
In the end, the FBI didn’t have to call upon the self-proclaimed l33t social engineering skillz of John McAfee.
The US Department of Justice has managed, with the help of an unknown third party, to successfully access data held on an iPhone 5C used by one of the dead killers who struck in San Bernardino, California, last December.
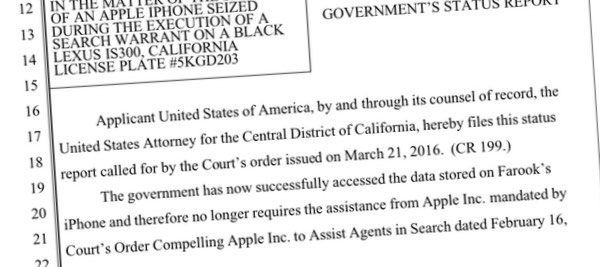
In a court filing, the DoJ said that it no longer needed Apple’s assistance and withdrew demands that the technology company build a special version of its iOS to unlock the iPhone – something which many in the computer security world felt set a dangerous precedent.
This latest development marks the end of the battle between the FBI and Apple, but it will probably only be a matter of time before the issue raises its head again – whether between the FBI and Apple, or another technology company being ordered to build backdoors that can allow law enforcement to breach systems built to protect our privacy.
Maybe next time the FBI will take on a company which doesn’t have the backbone of Apple, and isn’t as prepared to stand up – meaning a precedent might be set much more easily. In some ways I’m disappointed that this important debate didn’t come to court. After all, then at least we would know if law enforcement agencies could compel Apple’s software engineers to write code that they didn’t want to write.
Some questions, of course, remain.
Perhaps foremost, has the FBI told Apple how it managed to break into the iPhone 5C? If not, then potentially many other iPhone 5C users and their data could be at risk. One hopes that information has been shared with Apple, in case there is a way it can better protect consumers – but in the current climate I am not especially hopeful.
Secondly. who helped the FBI? Last week reports appeared that an Israeli mobile forensics company called Cellebrite was providing its services, and might have a way of extracting data from the iPhone 5C.
https://www.youtube.com/watch?v=Y48KDl9Link&rel=0
The FBI hasn’t said who helped them, and Cellebrite hasn’t yet confirmed its involvement – although they do say that they have worked for the FBI in the past.
And finally, will we ever find out whether anything of interest was found on Rizwan Farook’s iPhone?
One thing we do know, says iOS expert Jonathan Zdziarski, for stronger security iOS users should be using a long alphanumeric passcode to lock their devices rather than a short four or six digit numeric PIN.
The final word, for now, goes to Apple:
“From the beginning, we objected to the FBI’s demand that Apple build a backdoor into the iPhone because we believed it was wrong and would set a dangerous precedent. As a result of the government’s dismissal, neither of these occurred. This case should never have been brought. We will continue to help law enforcement with their investigations, as we have done all along, and we will continue to increase the security of our products as the threats and attacks on our data become more frequent and more sophisticated.”
“Apple believes deeply that people in the United States and around the world deserve data protection, security and privacy. Sacrificing one for the other only puts people and countries at greater risk. This case raised issues which deserve a national conversation about our civil liberties, and our collective security and privacy. Apple remains committed to participating in that discussion.”



Congratulations, Apple morons. Here I thought your encryption and security features were strong, and it would take a court order and your help in weakening the security features so that a brute force attack could even be possible on a case-by-case basis – but it turns out that a 3rd party was able to publicly bypass it.
Is this supposed to make me feel more secure and have confidence in your products?
The FBI might be bluffing though. The article says that no third party has confirmed doing it, nor has the method been made public.
Deceiving your enemy and making them think you know something that you don't is a crucial part of spycraft in the intelligence world.
Apple is not the enemy here, terrorists are. Apple merely obstructed an investigation, up to a point. I don't believe that Cellebrite got past the encryption – I think a backroom deal was done with Apple. They get to save face, the FBI gets to show the world how clever it is, they both win.
Especially as the general belief is that there is nothing worthwhile on the phone anyway.
Ash, there is not a single product in the world that is entirely secure. Every product is subject to scrutiny based, usually based on how popular a device is or what the impact could be if a device were to be compromised.
I invite you to look up Schneier's Law and consider what it means.
You're in for a world of hurt and much disappointment if you think life is that simple.
