Google is working to remove malicious apps that enlist infected Android devices into a botnet from its Play Store.
Alon Menczer and Alexander Lysunets of the Check Point Research Team found that the malware, which goes by the name DressCode, exists in 40 apps available for download from the official Google Play Store.
That doesn’t include an additional 400 applications found on third-party websites.
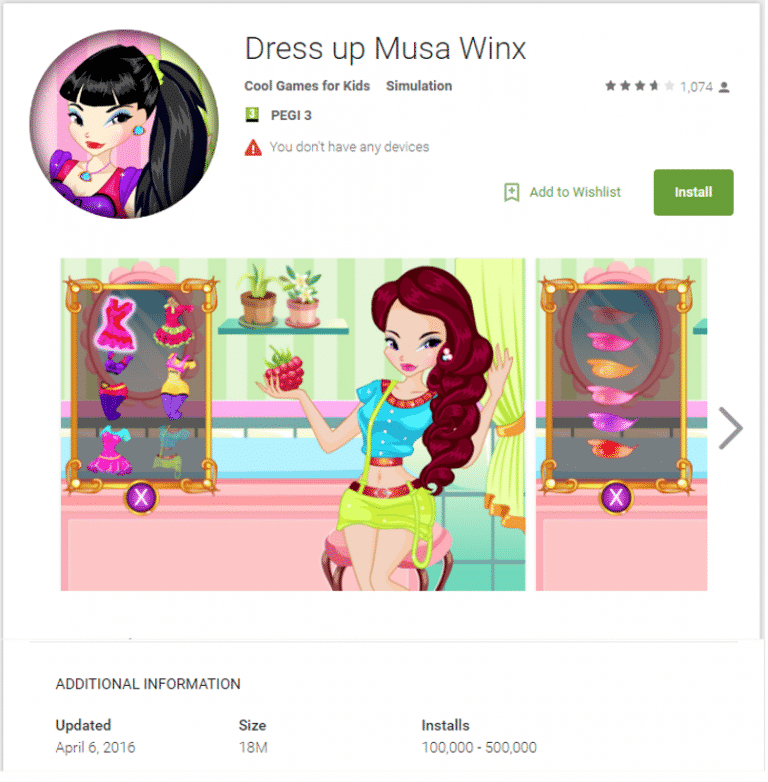
Wow. For something so cute, DressCode isn’t messing around… especially when as many as 500,000 users have downloaded each infected app from Google Play.
So just what does the malware do?
According to Menczer and Lysunets, nothing at first:
“Once installed on the device, DressCode initiates communication with its command and control server. Currently, after the initial connection is established, the C&C server orders the malware to ‘sleep,’ to keep it dormant until there’s a use for the infected device. When the attacker wants to activate the malware, he can turn the device into a socks proxy, rerouting traffic through it.”
That capability gives those behind DressCode with a few options. First, they’re able to use all of the infected devices as a botnet based on proxied IP addresses, presumably to disguise ad clicks and generate false traffic (and, by extension, cash for the its authors).
Second, by routing traffic through devices, DressCode’s developers can access available networks and conduct secondary attacks like data theft against victims as well as the organizations for which they work.
Check Point’s researchers detail one such attack in the video shown below:
Clearly, DressCode poses a serious threat to users. That’s why Menczer and Lysunets haven’t wasted any time in notifying Google, whose researchers are working to remove the malicious apps as we speak.
This isn’t the first time security analysts have come across malware hidden in apps available on Google Play, either. In the past year, malware has masqueraded as an IQ test app, a mobile development tool, and a photo-altering service, among other disguises.
Aside from stealing users’ information, some malware have had the ability to display advertisements and download unwanted applications.
With that in mind, Android users have every incentive to protect themselves against mobile malware like DressCode. They can do so by avoiding all “DressCode”-themed apps they come across on the Google Play Store.
As a rule of thumb, they should also be extremely wary of ever installing apps from anywhere else than the official Google Play store.