
A new attack allows Mac malware to record video and audio whenever a victim legitimately turns on their webcam, without drawing attention to itself.
Now it’s no surprise that malware would leverage webcams in an attempt to spy on OS X users. A victim could blurt out personal information which attackers could use for identity theft, or peeping toms could secretly record footage with the intention of blackmailing the unwitting victim.
That explains why some of the recent malware samples for OS X, including Eleanor and Mokes, come equipped with the ability to record video and audio content from infected computers.
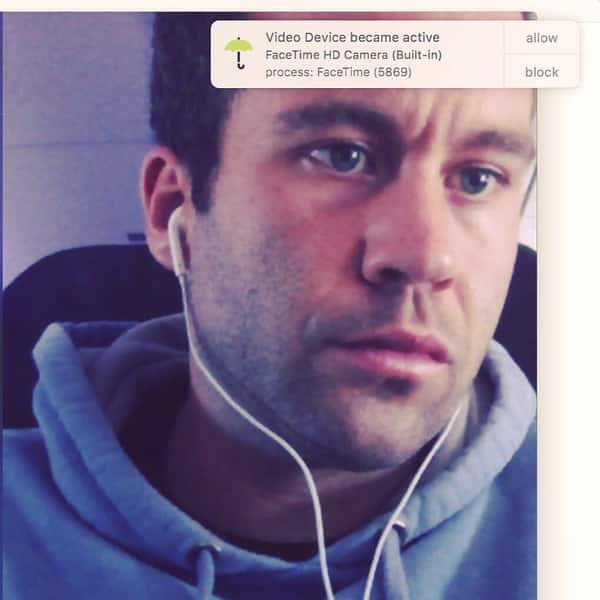
But it’s not easy to activate the webcam without the victim knowing. Just take a look at the image above.
See that little green dot? That’s an firmware-based LED light that activates every time someone turns on the camera. As such, an actor would have a hard time disabling the light.
But according to one security researcher, that little security feature might not matter anymore.
The new attack has been described by Synack’s Patrick Wardle, who in the past uncovered a way to bypass GateKeeper, developed possible exploits for the Rootpipe security flaw, and created a host of free tools to advance OS X security.
As Wardle is explaining at the Virus Bulletin 2016 conference in Denver, Colorado, this week:
“After examining various ‘webcam-aware’ OS X malware samples, the research will show a new ‘attack’ that would allow such malware to stealthily monitor the system for legitimate user-initiated video sessions, then surreptitious piggyback into this in order to covertly record the session. As there are no visible indications of this malicious activity (as the LED light is already on), the malware can record both audio and video without fear of detection.”
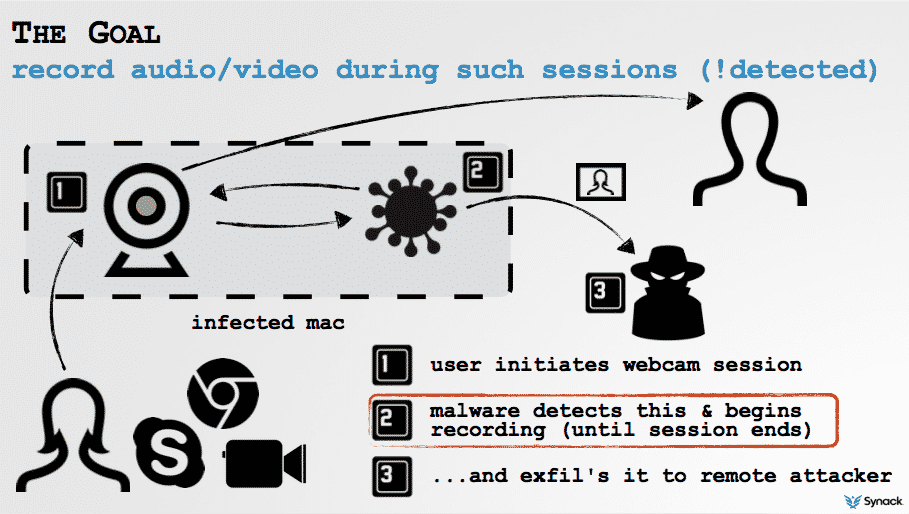
To detect the webcam session, the malware enumerates the camera and registers for notifications. Once it receives a notification that the camera is turned on, it begins recording. It then turns off once the session has ended.
And the user never even knows any of this has happened!
Okay, so what’s the big deal? Just slap a piece of tape over the webcam and call it a day.
That might work for some people but not for all users. What about the couple that likes to FaceTime while one of them is on a business trip? Or the business team that relies on Skype for its telecommuting workforce?
It’s because of those users that Wardle has developed OverSight, a new tool that protects against piggybacking OS X webcam attacks.
Whenever a program activates the internal mic or accesses the webcam, OverSight displays an alert. A user can then choose to allow or block the program.

Best of all, the tool is absolutely free.
You can also learn more about Wardle’s talk and other presentations at Virus Bulletin 2016 on the conference website.


