
Beware if you’re paying your bills for local government services – the payment information you type into that web form may be heading straight to cybercriminals.
Security experts at Trend Micro report that they have identified eight cities in the USA where online payment portals have been compromised to host Magecart-style credit card skimming code.
Magecart is a family of Javascript malware used to steal credit card details and personal information from unsuspecting internet users as they interact with websites – often as sensitive details are entered to make a purchase.
What makes this type of attack often more serious than a conventional data breach, is that most companies do not store your full credit card details, such as your CVV security code. But those details are entered on online checkout forms by consumers, and can be stolen by a malicious script hidden in the website’s code.
As Trend Micro explains, the common factor between the affected websites they have uncovered is that they all use the third-party Click2Gov platform:
These sites all appear to have been built using Click2Gov, a web-based platform meant for use by local governments. It is used to provide services such as community engagement, issues reporting, and online payment for local goverments. Residents can use the platform to pay for city services, such as utilities.
According to the researchers, the attacks against the eight unnamed US cities started in April, when malicious Javascript code was planted on the websites, silently harvesting credit card details and residents’ personal information as they entered it into online payment forms.
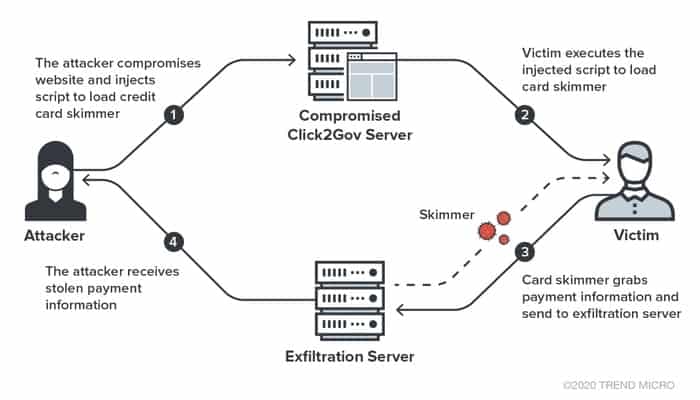
Unlike other skimmers which grab data on various types of payment forms, the skimmer used here is rather simple and only works on a Click2Gov payment form. No obfuscation or anti-debugging techniques were used. The skimmer hooks the submit event of the payment form; when a victim clicks the button to send the payment information, the skimmer will grab the information from the selected columns inside the payment form and immediately send the collected information to remote server via a HTTP POST request.
Details exfiltrated by the script to a remote server under the hackers’ control included credit card numbers, CVV security codes, card expiry dates, cardholder’s name, address, and postal code.
Simple the skimming code might be, but that doesn’t mean it’s not effective.
Rightly or wrongly, Click2Gov is earning itself a bad reputation. In recent years security researchers have been tracking attacks launched against the Click2Gov payment portal, with reports of breaches involving city websites stretching across the United States and Canada.
Late last year, for instance, the city of College Station admitted its Click2Gov online utility payment system had been hacked for some months, as had the City of Waco’s Click2Gov portal for water bill payments.
The onus is on cities to follow best practices when building and maintaining its online payment systems, ensuring that patches and security updates are applied in a timely fashion and that networks are properly secured.
Meanwhile, other websites with payment forms online would be wise to remember that credit-card skimming attacks are not limited to local governments taking payments from residents.
Magecart-style attacks have been seen hitting a diverse range of victims, including hotel chain booking websites, academic campuses, as well as the likes of Ticketmaster, British Airways, Forbes, Umbro, Vision Direct, and Newegg.
If you’re making online purchases (and hey, these days, who isn’t?) you might want to investigate disposable virtual payment cards, so you’re never exposing your real life credit card to the websites to which you are making a payment. A virtual card could be locked to a single merchant, have a limited amount that can be used in a single payment, or be single-use.
There is more discussion of virtual credit cards in this episode of the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Hello, hello, and welcome to Smashing Security episode 182. My name is Graham Cluley.
