
More than 400 Android applications available for download on Google Play Store are distributing the DressCode trojan.
The malware originally made news back in late-August, when Check Point’s research team found 40 instances of DressCode in the official Google Play Android app store, and a further 400 overall.
It would appear the trojan has been busy since then. As explained by Echo Duan, a mobile threat response engineer at Trend Micro:
“Trend Micro detects this as ANDROIDOS_SOCKSBOT.A and has found at least 3,000 Trojanized apps. The Trojanized apps were hosted by several well-known Android mobile markets, including more than 400 detected on Google Play. They range from the recreational apps like games, skins, and themes to phone optimization boosters.”
One such infected app is the following Grand Theft Auto 5-themed mod available for Minecraft on Android devices:
As many as 500,000 unique users downloaded that particular app.
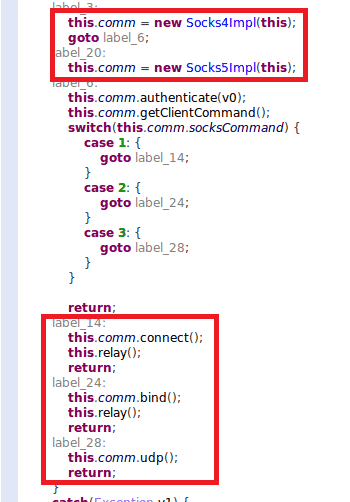
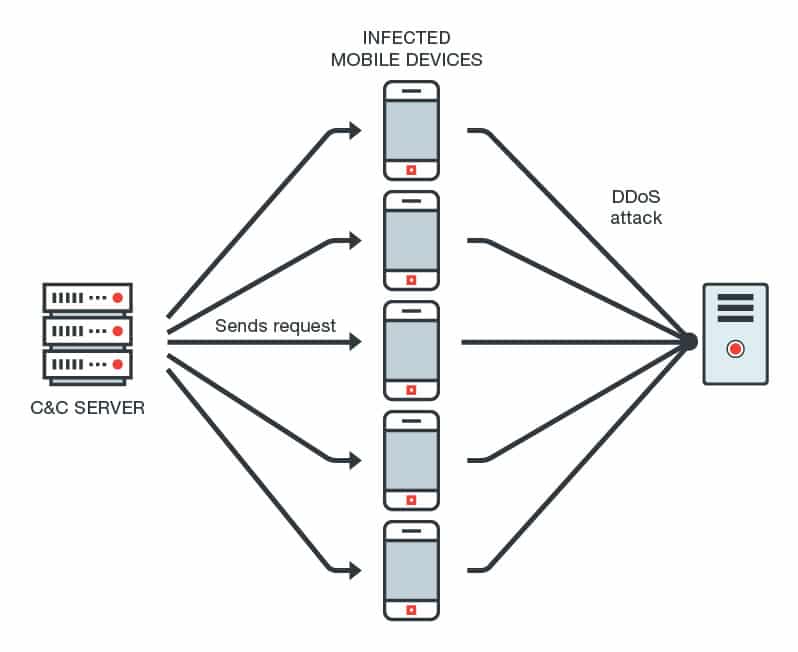
Aside from the growth of DressCode infections, the malware itself hasn’t changed all that much. Successful installation enables the malware to connect to its command and control (C&C) servers via a Transmission Control Protocol (TCP) socket. Whenever the C&C responds back, an attacker can create a TCP connection between themselves and the infected device. That link empowers the attacker to issue commands to the infected device via the SOCKS protocol towards several different ends.
Hmm… what kinds of ends?
Well, an attacker could target an internal server by gaining access to a victim’s network environment and bypassing a network access translation (NAT) device.
They could also compromise other devices connected to that network or leverage the SOCKS proxy to create something even more sinister. According to Duan:
“The malware installs a SOCKS proxy on the device, building a general purpose tunnel that can control and give commands to the device. It can be used to turn devices into bots and build a botnet, which is essentially a network of slave devices that can be used for a variety of schemes like distributed denial-of-service (DDoS) attacks—which have become an increasingly severe problem for organizations worldwide—or spam email campaigns. The botnet can use the proxied IP addresses also generated by the malware to create fake traffic, disguise ad clicks, and generate revenue for the attackers.”
DressCode is hard to spot in the infected applications because its malicious code only makes up for a small part of an app’s software.
With that in mind, users should be careful when installing apps from Google Play Store. That includes reading the reviews so that they can learn if anyone else witnessed some suspicious behavior when they downloaded the apps.
Users should also update their systems often, maintain an up-to-date anti-virus solution on their devices, and download apps only from the Google Play Store and not third-party app markets.


With this being at the top of google search when searching for google play apps, I am surprised you do not have a single comment. Ok maybe this one I am guessing if it is approved. I am an android app and game developer. Google play checks for any little thing to approve of an app or game. I find this hard to believe.
Now that you've told us about the DressCode malware in Android apps from the Google Playstore,, please tell us how to get rid of this malware.