A vulnerability allowed users of a healthcare data portal to access other users’ medical records and thereby view their sensitive information.
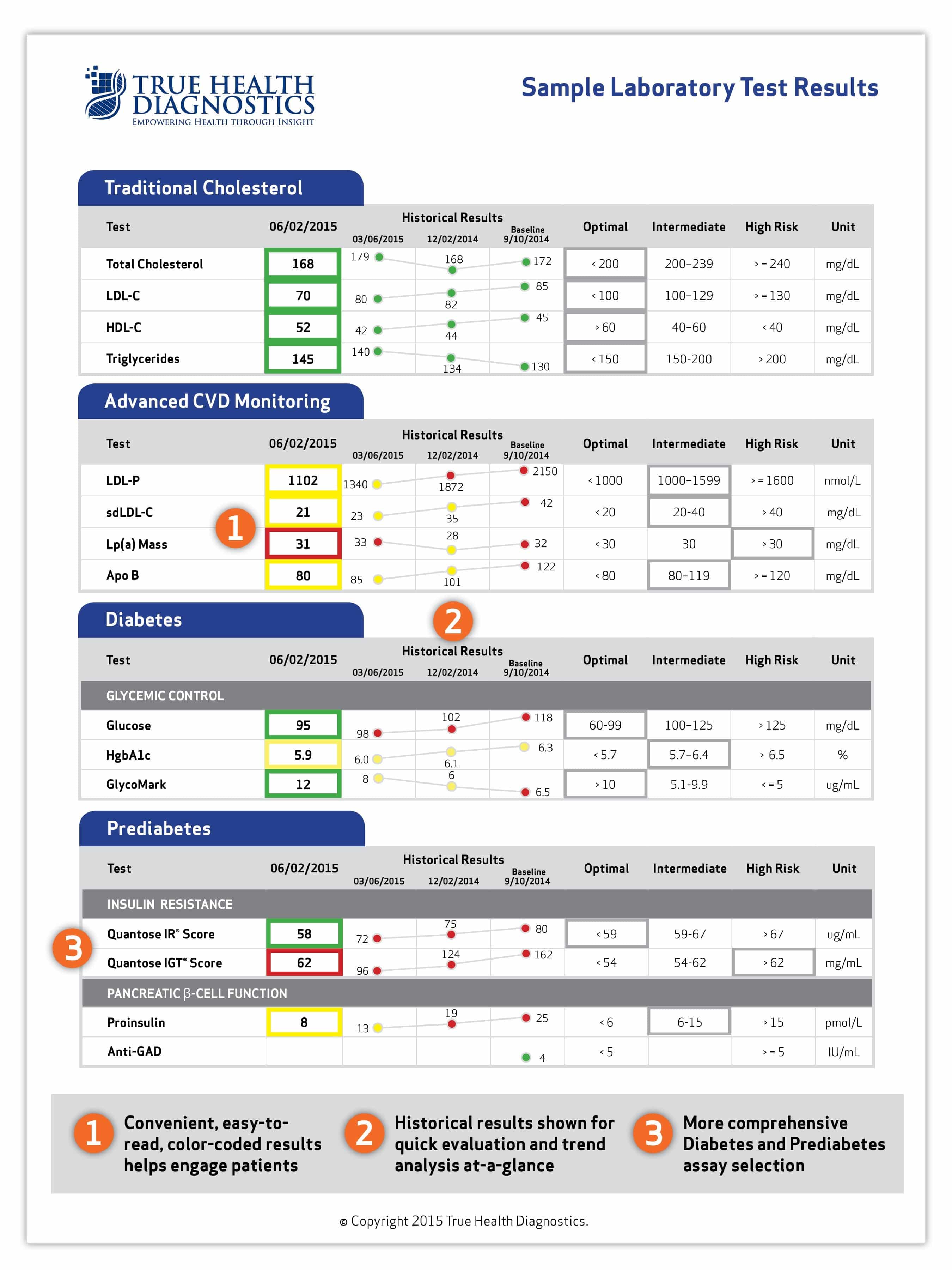
In the beginning of May 2017, security blogger Brian Krebs heard from Troy Mursch, who’s received lab results through True Health Diagnostics over the past two years. The Frisco, Texas-based company provides services that assist in the “earlier detection and management of chronic diseases.” As such, it provides a portal where account holders can review their lab results in PDF form.
It’s a worthy mission…as long as there are measures in place to safeguard users’ medical information.
Unfortunately, True Health Diagnostics came up short in this regard by overlooking a key vulnerability. As Krebs explains in a blog post:
“To demonstrate the flaw, Mursch logged into his account at True Health and right clicked on the PDF file for his latest health report. He showed how the site would readily cough up someone else’s detailed health records and blood tests if he modified a single digit in the link attached to that PDF record and then refreshed the page.”
Yikes, that’s no good! Even an unsophisticated attacker with some free time on their hands could have figured that one out. Had they stolen a user’s account credentials via a phishing attack, they could have gained access to other members’ information, which they then could have monetized on the dark web and/or leveraged to conduct secondary attacks.
True Health didn’t like the sound of the bug when Krebs notified the company about it. That’s why it immediately disabled the healthcare data portal and reportedly addressed the issue over the following weekend. Currently, the diagnostics firm is still looking into how long the vulnerability remained open. But it said in a statement to Krebs that it’s confident the issue didn’t cause significant damage:
“Upon discovering the potential for registered users of our patient portal to access data for individuals other than themselves, we immediately shut down the system in order to resolve any vulnerabilities. True Health has total confidence that all patient records are fully secure at this time. We regret this situation and any harm it may have caused.”
Let’s hope True Health is right. According to the numerical sequence of health records accessed by Mursch, the flaw could have exposed as many as two million patients’ information.
Acknowledging the threats posed by ransomware and other digital attacks to healthcare organizations, companies need to do all they can to prevent an unauthenticated party from viewing someone else’s medical information.
Alex Holden of Hold Security says companies should not use sequential account numbers in sensitive PDF documents, should require patients to authenticate themselves with a username and password before accessing their sensitive information, and should encrypt any sensitive portions of a link pointing to healthcare records. He also recommends that companies use security measures to verify that an account holder is logged in when they are viewing their medical information.