
Mastodon is hot right now. After some years of only being used by geeks (yes, I’ve had an account for a while now) it’s at the tipping point of becoming mainstream… all because of two words:
Elon Musk.
Elon Musk’s purchase of Twitter, his erratic pronouncements, and the layoff of many of the site’s staff, has sent shockwaves through the Twitter community who are concerned about how the service might change.
So what’s the alternative. Many consider Mastodon to be a good new home. It’s free and ad-free, it doesn’t mine your data, it’s decentralised (which means that – unlike Twitter – there’s not one entity or crazy-ape-bonkers billionaire in charge of your content).
It’s perfectly possible – if you’re nerdy enough and fancy the job of maintaining a web server – to create your own Mastodon ‘instance’ (the name Mastodon users commonly use for a server) and be able to talk to anyone else on Mastodon.
Compare this level of control to your traditional social networks like Facebook or Twitter which control what you get to see in your timeline, mine for your personal data, and bombard you with targeted ads.
Mastodon isn’t like that.
If you’re interested in joining Mastodon, you can learn more about it here, or watch a video explainer.
You may even want to eventually follow me on Mastodon. I’m @.
But what I want to do in this article is mention some of the security and privacy considerations you should make if you’re going to start using Mastodon.
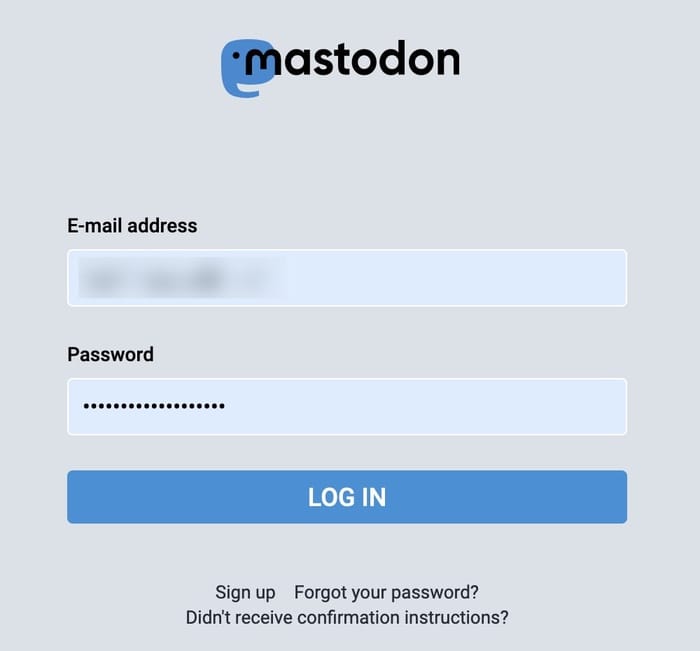
Passwords on Mastodon
Choose a strong, unique password for your Mastodon account. That means ensuring that you’re not using the same password elsewhere on the internet, and one that can’t be guessed by a friend, family remember, co-worker, or hacker with access to a database of 100 million of the most commonly-used passwords.
Ideally you should be using a password manager like Bitwarden, 1Password or LastPass to securely generate and store your passwords for you. I couldn’t tell you what my Mastodon password is, because I don’t know it. My password manager remembers it for me on my behalf.
Two-factor authentication on Mastodon
Having a strong password is the first step, but I also recommend enabling two-factor authentication (2FA).
Once you have enabled 2FA, you won’t just be asked to enter your Mastodon username and password – you’ll also be asked for a two-factor code. This is a time-based one-time-password that can be generated by an authentication app on your phone.
