
A boss is bitten in the bottom after being struck by one of the worst crimes in Finnish history, Strava’s privacy isn’t so private, and a private investigator uncovers some TikTok tall tales.
All this and much much more is discussed in the latest edition of the “Smashing Security” podcast by cybersecurity veterans Graham Cluley and Carole Theriault, joined this week by T-Minus’s Maria Varmazis.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Hello, hello, and welcome to Smashing Security, Episode 319. My name's Graham Cluley.
So it's targeted at space professionals. Yes, there are such a thing. And people who are interested in what's going on in space.
So if you're interested, give T-Minus Space Daily a listen.
Now, coming up on today's show, Graham, what do you got?
And she wants the company to be high-tech. She's thinking dot-com, she's thinking, "Oh yeah, that'd be so cool. I'm gonna use computers as much as possible.
We're gonna be cutting edge." So who does she get to handle all the techie stuff?
Who's the guy who she brings in to sort out all the techie stuff at all of these different therapy clinics up and down the country? She calls in her son, Vil Tapio.
That's what you do. You call in your son.
And he's a very hands-on CEO. In fact, he is still doing a fair amount of all the techie stuff. And we've worked for bosses, I think.
We've worked for people who may have founded large companies, but still think, "I will build an intranet. I will do this. I will program it. We will not have monkeys.
We will not pay idiots to write this software."
I've written a script that will allow us to tell your partner what you've had for lunch so she doesn't cook the same meal kind of programming would come up.
But as the company grows more— What happens when a company grows more successful and it doesn't build its IT team? Its technical debt increases.
So, you get more and more garbage and things going wrong all the time.
And yes, of course, they've got more and more psychotherapists and more and more patients coming through the doors, but there was a constant need to maintain the database which this guy had built himself.
Using SQL, and it meant the tech team running the operation had to be able to log in any time, day or night, and fix things. And so they had to make it accessible for remote login.
I know it's a shock about this psychotherapy database, and obviously that would be disastrous.
The good news, the saving grace at this point, is of course that all these database notes are encrypted. They're securely encrypted, not using an encryption algorithm.
They're encrypted using the really novel but completely brilliant encryption system known as Finnish, which hardly anybody in the world can understand. That's true.
No, okay, we're fine, we're fine. March 2019, round about 6 months later, they got hacked again.
And unfortunately, this time it became obvious that they'd been hacked because the hackers, when stealing the database during the intrusion, they also crashed the database.
He's running it all himself because he's the only one with the smarts to do it.
And the last thing he probably wanted was for the people buying the firm to find out that they'd suffered a hack. And so what he did was he held his breath.
In fact, this database, it turned out later, you could access it just by entering the admin's username.
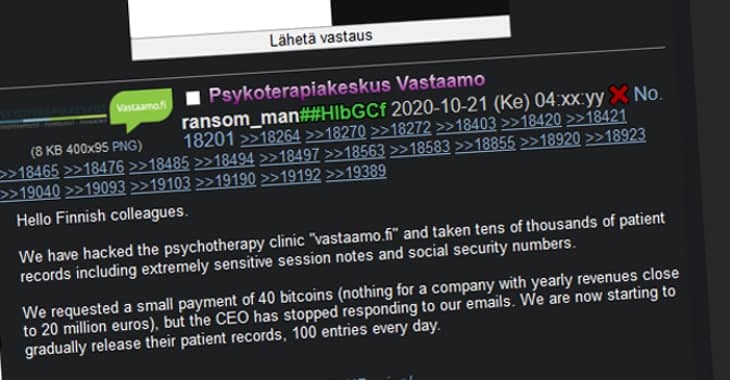
There was no password to actually access this database containing psychotherapy notes of tens of thousands of people.
Clearly, someone who spoke Finnish has gained access to the database and realized what it actually is and can read it. And so Vastaamo goes public.
It says, "We've suffered a data breach a while ago." The CEO gets fired, because obviously he's been incompetent. He's been covering this up from everyone else inside the company.
He loses his job. And what it turns out had happened was that a hacker had contacted Vastaamo, had demanded payment.
He demanded, I think it was something like €450,000 worth of bitcoin. He demanded, this guy called Ransom Man.
