
Researchers at the Massachusetts Institute of Technology (MIT) have revealed a new anonymity scheme that could rival the popular onion encryption-based network Tor.
In response to the disclosure of vulnerabilities in Tor’s design, researchers at MIT’s Computer Science and Artificial Intelligence Laboratory and the École Polytechnique Fédérale de Lausanne created Riffle, a system that allegedly provides better security and uses bandwidth more efficiently than Tor.
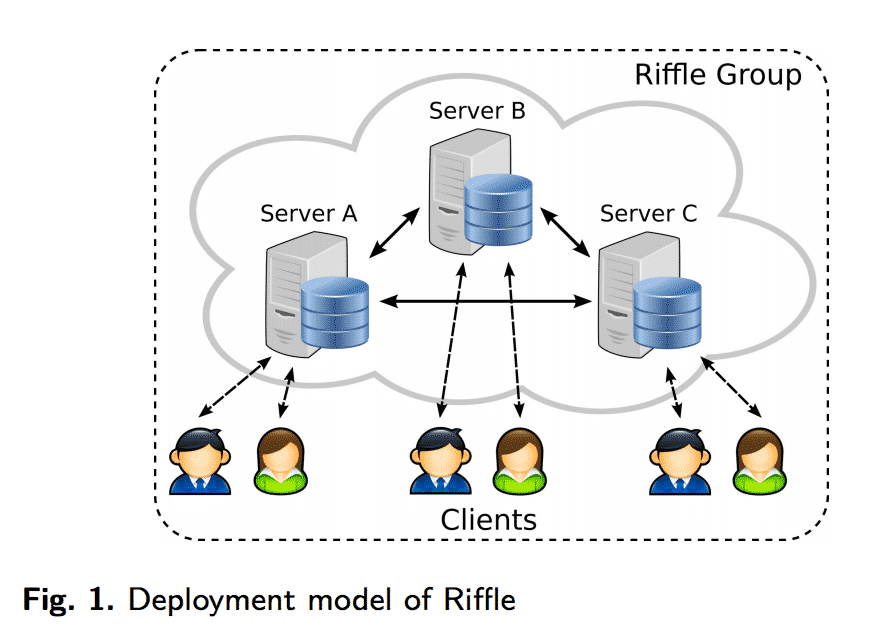
As the researchers explain in a paper, the core of Riffle is a mixnet, or a system that prevents traffic analysis by routing each user’s message through a set of servers known as mixes. Those servers, in turn, mix up the order of the messages in which they received them before passing them on to the next server.
Larry Hardesty of MIT News Office provides an example:
“If, for instance, messages from senders Alice, Bob, and Carol reach the first server in the order A, B, C, that server would send them to the second server in a different order — say, C, B, A. The second server would permute them before sending them to the third, and so on. An adversary that had tracked the messages’ points of origin would have no idea which was which by the time they exited the last server. It’s this reshuffling of the messages that gives the new system its name: Riffle.”
Like Tor, Riffle uses onion encryption, which means each message is wrapped in multiple layers of encryption. Those layers are peeled off as the message makes its rounds to the various servers in the anonymity network.
An active adversary could just as easily target Riffle as they would Tor by tampering with some of the anonymity servers using their own code.
To protect against these types of attacks, Riffle uses verification shuffle, a mechanism which generates a mathematical proof indicating the message it sends is the same as the message it received. Once a secure connection is established, the system then resorts to authentication encryption to verify the authenticity of an encrypted message, thereby helping to conserve computation power.
Jonathan Katz, director of the Maryland Cybersecurity Center and a professor of computer science at the University of Maryland, feels the researchers add much to the conversation in the way of secure mixnets:
“The idea of mixnets has been around for a long time, but unfortunately it’s always relied on public-key cryptography and on public-key techniques, and that’s been expensive. One of the contributions of this paper is that they showed how to use more efficient symmetric-key techniques to accomplish the same thing. They do one expensive shuffle using known protocols, but then they bootstrap off of that to enable many subsequent shufflings. When you use standard encryption on the Internet, you use an expensive public-key crypto system to encrypt a short key, and then you use symmetric-key techniques to encrypt your longer message. But it’s novel in the context of these mixnets. They’ve been around for 20, 25 years, and nobody has had this insight until now. In the standard context of encryption, you have the honest sender and the honest receiver, and they’re defending against an external malicious attacker. Here, you need stronger properties. The issue is that the server that’s doing the shuffling might themselves be malicious. So you need a way to ensure that even a malicious server can’t shuffle incorrectly.”
In addition to these security improvements, Riffle has performed better than Tor and other anonymity networks in experimental tests.
The system provided a good file sharing service for up to 200 clients at 100 KB/s of effective bandwidth, while less bandwidth-intensive use like microblogging could accommodate 100,000 users at under 10 seconds of latency.

There is currently no version of Riffle that’s available for download. Neither is there a plan to commercialize it. However, the researchers will be providing more information on the system at the Privacy Enhancing Technologies Symposium in July. Perhaps they will flesh out a plan of what’s in store for Riffle.
One thing’s clear: assuming it doesn’t suffer from glaring coding errors or security vulnerabilities, a commercialized Riffle could reshape the anonymous browsing landscape.


