
A researcher has released a decryption tool for a strain of ransomware that uses a “bizarre” routine to encrypt victims’ files.
Last week, security researchers Michael Gillespie, Katja Hahn, S!Ri, and MalwareHunterTeam first came across the ransomware, which is called “Alpha.”
Lawrence Abrams of Bleeping Computer explains in a blog post that after successfully infecting a computer, Alpha stores at %APPDATA%Windowssvchost.exe its main ransomware executable, which it automatically removes once it has finished encrypting the user’s files. It also creates an autorun called Microsoft, which allows the ransomware to continue functioning even if the victim reboots their computer.
At that point, the ransomware initiates its encryption process.
But Alpha is not like other ransomware variant, as Abrams observes:
“This ransomware has somewhat of a bizarre encryption routine. On the computer’s SystemDrive, which is usually the C: drive, it will only encrypt certain file types in the Desktop, My Pictures, and Cookies folders. All other folders on the SystemDrive will not be encrypted.”
In total, Alpha targets approximately 249 different file types on the SystemDrive.
On every other fixed disk, the ransomware encrypts all files types using AES-256 encryption and the .ENCRYPT extension. It then displays its ransom message, in which it asks for US $400 in iTunes gift cards.
Greetings,
We’d like to apologize for the inconveniences, however; your computer has been locked. In order to unlock it, you have to complete the following steps:
1. Buy iTunes Gift Cards for a total amount of $400.00
2. Send the gift codes to the indicated e-mail address
3. Receive a code and a file that will unlock your computer.
Please note:,
– The nominal amount of the particular gift card doesn’t matter, yet the total amount have to be as listed above.
– You can buy the iTunes Gift Cards online or in any shop. The codes must be correct, otherise, you won’t receive anything.
– After receiving the code and the security file, your computer will be unlocked and will never be locked again.
Sorry for the inconveniences caused.
Alpha is the third ransomware to ask for gift cards as ransom payment in recent weeks.
Last week, I reported on TrueCrypter and Cyber.Police, two ransomware variants which asked that victims pay them in Amazon and iTunes gift cards, respectively.
Both TrueCrypter and Cyber.Police suffered from design flaws which largely rendered them as little more than a nuisance.
It would appear the same is true for Alpha. A bug in the ransomware’s code prevented the emails to which victims are supposed to send payments from being listed.
But that doesn’t even matter anymore. Michael Gillespie has since spotted a more significant coding vulnerability, which he has used to develop a decryption tool for the ransomware.

Any victim who has been affected by Alpha should download Gillespie’s utility here.
In the meantime, I cannot help but wonder if Alpha, TrueCrypter, and Cyber.Police are all connected somehow.
Is a single individual or group of amateur malware authors responsible for all three variants?
Whoever is behind these samples, let us hope they don’t realize how foolish it is to accept gift cards as a form of ransom payment.
Even if they do manage to come up with a semi-functional piece of ransomware, Amazon and Apple can help track the cards back to the responsible parties.



Any victim who has been affected by Alpha should download Gillespie's utility here.
The link gives a code 404 error
Harold: Try sending them a gift card. ;-)
Gives a 429 error now due to large demand to download the linked file. Time to find another host for the file in question.
Perhaps time to give it to a few trusted mirror locations.
You can get it here as well:
http://www.bleepingcomputer.com/news/security/decrypted-alpha-ransomware-accepts-itunes-gift-cards-as-payment/
Anyone that's been a "victim" of this should just restore from known clean backup. Should be default behaviour for anything that isn't how it should be. Put it back to the last time it was.
Solved. Without the requirement to obtain additional code, that in all reasonablility should only require to operate once.
They should also be ridiculed for allowing this to happen in the first place. There's something common with everyone that have had themselves infected with ransomeware – they did something stupid. By ridiculing them intensely, then maybe they won't be quite as stupid twice.
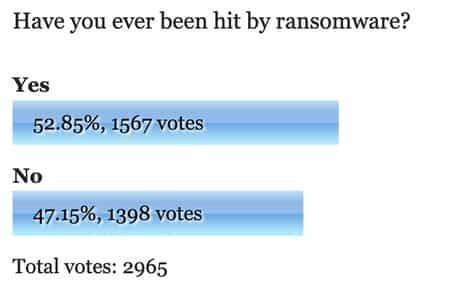
Little poll above needs a "lol, are you serious?" option.
What I'm waiting for is when they figure out they can push malware via SMS as a provider systems update and start locking up people's phones. Wouldn't even need to do something stupid with that. Should be funny.