
A reconnaissance campaign dubbed “Operation BugDrop” has stolen gigabytes of data from at least 70 organizations in Ukraine and elsewhere.
The threat intelligence research team at CyberX came across the operation after discovering an in-the-wild malware campaign.
So far, the malware has captured documents, passwords, and screenshots from dozens of targets located in Ukraine, Saudi Arabia, and Austria. Those victims include a manufacturer of industrial control system monitoring equipment, a human rights institution, and a scientific research institute.
Operation BugDrop has also stolen victims’ audio recordings by surreptitiously turning on infected computers’ microphones.
Obviously, covering your webcam does nothing to prevent against this type of attack, although there are platform-specific tools available that issue alerts when a program activates the microphone.
Few threat actors can conduct an ongoing campaign of this magnitude. As CyberX notes in a blog post:
“Operation BugDrop is a well-organized operation that employs sophisticated malware and appears to be backed by an organization with substantial resources. In particular, the operation requires a massive back-end infrastructure to store, decrypt and analyze several GB per day of unstructured data that is being captured from its targets. A large team of human analysts is also required to manually sort through captured data and process it manually and/or with Big Data-like analytics.”
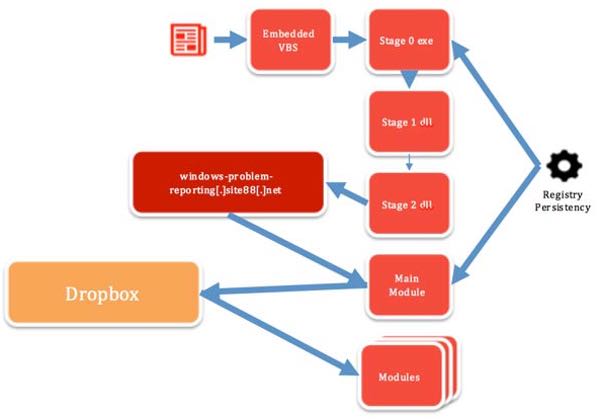
An BugDrop attack begins when a target receives a specially-crafted email that comes with a Microsoft Word document purporting to contain a list of military personnel’s personal details.

The attachment contains malicious macros that, when executed, load a malicious VBS script that runs the malware’s main downloader from the temp folder. This downloader is copied from a Russian social media site; its icon is a meme that makes fun of Ukrainians.
The dropper comes with two DLLs, which are loaded via Reflective DLL Injection in a manner that’s similar to the 2015 BlackEnergy malware attack against a Ukrainian utility company.
The first DLL achieves persistence for the malware, whereas the second downloads the main module. This latter component loads up data-stealing plugins that encrypt all the data they find using Blowfish and then send it to a Dropbox account under the control of the attackers.
As of this writing, CyberX has found no forensic evidence linking the operation to a particular group.
The security firm is therefore advising organizations to be on the look for anomalous behaviors on their networks. They should also disable Office macros on all workstations by default and should educate their employees about the dangers of phishing attacks.


