
Owners of hardware Trezor cryptocurrency wallets should be on their guard after an email was sent out by thieves attempting to dupe them into downloading new software to their devices.
The emails claim that Trezor, which has been making physical USB-connected devices to protect the cryptocurrency and tokens of users since 2014, “experienced a security incident” yesterday that breached the data of 106,856 of its customers.
Here’s a screenshot of the email, which has the subject line “Your Trezor Suite might be compromised”:
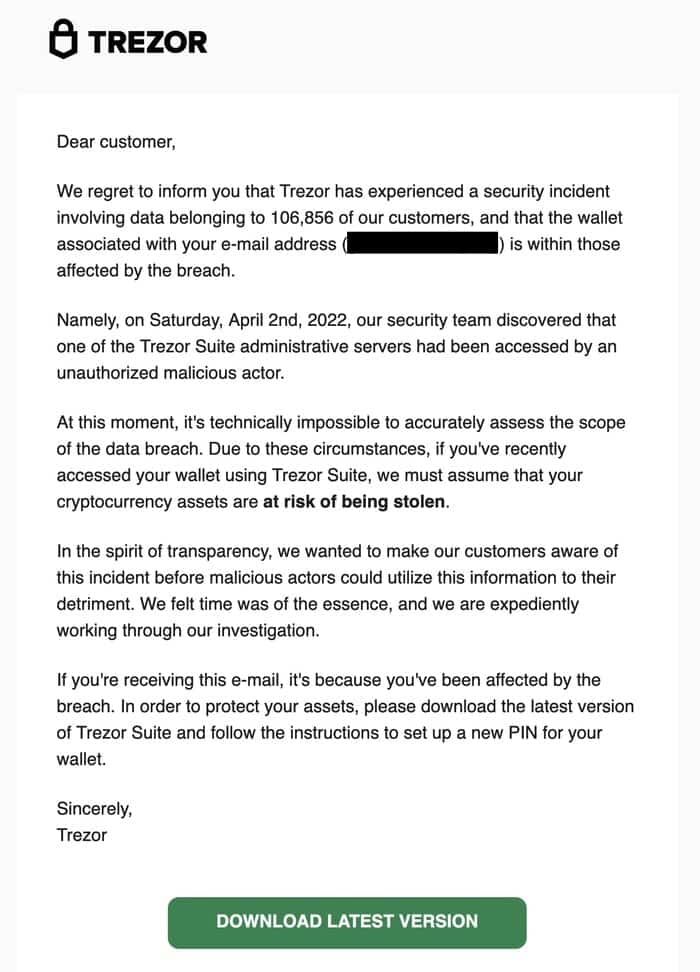
Part of the email reads:
At this moment, it’s technically impossible to accurately assess the scope of the data breach. Due to these circumstances, if you’ve recently accessed your wallet using Trezor Suite, we must assume that your cryptocurrency assets are at risk of being stolen.
However, in reality, the email is not from Trezor at all – but is instead an attempt to dupe unsuspecting owners of Trezor devices into downloading a bogus version of the company’s desktop suite software from a lookalike website.
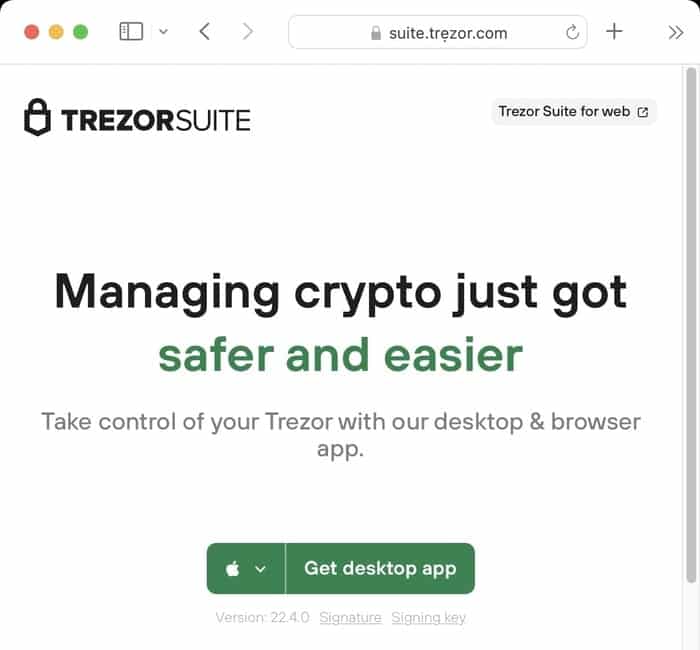
If you were unfortunate enough to click on the link offered in the email you would find yourself taken to: https://suite.trẹzor.com
Notice anything odd about that? Take a closer look.
