The FBI might have found a way to unlock the iPhone of one of the San Bernardino shooters that would not require Apple’s assistance.
In a filing submitted late Monday in a central California federal court, the FBI asked that a court hearing due to take place on Tuesday be canceled and that court proceedings be suspended until April at the earliest.
The Register reports the court has granted the U.S. Department of Justice its request.
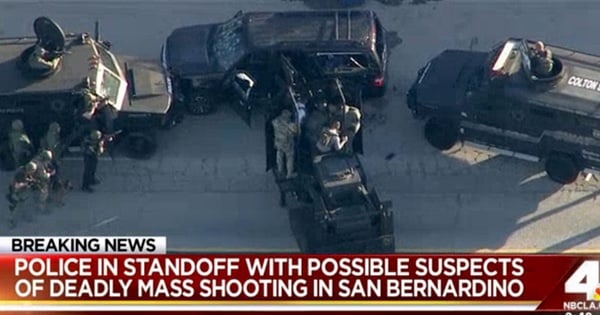
This postponement marks an unexpected reversal for the FBI, which has argued in multiple court filings that it absolutely requires the assistance of Apple in order to unlock an iPhone formerly owned by Syed Rizwan Farook, one of the two individuals who perpetrated the mass shooting and attempted bombing in San Bernardino, California last December.
Apple has refused to abide by the DOJ’s demands, arguing that it would need to compromise the security of all iPhones and not just Farook’s device if it were to assist the FBI. Many privacy advocates and well known figures in the tech community, including the CEO of Google, have subsequently rallied behind Apple in defense of its position.
Here is a video Graham Cluley posted on his YouTube channel last month about the controversy:
For a full understanding of this ongoing controversy, please refer to this timeline of events.
As revealed in Monday’s filing, the FBI has responded to Apple’s refusal by exploring other options through which it could unlock Farook’s iPhone even as it has filed court documents reaffirming the necessity of Apple’s assistance, reports The Guardian.
 These efforts have led several “outside parties” unaffiliated with the U.S. government to come forward and offer their technical expertise to the Department of Justice. It is now evident the FBI has chosen to investigate one such party’s method and to report back to the court afterwards.
These efforts have led several “outside parties” unaffiliated with the U.S. government to come forward and offer their technical expertise to the Department of Justice. It is now evident the FBI has chosen to investigate one such party’s method and to report back to the court afterwards.
Security expert Susan Landau, a professor at Worcester Polytechnic Institute in Massachusetts, feels this sudden abrupt face represents what she has felt to be true all along: that the FBI is lacking in technological capabilities:
“The FBI has been viewing security as an impedance rather than a necessity. That the bureau may not need Apple’s help to access the phone points up what’s been true in this case all along: the FBI needs to strengthen its own technological capabilities.”.
For its part, Apple and its defense attorneys are a bit suspicious about these recent developments. Here is what Alex Abdo, an attorney with the American Civil Liberties Union, which filed an amicus brief on behalf of Apple in the case, was reported as saying by The Washington Post:
“This suggests that the FBI either doesn’t understand the technology well enough or wasn’t telling us the full truth earlier when it said that only Apple could break into the phone.”
Apple has gone on to request that the U.S. government share information with the tech giant if it is able to unlock the device. However, if the FBI decides to drop the case, it will be under no obligation to do so.
FBI: Hey Apple, wanna fight?
Apple: Yeah okay, let's fight
FBI: Ok, gonna fight you now
Apple: K let's fight.
FBI: Uh something just came up— Evan Greer (@evan_greer) March 22, 2016
Monday’s filing certainly seems to contradict earlier statements made by the FBI. At this time, however, we neither know the identity of the outside party nor whether their proposed method will work. All we can do is wait and see what happens next.



So where's John McAfee hiding out with his hareem, dogs and guns these days? I really hope the FBI has taken him up on his offer. I'd love to be a fly on the wall of *that* meeting.
