British contact lens vendor Vision Direct has revealed that some 16,300 customers have had their personal details, including full payment card details, stolen by hackers.
In a statement published on its website, the company explained that customers who who updated their accounts, or who made online orders, between 12.11am GMT 3rd November 2018 and 12.52pm GMT 8th November had their personal and financial details stolen.
The company emphasised that the stolen data was breached as it was entered onto its website and not taken from the Vision Direct database.
So what happened?
Unfortunately, it seems that Vision Direct is the latest in a growing list of companies who have fallen foul of hackers who have managed to run malicious code on merchants’ websites, skimming sensitive information as it is entered by customers.
That explains how it wasn’t just customers’ names, billing addresses, email addresses, passwords, telephone numbers and payment card numbers and expiry dates that were exposed – but also the three digit CVV security codes that merchants know they should never store.
In this instance, it appears that a reference to a fake Google Analytics script was planted on the website, and it is this which grabbed customers’ information as they entered it into the compromised pages.
Similar card-skimming breaches have affected other well-known brands in recent months, including Ticketmaster and British Airways.
Just last week I described how Magecart was haunting online stores, stealing payment card details from shoppers.
Vision Direct says it is contacting affected customers, with instructions on how to reset passwords. Obviously if you were committing the cardinal sin of using the same password elsewhere on the web, it would make sense to change those passwords too, and ensure that you never re-use passwords ever again.
Vision Direct says its website is now safe to use again, but there’s no word as to whether they will update their FAQ which now looks a little awkward:
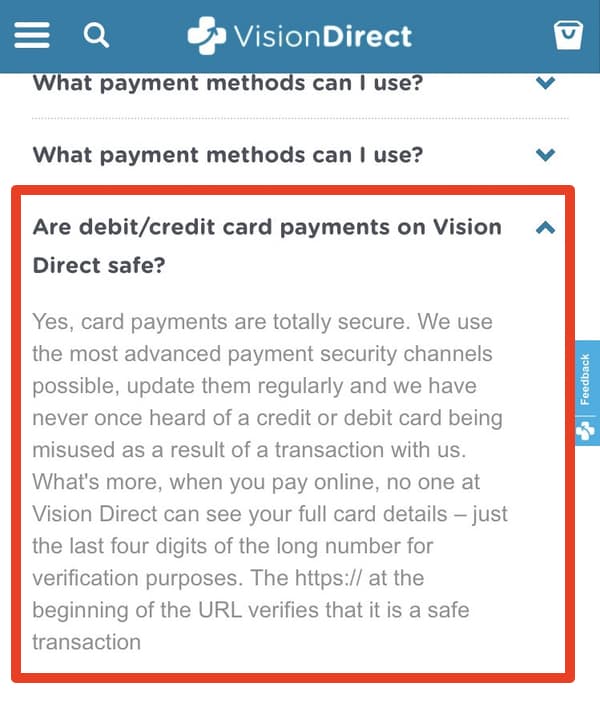
I’ve made that screenshot quite large for those who can’t find their glasses, or have run out of contact lenses.
Technical measures that Vision Direct may wish to put in place include SRI (Sub-Resource Integrity) and CSP (Content Security Policy) to have tighter control over the third-party scripts that you allow to run on your website.
You can learn more about CSP and SRI by checking out some of the articles on Scott Helme’s website.