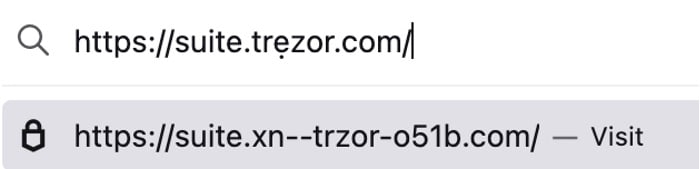
Now you’ll hopefully notice that there is an underdot under the letter “e” in “trẹzor” in that URL. And that means you’re not going to the real Trezor website (which is at https://trezor.io – the real domain is not even .com!)
This is known as a unicode domain phishing attack.
So, don’t trust the email. Don’t click on the link. The genuine Trezor Suite doesn’t ask you for your wallet’s private keys and doesn’t store them online, but who knows what this bogus software might ask you to do.
If you do want to update your Trezor’s firmware or desktop software, go to the official Trezor website instead.
One question remains – how did the malicious email get sent to so many Trezor customers? Is it possible Trezor, or one of its marketing partners, has suffered a security breach that has exposed members of its mailing list?
Update:
Trezor says it is investigating whether an opt-in mailing list it runs at MailChimp may have been breached. That would certainly explain how Trezor customers were targeted.

Sources inside Trezor tell me that this “was an inside job by a MailChimp rogue employee.”
That’s how they targeted Trezor users in this highly-convincing attack.
Hear more views on this incident in this episode of the award-winning “Smashing Security” podcast, with me, Carole Theriault, and special guest Zoë Rose.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Smashing Security, Episode 269: Trees or Deep Throat, a CCTV Stalker, and Amazon's List of Banned Words with Carole Theriault and Graham Cluley.
Hello, hello, and welcome to Smashing Security, Episode 269. My name's Graham Cluley.
And the other big news with you, of course, is that since you were on, you've had a child.
Now, coming up on today's show, Graham, what do you got?
Drag myself out from under the duvet.
Do you know what a Trezor is?
And what you do is you store your cryptocurrency wallet on it.
So if you don't trust online cryptocurrency wallets, brackets, you shouldn't trust online cryptocurrency wallets because they're getting hacked all the time, then you might choose instead to store it on a USB stick via one of these things, which stores it securely.
Now, I've only got about £5 worth of cryptocurrency.
But I received this email, which appeared to come from Trezor, and it said, "We regret to inform you that Trezor has experienced a security incident involving data belonging to 106,856 of our customers.
And the wallet associated with your email address is within those affected by the breach." Because you have often talked to people about using hardware wallets, right?
Absolutely, I think if you're going to dabble in cryptocurrency, it's probably the sensible place to store your wallet as it makes it more difficult for hackers to break in or access it.
And this message, which looked pretty legitimate, said that hackers had broken into Trezor's admin servers the day before, last Saturday.
And they said, we're looking into this data breach, but we think that there could be a problem for you.
So you need to update the desktop piece of software on your computer called Trezor Suite, because otherwise your cryptocurrency assets are at risk of being stolen.
Now, obviously, at first I was thinking, well, it might be real because I do have a Trezor device. So they may well have my email address when I bought it.
And I clicked on the link in the message and it took me to what appeared to be the Trezor site. And I thought, well, this is quite a good story.
I thought I should write this up for my blog, quite interesting if Trezor have been hacked.
And I looked online and genuine Trezor customers are saying, I've received this, what on earth is going on? And my spider senses, I've got spider senses.
My spider senses were tingling.
So I look at it on my phone and it looks like it's taken me to suite.trezor.com. And I thought, okay.
And I took a really close look, which isn't easy with my eyesight on a tiny little iPhone SE.