It's Host Unknown's sole founder, Thom Langford. Hello, Thom.
I listened a couple of weeks ago and you said something about having guests on who are less security-minded and, you know, don't have any expertise in security.
And lo and behold, here I am.
And there've been a fair few mentions of Carole and myself on the podcast. Although you seem to refer to it as Graham's podcast.
Now stay tuned at the end of the show for a special feature interview with Robert O'Brien of MetaCompliance.
Not only does he share some great info on onboarding staff into better cyber awareness, but he has quite the dreamy voice. He does, let me tell you. ROBERT O'BRIEN. Hello.
And I'm looking into how we can make it harder for credit card hackers to dupe us. All this and much more coming up on this episode of Smashing Security.
I want you to imagine this scenario. Imagine that you personally suffered a security breach. Okay? You leaked data in some way. What would you do?
This is when I still had a manual leap over the desk and almost ripped the machine off the desk.
Make sure you don't do it."
What's your recommendation? Thom, I guess it's still transparency and honesty.
I hope you wouldn't send in the lawyers.
I wrote about this UK security vendor who I'll probably bleep out, actually. I'll probably redact them from the podcast, but the name is Keeplabs. I wrote about them.
Bob Diachenko, who's an extraordinary security researcher, he's always uncovering massive databases that have been left exposed online, unprotected with even the simplest password.
He came across a database containing more than 5 billion, with a B-B-B-B, records.
I imagine they were collecting data about past data breaches, but they then accidentally exposed it in some fashion. Right. So I wrote about them and I named the company.
And what I noticed over time was that that company's name, which had been reported in other places on the internet, began to disappear mysteriously.
Suddenly no one was naming the company. And then I received an email from this company saying, "Ah, hello.
Can you please update your article to remove our name from it because it's inaccurate and it's bad for our image?" You know, Graham, this is not the only time this happened last week.
Oh, really?
And they were unable to answer any questions I might have regarding the editor and the writers being made redundant.
Because I would love to fix it. I don't want to have inaccurate information up there. And they said, well, none of our customers were involved in the data breach.
And so I said, well, I didn't say any of your customers were involved in the data breach, so I haven't got any words to fix about that.
And they said, well, it wasn't really a breach because this was data which had already been breached.
And I said, well, I think that's still a security breach because people can find it that didn't have access to it before.
Yeah, you facilitated potentially— who knows if it actually happened or not, but potentially other people may have been able to access that data because you handled it.
Carelessly in some fashion.
And I said, well, that's fine, but you know, if you've got something to say, please let me know and I will put it up on the thing.
Or if you've got any refutation or any statements you'd like to officially make, I will post it up on my article so that you can have your position. And they didn't want to do that.
They didn't want to give me any statements whatsoever.
But what they did do is they said, oh, and by the way, maybe you'd like to work with us on some business opportunities in future.
Before we discuss any other sort of business.
Next thing I knew, I got a letter from their lawyers telling me to take down their name and redact it and saying it was bad for their company and all the rest of it.
Now, I believe I haven't said anything inaccurate in that blog post, right? And I've given them a chance to have their say as well.
But what I didn't want was I didn't want to get bogged down in lots of legal arguments and letters where only the lawyers are going to get rich.
And this could go on for months and months and months. And who frankly gives a damn about it.
And in fact, what I did was I redacted their name, so I replaced it with black blobs.
And I said, you know, I apologize to readers, but, you know, I can't afford to get into a legal fight.
Now, that did have an unforeseen consequence which I couldn't possibly have imagined would happen.
There were people on Twitter who were able to determine what the company's name was.
In fact, apparently over 100,000 people saw the tweet and it was— there were lots and lots of comments on it.
I haven't commented on my tweet or anyone else's comments regarding it or liked—
I do know that Javad Malik of the Host Unknown podcast, because he spoke about it on his latest episode, folded like a pack of cards. He was contacted. He hadn't written about it.
He actually used the term breach because let's face it, nowadays it's kind of a generic term, really, a bit of a catch-all for anything that's been lost or not secured or whatever.
