Researchers at DomainTools have issued an alert about a malicious Android app that pretends to warn users about those infected with the COVID-19 Coronavirus in their vicinity.
In truth, the app locks users out of their devices and demands that $100 worth of Bitcoin ransom payment is made within 48 hours. If payment is not made, the ransomware claims, the phone will be completely erased and pictures, videos, and social media accounts shared online:
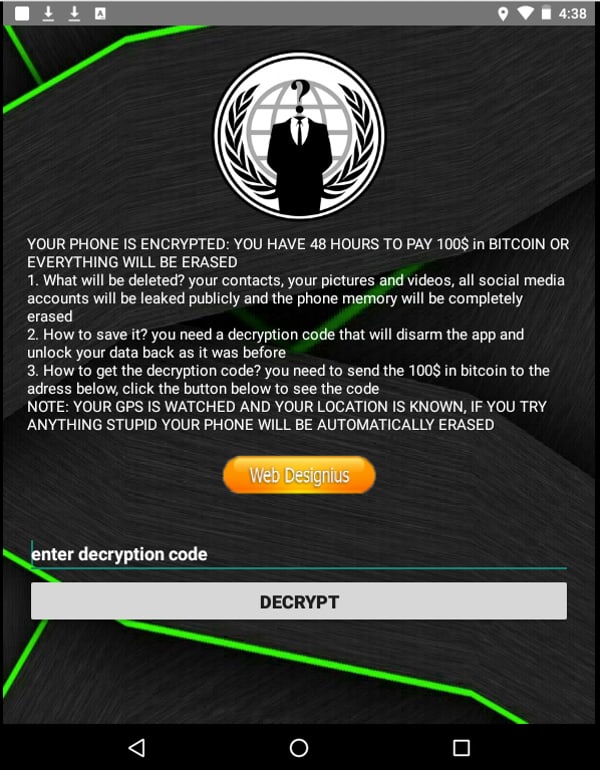
YOUR PHONE IS ENCRYPTED: YOU HAVE 48 HOURS TO PAY 100$ in BITCOIN OR EVERYTHING WILL BE ERASED
1. What will be deleted? your contacts, your pictures and videos, all social media accounts will be leaked publicly and the phone memory will be completely erased
2. How to save it? you need a decryption code that will disarm the app and unlock your data back as it was before
3. How to get the decryption code? you need to send the 100$ in bitcoin to the adress below, click the button below to see the code
NOTE: YOU GPS IS WATCHED AND YOUR LOCATION IS KNOWN, IF YOU TRY ANYTHING STUPID YOUR PHONE WILL BE AUTOMATICALLY ERASED
The researchers at DomainTools discovered the malware – which they have named CovidLock – after investigating the increased number of domain registered in the past few weeks related to Coronvavirus and COVID-19, many of which have been used to spread scams or false information.
In this particular case, the researchers discovered the malicious Android app was being distributed from a site called coronavirusapp[.]site (I don’t recommend visiting it), rather than via the official Google Play marketplace.
The fact that the app is only available from a third-party source does limit its ability to infect Android devices, as only users who visit the site, ignore the many warnings issued in the past about “side-loading” apps from unknown sources, and grant the app permissions to access the device’s accessibility settings and lock screen will be at risk.
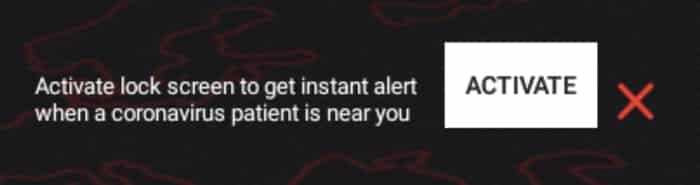
Activate lock screen to get instant alert when a coronavirus patient is near you
DomainTools says that CovidLock’s screen-lock attack will not work on devices running Android Nougat or higher (Android 7.0 or later) if an unlock password has already been set by the user.
Fortunately, CovidLock does not appear to be the most accomplished ransomware ever written – and so even if you are unlucky enough to have had your phone infected it may be possible to recover access to your data without paying a ransom. Reddit users report that they have successfully analysed the app and determined the decryption password.
As ever, despite its shortcomings, Google’s official Play Store is a safer source for apps than third-party unofficial sites. Furthermore, if you’re an Android user always be very careful about what permissions you grant an app. One careless choice could lead to your data and privacy being put at risk.