Anyway, so I wrote about this on my blog, 'cause I thought, "Ooh," I thought, "No one's really—" I thought, "That definitely isn't the real Trezor website.
I don't know what it's downloading, but I thought this is dangerous. I need to warn people, 'cause people are believing this." And so I posted a warning up on Twitter and on Reddit.
I linked to my story on my blog, and I found other people had also been posting on Reddit saying, "Hey, I've received this email. What's going on?
You know, it could be a bit dodgy." And what was interesting is their messages on Reddit were being downvoted. Someone was choosing downvote, downvote, downvote, downvote.
Who has a vested interest in downvoting a warning about an attack against Trezor users?
My website was slowing down a lot because as I was trying to update my story about this attack, my website began to time out. I thought, that's not normal. I'm not that popular.
But I thought my website should be able to handle this. And so I thought, okay, well, what I'll do is I'll just drop a line to my web host.
So I log in to them, the people who manage my website for me.
And I thought, that's a bit of a coincidence, isn't it?
So I've just written about this attack and suddenly my web host has gone down and my hosts are not in the habit of going offline.
I thought, wonder if someone's trying to silence me, just like they're downvoting these other messages on Reddit.
And now they've got something set up to send off a DDoS. That's interesting.
So I went back on Reddit and what I noticed now was that my warning about the scam email, the one which was linking to me, suddenly been massively downvoted by persons unknown.
So I thought, okay, there's definitely an attempt to stop people from hearing about this attack that's going on. Did you take to the streets, Graham?
There was nothing on their site, there was nothing on their Twitter account. And I wondered out loud in my article, how was it that Trezor customers had been targeted by this scam?
You know, had anyone who wasn't a Trezor customer received this email? Had someone hacked Trezor or maybe hacked the service that Trezor used to send out the emails?
Maybe Trezor didn't have two-factor authentication in place on their mailing list or what's going on? And it was about now that someone from Trezor contacted me.
And he said, look, you know, stop speculating. He said, we haven't done anything wrong.
He said to me, what's happened is that Mailchimp, the mailing list service that we use, they are responsible.
He said, it's a rogue insider at the firm who has hacked our account and stolen our addresses and is spamming people. And I said, ooh. And he said, can you update your article?
And I said, well, I can't update my article at the moment because my site's been DDoSed. I can't log in.
He said, but I don't want my name in it because our official CTO, he's going to want to say something about it and I'll be jumping on his toes.
I was able to eventually update my website, although it was still very slow to say Trezor saying, it's not them, their Mailchimp account got attacked by an insider inside Mailchimp.
And on Monday, Mailchimp said that their service had been compromised targeting crypto companies.
And it's unclear a little bit as to whether it's a Mailchimp employee or whether a Mailchimp employee had their account breached.
But what Mailchimp are saying is that a hacker accessed internal tools at Mailchimp, accessed over 300 Mailchimp accounts used for sending out mailing lists for companies in the cryptocurrency and finance industry.
So not just Trezor, but hundreds of other companies. And the hacker ended up exporting the mailing list for over 100 of those mailing lists to do whatever they wanted.
There may be subsequent attacks which are gonna happen, which may look like quite plausible messages from your crypto company or your crypto wallet firm or whatever it might be, trying to trick you.
But I did hear from people who said they had literally had their entire cryptocurrency investments absolutely raided, and so they have nothing left. And some people— Really? Yep.
Some people told me that they lost everything over the weekend. And what a poop storm as well for Mailchimp.
Well, yes, obviously a lot of companies who have been affected by this breach are going to be concerned.
And I would hope that those crypto companies are going to be contacting their customers and saying, look, your details may have fallen into the hands of hackers, so be on the lookout for phishing attacks and who knows what.
And I'm not going to lie, if I was a cryptocurrency company, I wouldn't probably value Mailchimp that high on my making sure that they meet, you know, some security standard.
So I could see that there's a bit of a gray area of who's going to be held responsible. One, Mailchimp, did they have the right controls?
Two, the cryptocurrency, did they do their due diligence there?
It's unclear whether it may have been a legitimate employee who was socially engineered maybe into giving access to someone else. Yeah, totally.
Yeah, which is— It's a gray area for sure, but clearly less than ideal. What's going on?