And when the company refused to pay it, the hacker then contacted each of the individual patients saying, "I am publishing your psychotherapy notes on the darknet unless you pay me €200."
So you've got people who were seeking mental health assistance, therapy, and now — I mean, it is — It's probably the most horrendous thing I've ever heard of when it comes to extortion and blackmail.
What she did was she posted up a screenshot of the blackmail email she received from the hacker, and she said to him, smell the shit, she said, albeit in Finnish.
Because in the ransomware demand messages, the hacker asked people to pay via a particular Finnish bitcoin or cryptocurrency transfer site, and that transfer site shut it down.
And so you couldn't make payments through it. You could make payments in other ways if you knew how to use bitcoin and things, you could do it.
But essentially the hacker didn't actually make very much money. But this was the biggest criminal case in Finnish history.
Where about 30,000 mental health patients suffered as a result of this.
And when the breach became public, it was so big, the Finnish police crime reporting portal on the web went down. It crashed.
Because it turned out, although he was planning to slowly leak people's data, 100 patients at a time, after about 4 days, he published the whole lot.
Let me just give you the headlines of what has happened since. The Starmo, the psychotherapy clinic, they went bankrupt, right? Quite right too. Who's going to trust them in future?
Even though They contacted their patients and said, "Look, we're really sorry about this. We'd like to offer you a free psychotherapy session.
And we can tell you that we won't record any notes as to what happens in this therapy session." Oh my God. Oh, well, that's all right then. It's okay.
And it was just the IT guy who also happened to be the CEO who'd clearly goofed.
They've seized his yacht. You know, he's been taken to court.
For the last few years, the Finnish police have been digging through this archive, trying to put together a solid case as to who he might be.
And late last year, I think it was November last year, they put out a warrant. He's on the Europol top wanted list.
His name is Julius Kivimäki, and he's no stranger to cybercrime because he has actually been involved in a number of attacks in the past.
He is a member of a group called Lizard Squad, and they launched a DDoS attack on the Sony PlayStation Network one Christmas Day. They stopped Sony PlayStation Network working.
Do you not feel guilty that you've taken so much enjoyment of gaming away from more than 100 million people over this Christmas period?
I'd be rather worried if those people didn't have anything better to do than play games on their consoles on Christmas Eve and Christmas Day. I mean, I can't really say I feel bad.
I might have forced a couple of kids to play, spent their time with their families instead of playing games.
So he had no empathy. He was found guilty back in 2015 for orchestrating more than 50,000 cybercrimes, this Julius Kivimäki, back in 2015.
But because at the time he was only 17, he got a suspended sentence.
And I can tell you that earlier this year, French police responding to a domestic violence report— apparently someone had been out with a woman in a suburb of Paris at a nightclub.
They'd got into an argument. Someone called the police. Police went to knock on this guy's door. French police.
And they looked at him, and he was a blonde, 6-foot-3-inch, green-eyed man. When you see a picture of Julius Kivimäki, you know he is not Romanian. They were like, come on, mate.
And meanwhile, just last week— and this is why I'm talking about it now— last week, Ville Tapio, remember him, the CEO, the IT expert?
You've been a complete and utter muppet. They said you must receive a prison sentence for what you've done.
So we were talking in that episode, actually, I was on that episode, which is funny. I didn't realize that I was, but I was.
We were talking about this app called Strava and Carole, I think actually this was your story and it was about, all right, so Strava for people who don't know, it's a fitness app and you use it to track your activity and compare yourself to past performance.
And it's mainly for people who do cycling and running, but other sports too. But those are usually the two things. And it's a big part of the app is that it's location-based.
So that's a huge part of the appeal because that's how you can compete against other people who maybe ride on the same paths that you do or the same roads.
And then you can sort of own segments and saying, you know, like, I'm the fastest person on that segment, or I'm a local legend for owning this part of my neighborhood. Yeah.
It's totally bragging rights, but that is a humongous part of the Strava appeal, to be honest with you. So yeah, I mean, I'm a big Strava user, so this story is important to me too.
So in 2018, Carole, in your story, you talked about how a soldier on a US military base, do you remember this?
