 Plex, an application used to organise and stream video collections between devices, has found itself on the sharp end of an attack from a ransom-demanding hacker.
Plex, an application used to organise and stream video collections between devices, has found itself on the sharp end of an attack from a ransom-demanding hacker.
In an email to users, Plex admitted that the hacker had been able to access the IP addresses of users, private messages, email contact details and encrypted password hashes.
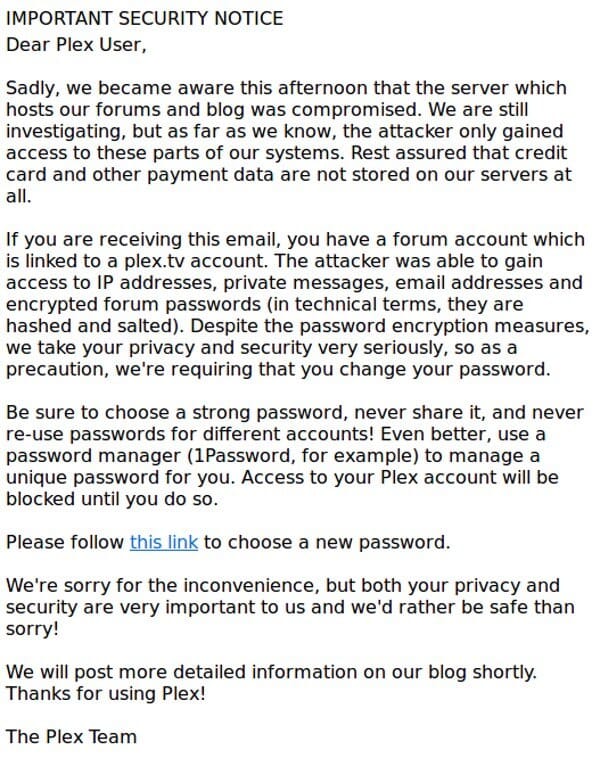
“Sadly, we became aware this afternoon that the server which hosts our forums and blog was compromised. We are still investigating, but as far as we know, the attacker only gained access to these parts of our systems. Rest assured that credit card and other payment data are not stored on our servers at all.”
Personally I would have preferred to see the firm not embed a clickable reset password link into its notification email, as that’s precisely the kind of trick used in phishing attacks.
Plex said it was advising users to change their passwords, and to ensure that they were not using the same password elsewhere on the net. That’s good advice, after all if you re-use passwords it only takes one website to be hacked for you to suffer a world of pain.
Furthermore, Plex wisely recommended that users run a password manager (they suggest 1Password, which is an excellent choice but others are available…) to store their passwords securely and generate complex, hard-to-crack passwords.
From the sound of things, only Plex users who have registered on the company’s forum need to be concerned at this stage – so don’t be surprised if you are a customer of the company but have not received a notification email.
A (now removed) post made by the hacker on the Plex forum described his ransom demands:
Hello,
My name is savaka and I like to hack things. Recently https://plex.tv/ (s) forum & website was compromised by me. I managed to obtain all of your data, customers as well as software and files.
I replaced the index.php of the administrator cpanel with a nice message, but the ones in charge of your data decided that it would be pretty lulzy’ to remove the message and place the original index back there.
I gave them until the 3rd of this month to send 9.5 BTC to [redacted] or I would release all this data.
This ransom is still active and on the 3rd: if no BTC payment is made, the ransom wll go up by 5 BTC.
Eventually if no BTC payment is made, the data will be released via multiple torrent networks and there will be no more plex.tv
You can also pay me to remove your data from the content that’s going to be released by e-mailing “savbtc@[redacted]” – If you send an e-mail without BTC ready to send, I will add your data to a special list.
savaka
P.S I don’t care who the BTC comes from as long as the payment is made: no data will be released.
Plex co-founder Elan Feingold responded on Reddit, confirming that computers running the online forum had been “definitely compromised”, most likely due to a “PHP/IPB vulnerability”. He went on to say that there was no reason to believe that any other parts of its infrastructure was compromised.
Obviously giving in to blackmail is never a good idea, as there is no guarantee that the extortionist won’t simply ask for more and more money.
Instead, invest the money in better security – and perhaps either patching your software, or getting a solution which is more capable of defending itself against future attacks.



OK…let me see if I've got this straight. This "savaka" assclown hacks a site he doesn't own, steals data he doesn't own (or so he claims), makes a demand for money he doesn't own, and threatens to release private information he doesn't own (including a threatened damage escalation if his demand isn't met)…and he expects Plex to trust that he'll honor his word if they cough up the ransom?
Wow. Just wow.
What do morons like that use for sense?
Not at all surprising though, is it? Isn't this how ransom always works? This includes hostage situations.
"What do morons like that use for sense?"
Wishful thinking and finding the target that will actually fall prey. This is exactly why spam will never go away; as long as one person responds they will have a reason to add poison to the already toxic waste, affecting mail servers, time, money, etc. You can replace spam with many other things too, unfortunate as it is (example: this issue here).
The hacker's use of grammar is atrocious. They should refuse to negotiate on that basis alone. With apostrophes so poorly used and placed, I'm guessing it wasn't an SQL injection that got him in to their server.
I bet he speaks English far better than any of us can speak his native language (what ever that is).