They broke up and he was not too happy about that, and he had previously installed her CCTV system and was watching her on it.
And even worse is he took pictures of her flat and then when she came back, sent them by email to her. Without context, just pictures of her flat.
But when he was interviewed by police, I think he originally had said he had been sent them by somebody and he was sending them on to her because he was concerned for her safety, but he obviously admitted to being the one that took the photos and sent them later when he was interviewed by police.
Unfortunately, I've been in a very similar situation. I won't give the full details.
It wasn't CCTV and it wasn't photos of the flat, but it was access to one of my accounts, and there were pictures involved. I'll give that detail many years ago.
And so I've been in that lady's position. And it's a sense of control. It's not even— a lot of people were like, well, that just doesn't seem logical.
Why would he take those photos and then send it to her? Because he's clearly showing he's done something.
If only you had a big manly burly boyfriend who could protect you from this person who's breaking into your house and taking photographs.' Do you think that's the thinking?
It's not logical.
In some cases it may— Graham, you may be right— it may be, look, I could have protected this, or look, you're extremely vulnerable, but it also is, you know, I can still control you.
Even, for example, in my situation, the person had access to my email account. I knew how to get him off of it.
I knew how to check if he still had access, but it's still terrifying because what else does he have access to? Our lives are so online. In her case, it's her bloody CCTV.
I think they actually say in the article she had unplugged it knowing he had access to it.
When he went in when she was on holiday, he plugged it back in, which is how she knew he was in the flat.
I can understand if you've shared your email password with somebody and you've then broken up— you shouldn't probably share your password anyway, but if you have done, obviously change it.
But are there other rules and guidelines and pieces of advice you can offer people?
Sometimes it's actually leaving their access because it can escalate, especially if they have intimate access to you, like they're in your home, right?
But if it's that you have physically left the situation, most of the time the advice I give is start over, get a new account or get a new phone.
Because you never know, especially if you're not a tech person.
However, when it comes to things like, you know, you're a bit more confident, maybe you have an organization like Safe Escape to support you.
It would be things like ensuring MFA is in place, multifactor authentication, ensuring you have a strong password. In my case, I did not give them that password.
Actually, it was so long ago, I don't even know how he got it. But I'm a security person and I made a mistake and he got it. No matter how much you do, this can happen.
It's just being aware of what information you have online and also being aware of what information can be seen in your email.
It doesn't specify in the article how he got in, I'm making the assumption he had a key because it doesn't say he broke anything, but yeah, that goes to what's left over.
I remember years ago where somebody had put a camera up in their ex's house and the camera was in a private room, you know, so they want control, they want to use anything that they can, and they'll use things that you would never imagine, like CCTV accessing your email, or, you know, putting cameras up.
So it is scary, but I think the biggest thing is just knowing what you have in your environment, and I suppose figuring out if you can secure it or if you need to remove it.
I don't know if it's just from a female point of view, but the idea that you can be kind of terrorised, mentally terrorised in that way. And then it's not considering—
They made it sound like that was such a big deal.
Something like that, which will work really, really well. And we cause any problems in future.
They are the ones to make it as easy as possible for you to get up and going and running, not necessarily the best.
CCTV is closed circuit TV, I think is what it actually stands for, but that doesn't mean that it's actually doing what it's saying it's doing.
Because a lot of them, they're actually online, they're available on the internet.
So make sure that what you set up is actually doing what you think it's doing, not just that the default of is it secure, but also is it accessible for people that you weren't expecting, let's say.
You know, there's a lot going on there, but that doesn't excuse his behavior. Yeah, please don't be a horrible person. At the very bare minimum, please don't be awful.
Yeah, I'm with you.
And they interviewed something like 3,000 different business leaders.
And half of these leaders intimated that their company already requires or plans to require full-time in-person work in the year ahead.
All these stats are concerning, not just for employees, but for companies, right?
Both large and small, they have to figure out a way to work with strained budgets and a stressed-out workforce and a lack of resources.
And one of the big questions is, what can companies do to boost morale without breaking the bank.
There's various ways to cheer up staff, isn't there, in the office? I mean, you could hire some mimes, for instance.
Interesting, because the Harvard Business Review published an article recently saying this is how someone might boost morale if they don't have any financial kickback to offer, financial bump.
