Mozilla has released Firefox 52, the latest incarnation of its web browser.
Most of you probably don’t realise that that’s happened, because most of you are using Google Chrome as your browser. Or, if you’re on an iPhone or iPad, you’re probably using the mobile edition of Apple Safari.
But for those of you who relish using an alternative web browser, this is an important Firefox update.
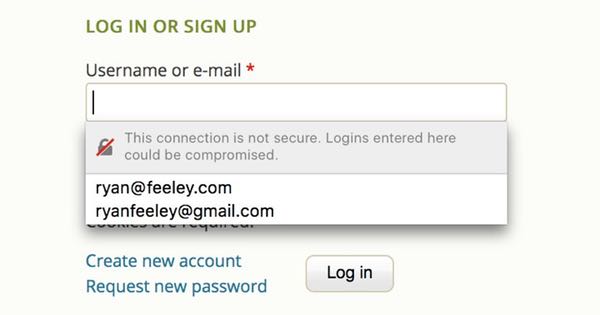
As well as patching dozens of security vulnerabilities, Firefox 52 takes a leaf out of Google Chrome’s book and now warns if you attempt to enter sensitive information into forms on unencrypted HTTP websites.
You’re most likely to see Firefox’s warning message if you try to type your password onto a webpage that is not secured with HTTPS.
This connection is not secure. Logins entered here could be compromised.
You then have a choice.
You can either attempt to contact the webmaster of the site you are attempting to log into, whack them around the head with a rusty mackerel, and then ask them to join the rest of us in the 21st century.
Or you could turn a blind eye to your web browser’s palpitations about being asked to enter sensitive credentials on an insecure form and go ahead regardless.
Personally, I wouldn’t recommend that second option.
It’s good to see Firefox helping web surfers keep proper control of their private information, and the new feature follows soon after Google Chrome introduced similar functionality for its users earlier this year.
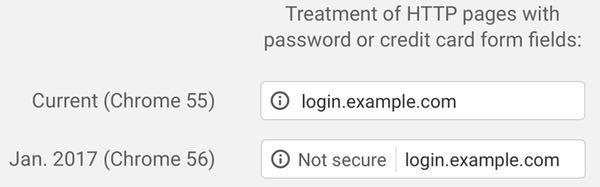
Fortunately, more and more websites are recognising the benefits of switching to HTTPS – making life harder for computer criminals eager to eavesdrop on your password – but we’ve still a long way to go.

It's great to see this feature making it to another common browser – I wonder when the others catch up…
I feel very secure running Firefox 52.0 on my Windows 95 box… ;-)
Graham: I'm glad you welcome this feature, and I'd agree that making users aware is a good thing, but *what are they supposed to do*? They can't force the webmaster to secure the connection, and if the task they're trying to complete is important and urgent they have to proceed *anyway*. So, assuming they take option 2 – which is what most people are going to do – what should they do afterwards to remediate the situation?
wg
First step: Call them out publicly on Twitter, asking why they're being so lax with their customers' security.
Second step: Find a friendly tech-savvy journalist :) who can bring more attention to the incompetence.
Third step: Take your business elsewhere, and tell them why.
There are a few other things you can do. If you're on an open Wi-fi network in somewhere like a cafe, hotel, airport, etc, fire up your VPN. Agreed, you should be doing that anyway when on an open Wi-fi network, but the browser warning you like this ought to be a good reminder of why you should be doing it.
And yes, the VPN will only protect the data along part of its journey, but it will rule out a MITM eavesdropping your traffic on the open Wi-fi network. Or even a rogue open Wi-fi network masquerading as a legitimate one, which is very easy to do.
Alternatively, never use open Wi-fi networks at all. A secured mobile Wi-fi hotspot on your phone is a good option, or a wired USB tether to your phone will do the same but keep the battery topped up.
Separate to the above, something else you can do is edit the URL and try HTTPS instead of HTTP. We might question why a site would be serving HTTPS but not redirecting to it automatically, but it's worth a try anyway.
Finally, ask yourself is this really the site I think it is? Did you make a typo in the URL? Did you click a link that looked correct, but on closer inspection has a small difference, e.g. an extra character? It could be an imposter website, or even if the URL looks correct, you could be a victim of DNS spoofing. Do a web search on how to do a DNS query to a 3rd party DNS server, e.g. Google on 8.8.8.8 – you can then compare the IP addresses resolved with those resolved on your own device.
The warning from Firefox or Chrome is a good reminder to bear all of the above in mind.