
What’s happened?
Just days before Christmas, when most people probably weren’t paying too much attention, password management service LastPass revealed that hackers had accessed customers’ password vaults.
That sounds really bad. But wasn’t there news of a LastPass hack earlier in the year?
You’re probably thinking of the original announcement LastPass made back on August 25 2022, where it said that a hacker had managed to gain access to a developer’s account, and stolen some of its source code from a development environment.
Back then LastPass said that it had “seen no evidence that this incident involved any access to customer data or encrypted password vaults.”
So they were wrong when they said that?
Well, LastPass might have not seen any evidence that customers’ passwords vaults had been accessed then, but…
But when a company says it has “seen no evidence” of anything bad happening, that’s not necessarily the same as saying “nothing bad happened”?
Correct. And sure enough, just before Christmas, LastPass confirmed that the information stolen from a developer’s account in the August 2022 attack was actually “used to target another employee, obtaining credentials and keys which were used to access and decrypt some storage volumes…”
Gulp! That sounds much worse. So let me get this straight – the theft of the password vaults and other data from LastPass may well have occurred in August or September… long before they announced it as I was distracted wrapping Christmas presents?
Perhaps. LastPass hasn’t said when it believes the theft of the password vaults occurred, but the most important thing to you is probably what the stolen data contained, and how it could be exploited by hackers.
Ok. I’m bracing myself. Tell me the worst…
The stolen data includes the following unencrypted data:
- company names
- end user names
- billing addresses
- telephone numbers
- email addresses
- IP addresses which customers used to access LastPass
- website URLs from your password vault
In other words, cybercriminals now know that you use LastPass, they know how to contact you, and they know which websites you use.
That’s valuable information for anyone attempting to phish further information from you, as they could easily pose as one of the websites you access and send you a scam email.
Furthermore, simply knowing which websites you access (and store in your password manager) might reveal private information about you that you would have rather remain confidential.
And further still, it’s possible you stored password reset links for these websites in your password manager that might not have expired, or other sensitive information or tokens in your website URLs that you wouldn’t want to fall into the wrong hands.
This sound terrible…
Hang on, I haven’t finished.
Because the hackers also stole encrypted customer data including:
- website usernames and passwords
- secure notes
- form-filled data
But that’s encrypted, right?
Yes, it’s encrypted. The hackers need to determine what your LastPass master password is, to access the crown jewels – the usernames and passwords to all your online accounts.
Well, I have a strong, hard-to-guess, unique password. And I have two-factor authentication (2FA) enabled on my LastPass account. So I’m safe…
Hmm, well… 2FA is irrelevant in this case. The hackers have already stolen the password vault data, they don’t need to bother logging into anyone’s LastPass account.
Similarly, changing your password now doesn’t undo the data breach. It may still be a sensible step to take, of course.
And what’s going to help the hackers is that many many LastPass users are likely to have chosen master passwords that are much weaker than LastPass itself recommends.
Since 2018, LastPass says it has recommended and required a “twelve-character minimum for master passwords”.
Aside from the fact that the number of characters alone isn’t a good indicator of password strength, it appears that customers who have been with LastPass since before 2018 have not been required to update their master passwords to meet LastPass’s own recommendations – leaving the encrypted parts of their password vaults much more vulnerable.
It sounds like LastPass missed an opportunity to boost its users’ security there…
Yes, it does rather.
And what’s more, security researchers have revealed that at least some of the master passwords stored by LastPass for its longer-standing users’ vaults have been encrypted in a way which makes them far too easy to crack.
What do you mean?
As researcher Wladimir Palant details, LastPass salts-and-hashes master passwords using the PBKDF2 algorithm, with 100,100 iterations.
The number of “iterations” is an indication of just how much “work” someone (or more likely a modern graphics card) is going to have to do to break your password.
However, many LastPass users who have had their accounts for a long time appear to have only had their accounts configured for 5000 iterations, or in some cases as low as 500, or even one!
Such poorly-secured vaults may not take too long (or cost too much money) to unlock.
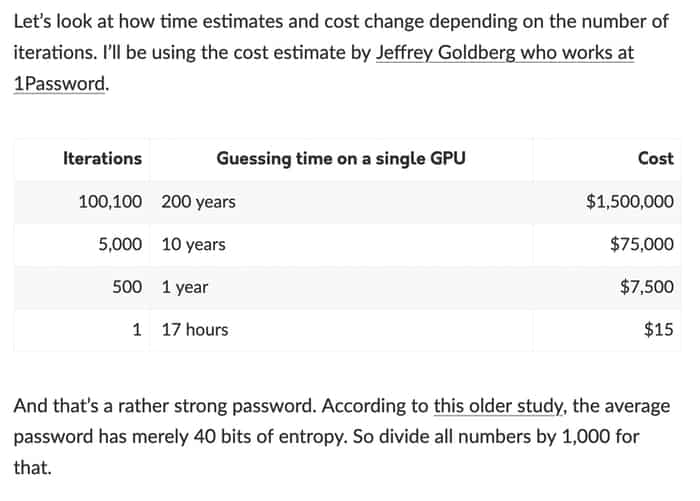
And, as LastPass rival 1Password explains, the figures become much worse when it is a human-created password that the hackers are trying to crack rather than a truly randomly-generated one.