And one is public recognition. So basically McDonald's Employee of the Month kind of thing, right?
Because you can think, why has Bob Middleton been promoted as employee of the month when I know he's useless at everything, can't even carry wood, and he's just a waste of space who we need to get rid of.
And for some reason, the bosses have decided he's brilliant, and they have not seen the enormous amount of useful, positive work which I have done this month.
You know, you could be demotivated by that kind of scheme, couldn't you?
So you'd have, you know, Dear Zoe, we just want to say that you're such a star. Thank you so much for showing up every day and doing all the stuff you do. Signed, the CEO or someone.
Yes, they've got enough money to post you compliments and stickers, or they've got enough money to praise Bob Middleton and frame his photograph on the wall.
And one of those people is Amazon, right? Because they want a more innovative, more, you know, modern, approach to dealing with this type of thing.
So according to The Intercept, and this is according to sources on the inside, last November, Amazon top executives had a little chit-chat about creating an internal social media program.
And this social media program would allow employees to recognize co-workers' performances with posts called shoutouts.
It's just, you just want some money. Just pay me properly and then I'll be motivated.
Full disclosure, I'm motivated by money because I have a family and I would to eat. Absolutely.
Where you get virtual stars, not real ones, unfortunately, because that would be cool, but you get virtual ones and badges, which is practically a sticker, Zoe, practically a sticker for activities that add direct business value.
The underlying thing is you have to meet your employees where they are, and if they're starving or if they can't pay their bills, or if they're working to the point of exhaustion, I don't bloody care how many stickers you give them or digital versions.
They have enough money and don't understand why people aren't being, you know, so thankful that they bother to give them any money. Well, I don't know.
The kingpins here are going to keep employees happy and productive so they won't look elsewhere for work.
But let's assume this person at the meeting, I don't know, we'll call them Bob, right, Graham? Bob. Okay. Yeah.
They're like, "How do we stop disgruntled employees from basically complaining?" screaming on the internet, right? How do you do that?
Like, you know, because obviously negative blocking keywords—
Now I have to say Amazon have contested saying, well, you know, if this social network does go live, not all these words are going to be blocked.
And what they're saying is that it's called an "auto bad word monitor," quote unquote, and it was devised.
It's effectively a blacklist that would flag and automatically block employees from sending messages that contained inappropriate keywords.
And this is beyond obviously swear words or inappropriate language. These are kind of like the word prison, for example. Yeah. Right. Or ethics, interestingly, is in there.
I was thinking along the same lines, right?
So if I wanted to communicate in this intranet, "I fucking hate working here," what could I say instead?
But they didn't block the loo. So I really think just spell things in the British spelling and use a lot of parentheses.
I cannot begin to tell you how much I adore our overlords at Amazon and how they bring lightness and wonder to my life.
I would say something like, oh, you know, I had to miss my child's, you know, big development stage thing, but it's okay because working here is my favourite thing in the world.
Just something as simple as that because it sounds very positive. Yes, yes, I would definitely choose working here because I love it so much. They've got representation blocked. Wow.
They've really put some thought into this.
If any of you listeners want to see the list of words, I have a link to the Intercept article as well to a number of articles. Just let you know that all's great out there.
Everything's wonderful.
Collide is perfect for organizations that care deeply about compliance and security but don't want to get there by locking down devices to the point where they become unusable.
So instead of frustrating your employees, Collide educates them about security and device management while directing them to fix important problems.
Sign up today by visiting smashingsecurity.com/kolide. That's smashingsecurity.com/kolide.
Enter your email when prompted, and you will receive a free Kolide goodie bag after your trial activates.
You can try Kolide with all of its features on an unlimited number of devices for free for 14 days, no credit card required. Try it out at smashingsecurity.com/kolide.
That's smashingsecurity.com/kolide. And thanks to Kolide for supporting the show. So imagine this scenario.
You're out of the office unexpectedly and a colleague pings you because they need access to some system you have credentials for.
Now, listeners would never send passwords over email or Slack. But what about your coworkers? How many organizations out there are sending logins back and forth in plain text?
Worse yet, how many just store all of their logins on a shared spreadsheet?