He mentioned that, and this particular company in question reached out to him and said, take your comments down. To which, you know, Javad said, I can't, it's not my article.
I suggest you contact the publisher, the owner of the article. And he also said, you know, as a courtesy, I have contacted them to ask them to review it, but I can't do anything.
And then they basically then came back threatening legal action, at which point he said, speak to my lawyers, and left it at that.
And how is it used? That's the only—
What it is, is putting it out there again in another easy-to-find format on the plain, regular internet. So that even more people can get access to it.
Done.
It was an Elasticsearch database, I believe, which ships and installs with everything security-wise switched off, as I understand it.
And we get it as security professionals, we get it. You know, switching security on is difficult because it limits functionality. It can slow things down in some cases.
You know, it's difficult. But if you are a security company, you need to have your shit together.
You've got to, you know, you've got to have these processes in place that make sure that anything that faces the internet or anything that contains personal or confidential information needs to go through a hardening script of some kind, be it automatic or manual.
And if it doesn't work for some reason and you get found out, then tell us why it didn't work and what you should have done so that we can all learn from it.
I think transparency, honesty, prompt response to these kind of incidents means that, you know, when something bad happens, it doesn't have to be as big a deal as you can make it by responding badly.
And we know this because, you know, many of us in security roles have experienced this when other companies register domain names that are either very close to your company name or they are the same but with a different, you know, .com or .co.uk at the end and start impersonating you.
And this is a big deal. And as a result, there's a whole sort of almost a sub-industry of, you know, brand management.
And when you register a domain, it will— you can automatically get similar domain names registered.
There are services that search out to see if there are domain names that are registered with you know, Cyrillic alphabet characters, but still looking like your domain, et cetera.
So the US a couple of years ago, or Mr. Trump, announced Space Force, the fifth wing of the US military.
He's just sitting in the background, "Oh, I want to get the laser guns." I don't know, but bottom line is he watched Moonraker, James Bond's Moonraker, and decided that's for him.
So they've yet to get involved in any kind of serious operations. They've yet to launch anything. They've kind of just been bubbling under.
They're probably still deciding what sort of camouflage they should have on their uniforms.
But it just strikes me that it doesn't matter how big your organisation is or how well-funded it is.
And let's face it, the US government has got to be kind of up there, size, complexity, and amount of characters.
But yeah, I just find it amazing that such basics like this, it's a bit like when you hear that somebody forgot to renew their certificates for their domains and stuff like that.
I find it just stunning that such basic stuff is not being done. I would imagine US Army is probably trademarked or copyrighted or something.
Which I'm— because I'm looking at—
In fact, I have someone else in my household who does most of the shopping, so I think they may have a credit card, but I don't.
I'm trying to explain it to the listeners too, Graham. It's a radio show, right? So it's not just about your knowledge.
Sometimes you have to pretend you don't know stuff to make it fun.
But with a creditor, you share responsibility and you can say, you can sometimes claw money back from it from your creditor if you can prove it wasn't your fault.
So always purchase a credit card.
I have peppered my story with a few jokes, which I got off the internet while looking for credit card jokes. Okay? And that is how we're gonna keep this light.
People are setting up new online accounts, registering their credit card details with them willy-nilly because guess what?
They can't go to the bank and they can't go to the stores to buy the things that they require.
But others who are in the eye of the storm, you know, maybe jobless, or, you know, they're out protesting unbelievable injustices, or they're, you know, and they're staving off the bills with credit card payments.
Okay, joke time, right?
Online shopping is up, and April saw a 200% jump in new mobile banking registrations, and mobile banking traffic rose 85%.
And we're not surprised by that because people are locked at home.
So since the corona shutdown, the US economy, Fidelity National Information Services, they're a fraud monitoring services for banks, have seen a huge jump in credit card scams.
That's how bad the numbers are.
So phishing, phone, SMS scams, the whole nine yards.
And one pundit said, while your day job may have gone up in smoke or become way more difficult, the hackers' day jobs just got a whole lot easier.
