
Ransomware just got personal.
To make sure victims can penny up for their files, a version of the Shade encryptor targets infected computers with a special gift: remote control tools.
The Shade ransomware first made news back in September 2015 when researchers at Kaspersky Lab identified it was being distributed via spam email and exploit kit campaigns.

During their analysis of the encryptor, the researchers spotted something odd after Shade finished encrypting a victim’s files:
“…Unlike most other encryptors, Trojan-Ransom.Win32.Shade doesn’t stop there. It doesn’t terminate its process, but instead starts an infinite loop in which it requests a list from the C&C server containing the URLs of additional malware. It then downloads that malware and installs it in the system. This sort of activity is typical of download bots.”
Insidious, to be sure… but only the beginning of a destructive stream of behavior.
Shade’s authors have been busy in recent months. They’ve come up with an updated version of their encryptor that doesn’t initiate its encryption process immediately after activation. The ransomware, which like Enigma is predominantly targeting Russian users, first looks for signs of accounting activity on the infected computer.
Fedor Sinitsyn, a senior malware analyst at Kaspersky Lab, elaborates on this unusual feature:
“For the initial check, the updated Trojan (verdict Trojan-Ransom.Win32.Shade.yb) searches the list of installed applications and looks for strings associated with bank software. After that the ransomware looks for BUH, BUGAL, БУХ, БУГАЛ (accounting) in the names of the computer and its user. If a match is found, the Trojan skips the standard file search and encryption procedure and instead downloads and executes a file from the URL stored in the Trojan’s configuration, and then exits.”
Don’t believe for a second that Shade has left the party. It’s all part of a larger plan to extort as much money from victims as possible.
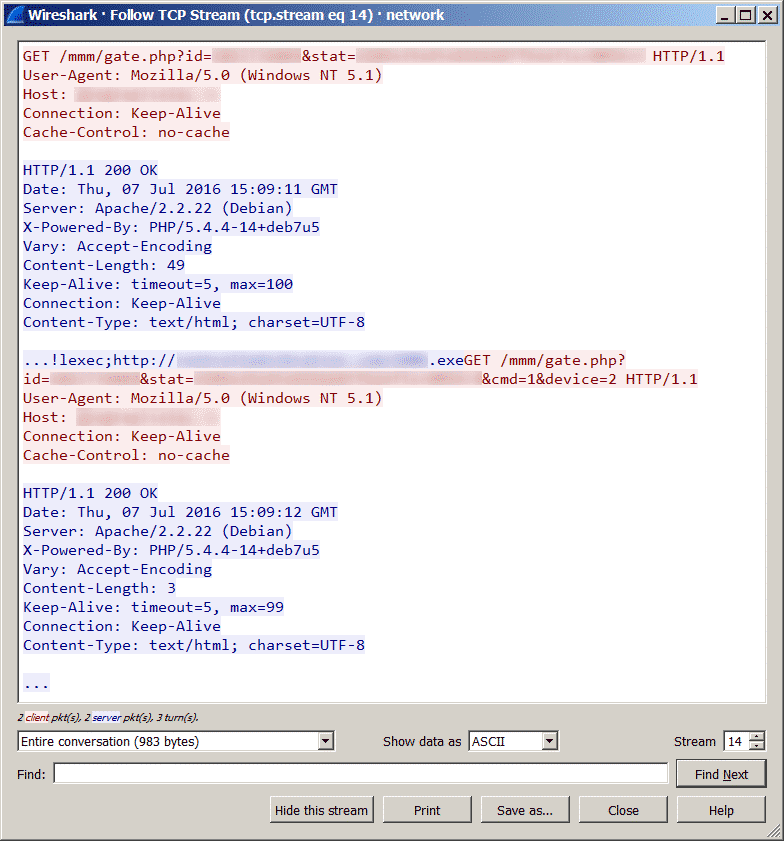
Shade downloads none other than Teamspy, a bot which uses the TeamViewer 6 remote control utility to communicate with a command-and-control (C&C) server and receive a number of commands, including the ability to start/stop audio and video, download a file from a URL provided by the C&C, and enable remote control.
The bad guys can then use those commands to gather as much intelligence as they want about a victim, explains Sinitsyn:
“The use of the bots offers malefactors a wide range of possibilities to enrich themselves, and even a single successful infection can bring in substantial cash flows. Essentially the Trojan encryptors pass the initiative to the user (and it’s up to the user to decide whether to pay for their files or not) and the owners take into consideration the average financial solvency of the victim in assigning the ransom sum. The option of remote access to an infected accounting system allows the malefactor to secretly keep an eye on the victim’s activities and collect detailed information on the victim’s solvency in order to use the most efficient way of getting cash.”
Once they know how much money their victims can afford, the attackers can command Teamspy to download a tried-and-true locker version of Shade onto the victim’s computer. That encryptor in turn demands a customized ransom amount from the victim, all in an effort to increase the likelihood (and amount) that the victim will pay.
As always, users can protect themselves against ransomware like Shade by having a secure backup regime, and avoiding suspicious links and attachments.
In the event they are infected by the ransomware, users can download a free decryptor for their files hosted by the No More Ransom project. (It’s unclear whether that decryptor works for this updated version, however.)



I am hoping to get infected by the malware that pays off my credit card balances.