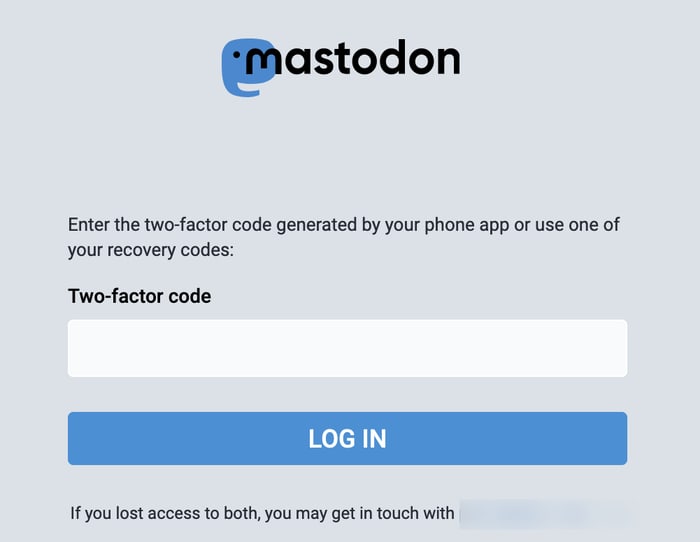
The idea is that a hacker might have stolen or guessed your password, but they won’t know the special code is.
Popular authentication apps that can generate codes for your account include Google Authenticator, Duo, and Authy. It’s possible your password manager (you have one of those, right?) also generates 2FA tokens.
You enable 2FA protection on your Mastodon account by logging into the account you have setup on your chosen Mastodon server’s website, and choosing Edit Profile > Account > Two-factor Auth.
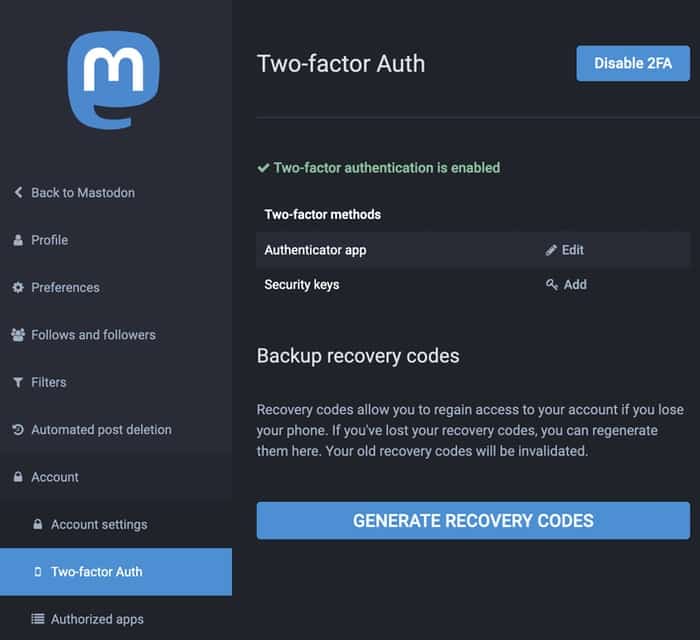
Just follow the instructions there. You can also enable a hardware authentication key for additional physical security if you have one.
Direct Messages on Mastodon
This is an important one, as direct messages work differently on Mastodon than how they work on Twitter.
Direct Messages (DMs) on Mastodon are stored in clear text on the Mastodon server. They’re not encrypted. That means that they could be read by whoever is administering your Mastodon server. Furthermore, direct messages with users on other servers will be delivered to different servers and copies may be stored there.
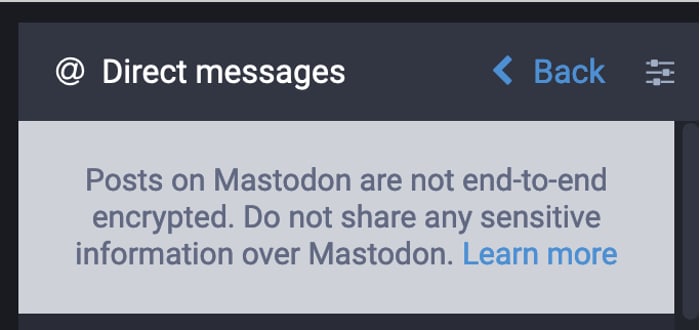
In fairness, Mastodon does display a warning about this – but I wonder how many people will take that much notice.
There’s actually a similar privacy concern with Twitter. Twitter staff can read your DMs.
In short, if you want to say something private to somebody – don’t use Mastodon. You probably shouldn’t use Twitter either. Use a more secure end-to-end encrypted messaging system like Signal instead.