Oh, by the way, OWASP’s 2021 guidance is for… err… 310,000 or more iterations…
Years ago, shouldn’t LastPass have contacted those customers who had a low number of iterations, and forced them to boost their security?
You would think that would have been a good idea, right? Years have gone past, modern graphics cards have got faster at cracking passwords, LastPass failed to better protect its most loyal customers.
You won’t find any mention of the data breach on the homepage of LastPass.com either. Which also seems like a missed opportunity – even if it’s closing the stable door after the horse has bolted…
Blimey. Ok, let’s cut to the chase. Is my LastPass password vault at risk?
Perhaps.
I would say your LastPass password vault is more at risk if a hacker is prepared to put the resources into cracking your master password. For instance, if you are…
- one of the 100,000 businesses worldwide that uses LastPass
- a journalist
- a government worker or politician
- a human rights defender
- a celebrity
- a cryptocurrency investor
- “a person of interest” to an authoritarian regime
I’m not one of those. I’m just Joe Schmoe. Could the passwords I store in my LastPass vault still be accessed?
Perhaps. Especially if your password isn’t as strong as it should be, or if you’ve reused your master password elsewhere on the net, or if you’re likely to be phished, or if LastPass was not using enough iterations to make it harder to be cracked.
So what should I do?
The sensible thing to do would be to assume that your passwords have been, or could be, compromised.
In which case you should change your passwords. And not just your LastPass master password – *all* the passwords stored in your LastPass vault.
Sheesh. That’s going to be a lot of effort
I hear you. I have over 1600 unique passwords in my password vault (I’m not using LastPass, thank goodness), as well as other documents that I would like to remain secured.
Should I ditch LastPass?
That’s something only you can decide.
I feel bad because LastPass is a product that I have recommended to users in the past (they used to sponsor this website back in 2020, and between 2018-2020 sponsored the “Smashing Security” podcast I co-host).
I’ve always been a big fan of password managers (1Password has also been a sponsor of this blog and the podcast, and Bitwarden currently sponsors “Smashing Security”).
I continue to believe that using a password manager – just about any password manager – is better than not using a password manager.
But I can’t bring myself to recommend LastPass now. There are better choices out there.
Where can I learn more?
There are some good blog posts on the topic by Wladimir Palant. Also check out this Mastodon thread by Jeremi M Gosney.



Thank you for sharing your thoughts and recommendations, Graham! ????
It is still unclear if the "notes" field within a password item is encrypted. All I know is the a "Secure Notes" item is encrypted which is not the same thing.
The notes field on site entries is along with secure notes. The developer of this third party LastPass vault parser clarified it and even posted on Reddit to confirm it.
https://github.com/cfbao/lastpass-vault-parser/wiki/LastPass-Vault-Format
https://www.reddit.com/r/Lastpass/comments/zzz5x4/notes_are_encrypted/
However, LastPass itself not confirming this hasn't helped, but it has been verified. If you want to confirm it for yourself, you can run your own vault through the tool and not specify the master password, this will then output data that's unencrypted only while the encrypted data will be scrambled in the CSV
Great article Graham. Easy to understand for someone that is not Jeremi or Waldmir.
After reading LastPass' statements it kind of reads like they didn't do much in terms of enacting post breach procedures. It sounds like the threat actor was able to somehow gain possession of another employee's credentials in order to access customer vaults? Wouldn't it have been prudent to change credentials almost immediately after the breach in early August?
What are the better choices than LastPass?
Bitwarden and 1Password.
Recommending another online password manager is tantamount to telling people to stay with LastPass. At one point people were praising LastPass and its the same with 1Password. There isn't anything 1Pass is gonna be able to do; eventually, they will get hacked just like the rest do.
