swiss security researchers discovered that the audio driver being shipped on a number of HP laptops didn't just drive your audio and do all sort of audio sort of things.
It also secretly logged every key press which you made.
So I mean, the first thing that HP did when this was found out was like, "We're not getting any of these key presses," which obviously could have included password details and credit card information.
All, you know, basically everything you type, right? All of your, all of the sexy messages which you may send in the office.
Now, the reason why these keystrokes were being kept was actually because the programmers who were writing the audio driver were using it as a debugging method.
They wanted to capture whether things like function keys were being pressed in order to mute the microphone or unmute it and all that kind of jazz.
You need to be confident that your software, you know, you want it tested.
You want it tested and you want to know it's the software which you expected to ship, which you're actually shipping.
So, you know, it's bad enough there are thousands of Trojan horses being released all the time that spy on people's keyboards without also having legitimate software silently collecting it.
And even if it was unlikely that remote hackers might be able to grab hold of this information, imagine being at home, maybe you've got a jealous partner or you have a business rival.
If they gained access to your laptop, they'd be able to find everything, wouldn't they? On that, in that file, everything which you'd been typing. Pretty bad stuff.
I've done some work before with the Digital Stalking Trust who are, you know, trying to share information and spread advice about how to avoid being spied on and stalked online.
So, you know, I think this is a real fear. Now, of course, this big stink got kicked up over this, right? Oh, how can they do this? And HP, you know, they did the right thing.
They issued an update.
What they did was they changed the registry key, the setting, to turn it off. Which means, in theory, I mean, obviously that—
You know, they just wanted to get something out really quickly, and maybe this was the way to do it.
You can kind of understand why somebody leaves debugging code in software, but there should be a QA and they shouldn't have done it.
I would expect now Trojans just to be turning that registry key back on and seeing what's in there.
So it may have got buried in the press.
You must be— it's nice that it's maybe not made it on all the top of the front pages.
Make sure that you're running the very latest version of the audio drivers so that they're not secretly logging any key presses. Maybe look for that file, mictray.log.
So it's mic as in microphone.
Just to make sure that it's not there and indeed that you haven't been backing it up somewhere because there may be copies of it elsewhere because you do back up your computers, don't you, and your data.
And you were probably still in kindergarten, Carole, but I'm sure Graham remembers the Morris worm.
Everything is ransomware. Yeah, no longer are people writing worms and viruses for fun to impress their mates. They're doing it for financial gain.
And so the bad part about WannaCry is it was ransomware, and as people have said it will make you want to cry.
It was a network worm and it exploited a known vulnerability in SMB, Windows network sharing software.
And the particular vulnerability was publicized by the Shadow Brokers NSA hack, and it's been patched for about 10 weeks now. But there were actually two vulnerabilities used.
So there was a vulnerability called EternalBlue, and that allowed people to write a file to a remote SMB share.
And there was another vulnerability called DoublePulsar that allowed you to execute files from a remote SMB share.
And they created basically these exploits, having found the vulnerabilities in Microsoft's code, in order to spy and snoop on people, didn't they?
But the other half of their job, and part which arguably they failed to do on this particular occasion, is also to protect and secure the United States and other organizations against these sort of threats.
But yes, and I think we'll talk about that more in a minute, Graham.
So this exploit, this worm used these two exploits and most people first heard about it when Telefónica alerted on this, telling its employees to shut down their computers amid a massive ransomware strike.
So it seems that lots of NHS trusts— and for non-UK-based listeners, the NHS isn't one homogenous organization.
It's lots of federated hospitals that come under the umbrella of the NHS.
And the NHS got hit quite badly to the effect that A&E waiting times went up, hospitals stopped surgery. They stopped MRI scans because their computers didn't work.
Reports are that businesses and organizations in over 150 countries got hacked.
And this all came to an end early in the UK evening, about 6 or 7 o'clock, when somebody registered a domain that was in the code.
So a young computer researcher was looking at the code and he saw a domain that was looked up by the virus or worm, and he registered that domain so he could track how many computers had been infected.
So the action which was taken by that guy, MalwareTechBlog he is on Twitter, if you want to give him a thumbs up and what he did, had this really positive effect because it prevented the malware from spreading any further.
It effectively was a kill switch on the malware.
I wasn't for a minute suggesting, I'm just saying I had a problem with the word kill switch that the media used because I think it gave people a false sense of security.
And clearly it hit the UK's National Health Service, but also hit very hard in Russia and elsewhere around the world.
Maybe what would be interesting for us to discuss is whose fault is this?
Because it seems there's a lot of blame and a lot of finger-pointing which is going on right now as to who should be taking some flak.
And I don't know if the NSA told them about it, but they certainly patched those in all the supported systems quite quickly and said it was a critical update.
And that was about two months before this actually exploded.
And also let's not forget, okay, Microsoft did have a bug in their software, naughty, naughty, but what programmer can put his hand up and say he's never written a program with a bug in it?