He went for a run around the base, which was in one of those undisclosed locations and with Strava enabled, and he kind of gave away military location secrets through Strava.
I mean, why is somebody in the military using a location-based app when they're on a secret base? That's kind of a PEBCAC, right? Okay.
So folks who give a damn about privacy, which is us presumably, said maybe showing every step I take through the Strava app is not a great idea. Maybe it's not totally necessary.
So maybe some of the information about my run or my ride can stay between me and the app. And some of it, at least where I'm starting or ending, can stay private.
Because I don't know about you, Carole, maybe you've heard about this and Graham, you might have as well. Sometimes people stake out Strava users.
They'll look at what's going on locally and they'll say, hey, that person's got a really nice bike.
Maybe I can find out where they live and steal that bike from their garage when they're sleeping.
Isn't it great? And this is exactly where I live.
So anyway, back in 2021, Strava decided to sort of catch up to what other fitness apps were doing and they said, "We'll allow you to adjust your location privacy a bit so you can turn the location tracking off completely." But if you do that, you can't be a contender in any of the segment competitions, which again, sort of the appeal of Strava.
So that essentially neuters Strava for you, but you can do it if you want to use it that way.
And the other rollout that they made in 2021 is what they're calling a privacy zone, an endpoint privacy zone.
And that allows you to hide your location from where you start and end your route up to within a mile or a kilometer.
So it kind of just draws a giant circle around where you start and end your ride, and it blanks it out.
But yeah, it basically says you can't see anything that happened within the circle, so you have to guess where this person maybe started their ride.
So privacy problem solved, maybe, right? Fast forward to today.
Two PhD researchers at KU Leuven in Belgium have pointed out to Strava that actually it's really, really, really easy to figure out someone's home location from the app, even if the user has Endpoint Privacy Zones set up.
And they said in their research that about 85% of the protected end zone locations can be easily sussed out by an attacker.
So, the researchers released their findings in a study actually in December or November last year and it's called "A Run a Day Won't Keep the Hacker Away: Interference Attacks on Endpoint Privacy Zones and Fitness Tracking Social Networks." And they wrote, "Despite the usage of spatial cloaking, we show that these protected locations can still be discovered reliably.
Our attack leverages the reported distance traveled within the endpoint privacy zone, as well as the layout of the street grid to de-anonymize protected locations with a success rate of up to 85%." Okay.
Like you just need to view source in your browser. There's not some crazy sophisticated hacking tool you need to do. It's being sent back to Strava.
And in that metadata is the full distance of your entire run or ride. And that includes the bit that's supposed to be hidden by the endpoint privacy zone.
So I mean, you combine that with the fact that I know in my case, I just crank up the privacy zone to its maximum. So it's a mile in my case. So it's a circular zone being drawn.
So if you're living in somewhere that's not super population dense, outside of a city or a typical American suburb especially, it's kind of a basic geometry problem.
It's okay, here's your circle. You know, the distance within it, where does it meet? It's really not super hard.
So unless you're maybe departing from an extremely dense city, in most cases it kind of gives it away.
So the researchers reached out to Strava late last year and they published their findings.
And Strava has said since then, thank you for your research, but we have no evidence of anyone doing anything naughty with this information. So we're all good.
So I was trying to figure out as a person who uses Strava a lot, what I could do to maybe keep my home location a little more private.
And one little hack that I've seen people talking about on forums was don't start up Strava until you're a certain distance away from your house and then start it and then scramble that location from time to time.
So start your Strava app in different locations from maybe where you're actually starting, sort of fake that data.
But for a lot of people, having all of that information public is sort of a way of saying, who did I pass by on my route?
Like, hey, I saw this person with this really awesome bike and they were killing it on the route. And I just want to know, how did I stack up against that person?
It's a lot of competitiveness.
The public social aspect of it is a big part of the appeal for a lot of people. So it is the bragging rights of being able to say, I was the fastest person in this segment.
People are always competing against each other, but also knowing who else is riding on the same route as you or running on the same route. That's part of the thing.
And if you lock down to friends only, you're not going to make that discovery. So I don't know how they're going to fix this, but other apps have figured it out.
Like Komoot is another one and they allow people to draw sort of weird, irregular shapes for the privacy zone.