I might add that cryptology is exceedingly complicated. But since you're so capable you could be very rich since you can clearly make it much more secure. Perhaps we should set up crowd fund for you? We can call it 'Volcanic Encryption: Encryption As Hard As Diamond and as Dense as Ash'. What say you? You could be the hero of the century by making encryption 100% secure! Isn't that what you want? If not why are you insulting Apple for a flaw in their security (and nothing in this world is 100% secure)? Are you sure your name isn't Tom, Bert or William? If not are you sure you're also not one of the trolls of Morgoth?
The fact we don't even know what the vulnerability is and the fact you only insult Apple (as far as security) clearly without much (if any!) experience in security means that the only 'moron' (if I am to use your wording) is 'Ash' aka you (in which case I say that 'moron' is far too generous). Those who only criticise (insult but offer nothing constructive) do so because they have nothing intelligent to offer and it makes them feel better about themselves (just like bullies). I admit that we all (and I am no exception) sometimes come across as doing this BUT more people TRY to offer something but might fail at times due to poor wording/haste/not thinking it out completely/other things. But you didn't even try. Are you capable?
Incidentally, it wasn't publicly circumvented. The fact that those involved haven't commented on it (last I knew) means it most certainly is NOT public.
I imagine the weak point may be the 'Apple Account' – this is something which Apple could essentially 'hack' into without actually breaking any encryption. Apple forces a reset of the users password – as Apple own the mail servers, they can intercept the password reset process and allow the FBI to reset the password. Without Apple's help on this, the FBI could just take control of the suspects email account and reset the password that way.
IIRC, that is what the FBI did already but the issue was accessing the data which hadn't been backed up to the cloud in the last 2 weeks before the suspect's demise.
I'm in the camp that believes the FBI are bluffing but I would be very happy (and interested) to be proved wrong.
That a third party can do this does seem concerning – but I have to say I was with the FBI on the legal side – still dont really understand the concerns – except that of course the criminals would use phones made by those outwith the reach of the US courts perhaps –
Ash, it was an old phone with old technology inside. "Congratulations" for jumping to the conclusion their products are insecure.
Clearly their security is strong otherwise the FBI wouldn't have needed help but it's only as secure as the end user.
If somebody wants to lock down an iPhone (and they know what they're doing) then they are able to do so. Other device manufacturers don't give tech-savvy users the ability to secure their phones to the same degree that Apple do.
Even this 'unknown' third party acknowledge they can't break long alphanumeric passwords. A four digit PIN can be broken even with the device wipe functionality enabled because of how it was implemented in old devices (the iPhone 5C here). If the owner of the phone had used a long password then it'd be game over for the FBI.
An iPhone is secure out of the box, an Android phone isn't. For most users enabling security be default protects them.
All this cases shows is that the FBI have lied to the courts. The third-party has had this functionality (against old phones) for a few years. The real reason the FBI wanted to win was to set precedent because they know full well that the newer devices can't be broken into – that frightens them. They wanted a court case to make the law books so that they could go up to Apple again in the future and compel them to break into their own products.
There's hundreds, if not thousands, of iPhones other states want broken into but the third-party haven't been able to help them (despite selling their products to those Police Departments). Why? Because they are the newer iPhones. That suggests that the newer more modern security is working.
What's the end result? Apple are now securing their products even more and law enforcement will suffer because of their lies to the public, government and courts.
And finally, will we ever find out whether anything of interest was found on Rizwan Farook's iPhone?
Everyone continues to forget that the phone was owned by the local government. The phone was never owned by the terrorist. It was a work phone assigned to him. In my opinion the phone was very badly managed by it's "owner".
Most likely we wouldn't find out what is on the phone no matter who 'owned' it – even a corpse like McAfee offered to social engineer. How is it badly managed? I don't think so. It's nothing new that corporations give out mobile phones. Before that they gave out pagers.. and now too they use email. Those are only some examples. To call this bad management is ignorance if not absurd. Or do I misunderstand you?
Be careful how you parse the FBI' statement: "the government has now successfully accessed the data on Farook's iPhone." This could mean anywhere from "we broke the encryption and now have access to the plaintext data" or "we copied the data to another device". And no, I don't think we (the public) will ever here exactly how the FBI accessed the data, or what information they found on the iPhone (assuming successful decryption.) In any event, the "All Writs" law is still on the books, simply waiting to be dragged out again sometime in the future for the same purpose.
