A cryptocurrency-mining malware began exploiting a leaked NSA vulnerability several weeks before WannaCry sank its teeth into it.
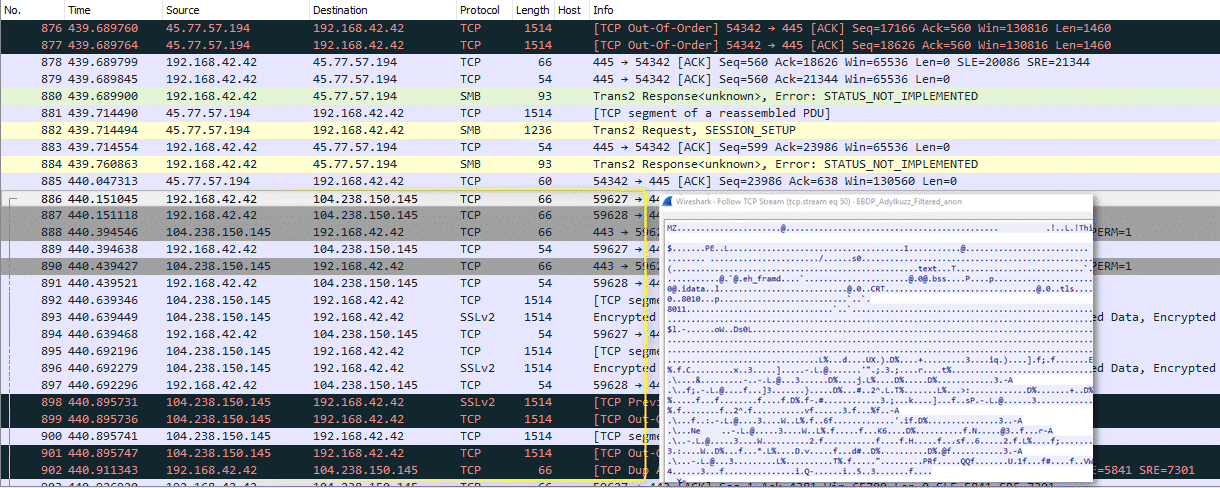
Proofpoint’s security researchers came across the malware while researching the global WannaCry ransomware outbreak that started on 12 May. This campaign leverages “EternalBlue” and “DoublePulsar,” two tools developed by the National Security Agency (NSA) and subsequently leaked by hackers known as the Shadow Brokers. The utilities allow WannaCry’s handlers to abuse a Windows vulnerability, leverage it to detect and spread to vulnerable machines on a network, and download the ransomware payload.
WannaCry had spread to over 150 countries and reached more than 200,000 victims.

The researchers expected to see the ransom message above when they looked at a lab machine vulnerable to EternalBlue. Instead they found a subtler threat: Adylkuzz.
This malware relies on virtual private servers scanning the Internet on TCP port 445 for distribution. If infection proves successful, it enlists victims in a cryptocurrency-mining botnet. But Adylkuzz isn’t interested in sharing an affected computer that’s capable of communicating over Microsoft’s Microsoft Server Message Block (SMB).
Security researcher Kafeine elaborates on that point:
“Upon successful exploitation via EternalBlue, machines are infected with DoublePulsar. The DoublePulsar backdoor then downloads and runs Adylkuzz from another host. Once running, Adylkuzz will first stop any potential instances of itself already running and block SMB communication to avoid further infection. It then determines the public IP address of the victim and download the mining instructions, cryptominer, and cleanup tools.”
In that sense, Adylkuzz blocks other threats like WannaCry from leveraging ExternalBlue to infect vulnerable computers.
That’s not cause for celebration, though. Using one of its multiple command and control (C&C) servers, Adylkuzz downloads mining instructions and software for Monero, a developing cryptocurrency which a Star Trek-themed ransomware is already using for ransom payments. These mining implements strain a machine’s computing resources when activated, causing a degradation of PC and server performance. They also result in a loss of access to shared Window resources.

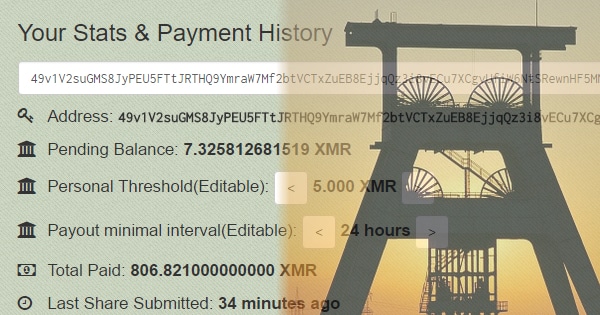
Payment activity associated with a single Adylkuzz-operated Monero address began surging on 24 April–well before WannaCry began exploiting EternalBlue on 12 May. The payment activity peaked at 11 May before dropping off, which could suggest the attackers are actively rotating addresses to evade detection.
But that might not be all the threat activity there is to see. Kafeine is concerned there are (and/or will be) others out there exploiting EternalBlue:
“Whether they involve ransomware, cryptocurrency miners, or any other type of malware, these attacks are potentially quite disruptive and costly. Two major campaigns have now employed the attack tools and vulnerability; we expect others will follow and recommend that organizations and individuals patch their machines as soon as possible.”
The prospect of additional attack campaigns explains why Microsoft is fed up with governments stockpiling vulnerabilities. As a result of hacks and leaks perpetrated by actors like the Shadow Brokers, hoarding security flaws ends up harming ordinary users. This fact, not to mention the corresponding need for governments to change their treatment of software bugs, becomes more apparent with each day spent in WannaCry’s wake.