If I wanted terrorists to "believe" their encryption tools may not be all that impervious, I'd plant a similar story…
I heard on NPR last night that the phone doesn't belong to Farook, but rather to the municipality that he was working for. Further, the municipality is waiving any rights it might have. Farook has no privacy rights in someone else's phone. This case does not seem to involve all of the privacy concerns, and the protections of multiple Constitutional Amendments as had been previously reported. The issues of everyone else's privacy, and private encryption issues versus the law enforcement 'need to know' is still out there.
I can't speak for the municipality, but government property issued to users in my domains comes with a hefty warning which boils down to a complete lack of privacy as to anything on that phone.
What I think the issue is, is that We The People don't trust the government not to abuse the tool that the FBI is iinsisting that Apple create. There have been multiple reports of NSA abusing the rights of people in the telephone records they previously held. There have been multiple examples of the government not protecting the data we have been required to give them, such as security clearance forms, tax returns, email, and much much more. If Apple is ultimately required to make the tool the FBI demands, how will the FBI keep it out of the hands of abusers in its own staff, keep it away from those that seem to enjoy hacking the FBI, and once they share it with other law enforcement agencies (they will of course do that), that the Sheriff of Little Town USA, with a SOHO firewall won't let it get snatched.
This is old news. It has long been known that the iPhone belonged to the local government and they 'waived' rights to it. They are also the same imbeciles who effectively locked themselves out of the device (by changing the iCloud password) which prevented it syncing with Apple servers. On top of that they failed to install a corporate backdoor (a master override password) which any administrator who manages iPhones can do – it's called Mobile Device Management (MDM). MDM policies are commonplace but for some reason San Bernardino didn't bother.
Incompetence has been the catchphrase of this case.
Personally I doubt the phone has anything of any value on it. Can you honestly say that you think he'd store his plans on a phone issued by local government? He probably realised his employer could monitor all of his communications hence why it's unlikely he used it to communicate with people of interest.
We heard that he physically destroyed all of his other devices and they cannot be recovered. If he prepared himself in so many other aspects what makes us really believe that this phone will contain secrets?
OK not to be daft, but has anyone tried unlocking the phone with the corpses' thumbprint? I mean it seems so obvious.
An iPhone 5C doesn't have a Touch ID sensor!
However even if this was a newer device (i.e. with a Touch ID sensor) it wouldn't work because you're required to enter your password whenever:
you restart your device
more than 48 hours have elapsed from the time the device was last unlocked
the device has received a remote lock command
after five unsuccessful attempts to match a fingerprint
Obviously the first two are the most relevant points but even if they didn't apply the police would only have a 50/50 chance to match his fingerprint before the device locks itself with the password after five unsuccessful attempts. But this is all academic because the 5C doesn't have a fingerprint sensor.
As the first part of the article clearly shows, what the US Attorney demanded does not weaken the security of any iPhone other than the one targeted by the search warrant issued previously. The digital signature requirement, along with the fact that Apple was not required to deliver the modification to the FBI, effectively guarantees that. The order for Apple's assistance does not require that they deliver their work to the government, and as the author states clearly, the government could not use it if they did.
It certainly is true that the government and others view the case as a precedent. I is publicly known that there are several hundred other iPhones for which search warrants have been issued or will be sought, and if the government wins its case Apple might be asked to assist in the same general way. What most articles, including this one and the accompanying video, and nearly all comments on this subjects fail to take notice of are the legal and procedural requirements that go with search warrants. These equally protect iPhone users (whether or not they encrypt their devices) and users of devices with Android or other operating systems. The All Writs Act on which the order to Apple is based, does not enable the government to request anything but what is necessary to carry out other lawful court orders, in the case at hand, a search warrant.
When the 'secret' method leaks then it compromises the security of every iPhone user in the world. Forget Apple's digital signature – there are ways around that which security researchers have published. Even the NSA are speaking out against the FBI being allowed to do this.
The misuse of the All Writs Act probably doesn't apply because CALEA seems to exempt this form of communication. The All Writs Act is a 'catch-all' act and therefore cannot be applied.