For more discussion of this topic, listen to the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Smashing Security, Episode 170: Pornhub, Coronavirus Apps, and Remote Working with Carole Theriault and Graham Cluley. Hello, hello, and welcome to Smashing Security, Episode 170.
My name's Graham Cluley.
Actually, in the last week and a half, I'm just releasing reruns because recording in my attic, the sound quality is not too bad, but it's different than the usual sound quality, different environment.
So I'm leaving the quarantine in like 2, 3 days. And then I'll return to normal scheduling.
But apparently a corona patient, one of the very first corona patients in Israel, boarded my train at exactly the same time. And you know how it is.
I mean, it's a long train, probably 1,000-plus people on the train.
At some point, I kept forgetting what day it was, because every day seemed like the last one.
It was in France somewhere in a cave. And he went apeshit, I think, after a few weeks.
Now on today's COVID-19 special, Graham tells us how to avoid being duped by scammy apps.
Ran is gonna talk about how Israel is using anti-terror tech to help combat the invisible enemy that is corona.
And I will help you newbie homeworkers out there make sure you have all your cyber bases covered. All this and much more coming up on this episode of Smashing Security.
COVID's Diary.
Some of them have the sniffles, some have sore throats, some aren't showing any signs of infection at all. They might be a bus driver, a cleaning lady, neighbours, partners.
Now, for a day or two, it seemed even the germaphobe-in-chief at the White House— he might be one of them, but he's now been given the all-clear— we are all quite understandably worried and concerned about not only catching the coronavirus, but also running out of toilet paper.
Yeah, exactly. I've just— I've literally just come back from the supermarket again completely bereft of all loo paper.
But if enough of us manage to hold it off for long enough, maybe we'll be able to give the hospitals the best chance to cope with the increased demand.
It's like, like you said, Carole, it's like a zombie apocalypse movie.
Wouldn't it be wonderful to have a magic wand that we could use to wave in front of people to determine if they're catching a virus? Maybe— That isn't a dolphin impression.
That's my Geiger counter, being able to tell who's got it. I would love one of those.
They come and they test you at home and you don't leave your home unless real life danger.
They are beautiful people, but they're also rather tough. You don't want to get on the wrong side of an Israeli.
Is there a bit of a macho bit of you which kind of thinks, oh, we can just sort of rough this out? Is that so?
And turns out there are apps which claim to do that. They actually exist.
People, do not type in that name of that website, because that website, which is by the way also run by a group of people who also run a website called Dating for Sex, which feels like tautology.
But at the top of this particular one, it has a banner which pops up, which invites Android users to get a real-time number of coronavirus cases based upon your GPS location.
Sneaky, sneaky.
And of course, this is something people want right now, right?
I would love to know if I should go down the bottom of the hill or not, or whether I should stay up here at the top of it, right? Where it's going to be safer.
Now, this isn't a Google Play app. This is an app which you get from a third-party site. So it's a sideloaded app.
And as we all know, although Google Play isn't perfect and there are malicious apps which get in it sometimes, it's a heck lot safer than downloading apps to your Android phone from any Thom, Dick, or Harry site.
So I would just assume if it's not in the Play Store, don't get it. So how do people download that? How does that happen?
Do you want to have a map to know if— and then mom would be like, wicked. Yeah, as long as it's free. Okay, got you.
So when he built the iPhone and the iOS operating system, it was all about incredible levels of control.
And it says, "Your phone is encrypted.
You have 48 hours to pay $100 in bitcoin or everything will be erased." And it claims to have grabbed your contacts, your pictures, your videos, all your social media accounts.
And it says it will leak them publicly and the entire phone will be completely erased and it locks your phone.
You can't use your phone anymore 'cause you have to enter the magic number, which it says you will only get if you pay the ransom.
Turns out that this ransomware, which they've called Covid Lock, doesn't actually encrypt or steal your files at all. The ransomware is lying.
All it has done is locked your Android phone.
So it's sort of mimicking that it's doing something. Doing things in the background. And then displays the ransom note.
And so you think, "Oh crikey, it must have done all this stuff in the background." It's done nothing of the sort.
And a new variant of the ransomware is now asking for $250 as opposed to $100. So the price has gone up.
But according to the researchers, and this is where we come back to Ran's point, the bitcoin wallet which it's asking to be paid has so far received absolutely nothing.
If you thought the world was having enough disaster, here's another disaster compounded, which is that the ransomware authors are a load of old rubbish.