So you might get an SMS or an email that says, hey, free Netflix for a month or 3 months or 6 months.
Now, the reason this is hard for people to spot is because Netflix and other service video companies are offering incentives to get more users.
Oh yeah, there's loads of people that have filed for legitimate stimulus checks coming in from the government.
So what if you get a phone call or an email, someone purporting to be a bank or government official, right, saying we need to get some more information to make sure you get your check, or we just want to double-check your postal address, we get the check in the mail for you.
Ironically, I saw on Twitter that people are mistaking their stimulus checks for junk mail or a scam because I don't know if you've seen what it looks like.
And it also has Donald—
I am getting legitimate text messages from my bank saying, "Hey, we're gonna freeze your interest that you owe us during this period."
You know, don't click here, please.
If the communication includes a link, many people will use the link in the communication or told to them down the phone rather than finding out what the real link is.
Instead, work out what the real link is and go to it directly on your computer.
One guy on Twitter was saying that he keeps getting calls, and the way they start the call off is, 'Credit card services, how are you doing?' And then they offer to lower your credit card interest.
So of course, many of us had plans for the summer, like perhaps we are renting a vacation home or going on a flight or doing something with the family, and some of us have had trouble getting money back from those things.
Emails saying, "Here's your Airbnb cancellation. We just need your banking details to refund your card," could also work pretty well. Okay, it's getting bleak.
You need a joke, don't you?
Now before I get into advice, the reason I wanted to bring this up today is because you guys are both smart and you will have better advice than the advice that is given on the official FBI credit card fraud site.
So every time your bank number or credit card is used for a purchase, you get a secondary notification that tells you, hey, your card has just been used.
I know it makes everything a little bit faster, but actually it's much safer not to save it with a bunch of different companies out there.
And you can also use things like either PayPal or Apple Pay or Google Pay.
These might be a smarter way to be able to manage your money because then you have a kind of an account you can manage.
That's a great idea. I've also heard some people use, are they called virtual credit cards? What's the name of these things? Do you know about these, Thom?
So you get either a virtual credit card, which is you've got your regular card, but then your app will generate a virtual card, so you don't actually get a physical card, and you can use that for all your purchases, say, at Amazon or John Lewis or wherever.
And if something happens to that card, you can just delete that card. You don't have to apply for a new card because you've obviously still got your credit card.
But you can also get disposable cards as well, which are good for one shot. So you create a card, use that number for your purchase, and then that card is immediately destroyed.
And this way, you follow the rules and at the end it just goes poof and they can't hold you for money.
I don't know if this will work or not, but this one guy called Deldy on Twitter said he's been getting way more scam calls recently, so he's been opening with the line, "Hi, I was actually wondering if I can share my Social Security number and credit card info before we move any further." And apparently they instantly hang up.
So anyone who's inundated with calls, try that one.
In the guide, you will learn what cybersecurity awareness means for your organization, how to implement a cyber risk awareness campaign, the critical role of policies to establish safe baselines, how to maintain momentum and staff engagement, 10 cybersecurity awareness best practices, and oodles, oodles more.
Grab a free copy of the Cybersecurity Awareness for Dummies book from MetaCompliance now. More at smashingsecurity.com/cyberaware.
LastPass by LogMeIn is a password manager both for consumers and the enterprise.
In a company, you get extras like central admin oversight, controlled shared access, automated user management, and everything is protected with multifactor authentication.
Learn more at lastpass.com/smashing. Oh, and if you're a home user, LastPass is available for free, so check it out, lastpass.com/smashing. Back to the show.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish. Doesn't have to be security related necessarily.
He is the inventor of the Iain Knot, which he claims is the world's fastest way of tying your shoelaces. He also has an app for Android and iOS.
If you want to learn over 60 different ways of lacing your shoes, then his app is the one that you want.
Now, this is an extraordinary website all about shoelaces and how to tie your shoes, which is incredible.
What I find particularly astonishing is that Iain admits he doesn't actually give a shit about shoelaces, but he wanted to be the best at something and produce some corner of the internet, which has been there.
