 There’s an interesting story in The Telegraph today about the hack of mobile phone retailer Carphone Warehouse which became public at the weekend, and saw the personal and banking details of 2.4 million customers put in danger.
There’s an interesting story in The Telegraph today about the hack of mobile phone retailer Carphone Warehouse which became public at the weekend, and saw the personal and banking details of 2.4 million customers put in danger.
According to The Telegraph‘s article, an unnamed source with knowledge of the attack claims that the company’s online retail systems were bombarded with a DDoS attack “as a cover to help them infiltrate the retailer’s systems and perpetrate one of Britain’s biggest ever data thefts.”
Hmm.
Okay, first thing’s first.
How would the source know that any distributed denial-of-service attack suffered by Carphone Warehouse was linked to the hack? DDoS attacks are run through botnets of compromised computers around the world, so it’s not as though it’s likely that they would be able to compare the IP addresses of the hacking and DDoS-ing computers.
Secondly, if a large amount of data was taken from Carphone Warehouse (which in turn also impacted customers of OneStopPhoneShop.com, e2save.com, Mobiles.co.uk, iD Mobile, TalkTalk Mobile, and Talk Mobile) then is it possible that the hackers’ attempts to probe Carphone Warehouse’s systems and exfiltrate its data might have themselves given the appearance of a DDoS attack?

In other words, “oooh.. our site’s a bit sluggish”. “Yeah, well, it’s because 2.4 million customer records are being stolen from under your nose, dumbo.”
Of course, it’s hard to shed any meaningful light on the claim without some real information from the affected companies as to what happened and how.
It certainly is possible that a DDoS attack could have been used as a diversion to distract the attention of the company’s IT security team, or that a tidal wave of unexpected traffic hitting their servers might have made the company relax some of its regular network rules, and made it easier for the attackers to sneak away with the stolen data.
But it’s equally possible that the hackers attempted no such thing.
Frankly, the only people who know what happened are the hackers themselves and (perhaps) Carphone Warehouse and the other affected companies.
What we do know is that the news that Carphone Warehouse had been hacked came out at the weekend, days after they first detected that they had a serious security problem.
Some have suggested that the company deliberately delayed the announcement until the weekend in order to try to bury the story. That is a view I’m sympathetic with, but I’m also sure that staff wanted to be sure of their facts, and precisely what customers might have been impacted, before saying anything that was likely to send all of their customers into a blind panic.
After all, it’s not always possible to know what precisely has occurred, and whether systems are now secure, on day one.
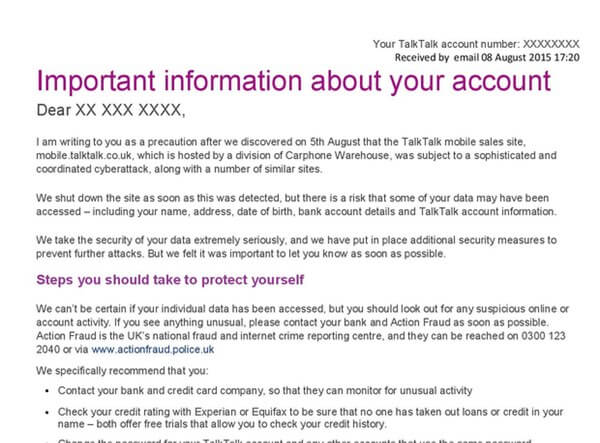
If you’re curious, you can read the extremely similar statements that the firms have published for their customers, recommending that affected individuals notify their banks and credit card companies, and look out for suspicious account activity:
- Talk Talk: Potential issue affecting the personal information of mobile customers
- Mobiles.co.uk: Important data information issue 8th August 2015
- iD Mobile: Important data information issue 8th August 2015
- e2save Mobiles: 8th August Data Information Notice
- Carphone Warehouse: Important data information issue 8th August 2015
Naturally, they all say that they take security seriously. A phrase that has become something of a cliché for organisations post-breach, and is somewhat difficult to believe when some of the sites continue to suffer from elementary HTTPS certificate mismatches.




The idea that mobiles.co.uk takes security seriously is a laughable. The ssllabs.com report says all you need to known : vulnerable to the POODLE , uses SSL 3 , RC4 SHA1withRSA and not supporting forward secrecy and that if you over look the fact the certificate is not trusted.
https://www.ssllabs.com/ssltest/analyze.html?d=mobiles.co.uk
Thee's more and more evidence suggesting that the Guardian story was spot on about this being a DDOS attack. You offered no hard data to back up your speculation. You ought to print a retraction for putting out such rubbish.