But there’s more danger potentially associated with direct messages on Mastodon.
Imagine you are having a direct message conversation with someone on Mastodon about a sensitive subject.
Maybe George and Paul are bantering via direct message on Mastodon, and one of them says “I’ll tell you who’s a twit. That bloody @Ringo”
Well, because @Ringo has been mentioned in the chat, he now sees a copy of the message too. Ouch, that’s awkward.
This would be particularly dangerous if you were communicating with another Mastodon user to report abusive behaviour. Suddenly your abuser knows you are complaining about them.
Email doesn’t work like that. Twitter direct messages don’t work like that.
(Sorry Ringo for using your name in this example, Peace and Love man!)
Verified users on Mastodon
As we all know one of the pickles Elon Musk has got himself embroiled in on Twitter is “verified accounts.”
Verified accounts on Twitter (the ones with a so-called “blue tick” – it’s actually a white tick on a blue background) used to be handed out for those free to public figures, celebrities, journalists and the like who had verified their identity with Twitter.
They also used to be free, but Musk appears to be hell-bent on doling out verified ticks to anyone who pays a monthly subscription for the privilege.
The rights-and-wrongs of that are outside the scope of this article, but what’s important for Mastodon users to know is that it doesn’t have a “blue tick” system.
Yes, Mastodon users can add an emoji of a blue tick to the end of their username if they wish (or an elephant, or an eggplant… the list is pretty much endless) but it doesn’t mean that they are verified.
But what Mastodon does do is let you self-verify yourself.
Here’s how Mastodon describes the process:
Mastodon can cross-reference the links you put on your profile to prove that you are the real owner of those links. In case one of those links is your personal homepage that is known and trusted, it can serve as the next-best-thing to identity verification.
If you put a link in your profile metadata, Mastodon checks if the linked page links back to your Mastodon profile. If so, you get a verification checkmark next to that link, since you are confirmed as the owner.
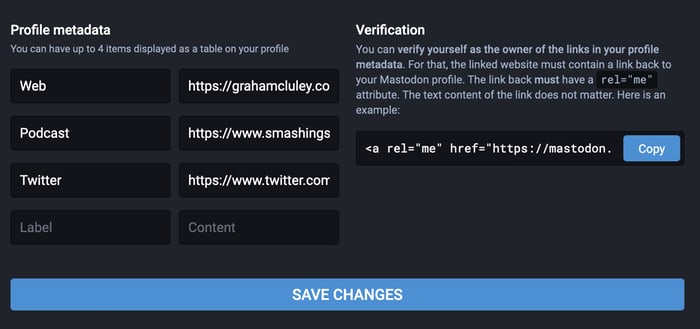
I have put a link on this website (grahamcluley.com) to my Mastodon account. To find out what link I had to put in, I logged into the account I have setup on my chosen Mastodon server’s website, and navigated to Edit Profile > Appearance.
In my case the link I have put on grahamcluley.com is: <a rel="me" href="https://
And I have also put a link on my Mastodon account’s profile to grahamcluley.com. Mastodon checks that the two are pointing to each other, and displays a green tick against the appropriate link.
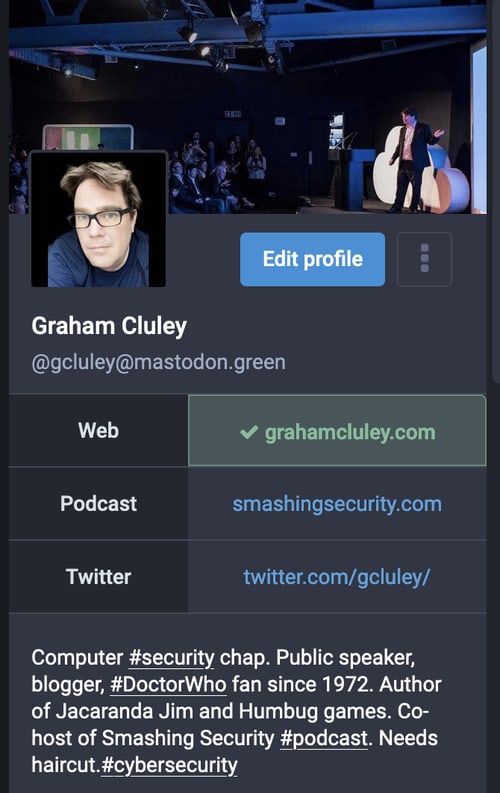
Anyone who wants to confirm that the Mastodon account belongs to the same Graham Cluley who runs grahamcluley.com can see that tick, and know that I’m the real deal.
