
On Friday, software engineer Tillie Kottmann’s apartment in Lucerne, Switzerland, was raided by police who seized electronic devices, according to a post from their Mastodon account:
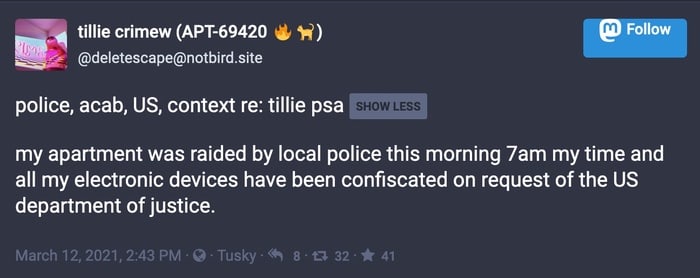
my apartment was raided by local police this morning 7am my time and all my electronic devices have been confiscated on request of the US department of justice.
Kottmann had their Twitter account suspended last week, following the revelation that the video streams of 150,000 webcams managed by Verkada had been breached at companies, hospitals, police stations, and jails.
Before having their account suspended, Kottmann had posted on Twitter that they had compromised the corporate networks of CloudFlare and Okta, and “could have probably owned half the internet in like a week.”
Kottmann is alleged to have gained “super admin” access to Verkada’s systems, which granted full access to customers’ video feeds.
Worryingly, especially for a firm which claimed to prioritise its customers’ privacy, it has been claimed that over 100 Verkada employees had “super admin” accounts, as Bloomberg reports:
The use of Super Admin accounts within Verkada was so widespread that it extended even to sales staff and interns, two of the employees said. “We literally had 20-year-old interns that had access to over 100,000 cameras and could view all of their feeds globally,” said one former senior-level employee, who asked not to be identified discussing private information.
According to the latest update from Bloomberg, the warrant used to search Kottmann’s apartment related to an investigation into Kottmann’s alleged unauthorised access to protected computers, identity theft, and fraud.
In the past Kottmann has claimed responsibility for leaking data from Nissan North America, Mercedes-Benz, and Intel.


