
Updated A new form of ransomware known as TrueCrypter has boldly designated Amazon gift cards as a viable option by which victims can pay their ransom fees.
Bizarrely, however, victims need pay nothing at all – as simply pressing “Pay” without submitting any payment information results in encrypted files being automatically recovered.
First detected by Jakub Kroustek, a reverse engineer and malware analyst at AVG, TrueCrypter is for the most part a run-of-the-mill ransomware sample.
Lawrence Abrams of Bleeping Computer explains that when TrueCrypter is first installed, it checks to see it is running in Sandboxie. If not, it looks for “antilogger,” “wireshark,” “fiddler,” and other processes that are known to be associated with security software. If it finds any of those processes are running, it will try to kill them. Otherwise it will simply crash, for there is no error handling.
In the event both tests come back negative, the ransomware takes a Caesar-21 encoded string and loads up configuration settings for its command and control (C&C) server address, bitcoin address, and other information. It then encrypts files on the victim’s hard drive using AES-256 encryption, appends .ENC to the filename of each affected file, and deletes all shadow volume copies on the computer before finally displaying its ransom message to the victim.

Those affected by the ransomware are presented with two payment options: Bitcoins or Amazon Gift Cards.
The latter is an odd design choice. Unlike Bitcoins, Amazon Gift Cards are not anonymous and can easily be tracked by Amazon. That threatens TrueCrypter’s author with considerable risk of discovery.
Stranger still, TrueCrypter is not the only ransomware that has asked for gift card ransom payments in recent weeks.
Last month, researchers at Blue Coat Systems identified “Cyber.Police,” a form of Android malware that breaks the crypto-ransomware mold:
“The ransomware doesn’t threaten to (or actually) encrypt the victim’s data. Rather, the device is held in a locked state where it cannot be used for anything other than delivering payment to the criminals in the form of two $100 Apple iTunes gift card codes. That’s unusual because it’s far more common nowadays for ransomware to demand non-trackable cryptocurrency, like Bitcoins. In theory, it might be possible for Apple (or its iTunes gift card partners) to track who used the gift cards provided to the criminals, which may help investigators identify them.”

Allowing users to pay in Amazon and Apple iTunes gift cards might not ultimately be just a mode of preference. It could also be a sign of amateur experience in the world of ransomware development.
Case in point, Blue Coat Systems found they could still copy all unmodified files from the internal memory of a device affected by Cyber.Police. They also discovered the malware does not persist after a factory reset.
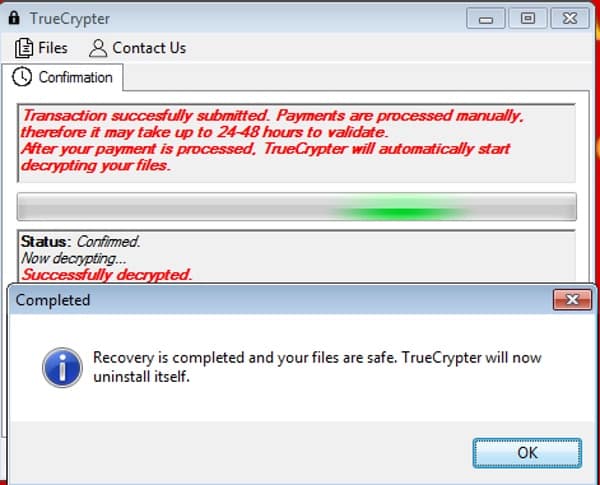
TrueCrypter is even more of a mess. When a user clicks on the “Pay” button, the ransomware sends over the text from the txtTransactionId textbox with the public key. It then starts a loop (one check per minute) by which it attempts to get the private key from the server.

However, if the server is offline or if the request results in an error message – which happens as a result of a timeout, firewall block, or even if the user is offline – the loop will stop, do a check, and begin decryption, with the ransomware using the error message as the private key.
At this time, the server has only been partially reachable for the past several days, with about 40% of all requests resulting in a timeout. If the user was lucky and pressed the button when the server was reachable, it would have replied with the private key, causing the ransomware to decrypt their files for free.
That’s the good news. The bad news is that for all those who were infected with the ransomware while the servers were down, they have no way of recovering their files – even if they pay the ransom.
Remember prevention is always better than cure.
Defend yourself with layered security, make regular backups of your critical data and keep it secure on unattached devices beyond the reach of ransomware, and always exercise caution over the files you open on your computer.
Hat-tip: Thanks to @malwrhunterteam for their technical input into this article, which has been updated accordingly.



Tsk! Amateurs bringing the world of ransomware into disrepute. Whatever next.
Now why is this not traceable?!??!?! Geesus!
My guess would be they would resell the voucher codes instead of using them. Not sure how anonymous voucher market places are but I'm sure there will be Bitcoin networks for this.
Or just back them all up online to Google drive or somewhere and if this happens, re format re install and re download.,
Simple!
Not easy when you have media libraries on the order of 10TB.
Like Callum, I also believe that they will just resell the Amazon Gift Card, and after getting the money from reselling, why should they care what happens to the buyer!
#StaySafe.
Oh my. I never heard of "ransomware" until tonight and the concept didn't even register in my head until I read about it. Actually ransoming people's computers. Glad I haven't gotten infected. I've been pretty careful since the last time I got a computer virus, like 8 years ago. But I ended up with something called AdAware on my laptop tonight, and had no idea where it come from… since Windows Defender had recently alerted me that it detected malware on my laptop, I was wary and looked it up. Apparently it was hidden inside Lavasoft or something. I can't remember why or for what I downloaded Lavasoft. Turns out it's not a virus, and is actually anti-malware, but it operates somewhat like malware in its secret installation via download of something else. And there have been scandals around it. So I decided to delete it ASAP. Anyway researching that led me here. Gotta be careful. Don't download shit from anywhere but the most reputable sources, and certainly don't open files in an email containing no text and just a random file. The last virus I got was from downloading a movie illegally. Don't do that!