They're not fulfilling their promises. They're not encrypting your data. They're not actually stealing your files, and they're not even making any money. Okay, but do—
One of the interesting things, of course, is that if you were infected by this, and at the moment it looks like it's just security researchers downloading it, rather than actual real victims of this.
But if you were to have your phone locked, the interesting thing is that the unlock code is actually hardcoded within it and is available for anyone to find.
So it's not even something which changes. So the unlock code, I can tell you right now, is 4865083501.
So all you have to do if you were unlucky enough to get infected, that's the solution. If only it was so easy to fix coronavirus, eh? Wouldn't that be good?
Because think about it, I mean, they probably invested like, I don't know, 1, 2 hours, few hours working on that app and the website. And that's all.
And if they get, I don't know, $100, $250, maybe $1,000 from like 4 or 5 people who really fell for that really silly scam, it's good money for a few hours of work.
They didn't invest any time in actually creating ransomware. So yeah, it could be smart.
And it actually gives you some hope for the future of humanity.
This gives us hope that the economy will be restored, that we won't face financial apocalypse because of all this horror which is going on right now.
Because we see actual entrepreneurial spirit in action, don't we? Because we're seeing these guys taking advantage of an opportunity.
Well, it's with some dread now that I say, Ran, what's your story for us?
I think it was the last time that we spoke, I also gave an example story from Israel because we've got lots of interesting news going around.
And actually, I think it was 8 hours ago, the government approved in a kind of a very hush-hush move and very quick decision for the, it's called, just a second.
It's the internal security force to track Corona patients' cell phones and report to people around them if they were in the vicinity of someone who was infected.
This is a bit clickbaity because it's not actually anti-terror technology.
It's a simple, you know, mobile tracking technology that you can contact the mobile companies, the mobile service providers.
And if you have the, you know, from the court, you have the proper documents, they'll give you the information about whoever is their client and where in the world he is moving around.
Basically the same technology that they use every day.
So for instance, imagine there is a train where a known coronavirus victim has been on the train, and would they use this to track other people who had been on the train to identify them?
Is that the sort of thing which is—
And then automatically they send messages to all the people whose phones were around this guy while he was moving around the world.
So if, for example, in my case, if the corona patient that was on my train was say in my immediate vicinity in the train, they probably could tell that from the geolocation of the mobile device and they could have sent me immediately SMS saying, you know, this guy who right now was tested positive, a week ago he was near you in the train.
So now go and test yourself or be quarantined. And I think it's a great idea basically because now you can really control the infection vectors.
If somebody is detected, you can get ahold of the people who were near him and everybody's got a cell phone.
And they are then all in quarantine for two weeks, and that happens everywhere, it's going to be an interesting time for us all.
All of them were quarantined because we don't know where that guy's been specifically on the train. Exactly.
If I knew he was in the same car as me in the train, I would be quarantined.
But if we knew that he was in the back of the train, I was in the front of the train, I would probably be safe. I wouldn't have to be quarantined.
So I think the potential of that kind of technology to really help control the epidemic sounds great. Really sounds great.
I think the only caveat here is that that decision, specific decision, which is a good decision basically, it was gotten to in a way which is very problematic because there's no parliamentary oversight over that decision.
And nobody prevents the government from abusing that. They just decided it. There's no oversight from judiciary system or the parliamentary system.
So nothing stops the government from tracking political rivals, you know, abusing the power as we are always afraid of governments.
So I think it's the process that's problematic here and maybe the practical use.
Let's take an example, for instance, Justin Trudeau, the boss of Canada, he's been self-isolating and his wife, I believe, was infected by coronavirus.
Now, I then heard that Idris Elba, the actor, also infected. He's also infected. Turns out he met up with Justin Trudeau's wife.
And now I'm not pointing any fingers here, but we all know what Idris Elba's a bit with the ladies in terms of the ladies' reaction.
I'm just saying, they were clearly in proximity, and that's possibly how it happened. Maybe it happened at a conference instead.
Anyway, I'm just saying there's clearly privacy angles here and this information could be used.
And I mean, people in Israel, of course, are talking about it, saying, well, this is obviously an invasion of privacy, but the consensus is that, okay, this is probably a good idea in the short term, not a good idea in the long term.
You know, you guys though, you keep thinking about yourselves in this time of crisis, and you're forgetting a very important industry that is seriously impacted by this.
Can you think what it is?