We all know that human errors are the biggest threat to your organization's security, but did you know that weak or stolen passwords account for over 80% of all data breaches?
There are tools out there that allow you to share credentials, set access permissions, and monitor the data dark web for stolen logins.
Keeper Security's enterprise password management platform does just that.
Keeper locks down logins, payment cards, confidential documents, API keys, and database passwords in a patented zero-knowledge encrypted vault, and it takes less than an hour to deploy across your organization.
Sign up for a Keeper free trial for your organization today and get a free 3-year personal plan VPN. So get started by visiting smashingsecurity.com/keepersecurity.
That's smashingsecurity.com/keepersecurity. And welcome back. And you join us for our favorite part of the show, the part of the show that we like to call Pick of the Week.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website or an app, whatever they wish. Doesn't have to be security-related necessarily.
Better not be. Well, my pick of the week this week is a little bit security-related because we have discussed this case on the podcast in the past.
It's related to the extraordinary story of QuadrigaCX and the death of Jerry Cotton, the company's CEO.
If you don't remember, tune in back to episode 114 of the Smashing Security podcast. I knew that off the top of my head where we talked about that case.
It is now a Netflix documentary. It's called Trust No One, which you can go and check out.
What happened with QuadrigaCX was that they had— they're a Canadian— oh, they're Canadian. Oh, they must be amazing then.
Cryptocurrency company who were storing a large amount of money. And what occurred was this chap, Gerry Cotton, went on holiday to India and then he died, or so the company said.
And allegedly only Gerry Cotton knew the password which could unlock the cold wallets into which people had put their entire life's savings.
So it's a very interesting story at the time. And there were, of course, investors who were deeply disturbed.
Some of them you will see in the course of this documentary, very worried about what happened to their money and were thinking that there was some kind of conspiracy going on.
I'm not going to spoil anything about the documentary for once.
Go and check it out, and it is my pick of the week.
So instead of a go-to bag, or, you know, an emergency bag for whatever incident you're investigating, being a mum, I now have a go-to travel bag for traveling with a child.
And you mean traveling, traveling, you don't mean going down to Sainsbury's? No, no, I mean traveler, traveler.
So I've traveled with my daughter from— I don't remember the first time she moved or she went to a country, but I think 4 countries now.
And this is not small travel, this is not just popping over to Germany because I'm in Holland. She's about 1 year old, right?
So it's been a bit of a journey, and this is traveling by myself with her as well.
Bottles, you know, those are helpful, but the main points that I think are really key is instead of carrying— because carrying a pram or having a pram with you, or if you might call it a buggy or stroller, I think is the other term, one that's collapsible, so easy to fold down so that they can put at the bottom of the plane and it's light, is key.
But also if they break it or lose it, replacing it isn't that difficult because— oh yeah. Yeah. Well, I've got two prams.
I've got my travel one and then I've got my main one and the travel one I actually more, but it costs maybe a third of the other one. So if it gets broken, not a big deal.
Interesting. The other thing that is important is a carrier for my daughter whilst I'm in the airport.
So instead of carrying her in the pram, I actually strap her to my chest essentially. Because that leaves my arms open.
I don't have to deal with a crying baby wanting to be picked up. And also, you know, it's just way more convenient.
And then on top of that is a light car seat because the car seat that I have in the car is bloody heavy. I'm pretty sure it weighs the same as me.
So this is a specific car seat that is actually clear for air travel.
So if you do want to take it on the plane for children that need their own seat, but also when even if you're checking it, you know, walking it in the airport and to the taxis is not going to break your back.
I don't even think it's very new, and you guys might be aware of it, but it's new to me. So it's called Literature Clock.
It was made originally for the eBook Collective, but there's now also a website that does it.
It basically grabs snippets from literature that include a timestamp that aligns with the one that is currently in your time zone.
So for example, when I was looking at it today, it just comes up on the website, it says, "It's 12:33 now and I could do it.
The station is just down that side road there." And that's from Five Red Herrings, Dorothy L.
Sometimes it's every minute, sometimes every two minutes, because obviously they've gotta find the right quote, and they add these in and it just refreshes.
And it's quite a nice backdrop to either— you can go visit online or to your e-reader.
So it's a perfect site to send to any book lover in your life. Right, so it's called The Literature Clock. It's my pick of the week. Links in the show notes.