Yes or she? So, I mean, Paul, you're a programmer. Have you ever written a buggy program?
You know, there are bugs found in Android all the time, aren't there? Which is sometimes quite serious as well.
Yeah, as we kind of touched on earlier, this bug was made public by the Shadow Brokers who stole it from the NSA. Is it the NSA's fault for writing this bug?
Well, the NSA's job, and just like GCHQ's job, is signal intelligence, and it's to try to steal secrets from foreign governments and enemies of the state.
So the NSA were doing their job by creating this, and it looks like, given the timing of the Microsoft patch, the NSA did tip Microsoft off about it when they knew that the Shadow Brokers were going to release this exploit.
We better tell Microsoft. There's another reason why maybe we can apportion some blame to the NSA. If we go— I love this.
We're going through our little blame list here, which is the NSA got hacked and the NSA are meant to be all about security. And here they go again.
Having a very embarrassing data breach. And I seem to recall they had another quite a big data breach, didn't they, a few years ago involving that contractor, Eddie Snowden?
Shadow Brokers claim to be an independent hacking team.
We would say, well, you get hacked by the KGB. Again, that's what the KGB is designed to do, to hack people like the NSA.
I am convinced loads of them are running legacy systems that are not running the latest and greatest. I wouldn't be surprised if there's even XP machines still running.
And, you know, how—
The issue with the NHS, like universities, is they don't often have one overarching IT system.
So the radiology department might have a slightly different system to the ICU or the ER or different parts.
And no disrespect to the IT guys in the NHS, they're not getting paid an awful lot of money, and they're getting run ragged keeping up to date with all the other things they have to do, allowing the doctors to use their iPads and whatever else they have on their plate.
So it's very difficult.
And so they don't have any more recent updates to the software and, you know, they can't get a Windows 10 machine to drive that piece of medical hardware.
And it would cost an absolute fortune, much more than replacing a computer to replicate this. And I think they're making that decision all the time.
It's like, well, we can spend this extraordinary amount of money and secure ourselves against some of these threats, or we can—
So for those who don't live in Britain or aren't aware, you know, the UK's National Health Service is pitifully underfunded.
You know, no one's saying they're not very responsible here. But if we had to go to, you know—
And we're not just talking a flimsy lock and a flimsy key.
I think triggering the ransomware immediately was probably silly of the author because the best pathogens want to keep their hosts alive.
In biological terms, it's no good killing patient zero, which this nearly did. There were several coding errors.
Reports are coming in now that the bitcoin code may not have worked properly.
And so this may be why it appears that so few payments have actually been made.
I think the last time I looked it was something like about $70,000, which, yeah, sure, it's great for a week's work, isn't it?
But for the scale of this attack, you would've expected them to have made more than that.
So back off.
Actually, speaking of movies, did you hear, did you guys read about the Texan who is suing his date for texting during a 3D screening of The Guardians of the Galaxy Vol. 2?
Anyway, apparently texting is one of his biggest pet peeves.
So he's asked this girl who's basically texting— she says she's texting because her friend's having some crisis, so she's just telling, you know, giving a few replies.
And he says, can you stop texting? When she doesn't, he tells her to go outside. So she does and does what any girl would do and doesn't come back.
He then— he's reportedly contacted her little sister chasing up the payment, and then he goes and sues her. So as I said, douche, right? She probably have a tattoo in his forehead.
Anyway, that's just—
You might have heard that the latest blockbuster— we don't know exactly which one, but people are thinking it's probably Pirates of the Caribbean— has been stolen from Disney.
Now, Chief Bob Iger says that the hackers have stolen it and they are demanding ransom for it. So this is not the first time we've seen this in Hollywood, has it?
Wasn't there— it was a few weeks ago, wasn't it? It was Orange Is the New Black. Yes, that was taken from Netflix.
So it's a similar situation here where they're saying if they don't pay up— and they haven't declared the sum that they're being asked, but they're asking for a large sum, a huge sum according to the Disney chief, in bitcoin— and otherwise they're threatening to release the first 5 minutes, and then they're going to release 20-minute chunks of the film until the financial demands are met.
Now, what's interesting—
Now the thing is, this movie is supposed to be released on the 26th of May, so that's— is that next week? That's next week. So they don't have very long to get their money in.
And the thing is, how is this happening repeatedly? So how is it that hackers are getting their hands on these final cuts?
I am sure these cuts are being watched with— by people's lives, how much money they cost. You know, there's a lot of— this is huge money.
So how do you think this may have got out?
And, you know, you're putting your trust in their computer security as well.
So even if you, as the boss of Disney, are thinking, "Oh yeah, our computer security is really locked down and everything," those partners of yours may not be as careful.
There's both the danger, the sort of insider threat danger of someone leaking the movies, and maybe they're getting more on top of that these days because there's been so much piracy in the past.
But there's also the computer security, isn't there, of external hackers. And it does seem that some of the hacking gangs have been particularly interested in doing this recently.
