
When there’s so much bad news in the world of cybersecurity, it’s always good to share a positive story.
Researchers at cybersecurity firm Unit 221B have revealed that they have been secretly helping victims of the Zeppelin ransomware decrypt their computer systems since 2020.
Victims of the Zeppelin ransomware since its emergence in 2019 have included businesses, critical infrastructure organisations, defence contractors, educational institutions, and the healthcare and medical industries.
Typically demanding a ransom in the region of US $50,000 (although ransoms of over US $1 million have also been requested), Zeppelin leaves a calling card alongside the files it has encrypted.
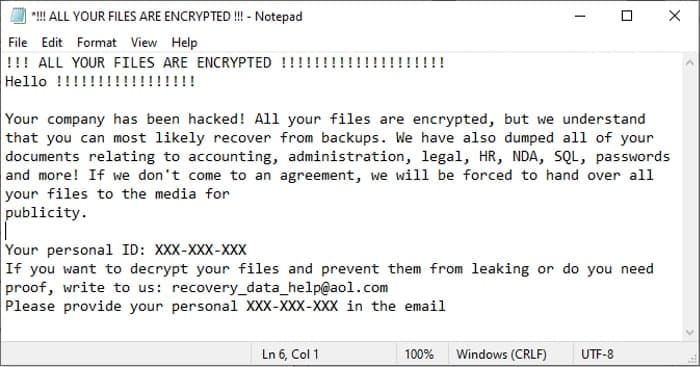
Your company has been hacked! All your files are encrypted, but we understand that you can most likely recover from backups. We have also dumped all of your documents relating to accounting, administration, legal, HR, NDA, SQL, passwords and more! If we don’t come to an agreement, we will be forced to hand over all your files to the media for publicity.
The boffins at Unit 221B turned their attention to the Zeppelin ransomware after it targeted charities, non-profit organisations, and even homeless shelters – all of which clearly have deserving things to direct their money towards than the pockets of extortionists.
Or, as a blog post on Unit 221B’s website eloquently puts it:
A general Unit 221B rule of thumb around our offices is:
“Don’t [REDACTED] with the homeless or sick! It will simply trigger our ADHD and we will get into that hyper-focus mode that is good if you’re a good guy, but not so great if you are an ***hole.”
What Unit 22B’s researchers discovered was that Zeppelin’s encryption flow contained a vulnerability, that temporarily left a key in the registry. Full details of how Unit 221B discovered the flaw, and were then able to exploit it to crack keys on victims’ computers, are contained in a technical blog post on the firm’s website.
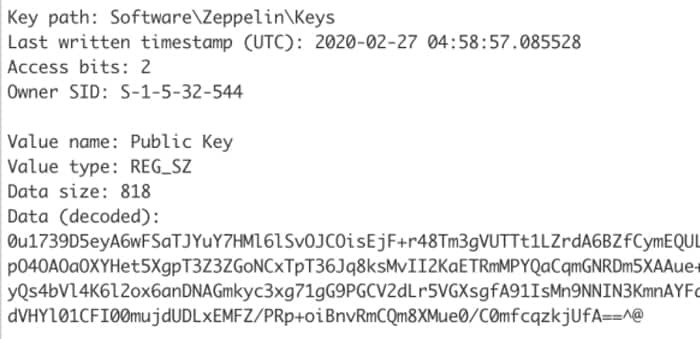
The end result was that the researchers were able to produce a decryption tool that victims could run on infected systems, that would extract a key. The keys would then be uploaded to some significant computing power – 20 servers (each with 40 CPUs on board) donated by Digital Ocean – which would eventually, after six hours huffing and puffing, crack the encryption key.
It’s an impressive achievement, which will have helped organisations that badly needed assistance in the aftermath of a Zeppelin ransomware attack.
And what also impresses me is that the researchers kept their discovery quiet all of this time, knowing that if they bragged about their accomplishment it would only reach the ears of the ransomware gangs using Zeppelin – who would change their approach, and put yet more organisations at even greater risk.
It is only after a significant drop in the number of Zeppelin victims that Unit 221B has chosen to reveal details of its work. The tool continues to be available free of charge, and should still work against even the latest versions of Zeppelin.
The researchers credit the security experts at Cylance for their prior work analysing Zeppelin, hosting giant Digital Ocean for providing computer power, and the developers of CADO-NFS for their assistance with the project.



No free bugs!!!