
Researchers have found it takes only 200,000 bots to jeopardize the availability of 911 emergency services across the United States.
Mordechai Guri, Yisroel Mirsky, Yuval Elovici of the Cyber-Security Research Center at Ben-Gurion Univerisity of the Negev have determined that bad actors can leverage a mobile botnet to launch a distributed denial-of-service attack against 911 services.
To do so, attackers need only exploit the FCC’s E911 First Report and Order (1996), which states wireless carriers must transmit all emergency calls to Public Safety Answering Point (PSAP) regardless of whether they are subscribers to a mobile network.

All they need is a mobile botnet under their control. As the researchers explain in their paper:
“The adversarial attack model… is as follows: The attacker builds a botnet of mobile phones by infecting devices with malware…. At the appropriate time, the attacker signals the botnet to continuously call 911…. This command is signaled via the attacker’s command and control server (C&C) located somewhere on the Internet or by sending covert SMSs to the bots.”
Attackers can infect each device via malicious SMS/MMS, malvertising campaigns, or malicious apps (as is the case with the DressCode Android malware).
The DDoS botnet may consist of non-anonymized (NA) bots, which call 911 from a mobile device’s main operating system and thus expose their International Mobile Station Equipment Identity (IMEI) and International Mobile Subscriber Identity (ISMI). Emergency services can use those values to block a call if they determine the bot is spamming their systems.
To circumvent those blocking measures, attackers can instead use anonymized (A) and persistent anonymized (A*) bots that conceal their information.
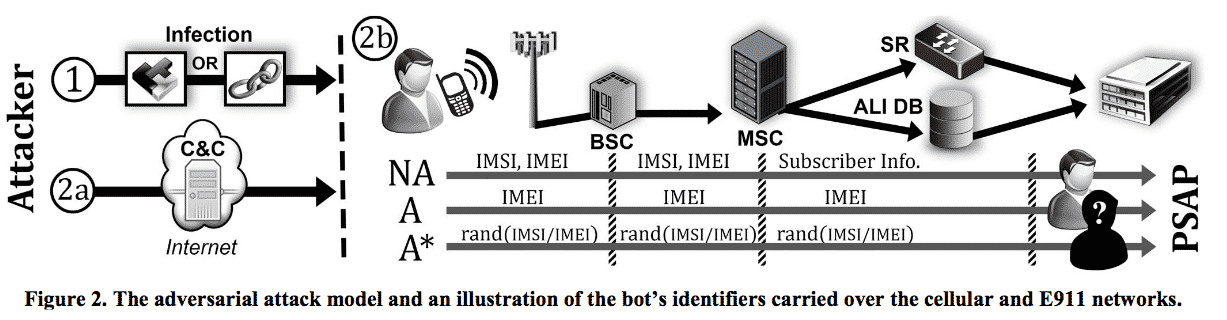
The researchers accomplished these particular bot implementations by infecting the baseband firmware with a rootkit.

The only step that remained was for Guri, Mirsky, and Elovici to test their bots.
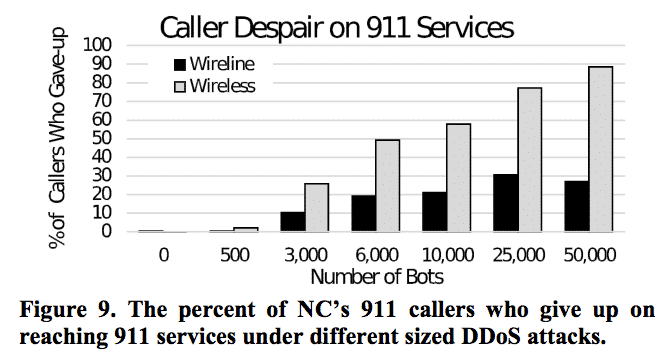
In a simulated DDoS attack campaign conducted in a lab environment, not only did the researchers verify the NA, A, and A* bot concepts. More importantly, they proved that with as few as 6,000 bots, an attacker could deny half of wireless emergency calls from ever reaching 911 services at the state level.
More bots means more firepower, so with a botnet numbering in the hundreds of thousands of infected devices, an attacker could potentially wreak havoc across the United States’ entire 911 framework.
The simulated attack confirmed that point:
“At the country-level, we found that as little as 200,000 bots, distributed across the population of the US, is enough to significantly disrupt 911 services across the US…. This means that an attacker only needs to infect ~0.0006% of the country’s population in order to successfully DDoS emergency services (In 2014, the USA has a population of ~319 million…). Under these circumstances, an attacker can cause 33% of the nations’ legitimate callers to give up in reaching 911.”
Scary stuff, to be sure!
So how can we prevent attackers from carrying out a DDoS campaign against our emergency services?
The researchers have some ideas. First, 911 services could stop accepting calls from those who lack a mobile service, which presents a thorny ethical question which would need to be debated by the FCC. Alternatively, all phones could relay some identifier to 911 services, whose call centers could use a “Call Firewall” to block DDoS activity.
However, these efforts would take the cooperation of government, security professionals, emergency services, mobile service providers, and others, so don’t expect significant change anytime soon.
For a deeper look into how a mobile botnet could threaten American 911 emergency services, download the researchers’ paper.



'The researchers have some ideas. First, 911 services could stop accepting calls from those who lack a mobile service, which presents a thorny ethical question which would need to be debated by the FCC.'
Terrible idea. It is a serious disregard for life and it is contrary to 'do no harm'. And what if someone can't afford service even if only temporarily? Should they be denied a chance at life? If a neighbour were to call for them they would have that chance so why shouldn't they have the chance just because they have no service? If the FCC were to debate it it would prove even more just how corrupt and disgusting the US government can be (in many respects 'IS').
Ask it differently: if it is morally and ethically wrong for an attacker to deny many people the right to emergency care (and it is) why or how could it even be debated making it acceptable for others to not receive care because they're unable to have phone service? (Arrogance, selfishness, cowardice and callousness to the extreme) Is there any difference? Can't get through because you don't have service or can't get through because of a service outage? There isn't any difference except that you might except this from bad actors but you'd not expect it from supposedly decent people. Anyone who doesn't see this frankly deserves to experience their own emergency and preferably 'a close call'.
I think you've misunderstood the article. What the researchers are suggesting is a system like we have in Britain.
You can't, contrary to popular belief, make a 999/112 call without a valid SIM.
Even if you've been disconnected for non-payment you can still make an emergency call. If you make hoax calls your SIM and handset will be blocked.
In the USA you can make the call without a valid SIM. Therefore you can't block the SIM. You wouldn't be able to block the handset as you can fake the IMEI.
The researchers therefore want a person to have a valid SIM to make a 911 call. For added security they suggest transmitting a unique, non-modifiable code so that if you repeatedly dial 911 they can identify you.
Am I missing something? 200,000 is ~0.06% of 319,000,000 rather than "~0.0006%" as above (and in the paper itself). Are they asserting that every American owns 100 mobile devices?