I guess because—
Everyone wants to talk about the Hollywood celebs, and it gives them a chance actually probably to put an ad up for the movie so they can get, you know, the newscaster, they know that the articles can get, or rather the publications can get a bit more attention.
Do you guys? I mean, what percentage of people that go to the theater might do that?
And maybe it's not just the people who are working on this, it's people who have to review it. It might have gone to the directors, or just to have final say.
And all I could think of was Mission: Impossible and this message must be destroyed after 5 seconds.
So they really need a way to play the movie and wipe it completely so you can't maybe copying it in these kind of scenarios.
And so they're sharing files inside a sort of encapsulated bubble or whatever, which gives them the ability to, you know, zap a file permanently, you know, and prevent people from copying it in unauthorized fashions.
But yeah, that's a really good suggestion, actually. The other thing is I don't think they're losing a lot of money.
And the other thing is they're getting a lot of publicity about the film, because I can't imagine that, you know, if I didn't know anything about the films, which actually I don't, right, I might go, oh, it's a popular film because someone's stolen it and is now holding it for ransom.
So I think there's some kind of weird sense that it actually makes the film more important and more people will actually go see it to see what the fuss is about.
It's called Smashing Security, and you can find it on iTunes. You can leave a review if you like as well.
But if you like the podcast, please subscribe, and that means you will automatically get it every time we release a new episode, which is normally every Thursday.
You'll find our email contact form and you can find a link to our Twitter as well.




Most infected computers are in Russia and it's a sign that WannaCry is a planned cyber-attack
against Russian organizations and institutions, including Ministry of Internal Affairs
of Russia and Investigative Committee of Russia as it's said there
https://malwareless.com/wannacry-ransomware-massively-attacks-computer-systems-world/.
Russian hackers never attacked computers inside their country with ransomware in order
to avoid further problems with police and FSB
Don't tell Trump…not that he'd understand any of what you have said here. Too many big words…sad! What worries me is if these guys attacked the National Grid? Can u imagine the chaos?
I don't think you understood what Graham has said, particularly the paragraph that begins "But it would be wrong to think that the NHS was targeted." This was a worm, not a targeted hack.
This looks like a lucky strike on very vulnerable internal system rather than a specific targeting of the NHS. I wonder if there are multiple encryptors due the the worm capability. Typically there is one PC infected and it does the encryption buit in this case there are reports of the ransom mesage appearing on many systems – -imagine the mess if the documents had been encrypted multiple times by multiple instances, the only way to return the files would be to decrypt in the reverse order the files were encrypted. Maybe this would mean that decryption was nearly impossible even when paying ransom.
Fingers crossed for robust backups!
Morrison's self-service tills run XP. I saw one booting up the other day.
That would be a version of embedded XP which still gets supported by Microsoft. Runs on an awful lot of Point-of-Sale systems and is supported until 2019
The WannaCry looks like the ".Locky" virus to me but they say that this virus needed users to download or open a file but this is not true because i picked .Locky" up on a dedicated machine that was talking to the Tor vidalia software so that i could screen scrape sites without being tracked. Browsers were not used on the machine.
No wonder Bitcoins have been going up for the past few weeks because you have to use these coins to pay for decryption key to get your files back.
Microsoft says we need updates, last thing that i will be doing since this virus they say go deployed by there NSA backdoor going wrong
I liked Tor and would not say this was it not true but see over the coming weeks if i am right or not.
Interesting to note that I tried to withdraw cash from HSBC on Thursday (the day before this) and every cash machine I tried said "Out of Service" on it. I thought at the time that something big must be going down for them to take every cash machine offline.
"These hackers "have caused enormous amounts of disruption— probably the biggest ransomware cyberattack in history," said Graham Cluley, a veteran of the anti-virus industry in Oxford, England."
You're a veteran!
Yeah, the media don't phone me up anymore either.
Amazing how some news agencies say that this is the best time to upgrade to Windows 10. There you go Microsoft, free advert and a huge jump in Windows 10 sales. Imagine if this happened when Windows 10 was still free!
Stop using Windows especially for critical systems. The only time it worked out positively is when the Iranians were stupid enough to use it at their nuclear facilities.
The problem for institutions is that they have a big investment in software (often bespoke) that runs under Windows. Changing operating system, even in some cases updating to the latest Windows, will cost them much more than just changing the operating system. Maybe this event will provide sufficient motivation.
Well. you can pay for it now or really pay for it later.
How ironic when the heads of the US intelligence and security agencies are stating they would not use Kaspersky, that the NSA is somewhat culpable in causing this massive security breach? Maybe if they had said Kaspersky was OK to use, it would not have happened?! (Massive tongue in cheek there!) Or do the NSA chiefs have lots of shares in Microsoft, hoping lots of Windows 10 sales come out of this?!
I am not an expert in these matters, but get the daily email from Graham to keep up to date with cyber security and protect myself. Thanks to you I now use a password manager after too many years of not bothering!
Which password manager do you use Barry?
Don't tell him, Pike!