Services at a number of UK hospitals are slowly beginning to resume after a computer virus infected the electronic systems of their managing health care trust.
On 31 October, the Northern Lincolnshire and Goole NHS Foundation Trust (NLAG) revealed that a computer virus had affected its electronic systems the day before.
The incident, which also affected the United Lincolnshire Hospitals Trust, forced NLAG to shut down several parts of its systems and to temporarily suspend most services at its hospitals in Goole, Grimsby, and Scunthorpe on 1 November.
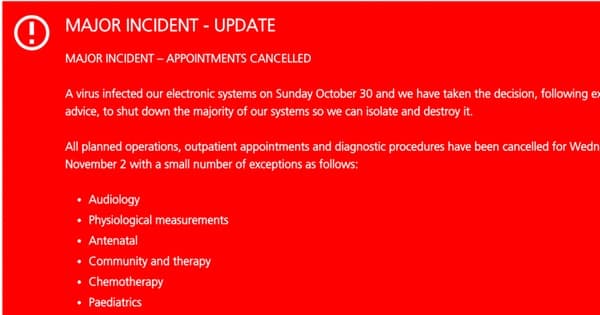
As the trust explains in a statement, which is quoted by Metacompliance:
“Our main priority is patient safety. A major incident has been called and all planned operations, outpatient appointments and diagnostic procedures have been cancelled for today (Tuesday). All patients should presume their appointment/procedure has been cancelled unless they are contacted. Those who turn up will be turned away.”

Fortunately, the situation has improved since then.
On 2 November, NLAG posted a new statement explaining that outpatient appointments and diagnostic procedures in antenatal, audiology, chemotherapy, immunology, and a few other departments would proceed as scheduled.
Urgent care will also honor many of its appointments. As Andrew Prydderch, Deputy Director of Urgent Care, told The Lincolnite:
“We are asking all patients to please turn up to their appointment as planned, unless they hear otherwise.
“We may still cancel a very small number of operations until all systems are back working but our doctors are working hard to keep this to an absolute minimum.”
Still, not everything is back to normal.
The NLAG computer system continued to experience issues on 2 November. In light of some lingering problems, the BBC reports that the health care trust might need to suspend appointments and operations for the next five days.
All of this begs the question: what caused the virus to take hold in the first place?
There’s no information regarding the source of the infection as of this writing. But there’s plenty that bad actors could have worked with to carry out the attack.
For example, Motherboard found out in September 2016 that dozens of NHS hospitals were still running the long-unsupported Windows XP on sometimes thousands of their PCs. Attackers could have exploited a vulnerability in that particular OS to gain access to the electronic system and plant malware.
Alternatively, actors could have abused some of the other security problems affecting the NHS health care system, including the fact that in the past many NHS websites have been found running outdated versions of WordPress with no central authority to manage them.
We can only hope this incident leads to the implementation of better security defenses at NLAG and NHS. In the very least, someone should make sure all relevant workstations are running up-to-date software. Doing so will help them better protect patients’ data and prevent a call from the Information Commissioner’s Office.