So you can't sort of draw a circle and be like, what's in the middle of it? So they make it— other people have sort of figured out ways to do this.
And so it's not an impossible problem. Just, I don't know if Strava's got the motivation to do it. But hopefully they will.
So note for me.
But then I veered left and I slipped down a fascinating rabbit hole. One that I'm going to share with you guys because it's a world that I know nothing about.
The world of PIs, private investigators. I've watched a lot of TV, read books. PIs are gold, right, in fiction always.
So you get them to do whatever, you know, you need them to do. And they skulk around in the night watching stuff that they shouldn't be watching, taking pictures.
It all sounds very, I don't know. Fascinating. And we have a PI to meet.
But first, before we get to that, I want to tell you about this story that piqued the interest of our specific private investigator.
So we start off in Johannesburg, South Africa, and we have TikToker known as SpillTheTea007 goes live with a special message.
And in this session, she talks about a friend of hers, a TikTok influencer who goes by the name of Bianca Iron. And apparently Bianca had been going through a tough time.
And she even lost a child a few months earlier, she said on her thing. And she was sharing this on her channel. And she wasn't in a good place.
She even reportedly took sleeping pills on air.
So in one of these hosted TikTok affairs, Bianca Irons was bullied, says Spill the Tea 007. So someone she calls Derek started posting all kinds of nasty stuff, right?
Calling Bianca in front of it publicly, like a bad mother, a bitch, a murderer.
But then Spill the Tea goes on addressing Derek directly in her TikTok.
She says, "Okay, in the way that you angled Iron, okay, Bianca Iron, in the live post last night and the screen recordings we have, she committed suicide.
So Derek, I hope today, after calling a bitch and a bad mother, I hope you're happy." And it goes on. Now this is live.
So people are gasping and saying no, and some people start crying. And people are watching this and people share this post and their condolences everywhere, right?
Rest in peace, beautiful soul, all this. And bullying online is bad. And weirdly, well, maybe not weirdly, but Bianca Irons' TikTok channel grew.
And people were looking at this because people were sharing the message and sharing the videos that supporters were sharing. And people were asking how they could help.
And perhaps this is why bank details were shared with the community, allowing followers to provide support. Support for the grief-stricken family members that were left behind.
So at this point in my research, I'm who's this Mike Bolhuis, right? Does he have an online presence? Let me just Google him. Well, guess what? He does. He has his very own website.
So maybe you guys can take a look and see, maybe describe him. Maria?
You know, and the people behind the alias want to teach this Derek guy or whatever, who was shit-talking, a lesson.
So they decided to kill the persona and call it suicide to get his attention. Or is it just all bullshit, the whole thing?
Oh yes, it was the big one that happened.
There used to be sort of where you could put in anybody's name and it'll claim that they died in a skiing accident or something.
While others think it's okay to tell jaw-dropping lies faking a suicide just to grow a channel or to get back at someone.
Or maybe they're just really, really messed up because they've gone through a heck of a lot of crap.
I've never read it, watched it, but there you go. But she's discovered a treasure trove of Harry Potter fanfic online, and it has a saucy penchant.
Unleash powerful fraud protection for your online properties with hCaptcha Enterprise, the leading security ML platform.
hCaptcha adapts to detect and block even the most sophisticated attacks, keeping you ahead of evolving threats.
Whether your bad actors are human or automated, hCaptcha Private Learning is the solution.
Easily combine your pre-blinded data with hCaptcha's thousands of signals to rapidly find fraud and abuse in real time.
hCaptcha's privacy-focused design works in every country, giving you worry-free compliance.
Visit smashingsecurity.com/hcaptcha, that's H-C-A-P-T-C-H-A, to get started with a free trial today. And thanks to hCaptcha for sponsoring the show.
Now, did you know that you can log into Bitwarden using a secondary device instead of your master password? Well, now you do.
Logging in with a device is a passwordless approach to authentication.
It removes the need to enter your master password by sending authentication requests to other devices you're currently logged into for approval.
With Login for Device, it can be initiated on the Web Vault, browser extension, desktop app, mobile app, and you can approve access on your mobile and desktop app version of Bitwarden.