And now I’ll give you a real-life example of why this matters…
Be wary of following famous/celebrity accounts on Mastodon
Like I said at the beginning, Mastodon is hot right now. Most users are brand new to the site, and don’t know the dangers yet. Furthermore, many famous people and public figures may not yet have established a presence on Mastodon.
So, if you see a Mastodon account for someone famous, always check to see if their profile contains a verified link to their official website.
It’s child’s play for someone to create a fake account in the name of a famous person, and then use the account to spread disinformation, cryptocurrency scams, or malicious links. It would be much much more difficult for a scammer to add a verified link from the account to the celebrity’s official website.
More to be said
There’s probably a lot more to be said about how to behave safely and securely on Mastodon, but much of it applies to *every* website you post to on the internet. Be wary of links that are shared, don’t trust everything you read, never share your password, be careful not to be phished, etc etc.
As Mastodon becomes more popular it is almost inevitable that scammers, cybercriminals and fraudsters will attempt to exploit unsuspecting users.
For more discussion of the tips I’ve included in this article, be sure to listen to this episode of the award-winning “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Hello, hello, and welcome to Smashing Security, episode 297. My name's Graham Cluley.
And there's no more podcast. What a shame. Cheery.
Now coming up in today's show, Graham, what do you got?
With his pronouncements, with his bizarre behaviour, particularly in election week. But never mind, let's not focus too much on that.
As we all know, at least I thought I knew, I thought I knew what Elon Musk was spending $44 billion on.
And Mastodon is a sort of Twitter without all the bad stuff. It's where you go if you liked Twitter, but you're worried that Twitter's going down the pan.
I think in the— oh, I'm not an archaeologist. I'm not someone who digs up fossils.
Because floods of people, I wouldn't say they're necessarily closing their accounts on Twitter, but what they are doing is they're worried and they're trying out Mastodon.
Because that's what Mastodon allows you to do. It allows you to toot. Now, I personally don't like the verb to toot. It sounds a little bit like—
And in fact, on my Mastodon app, I've managed to change the button so it says post rather than toot, because it just pleases me more because I'm of a certain classy nature.
Elon Musk bought Twitter and said, we need to have freedom of speech, right? He's very big on freedom of speech. And other people are saying, you know what?
Twitter's pretty nasty as it is, even with thousands of people moderating the content and getting rid of the unpleasantness. Do we really want complete free-for-all here?
And what's happened is Elon has fired a lot of Twitter staff, something like 50% of his staff have gone.
It was reported that use of the N-word, I don't have to tell you what the N-word is, we're not going to say it on this show, but use of that rose something like 500% after Elon Musk bought the site and people began testing just how much they could get away with.
So people are concerned there's going to be even more toxicity on Twitter.
Plus, Elon, of course, is trying to make money out of Twitter, not only with verified accounts, but he's also looking to monetize advertising more.
So to get more information out of you.
In fact, one of the ways in which he's actually promoting the verified accounts, he's saying, if you get yourself your little new blue tick, which you pay maybe $8 a month for, then what we will do is you'll only see half the number of ads.
And he's saying, if you pay the money, you'll also have more targeted ads, he says. The ads will be better, he says, than the ones used for the masses.
And that's worked for— in his favor in some respects, certainly. But it's also led to some, you know, rather insane behaviors.
If he had to purchase something that he didn't want to buy after he changed his mind and flip-flopped because, you know, he's a high-stakes roller, he's going to want to recoup as much money as possible.
And he seems to be doing it like crazy, like fire staff, charge people more, everything's going go, great, no one's going to leave.
People who work outside of cybersecurity, people who aren't addicted to Twitter. I turned on the radio, I went to the supermarket earlier today. What were they talking about?