Maybe actually, maybe there's probably some niche hazmat suit smut somewhere or something.
But if the Free Speech Coalition said in an announcement that it's asking the producers to voluntarily cancel all shoots through to March first so that performers stop shooting new content with people who aren't part of their households.
I've never heard it called shooting new content.
It's not like there isn't an awful lot out freely available. You don't have to go down the supermarket and find it on a shelf. It's everywhere, for goodness' sake.
Why would you need more?
Apparently China has announced a spike in divorce requests, claiming that the coronavirus has forced couples to spend too much time together during their quarantine, and they're just like, I have married a frickin' bozo.
And that's one of the ways we're trying to contain the spread of this contagion. And for a lot of us, that means working from home, which turns out is a big opportunity.
Those of us that have that opportunity should be feeling really blessed right now because there are millions of people that don't have that.
Now, for those of us that have been doing it for some time, we've inadvertently optimized our situations over the years, haven't we? And we've made our environments pretty bearable.
We know our neighbors, we have a snack cupboard, you know, we have hobbies and daily routines to try and manage all that stuff — entertainment, productivity, all that stuff, talking to people.
Because in the office, it was kind of obvious that I was choosing not to talk to people, but now at home, I can get away with it much more easily.
I don't know, 1 in 10. So 1 in 40. Oh, really? So 1.5 million people work from home. So 1 in 40 of workers work from home. And in the States, it's closer to 1 in 30.
So that means there are millions of people out there that are currently being asked to work from home for the first time.
Twitter has told people to work from home, Amazon, Google, NASA, JP Morgan, Samsung, the list goes on.
And I think all of us know something or two about security, and we know one or two things about working from home.
So, I thought we could share a few of our tidbit advice with our listeners to help them get through this. So, let's get the boring security stuff out of the way first.
So, my first piece would be that orgs really need to provide a to-do list for people to ensure that their home environment is safe for them to do work from and to access files and all the stuff they're supposed to do.
Some home workers are going to be asked to use their personal machines. Others will have dedicated working machines. Others will be waiting for machines to be delivered.
And the first big security nightmare, I think, is making sure that that home machine is safe to access work files and services.
So big companies out there are gonna know what to do, right? But there are some companies that are facing this for the very first time.
Yeah, I would say make sure you're not using the default password that was provided with your router.
Some of you with kids out there are gonna be having that problem of how do I get the kids, keep the kids off this machine so they don't play their games and don't get on it?
Because not everybody has a house full of tech and this might be the only piece of decent equipment in the house.
So making sure that the passwords are not known and not shared just because you can't be bothered to go put it in and don't let them play with it.
And if they do, I think you need to report it to IT.
I think companies should provide them with laptops from work because for many people, I think the home machines are vulnerable because we download stuff and we browse unsafe websites, whatever.
And I mean, I have 6, 7 people working for me. I can never be sure what their home environment is. I can never trust it.
So I would probably give them laptops from work and you only say you only access the company's, you know, IT infrastructure from these computers.
Don't log in from your home computer. That's probably a corrupted and virusful environment in the day to day.
The hardware manufacturers are going to do well at least if they manage to keep their supply chains going.
But I think from the security point of view, ideally they are going to be using an approved computer which has been checked over by the IT team rather than Lord knows what from Windows 95.
You'd have to probably bring a technician to actually operate this or set up the install.
But that's another option because giving people the option to log in from, I mean, it's a horrible environment, the home computer with games from the kids and everything.
There's probably a large percentage of malware ransomware hiding in those files anywhere. So I wouldn't give them the option to log in from their personal computers.
That's too big a risk, I think.
And one of the things to think about is organizations really ought to have a route so that staff know what to do in case there's problems, like who to call, what are the emergency procedures.
Think, for example, little Jimmy just stuffed a peanut butter sandwich into one of your laptops.
If they're running a computer, whether it's one that your company has provided or one which they have themselves, then it needs to be up to date with security patches.
It needs to be running up-to-date antivirus software.
You're probably going to have to have two-factor authentication in place to allow them to log into the company network remotely. You've got 3 of my 5.
Full disk encryption as well, because if you've got the sensitive data, company data, you don't want that laptop being stolen or mislaid at some point.
And number— is— What haven't I mentioned?
And in those cases, it is very nice to be able to wipe and reinstate from where you were. So keep a backup.
They've got something very cool I think you're going to like a capture the flag competition which can win you $100 in the form of an Amazon gift card.