Very, very cool. And the Bitwarden team has hardened the security of its vaults, protecting new vaults with 600,000 iterations by default.
And of course, existing accounts can also update themselves to the same level.
These and many other great security features are incorporated all the time into Bitwarden, keeping your passwords secure from hackers.
Learn more, try Bitwarden for yourself at bitwarden.com/smashing. That's bitwarden.com/smashing.
If a device isn't compliant, the user can't log into your cloud apps until they fix the problem. It's that simple.
Kolide patches one of the major holes in zero-trust architecture: device compliance.
Without Kolide, IT struggles to solve basic problems like keeping everyone's OS and browser up to date.
Insecure devices are logging into your company's apps, but there's nothing there to stop them.
Kolide is the only device trust solution that enforces compliance as part of authentication, and it's built to work seamlessly with Okta.
The moment Kolide's agents detect a problem, it alerts the user and gives them instructions to fix it. If they don't fix the problem within a set time, they're blocked.
Kolide's method means fewer support tickets, less frustration, and most importantly, 100% fleet compliance. Want to learn more? Of course you do. Visit kolide.com/smashing.
That's kolide.com/smashing. And thanks to Kolide for sponsoring the show.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app, whatever they wish. Doesn't have to be security-related necessarily.
I don't know how you feel about Owen Wilson, whether you're a fan of his or not and his shtick.
But in this particular movie, which is called Paint, Carole, and of course you are a keen popular painter. Owen Wilson has a new look.
And I'm going to link to the, in the show notes to the trailer for Paint. And you will see that Owen Wilson now looks rather a lot like Bob Ross.
But apparently he's not actually playing Bob Ross.
And dresses like him.
I don't know if it's done with the permission of Bob Ross's estate or not, but I thought, Carole, you would love this because I know that you love Bob Ross.
I haven't bothered to watch the movie because it's not streaming yet, but—
I thought that was the thing. It was an asshole version of Bob Ross. I've never seen it, but—
Now, there is, though, a proper Netflix documentary about Bob Ross, which may be more up your street.
That's called Bob Ross: Happy Accidents, Betrayal and Greed, in which I learned Bob Ross was a bit of a flirt and had a bit of an eye for the ladies.
And you know that whole whispering thing? You know, it's like, "I just put a little bit of blue here."
So if you are a fan of Bob Ross, go and check out the documentary and then think about whether you want to see this Owen Wilson comedy or not. And that is my pick of the week.
I know neither of you are gonna see it, I know it's not for you, but for listeners who are old school Next Generation fans and who tried to watch Picard season 1 and 2 and were like, "This is awful," I agree with you.
Season 3 is fantastic though, and they righted all the wrongs. And you can just skip 1 and 2 and just watch season 3 and enjoy the hell out of it.
It just finished, I'm not gonna spoil a damn thing, but if you were hurt by season 1 and 2, you said "I'm never watching this again," please watch season 3.
The final 2 episodes righted a lot of wrongs from the absolutely awful movies from the '90s that I remember leaving the movie theater and crying. That's how bad they were.
That's how bad those movies were. They were basically just like, "You like Star Trek: The Next Generation?"
I don't know if anyone who didn't grow up with the series would even care about it, but if you did and you loved the crew as much as I did, you will enjoy season 3 a lot.
There was the one Shatner directed where they're singing Kumbaya around the campfire.
But I mean, TNG had, I think, I would argue the only good one, and good is really relative, was First Contact. And the rest of them, I would be happy if I never saw again.
Yeah, yeah, they were all so bad. I saw them all in the movie theaters when they came out and literally was just like, why does the series hate its fans after a lot of those movies?
Why do they hate us? And now, with this, with this conclusion to the Picard arc and the TNG arc, I feel like they fixed it, which felt really nice, frankly.
So I really encourage people who like the show to watch it.
And then UK, I know there's a different one. Google it. Google it. Paramount does this weird thing with rights around the world. It's not my fault. Don't yell at me.
I'm not in charge of this. But yeah, Picard Series 3.
It is called Colin from Accounts. And I'm sorry, I screwed up. So, I just got a few messages about it. So, please accept my sincere apologies.
Today, my pick of the week is The Diplomat, which exploded across my little slice of Netflix last week. Stars Keri Russell. Have you guys seen it?