They were talking about Mastodon on the radio.
And I think if you remember when Twitter became really popular, Twitter became really popular, I think when Ashton Kutcher started going on about it all the time and it sort of reached that critical mass and the numbers of people who've been switching to Mastodon and the impact that's had on Mastodon sites with sites slowing down because of the deluge of traffic.
And I've had a Mastodon account for years 'cause I'm a bit geeky and nerdy. And to be honest, for years and years, all I ever did there was—
And so we would exchange toots, right, back and forth, and that would be about it. Now I am getting more messages on Mastodon than I do on Twitter.
I'm getting more engagement, more people replying to my messages. I'm having hundreds and hundreds of new people following me every day on Mastodon.
And that's crazy because I had a lot of followers on Twitter, but Mastodon works much better. It seems to be a nicer place.
You've been there a long time and you haven't waxed lyrical till now.
And it's like many of these sites, until you have a critical mass of people, they don't take off. And it's always that chicken and egg.
How are you gonna get people to come along if they don't know anybody there? It's a bit like getting—
So it produces annual stats of how many users are added every day. Mastodon is getting more users every day than Twitter is.
So I don't know about that, but I think Mastodon has just become another big player, but an unusual one because Mastodon, unlike the Twitters, unlike the Facebooks, is not owned by one entity.
It's not owned by one billionaire. It's a decentralized network, which means no one can ever buy it. No one can ever decide we're going to have ads on it.
No one can ever scoop up everyone else's data and information and try and exploit it. And I think people quite like it.
Now, as we're seeing lots of people coming on to Mastodon, what I thought would be useful— I know we have a slightly nerdy audience.
Well, people who are interested in technology listen to Smashing Security, and I thought it'd be useful, as many of those people might be considering checking out Mastodon, just running through a few of the things you should consider.
And if you've got, you know, friends and family who are going on to Mastodon, these are things to bear in mind as well.
Some of them you may not have realized and are like, whoa, that's a bit weird. All right. So let's begin.
But that, of course, is the first step.
With Mastodon, you can also enable two-factor authentication where it's not just going to ask you for your password, it's going to ask you for a one-time time-based password, and that's generated by an app on your phone or maybe your password manager, et cetera, et cetera.
Again, something we talk about a lot.
So if you have something like a YubiKey, which you use, and some people who are really concerned about security and privacy have those, 'cause it's an extra step beyond the authentication app.
Well, Mastodon handles that too. All right. Cool. Now, this is an important one, which is direct messages.
Well, not everyone, but there's lots of different Mastodon servers.
As I said, it's not just one site, but the server which you've chosen to associate your account with, they could see your messages.
So if you're messaging someone, just be aware someone else could read that.
And to their credit, they actually display a message saying, don't share any sensitive information over Mastodon and don't on your direct messages, you know, don't say something which you wouldn't want someone else to see.
Instead, what you should do, of course, is use a secure messaging system like Signal. Another thing that we've tried to get people to switch to but hasn't reached critical mass.
So everyone's on bloody WhatsApp instead, owned by Mark Zuckerberg or some other ghastliness. Right, so that's a fairly simple message, right?
Which is that the messages aren't encrypted, they could be read by someone else, the direct messages. But there's a bigger danger with Mastodon direct messages.
So imagine this, imagine that me and Maria are talking on Mastodon, right? In a direct message.
So if you mention anyone else, so the example, I've written a blog post about this and I'm imagining that the Beatles are arguing at Abbey Road, for instance, and George and Paul are bantering around, slagging off Ringo's drumming, and they make the mistake of tagging Ringo.
And before you know it, the Liverpool lover from Liverpool, you know, can see that his bandmates are slagging him off.
And you included his account name in the person you were telling it to, like, watch out for this guy, he just posted a dick pic at me or something.
It's not just a bit of, oh dear, suddenly your abuser could know that you're complaining about them.
I mean, as it becomes more mainstream, I think historically they've kind of thought, well, we warn people about this and we tell people, you know, don't do these things because it could be— it's more of a conceptual way of how these so-called direct messages work, I think, because it's really a post.
