Tag: Tor
February 1, 2018
Smashing Security podcast #063: Carole’s back!
January 31, 2018
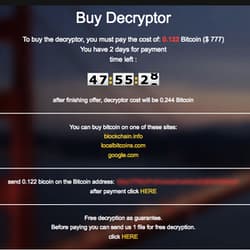
Bitcoin hijack steals from both ransomware authors AND their victims
Bitcoin hijack steals from both ransomware authors AND their victims
November 30, 2016
Spam campaign tiptoes via Tor to deliver Cerber ransomware
August 15, 2016