 It has just become that little bit easier to rob someone’s online bank account.
It has just become that little bit easier to rob someone’s online bank account.
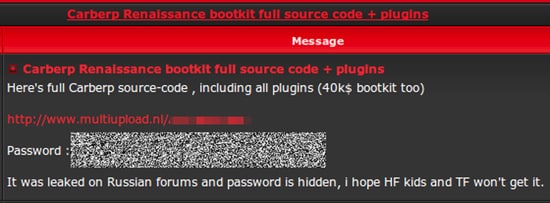
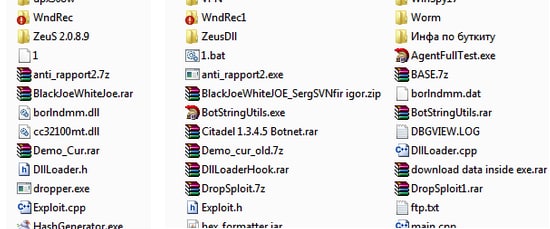
Peter Kruse, a security researcher at CSIS, has confirmed that a password-protect archive distributed on underground forums contains the source code for the notorious Carberp banking malware kit.
What’s worse, the password has now been published too – making it child’s play for someone with bad intentions to “roll their own” version of the malware.
Of course, anything which makes it easier for online criminals to create new malware has to be considered bad news.
And, as a result of this leak, it wouldn’t be a surprise to see the malware split into numerous different strains, as rival hacking gangs adapt the code for their own malicious ends.
Even if the resulting code contains similarities which anti-malware products can target in order to reduce the risk, the glut of different malware samples will continue to grow – and no doubt some innocent internet users will suffer as a result.
Carberp has been closely associated in the past with the Blackhole Exploit Kit, and has been seen frequently targeting computers by exploiting unpatched Java vulnerabilities through drive-by download attacks.
One possible silver lining is that those responsible for the Carberp code may now find it harder to monetise their creation, as if the code becomes widespread there will be little incentive for other online criminals to cough up the cash to pay for it.
Furthermore, the source code will hopefully also be closely examined by the authorities in the slight chance that it contains any tell-tale clues as to who might have written it.
The sheer fact that the code (which clearly had a significant value on the underground cybercrime market) has become available does suggest that there has been a schism in the Carberp gang, which we pray might lead to their eventual demise.
Here’s hoping the gang’s internal issues ultimately lead to its unravelling.