If you want to join in the fun, visit domaintools.com/smashing to enter the capture the flag competition before it closes on the 1st of April, and may the most geeky listener win.
LastPass ensures your employees have secure access to their work applications and provides remote employees the ability to securely share passwords across teams in order to stay on top of critical projects.
If you want to learn more, visit lastpass.com/smashing. On with the show.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish. Doesn't have to be security-related necessarily.
And many people are like Ran, and they've been locked up in their houses. And we saw Italy—
And hence, I was rather bemused to see an announcement from a website which said that it would be giving free access to its premium version to everyone in Italy for the entire month.
And the name of that website is Pornhub. And so Pornhub, who are quite good in the PR department, they're quite good at getting their name in the press. Amazing. They are amazing.
They announced that everyone in Italy can have free access to— apparently there is some premium version of Pornhub. I can't imagine what that gets you.
But anyway, that's what more you need, really. But anyway. More porn. I suppose. But—
Steam apparently just celebrated 20 million users in one day, which broke all records.
Lots of people are using their VPN to pretend to be in Italy to access Pornhub.
So apparently they're getting swamped by lots more requests than normal. And they've had to— apparently they are adding new servers as fast as possible to cope with the demand.
Obviously, there are supply chain issues.
See, they know how to live. I like the Italians. Actually, you know, I read another article. I think it was yesterday, something like that.
From Pornhub, they have what's called Pornhub Insights. It's a regular website. It's not, you know, it's just for research. Really, it's for research.
It doesn't have any porn, but it gives lots of interesting insights on statistics that they gather from the website.
Just need to check you for coronavirus. Just give you this little injection here.
No, I mean, actually, Pornhub is a great place for statistics because that website gets tremendous amount of traffic. And browsing the insights is fascinating.
I mean, it's not my pick of the week, but it's fascinating. Oh my God.
It's called earth.nullschool.net and it's a Google Earth-like visualization of global weather, winds, atmospheric pressure, ocean currents, etc.
And I would really recommend visiting it. I mean, if you're a weather buff, it's amazingly pretty because the animation is fantastic. You can see winds and circulation.
It's very interesting to watch that. I mean, everybody is usually focused on the weather in their specific location.
But when you zoom out, the weather over the Mediterranean, and how the weather in the UK is influenced by what's happening in Iceland. Is this live? Is this live? It is.
I think it's refreshed every few minutes or so. It's almost live. Maybe there's a short delay, but it's taking the data from lots of various resources.
Carole, what's your pick of the week?
So I asked my other half, right, what he thought my pick of the week should be. And he said, have more sex. What? So I'm just—
And what are they going to be called? What's the generation going to be called?" Oh. "Millenovids?" The COVID generation.
And you can't find gloves to save your life anywhere, would you consider putting two condoms on each of your hands? I think I would.
I'm recommending a podcast that should cool him down because it is called Cold.
From the very beginning, police suspected it was her husband Josh Powell, okay, that he was responsible for the murder, right? But they've never arrested him.
And this podcast is 24 episodes, each an hour long. And it's by this host who's an investigative journalist who I think is completely obsessed with this whole story.
So he plays the whole interview between the husband, the father, the one they suspect of murdering, and the cops. And you get to hear everything.
And he's also interviewing the detective at the same time, so you get to hear his view 10 years on, on what he did right and what he did wrong. I don't know.
There's just something quite glorious about it. You've got 24 hours of entertainment there if you need something to do other than talk about the virus. Sounds fantastic.
I've listened to 10 hours, so I felt it was fair to come on the— So anyway, I recommend if you like true crime and it's an unusual— he's, you know, I love it when someone really is into their topic, right?
And you can tell they're just nuts for it and they've really gone into it. So not only will this calm my husband down, so I recommended it to him, but any of you. Yeah.
So if you need something hot, go to Pornhub. If you need something cold, check out Cold podcast from Wondery.
It's quite difficult to find via search, so I will put a link into the show notes for you.
What's the best way for folks to do that?
And you can follow me on Twitter @MaliciousLife or @RanLevi, R-A-N-L-E-V-I.
Our aim is to keep going unless one of us gets sick. Also, a huge thank you to this week's Smashing Security sponsors, LastPass and DomainTools.
Their support helps us give you this show for free. Check out smashingsecurity.com for past episodes, sponsorship details, and information on how to get in touch with us.