It's really a post which you've said only this person with this user ID can see. So if you mention someone else's user ID, it includes them on the visibility to the post.
Does that make sense?
Because that's not what it should be called.
I would like to see them somehow address this.
You jump in, you think it's just a Twitter replacement and suddenly, uh-uh.
And blue ticks have historically been given to public figures, celebrities, top cybersecurity podcasters, that kind of thing, journalists, that sort of thing to verify their identity.
Of course, he's now gonna be charging. People want to be verified on Mastodon as well to say, yes, this really is me, right? This isn't a fake Graham Cluley.
It's actually a white tick on a blue background, but you get the idea.
But what Mastodon does do is it doesn't have a verified program like Twitter used to. It does let you self-verify yourself.
So what you can do is in your profile, you can include links like a link to your website, for instance, if you have one. And so I link to my website.
I say, here's my website, grahamcluley.com, blah, blah, blah, blah, right? Meanwhile, on my website, that links back to my Mastodon account.
And so the two see each other and it says, oh, Graham is pointing here and he's pointing back to here.
And because only Graham presumably can administer his website, this must be the real Graham.
So I have control over Graham Cluley conferences. And if we created a Smashing Security Mastodon account, we would do the same thing with that as well. So why else is this important?
This is my final really big tip on Mastodon is you are leaping onto Mastodon and you're looking for people to follow and maybe you're looking for famous people, maybe you're looking for celebrities that you used to follow on Twitter, because that was a big reason why people liked to use Twitter to see what celebs were doing.
Well, it's really easy for anyone right now to create an account using the names of famous people on Mastodon, people who may not have established a presence on Mastodon.
So make sure you go to their profile and look for a verified link to their official website, one with the little green tick mark.
Because otherwise it might be a fraudster who's at work and they could post disinformation, cryptocurrency scams, malicious links, whatever it might be.
So just be careful because I think what happens is people go on to Mastodon, they're looking for people to follow, and Lord knows how many people right now are creating accounts in the name of Elon Musk.
Don't trust everything you read. Never share your password. Take care about being phished.
And yeah, most of his stuff on his site seemed to be him looking really rather smug, very well groomed, with that kind of shiny complexion that can only come from— I don't know what the rich put on their skin.
You know, spoiled, deserving, looking deserving. Yeah. And maybe you're just saying this is why people join social media to go look at these kind of people.
So he has 2 million followers because people want to see pictures of a smug, rich, spoiled, and deserving looking person. Is that right?
If you are living in Doncaster and it's raining all the time, you might want to see someone having a fantastic time on a private jet flying to Paris expensive watches, you may just like, oh, that's great, how good for him, you know, guy having a great old time.
We're talking, you know, yachts and, you know, swanky cars and the clothes and the threads and everything.
And he publishes this, of course, by cybercrime and money laundering, specifically BEC scams, because Hushpups— Hushpups isn't into lonely grannies anymore.
This is how apparently he cut his teeth though, in the cyber underworld. But now he's into the big time where the fishies are fatter, juicier, richer.
And he used these BEC compromises to do businesses, you know, and you know how it works.
You know, you pretend you're someone legit in order to get someone to hand over money to you, right? And then they feel screwed.
Is it worse if I duped you into giving me all your money versus me sneaking into your house and stealing all your money? What's worse?
However, to answer your question, I wouldn't want Ray Hushpuppi coming into my home.
On top of that, he has been called one of the most prolific money launderers in the world.
And we covered this— by we, I mean you covered this in episode 265. Do you remember the story?
apparently faked the financing of a Qatari school by playing the roles of bank officials and creating a bogus website.
And he and one of his conspirators, Vinny, Vinny fell out mid-swindle. Hey.
You can hear the whole story in episode 265, 'cause it is a crazy story. You couldn't make it up.
And it's, there's more to read about this in Geoff White's book as well. If you grab a copy of The Lazarus Heist. Yeah.
Anywho, Hushpuppi, aka Ramon Abbas, he was arrested in 2020 in Dubai, then flown to the US in June 2020 to face charges of multimillion-dollar fraudulent schemes, including bank cyber heists.