And that's what he's done. He's built this. His website gets over 9,000 visits per day, which is quite a lot when you consider it's all about shoelaces.
I would call on to our more avid listeners to see if they remember which episode that came out of, because I don't remember.
Just a little bit.
And what it does is it allows you to very quickly and easily resize your windows.
Now, you might think that's not very useful, but you can drag a window to the top left-hand corner and it will automatically size it to a quarter of the size of the window.
You can drag it to the left and it will be half of the window. You can drag it to the very top, it'll be the whole page.
And there's also lots of keyboard shortcuts that allow you to pick it for an eighth or for a third or different locations, etc.
And in this age of very high-resolution monitors and all that sort of thing, and I've got, you know, two 5K monitors in front of me now, I can actually end up with 8 different windows of apps open at any one time, all nicely positioned.
So some are vertical, so, you know, Twitter and Signal, etc. Some are vertical quarters because they scroll up and down. Others are, you know, regular quarters.
So yeah, I was going to choose that as my pick of the week, but instead I thought I would, in a last-minute fit of ego, I thought I'd mention the Host Unknown podcast, which I think everybody really should be listening to.
So, there's— the central character is Lily. She's played by Sonoya Mizuno. She's played in other of Garland's films and works. Basically, she works at a kind of Google-like complex.
Her boyfriend works there too. He goes missing. Oh my God, yes! Did you watch it?
They tease you, drip feeding you a little bit of information of what's going on in there.
Plus, they have the coolest statue ever in the kind of campus, which I just think we should litter the entire planet with them as a reminder of what kind of future we want to build.
So, I say watch it. I watched the entire thing in two nights. Loved it, loved it, loved it. Geeky, dark, beautiful, smart. Well acted.
What's the best way for folks to do that?
And don't forget, if you want to make sure never to miss another episode, subscribe in your favorite podcast app such as Apple Podcasts, Spotify, or Pocket Casts.
And why not leave us a nice review as well? I always love reading those.
And don't forget, stay tuned after the show for our special interview with Robert O'Brien of MetaCompliance with the smooth voice.
Check out smashingsecurity.com for past episodes, sponsorship details, and information on how to get in touch with us.
Because that's how you test— I don't know if people know that, but that's how you test an accent to see if it does anything to your knees or not.
Get the person to say palimpsest, and if your knees kind of go a little bit weak, you are a sucker for that accent.
So we have a very special guest, a new guest, someone who hasn't been on the show before. I'd everyone to meet Robert O'Brien from MetaCompliance.
Robbie, thank you so much for coming on. ROBERT O'BRIEN. My pleasure, Carole.
I think, Carole, I've been a John the Baptist, a voice crying in the wilderness for, oh, I think about 15, 16 years.
Was really focused on the people aspect of security and data protection. And it's clearly the hardest piece of the jigsaw. People are difficult.
But unfortunately, I've become fascinated with that. And I've worked with a lot of companies who have tried to increase the vigilance of their teams.
And really, about 8 years ago, as phishing became prevalent and ransomware, this became a clear and present danger.
But I found that there wasn't any guides to how do you go about dealing with the people aspect of it. Where do you start?
And it was a surprise to me that when we engaged with organizations, one of the first questions is, well, what do you do? How do you start?
They hadn't really taken cybersecurity awareness or the culture change around security as a business as usual issue before.
And that really led me to go and write the Cybersecurity Awareness for Dummies book.
And a colleague thankfully edited out the more crazy things that I was trying to put into the book.
And it's totally focused on how a company can help get employees on board to be safer and help protect the company and themselves. Is that fair? ROBERT O'BRIEN. That's fair.
And I think we have condensed all the learnings and low-hanging fruit and approaches that we've seen organizations use to move this along and really brought it into an easy-to-use playbook.
And if you reach out to us, we can also send you a physical copy, which interestingly is an excellent way to get those Luddites within your organization to move forward where they have a physical book in front of them and they'll actually read that more than go and read a PDF.