And that's Agatha Christie. So you get some good books as well, I quite like it.
What's the best way for folks to do that?
And don't forget to ensure you never miss another episode. You should follow Smashing Security in your favorite podcast apps, such as Apple Podcasts, Overcast, and Google Podcasts.
For episode show notes, sponsorship info, guest list, and the entire back catalog of more than 200 episodes, 268 episodes, check out smashingsecurity.com.
Until next time, cheerio, bye-bye, bye, see ya, wouldn't want to be ya. I know I would, I would.



Cheer`s, it what I thought, confirmed.
clicked on link to see if the site looked dodgy, looks like it halfway downloaded the so-called 'new update' or whatever.
not connected trezor or been asked for any info. / seed etc.
what should i do now to get this potential malware off ?
I fell for it. It immediately drained 90% of everything in my Trezor wallet. What do I do now?
If funds have been taken from your wallet then there may not be much you can do at all… other than be grateful it wasn't 100%… :(
I think my Trezor wallet has been hacked. I tried logging into my account yesterday. I could no log in. I clicked on what I thought was a recovery site. It had a chat option. I put my phone number in the chat. A form came up to place my 24 word recovery names in.. I did this twice along with my pin number. Someone called me with an Indian accent said he couldn't help me. He knew how much was in my account. He said my account had been crashed. Then silence. What can I do to recover my account?
You tell people not to follow links in email but helpfully link to the "official Trezor website". For all we know, that link could be malicious. After all, I don't know you. Train people the right way. Tell them to Google it then bookmark it.
Although there have also been plenty of occasions where cybercriminals have poisoned search engine results – or bought ads on search engines – to direct unsuspecting users to fake websites as well.
Nothing's easy is it?
Using a third-party-service (MailChimp) for their newsletter was not a great idea, especially when handling sensitive information.
I Checked out their domain trezor.io with uBlock Origin, and it's full of third-party-services. Ideally, only trezor.io and sub-domains should be listed:
trezor.io
shop.trezor.io
adform.net
track.adform.net
ads-twitter.com
static.ads-twitter.com
akadns.net
track-eu.adformnet.akadns.net
track.adform.net
edgecastcdn.net
cs41.wac.edgecastcdn.net
platform.twitter.com
facebook.net
connect.facebook.net
fbcdn.net
scontent.xx.fbcdn.net
connect.facebook.net
google-analytics.com
www.google-analytics.com
google.com
www-google-analytics.l.google.com
www.google-analytics.com
www-googletagmanager.l.google.com
www.googletagmanager.com
googletagmanager.com
www.googletagmanager.com
twitter.com
platform.twitter.com
twitter.map.fastly.net
platform.twitter.map.fastly.net
static.ads-twitter.com
I was beside myself with panic but checked the email properties and saw .us where I was expecting .io! I then did a google search of the mail subject line and found this post of yours… Thanks so much for putting my mind at rest and I truly feel for anyone that fell for this despicable scam…
Thank you for the heads up. We need to stay aware of the bad players out there.
Got the email, but did not fall for it. Went to trezor.io to update trezor suite.
A long time IT security "expert" and I fell for this hook-line and sinker. Fortunately for me the device I read the email on wasn't the device I use for accessing my Trezor so I didn't click the link. I updated Trezor Suite from Trezor Suite and then changed my PIN just in case.
My excuse for falling for this is that I am terrified everytime I connect my Trezor, firmware updates are always problematic and I'm always expecting to see a zero balance!
What caught my attention in the podcast (though I may have missed something in the blog post) is that Trezor is totally absolved. People pay a premium for hardware wallets, mostly for the security benefits. If any software installed on the desktop can break this security, this is (excuse my French) a total scam. There's a *lot* they could do (e.g. a screen on the HW token, an on-board approve button, even as simple as a beep+delay) and yet the Trezor product quietly lets malware empty out the wallet.
I had all my coins stolen from my Trezor even tho i had not connected it for a few months how did this happen as when i contacted Trezor they where not helpful at all just told me to contact authorities even tho my money had been sent to binance account when i contacted binance to tell them they found the account and said my money had been withdrawn and are not willing to get me it back even tho they no who has taken it is this against the law or legal