Relevant in some ways. But even if they haven't bypassed the encryption completely you can be sure they are working on it – and that's the most important thing to keep in mind. But what I saw (I think in this case it was the BBC) is that a senator mentioned to the FBI that they make use of mirroring (funny that a politician could think of this but the FBI couldn't .. also scary in that it shows the incompetence of the FBI). Which is to say copy the data to another device so they could brute force that copy (maybe there was some limitation here but it's still ironic that a politician would think of it over the FBI). They didn't seem to understand it and certainly not enough to go through with it (or look into it); that they went to a third party to access the data makes me think it wasn't through mirroring (but probably will never know for sure). But regardless of what they did, the fact they're bypassing security is a problem. I agree with your opinion that they won't reveal how they accessed it and they won't reveal what they discovered (or perhaps more like did not discover).
This article, like many, parrots without comment Apple's technically false claim that the US court ordered them to create a back door. It is not clear why columnists who should know better, and probably do, continue to do that.
It also repeats, again without comment, the legally false claim that the case raised civil rights and privacy issues in the US. The government's order did no such thing. The government has a properly issued search warrant that entitled them to search the iPhone, and has the iPhone owner's permission as well. In the US, a valid search warrant answers the question of civil rights and liberties, and privacy, in the government's favor, and much the same is true in most other countries, unfortunately including some where basic legal protections are weaker.
What the US court ordered certainly would have set a precedent – that a manufacturer of certain types of device could be required, with compensation for direct costs, to help law enforcement officials execute search warrants, including help to bypass some security protections. Given the protections inherent in US law, that precedent is not obviously dangerous, constrained as it is by warrant limitations and judicial review. It is arguable that it would be better for manufacturers like Apple to help execute warrants more or less openly than for law enforcement agencies to have tools of unknown capability and availability that they (and possibly others) could use, perhaps without the formality of obtaining a search warrant.
You're a member of the group which is the dream of all governments (and potentially scammers and similar) because you're so easily deceived.
Technically you're right; it isn't a backdoor generally. But it's still making an exception to circumvent security and YES the precedent most certainly IS serious AND dangerous. This isn't the first time the FBI has demanded similar things and not all are for 'terrorism'. C.f. the case in New York where the FBI wanted phones broken into over DRUGS. Thankfully that was thrown (and it happened after this one started but it is obvious to anyone unlike your kind who understands how exceptions work; one exception turns into many exceptions) out BUT the fact of the matter is the FBI went to similar effort (the real problem).
As for warrants: before mobile phones were common if you didn't have a warrant for a wire tap BEFORE the call you were out of luck (for the actual correspondence). Maybe they did but if not I question why they didn't go to the carrier for further help (as in getting meta data). Perhaps that's less relevant in some ways and certainly doing so would be less serious than them wanting to bypass security (which is extremely hypocritical and extremely dangerous). Oddly enough the government seems to be ahead on this one whereas they stupidly are behind on most other laws related to technology. Actually, they aren't quite ahead here: not yet. They're working on it though. That's scary. It's a disgrace.
You're an example of one of the ways governments become more corrupt over time. Yes. You most certainly are whether you realise it or not.
Edit: And the reason they refer to backdoors is it is a generalisation that is understood; the point is they want a way to bypass security (in cases) for their own agenda. Saying it is or isn’t a backdoor in this way is semantics – and the governments love people like you who don’t understand this.
"In the US, a valid search warrant answers the question of civil rights and liberties, and privacy, in the government's favor…"
Oh. My. God. You obviously are in desperate need of an upgrade in your ability to discern between what is legal and what is right. Racial segregation used to be legal. That didn't make it right. The two classes are not congruent.
Your blind faith that legality automatically "answers the question" of civil rights, liberties, and privacy—in the U.S., or anywhere else—betrays a naivete that enables the state to get away with systemic erosion of fundamental rights. If people like you are in the majority, people who value their freedom are an endangered species.
Oh, and Graham? Thanks for the mockery of leetspeak. It's been a long time since I've seen that and it's probably been longer (than the last time I saw someone do it) since I last mocked it. That you're referring to McAfee makes it even better. And more appropriate.
On a more cheery note may I point out that this event may/should result in Apple, Google, Facebook et'al improving/strengthening their encryption which would be to everyones benefit except that is the FBI and NSA
I may be over simplifying things here but the 5C has a finger print sensor right? Well, if the shooter still has his thumb then pretty simple to get in…..crazy I know.
The iPhone 5C doesn't have a fingerprint sensor. I think you're mixing it up with the 5S.