Offline is where its at and thats it. Anyone recommending any online storage loses all credibility, IDC what type of security 1Pass is running. Humans are still responsible and humans are weak links to every security infrastructure in the world.
no, there is another private key on 1password, the master password is not enough to decrypt the vault, making it in theory impossible to bruteforce
That's right. 1Password talks about the secret key, and how it combines with your master password to offer another layer of security, here:
https://support.1password.com/secret-key-security/
This post does a good job of comparing LastPass with 1Password, Bitwarden and KeePassXC: https://alphasec.io/lastpass-vs-1password-vs-bitwarden-vs-keepassxc/
> I’ve always been a big fan of password managers (1Password has also been a
> sponsor of this blog and the podcast, and Bitwarden currently sponsors
> “Smashing Security”). I continue to believe that using a password manager –
> just about any password manager – is better than not using a password manager.
being in tech and security for many decades i guess i understood this kind of solution better or more paranoid and just clearly, its a bad idea and you still want to use a similar product?
some people never learn
Not sure why everyone says that "old" LastPass accounts were set to a low iteration count. I created a free account in 2020, and when I checked earlier this week, my account was set to 5000 iterations.
I had my account before that, and mine was set to 1!
I had heard nothing about this iteration count until now. It is incredibly negligent that they did not automatically or at least prompt me to change it.
How safe is Google Passwords Manager?
Thanks for a much more lucid summary than I have seen anywhere else. I used Lastpass for year and introduced it to a number of companies I worked at. I ditched it when they started charging to sync across mobile and computer and no longer use it on my computer.
I have a long and complex master password and hope that will be sufficient. I also took the opportunity to change the master password as that re-encrypts all passwords in my vault. I hope that would be to a different encryption than they were before the change and therefore possibly secure again.
To clarify, the hackers have a copy of your vault from a point-in-time when the theft occurred. Changing the master password now will re-encrypt what is on Lastpass.com, but will have no effect on the vault copy that the hackers have.
It's comparable to thieves making a copy of your computer hard drive. They have the copy. You can change the locks on your house to prevent the thieves from getting in again and even reformat your computer hard drive. But the copy the thieves have will be untouched by any of those things that you do after the theft.
I think the general idea is to set the password encryption iteration count as high as one can tolerate. On my copy of LastPass it was set to just over 100,000 and on a trial version of Bitwarden it was also about 100,000 (with an extra 100,000 being applied to the copy on the server). In the referenced OWASP "cheat sheet" the 310,000 iteration count was being used in an example of equally hard defenses, but it doesn't say "recommended."
Bitwarden recommends testing the selected iteration count on all of your devices to see if you get acceptable performance.
How do you find or set the iteration count?
Details from LastPass here:
https://support.lastpass.com/help/how-do-i-change-my-password-iterations-for-lastpass
You recommend both Bitwarden and 1Password, but later state 1Password has extra protect due to its secret key. Would that make 1Password more secure than Bitwarden?
Great article. What are your thoughts on Keeper Security as a password manager? I saw in a blog post on Keeper's Web site that 1Password "only encrypts at the vault level, and it does not encrypt every record. Additionally, 1Password is SOC 2 certified, but lacks ISO 27001 certification."
I'm trying to decide between the two offerings. 1Password's "secret key" feature seems like a differentiator from all the rest but Keeper's blog post about 1Password not encrypting each record is giving me pause.
I have been using Lastpass for more than 4 years after recommendations from couple of blogs I follow. But I am appalled by their response after all these hacks. I kept getting reasssured that it is minor and my data is safe. I planned to switch soon and by the time, I was ready to move on, I find that I am billed for one more year since it is set to auto renew. It is my fault as I should have been aware of all these predatory practices by most companies. I did call them on the same day I was billed, but they refused and said that I can still avail their services for a year !! I am extremely worried about the hack and this pisses me off more . Anyway, lesson learnt and run away from LogmeIn and Lastpass
I suspected the LastPass breach was much worse than they originally pretended it was, so I began transitioning to a new password manager after their first wishy-washy non-announcement.
I was upset when they chose Christmas eve to tell people the truth about just how seriously they had been hacked. The only businesses that release important news at Christmas are the ones who have something big they are trying to hide! I choose not to support companies that try to hide their huge failures like LastPass did.
They actually auto-renewed my account as well, and tried to tell me there were absolutely NO refunds for any reason, no matter how negligent their business practices may be.
The following lines from their Terms of Service allowed me to do a successful chargeback: "4.2.1. Information Security and Certifications: LastPass agrees to maintain appropriate organizational, administrative, and technical safeguards designed to protect your Content against any unauthorized access, loss, misuse, or disclosure, in accordance with industry standards." and "6. Disclaimer of Warranties… our entire liability and your exclusive remedy under this warranty will be, at our sole option and subject to applicable law, to provide conforming services, or to terminate the non-conforming services or the applicable order, and provide a pro-rated refund of any unapplied, prepaid, fees from the date you notify us of the non-conformance through the end of the remaining subscription term. "
The level of dishonesty displayed by LastPass management has ensured that I will never use any of their services again. I also refuse to work with any companies that their leadership team may migrate to as they leave that sinking ship.