In 2021, he reportedly pleaded guilty to money laundering in an LA court.
Apparently, two imams also wrote to the judge in Los Angeles appealing for leniency, saying he regularly helped out widows and orphans, as well as donating things to feeding programs.
I bet you feel her pain, Clew.
However, he was still sentenced to what they were expecting, 11 years. Ooh. And he sports a $2 million restitution hole in his pocket. Which he needs to pay back. So, there you go.
Do you trust him? Do you think he's changed? Do you think he's turned a new leaf, become a good guy?
He's obviously helped a few people, but he did hurt a huge amount of people and businesses. And then showed off.
Is he going to be posting pictures or is he going to be tooting from the prison cell, I wonder?
And the value and usage of information makes data very tempting to thieves.
With Sealit, however, you can protect, share, and monitor confidential emails and files without passwords. And it's all integrated with Gmail, Outlook, and file systems.
Deploy Sealit across your organization within minutes and achieve peace of mind thanks to its end-to-end encryption that relies on the Zero Trust security model.
Get the right tool to own your data and gain great Sealit benefits. Plus, Sealit is offering a very special deal for all Smashing Security listeners.
Anyone who signs up for the professional plan before 2nd of December, 2022 can grab 30% off Sealit for a year.
And if you sign up to Sealit, listeners can also grab a free Sealit signature no trust t-shirt.
And thanks to Sealit for supporting the show.
Bitwarden's password manager securely stores credentials spanning across personal and business worlds.
A free Bitwarden account begins with the creation of a personal vault, which allows you to store all your personal credentials.
These are unique and secure passwords for every single account you access. And it's easy to set up. It's easy to use. I honestly love Bitwarden.
I use it at home, use it at work, use it on the go.
Get started with a free trial of a Teams or Enterprise plan at bitwarden.com/smashing, or you can even try it for free across devices as an individual user.
Check it out at bitwarden.com/smashing. And thanks to Bitwarden for sponsoring the show.
You need visibility into your fleet of devices in order to meet security goals and reduce service desk tickets.
But how do you get that visibility when different parts of your company run on Mac, Windows, and Linux? Well, you get Kolide.
Kolide is an endpoint security solution that gives IT teams a single dashboard for all devices, regardless of operating system.
Kolide gives you real-time access to your fleet's data and can do things that traditional MDMs can't.
And instead of installing intrusive agents or locking down devices, Kolide takes a user-focused approach that communicates security recommendations to your workers directly on Slack.
You can answer every question you have about your fleet without intruding on your workforce. Visit kolide.com/smashing to find out how.
If you follow that link, they'll hook you up with a goodie bag just for activating a free trial. That's kolide.com/smashing. And thanks to Kolide for supporting the show.
And welcome back. And you join us for our favorite part of the show, the part of the show that we call Pick of the Week.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish.
It doesn't have to be security-related necessarily.
This isn't as dramatic a story as what happened to you, Carole, in the Viennese opera. But it was—
And Bill Nighy's not doing his usual shtick of being Bill Nighy. I think quite often he's asked to be Bill Nighy, right? He's got certain quirks about him.
And, you know, I think he's got quite a lot going for him, but he's quite often a little bit, you know, sort of aging rock star kind of thing. Anyway, he is superb in this.
He gives such a measured, gentle, quiet, unshow-offy performance. And he's actually—
And Bill Nighy is working at the London City Council, as it was then. And he's told that he has a fatal illness.
I thought, here I am, the aging, irascible veteran, and the young flighty thing, you. And she has all this pep, she has all this vim and zest and ignites something.
And they don't get off. There's no smuttiness going on. There is a belly dancer at one point, but other than that, there's nothing like that. But it's lovely.
The screenplay is by Kazuo Ishiguro, who did The Remains of the Day, and it is based upon a film which came out in 1952 in Japan called Ikiru.
It's called Living, and I recommend it.
And her main job is to nip from East Berlin to the West to eliminate enemies of the state.
So it's a bit Villanelle from Killing Eve.
And basically Kleo wants revenge on all those that hurt her, and she finds unusual sidekicks to help her along because it's pretty, you know, it's a bit of a thriller killer revenge story until these two who provide a bit of comedic relief show up in the story.
