 Websites run by Britain’s National Heath Service (NHS) are riddled with security vulnerabilities and could easily be exploited by online criminals, claims a newly-published investigation by Computer Active magazine.
Websites run by Britain’s National Heath Service (NHS) are riddled with security vulnerabilities and could easily be exploited by online criminals, claims a newly-published investigation by Computer Active magazine.
Part of the problem is that there are *so* many NHS websites – over 5000 are thought to exist – covering a wide variety of purposes from GPs’ surgeries to websites that offer advice about how to give up smoking or advice for breastfeeding mothers.
Critically, however, there is no central body responsible for maintaining these websites and ensuring that they are secure and – according to Computer Active – that means they can often be abandoned and never updated, making it easy for malicious hackers to take advantage.
Most of the flaws found in the investigation are caused by out-of-date versions of the WordPress blogging and website-building software. WordPress is used by approximately 400 .nhs.uk websites, but alarmingly fewer than 50 are using the latest and most secure version of the software (version 3.8.1 at the time of writing).
Outdated versions of WordPress are constantly targeted by hackers. In September 2013, security experts estimated that 70 per cent of all websites running WordPress were vulnerable to attack. In addition to old versions of WordPress, many of the NHS sites run outdated plug-ins – extra bits of code that add functions to a site.
The vast majority of these websites also use unsecured administrator login pages. This means that when a website administrator logs in their username and password are sent without encryption, making them vulnerable to interception by a hacker, who could gain complete control of the site. A number of other ‘.nhs.uk’ websites that don’t run WordPress also seem vulnerable to attacks, although exact numbers are hard to gauge.
Independent security researcher Terence Eden assisted the team at Computer Active by demonstrating how some of the flawed websites could be exploited.
For instance, Eden showed it was possible to embed a video of a bear fishing for salmon on an NHS webpage.

That in itself may appear harmless. But imagine if the video had instead promoted a dodgy “Canadian” pharmacy, telling website visitors to purchase drugs online, dodgy diet prodicts, or had pointed patients to a dangerous third-party site. It’s also easy to imagine how some online criminals could use such an attack to promote pornographic and gambling websites.
Eden also demonstrated a cross-site scripting (XSS) vulnerability on an NHS website giving advice on breastfeeding.
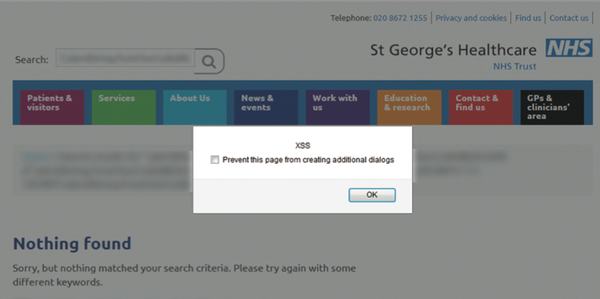
Such an attack could easily exploit visitors by tricking them into believing a pop-up was offering genuine advice from the NHS, or phishing for personal information.
Other bugs in old, outdated versions of WordPress could allow hackers to steal information or change the content of the NHS website pages, potentially infecting visiting computers with malware or taking patients to convincing-looking fake sites.

The problem is compounded, it seems, by many websites belonging to GP surgeries and NHS local authorities being developed by private third-party companies, rather than in-house IT teams, to save money.
A consequence is that when the private web development company has handed over the project to the NHS it may feel its job is over, and not responsible for any ongoing maintenance or security issues.
In Eden’s view, the government needs to grab the problem by the horns and take responsibility for the security problem:
“It’s inevitable that security fixes won’t be paid for, that responsibility for website problems will be impossible to determine, and websites will remain broken and vulnerable. If certain NHS websites aren’t able to be secured, central Government must take them over”
Of course, it’s worth remembering, that the problem of insecure WordPress websites is not limited to Britain’s NHS.
Time and time again, evidence is seen of attacks exploiting self-hosted WordPress sites, typically taking advantage of out-of-date installations, or old versions of themes or plugins.
Just last week, for instance, the vulnerability research team at SourceFire wrote about the “HelloEk” exploit kit using a variety of vulnerabilities to silently infect visiting computers that happen to visit compromised blogs.
 What is essential, if you run a self-hosted WordPress website, is to keep it updated.
What is essential, if you run a self-hosted WordPress website, is to keep it updated.
That doesn’t just mean keeping WordPress itself up-to-date, but also ensure that your theme and any third-party plugins you are running are also kept fresh to prevent hackers exploiting any security holes that may exist.
Malicious hackers are always looking for ways to infect computer users, and what better technique can there be than to compromise an existing, legitimate website and subvert it in such a way that it sneakily infects computer users when they visit it.
If you run a website and care about your visitors (and, if you run a website you *should* care about your visitors) then it’s essential to run a tight ship, and take security seriously.
I’ve run WordPress-related websites for years, and I’ve long understood the need to treat my site’s security as of paramount importance. That’s one of the reasons that I host my site with WP Engine. Yes, they’re a bit more expensive than some other WordPress hosts, but they understand the importance of running a tight ship.
If you want further reassurance that your site is not letting the side down when it comes to security, consider using an open source tool like WPScan, or asking a company like High-Tech Bridge to run an assessment of your site’s security.
For more details of the vulnerabilities discovered on the NHS website, visit Terence Eden’s blog.
(Please note: These same issues do not impact computer users who have decided to host their blog on WordPress.com. The .com version of WordPress is different from self-hosted WordPress websites, in so much as the version of WordPress on WordPress.com is always kept up-to-date, and there is much tighter control over what webmasters are allowed to do with the system).



Does this study truly cover "Britain's" NHS or does it just relate to England and Wales, bearing in mind that the NHS in Scotland is, and always has been, a separate entity and research usually reflects this.?
The report doesn't specify, but as it relates to .nhs.uk domains (which I think the NHS also uses in Scotland) it's reasonable to assume the same problems exist.
Thanks Graham.
Since the Scottish Government has eschewed any privatisation of NHS services I just wondered if it was safe to assume that the problems would be the same. Looks like I should ask NHS Scotland directly whether any such issues have been identified.
Hi Gordon,
Good spot! The FoI request that I found only covered England and Wales. However, the <a href="http://shkspr.mobi/blog/tag/unsecured-state/">research on *.gov.uk</a> covers every country, county, principality, and fiefdom :-)
Terence
It probably does not help having much of the NHS still using Windows XP either and probably older versions of IE