There's some really, really good information. Maybe we can start with the idea of what motivates a hacker. ROBERT O'BRIEN.
I think that there are as many different types of hackers as there are people.
And I think that every time the human race has come up with a brand new way of commerce, there has always been piracy.
When the Americas were opened and we were transferring goods between the Old World and the New World, you had this blossoming of piracy, Pirates of the Caribbean type thing.
And hacking is no different than that. It's really a way of people gaining advantage, mainly for money. In my experience, that is the great motivator.
There are certainly other issues, political, national players. And so you find that it's a very, very complex issue.
Then we have businesses who are going about their mission involved in what they've been doing typically for a very long time.
And we have this brand new backdrop, and they find themselves really at a disadvantage. And the hacker spends months possibly thinking about the organization.
The organization wouldn't necessarily be thinking months on awareness or security.
The demands of the day, the crises of the day typically distracts them from approaching this problem in a more systemized fashion.
I remember when I used to work in the corporate land, even working in cybersecurity, in a cybersecurity company, you could still see plans always fall off for immediate reactionary job that everyone had to be all hands on deck.
So do you find that people have good intentions with awareness, but sometimes just don't do their homework or don't actually follow through? ROBERT O'BRIEN.
Cybersecurity culture change is a change management project. And I don't think there's any organization out there that hasn't seen change management projects really crash and burn.
I think everyone's history is littered with the failures of those things. And the problem is that you really require two things.
Number one, you require the leadership team to be 100% behind it and give it the resources that it needs.
And the second thing is that the organization is braced for the long term because change takes time.
And in my opinion, to move the needle substantively for cybersecurity takes at least 18 months. Possibly 2 years, because you have some real hardened attitudes to change.
And the minute that people see a wavering of the commitment from senior management, the whole thing falls apart like a game of cards.
And I find a lot of companies kind of say, oh, you can do this overnight. It's not an overnight job trying to change a culture within an organization.
And two, you're absolutely right. If you don't have absolute buy-in from the senior management team and if they are kind of cutting corners, that's not a good thing, right?
ROBERT O'BRIEN. It's not a good thing. And I also think that unfortunately, so up until now, cybersecurity doesn't make you profit. It doesn't get you revenues.
And therefore, it was seen as an IT thing. Now, interestingly, that's changing massively.
And I've seen it change really from the introduction of GDPR, where within the supplier contracts that every company uses as an engagement mechanism, you now have a couple of things that have come to the fore.
Number one, you have cybersecurity insurance. Ten years ago, that was unheard of. But now, what is the level of liability that is covered by your cybersecurity insurance?
The second thing is, where does the liability sit for GDPR? Who is responsible for a data protection failure and who takes the liability?
And the third thing then is you get a risk assessment from your potential customer and you have to fill in that risk assessment.
Now, before GDPR, that was largely a box-ticking exercise.
But now the risk assessment will be called upon to defend the decision to go with that vendor, that vendor selection as part of an overall privacy lifecycle.
And also the lawyers are heavily focused on it.
So really having high levels of cyber hygiene, high levels of being able to demonstrate your cyber credentials now becomes a competitive advantage.
Having ISO 27001 now becomes a competitive advantage.
And I think going forward, that is going to become more and more a feature of how people look at cybersecurity, the people that they deal with, but more importantly, I think will justify the spend that's needed in these type of projects.
Lots of IT teams have been culled or have had to deal with resource issues on that front, plus they're having to manage a whole new workforce working from home, and they want to keep it safe.
So obviously, you wrote this before all this happened, but did you touch upon remote working? And do you have any views on that? ROBERT O'BRIEN.
In the industry, we have seen the incidence of phishing and cyber activity just go through the roof.
And the reason for that is that people involved in cybercriminal activity love change.
They love different things happening to us as human beings so they can exploit the moves between working in an office, working from home, people not being within their social circle and things like that.
The issue is vigilance. The issue is then having messaging or having a subject on a monthly basis that you address to your audience.