So you have Thilo. He's kind of, I think, the metaphor for West Germany because he's kind of just this kid jumping as in pastry. No, Thilo as in T-H-I-L-O.
And of course, the backdrop is late '80s, early '90s.
So the Wall's coming a-tumbling and the entire communist regime is falling apart in East Berlin, and the production is stylish, edgy, fun.
We haven't created a Mastodon account yet, @SmashingSecurity, no G, which wouldn't allow us to have a G. And we also have a Smashing Security subreddit.
And don't forget, we would love you to never miss another episode.
And the way to do that is to follow Smashing Security in your favorite podcast app, such as Apple Podcasts, Spotify, and Google Podcasts.
And of course, to our wonderful Patreon community, it's thanks to them all that this show is free.
For episode show notes, contact and sponsor information, and free access to the last 296 episodes, check out smashingsecurity.com.
Why don't you walk me through creating a Mastodon account and we could record the process and all my feelings and all the frustrations and we can slap it up for our Patreon listeners?
So if anyone wants to create one, they can do one with you telling them how to do it.
Take care of yourself and any friends who are venturing onto Mastodon, and if you have any questions either follow me on Mastodon or leave them below.




It might be worth pointing out that verification doesn't seem to get transmitted between servers. For instance, if I click on you on my Mastodon server, it takes me to the URL https://mastodon.social/@, which shows your information and your links, but not the fact that one of the links is verified. (Note that if you're not logged in as a user on mastodon.social, that URL will just redirect you to mastodon.green instead.)
counter.social is the only way to go. Full featured and secure.
It's worth adding that if there are lots of users associated with one domain that need to be verified, that domain / organisation will sometimes set up their own Mastodon instance and say that everyone on that instance is verified to be associated with their organisation.
For instance MIT (big university near Boston in the USA) has its own Mastodon instance at https://mastodon.mit.edu/ and the only people allowed to have accounts on it are staff and students at MIT, so any account on that instance can be verified as being from MIT – so anyone claiming to be an MIT professor and using some other instance is clearly dodgy.
"anyone claiming to be an MIT professor and using some other instance is clearly dodgy" or doesn't want their employer storing and censoring their social life.
A suggestion for describing Mastodon DMs to muggles who are Mastodon curious.
Mastodon DMs are DIRECT messages. They are not PRIVATE messages.
It's similar in a way to Facebook profile posts. On Facebook, if you have "Who can post on your profile?" set to "Only me", then the only way of directing a message towards you is via Messenger (one-to-one). But if you have "who can post" set to "Friends", well, then your Facebook friends can write a message on your profile, or wall as people used to say (one-to-many potentially). The typical use case for this: Happy Birthday! ????
It's possible to reply back-and-forth to such messages and others won't be prompted about the thread. BUT… it is also possible to mention/tag people in the replies of such posts and they'll be notified and pulled into the conversation. And all of it is generally visible to the larger group. Sort of like a private conversation in a public room at a party. If you call somebody over, it then becomes a direct conversation between three people.
In Mastodon's case, one must remember that the party host (the person running the server) is able to see everything at the party.
People often confused Facebook "wall posts" for private conversations back in the day. Hopefully that won't be the case on Mastodon – but I suspect that history will rhyme if people start adopting it en masse.
this is quite a useful comparison – thank You !
– just curious: any admin at a server can ALWAYS ? see all content?
– how do we actually know, WHO indeed is running a particular server?
See: https://blog.joinmastodon.org/2018/08/mastodon-quick-start-guide/
"Under the sign up form you will see a link to the rules page. It is likewise linked from the “Learn more” button under “Administered by”; on other pages, the rules are linked in the footer as simply “About”. You could also just enter the correct URL into the address bar of your browser directly as it always follows a format like https://mastodon.social/about/more."
"The rules page also tells you who the owner/administrator of the server is. Most servers set you up following the admin when you sign up, kind of like a modern take on MySpace Tom. This is great, it means you know who to ask if you run into problems and you can receive server-specific announcements (like when the software is being upgraded) and in general it’s great to know who runs the server you’re on."