And it's like a geopolitical drama, you know, a bit House of Cards-y, a bit Borgen.
You know, basically, you have a lot of intrigue, backstabbing, and cat and mousing, all on an international scale, right?
So that's when you mentioned France earlier, Graham, in your story.
I was like, "This is the kind of thing." It's like suddenly we're in France, and suddenly we're back in London, and now we're in America.
So, Keri Russell plays like an experienced diplomat who normally works in places like Kabul, you know, trouble zones.
And she suddenly finds herself due to some unforeseen circumstance to fill the vacant ambassadorship in the UK.
And it's kind of like you have the American in London angle, you know, like, you meant trousers, ambassador, not pants.
It's got everything really. I liked it. I liked it. It's worth a gander. I think you guys will both enjoy it. Very cool. And that's why it's my pick of the week.
Maria, I'm sure lots of our listeners would love to know what you're up to and where they can listen to you. What's the best way for folks to do that?
So T-Minus Space Daily, or you can go to space.n2k.com or just follow me on Twitter @emvarmazis or on Mastodon @. And you know, I'm talking about it there too.
So yeah, my phone number is— yeah, here's my phone number and my home address. Please listen to my show.
And don't forget to ensure you never miss another episode. Follow Smashing Security in your favorite podcast apps such as Apple Podcasts, Spotify, and Overcast.
It's thanks to them all that this show is free.
For episode show notes, sponsorship membership information, guest list, and the entire back catalog of more than 318 episodes, check out smashingsecurity.com.
It's unbelievable though. Don't watch it on YouTube.
Hosts:
Graham Cluley:
Carole Theriault:
Guest:
Maria Varmazis:
Episode links:
- Finnish therapy clinic’s CEO fired after despicable data breach and blackmail threats – Graham Cluley.
- Lizard Squad Member: Why I Took Down Xbox and PlayStation – Sky News on YouTube.
- Hacker Charged With Extorting Online Psychotherapy Service – Krebs on Security.
- Finland’s Most-Wanted Hacker Nabbed in France – Krebs on Security.
- Ex-CEO of hacked therapy clinic sentenced for failing to protect patients’ session notes – Bitdefender.
- Hackers can find your home on Strava even if you use privacy settings, researchers find – Yahoo Sports.
- Iron Bianca hashtag on TikTok – TIkTok.
- Investigators warn of fake suicide scams on social media platforms – MSN News.
- How did Iron Bianca die? Tribute Pours In As Tiktok Star Passed Away – PBK News.
- Spill-the-Tea-007 TikTok Channel – TikTok.
- Mike Bolhius Private Investigator – Mike Bolhius homepage.
- Paint trailer – YouTube.
- Bob Ross: Happy Accidents, Betrayal & Greed – Netflix.
- Star Trek: Picard – Paramount Plus.
- The Diplomat – Netflix.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff)
Sponsored by:
- Bitwarden – Password security you can trust. Bitwarden is an open source password manager trusted by millions of individuals, teams, and organizations worldwide for secure password storage and sharing.
- Kolide – Kolide ensures that if your device isn’t secure it can’t access your cloud apps. It’s Zero Trust for Okta. Watch a demo today!
- hCaptcha – hCaptcha Enterprise is the leading Security ML platform. hCaptcha adapts to detect and block even the most sophisticated attacks, keeping you ahead of evolving threats.Start your free trial today.
Support the show:
You can help the podcast by telling your friends and colleagues about “Smashing Security”, and leaving us a review on Apple Podcasts or Podchaser.
Become a supporter via Patreon or Apple Podcasts for ad-free episodes and our early-release feed!
Follow us:
Follow the show on Bluesky at @smashingsecurity.com, or on Mastodon, on the Smashing Security subreddit, or visit our website for more episodes.
Thanks:
Theme tune: “Vinyl Memories” by Mikael Manvelyan.
Assorted sound effects: AudioBlocks.


Excellent episode. Quote:
Graham: "He decided to hold his breath,"
Carole: "Well that wouldn't last long."
:-D :-D :-D
The Diplomat: I watched it myself. [EXPLITIVE] and I can't wait a year for the next season !!