So for example, a lot of our clients who take this really seriously immediately switched to secure remote working, immediately began sending out training based on the dangers of working from home, the increased levels of people trying to cajole you to do things that you wouldn't normally do in the office.
And they increased their vigilance. Those companies also continued with their simulated phishing attacks.
And then some people just killed them off altogether, saying, oh, you know, our staff are dealing with working from home, they're having a bad time, and they stopped.
Some people stopped simulated phishing.
And my view there was, well, in actual fact, that's what the hacking community is betting on you doing, betting on your change and the fact that everybody is disarranged.
And so I think the people that did continue with the phishing attacks actually increased the vigilance in this new environment, which is likely to continue in some form or fashion well beyond COVID.
So let's say I'm an IT guy and I really want to get through to my CEO, right? They're just not taking this seriously.
They've cut my budget, they've cut my resources, and I really need them to see the importance of cybersecurity.
Do you think a better approach is to go in with a bunch of stats to explain how dangerous it is out there?
Or do I want to talk more about how the company can grow and make more money and be safer, more secure? Lower risk. ROBERT O'BRIEN. I mean, I really feel for people in that situation.
Now, if someone had told me before Christmas that my entire organization would be working from home, all these controls would have been put into place, I wouldn't have believed them.
But now I am prepared to believe much more in terms of change. Change and the world that we lived in.
So getting someone to believe that we could have a cyber event that could cripple the organization, I think, is easier to believe. So I think that envelope expanding will help us.
Because of the change in environment, there's inherently a little bit more risk there until they can lock down both security and cyber awareness for home workers.
So this might be the time to say, look, the environment's changed. We need to be on top of it to make sure we're safe. I don't know. What do you think about that? ROBERT O'BRIEN.
Look, people have gone home. And we implemented one of the biggest changes in organizational working in centuries.
We did it in weeks where normally that would take months or maybe years for organization to put it into place and you would train everybody and so on and so forth.
But we flicked the switch and we got it done.
The other thing is the digital assets that the organization rely upon now exist within those homes, now exist within those firewalls within those homes and rely on people within and indeed rely on their families, not just the people that work for you, to be aware of the dangers and aware that certain things could happen.
And the only way to do that is to engage with your staff population and give them the information and give them the resources to actually make the change.
Because thinking it'll happen by osmosis is naive. It just won't.
And what has happened whilst there are many benefits from homeworking, from a security perspective, our perimeter has just morphed into something that is unrecognizable now.
At first, I was thinking this is really, really good for IT staff to understand what they're facing and how they can get their hands around all the different components.
But maybe, maybe, you know, maybe I was blindsided.
Maybe C-levels need to read this too, just to understand all the different components and the complexities that need to be understood so that they can be more sensitive when they're budgeting and dealing with IT.
ROBERT O'BRIEN. Carole, I mean, you've hit the nail on the head.
I mean, when I was writing this book, I sort of had an image in my mind of a CISO at a board meeting with a number of these books and basically handing them, physically handing them.
So, you know, I have the power of a gift. Here's a gift. And it's a Wiley book that we've all seen, The Dummies Guide.
And even if someone dips in and out of it, you've already made an impact. Because I think if you can get the C-level, the executive team on your side, you can change so much.
Because the problem I find with cybersecurity is that it isn't user-friendly. It involves implementing controls.
And people hate controls and they hate policies and they hate e-learning. So it's not a popular job.
But once you get the C-level involved, you get a tone from the top and people never focus on that. What does our organization stand for?
Do we have zero tolerance on these things or are we laissez-faire? Where do we fit?
And once the people in charge say, this is where we stand, then your initiatives are not diluted by middle management.
Someone who goes, look, don't bother with that e-learning, keep doing your jobs, get around to it whenever.
And suddenly your awareness campaign has just died because you have a manager somewhere who is just not supportive.
But if the CEO is supporting the actual initiative, you typically get people to buy into it.
Thank you very much, Carole.
That's smashingsecurity.com/cyberaware. See you next week.



