How do you feel about paying a subscription for software?
Are you happy to pay a monthly fee to get new features as soon as they are developed, helping to support software houses, or do you think you should only have to pay once – or, perhaps, not at all.
It’s definitely the case that many people dislike paying software subscriptions, and resent that more and more products are moving in that direction. And perhaps that’s why Qbix, the developers of a popular Mac scheduling app called “Calendar 2”, recently shipped a version of their software with an alternative revenue-generating feature.
Rather than paying a flat fee of $17.99 or a 99 cents per month subscription to gain access to all of Calendar 2’s advanced features, the app now offered “All advanced features for free” if you allowed it to “unobtrusively” generate the Monero cryptocurrency in the background.
Now, I don’t necessarily have a problem with cryptomining *if* it is done with the full, conscious permission of the computer’s user, who is aware of the possible downsides.
Unfortunately, users complained that the app was cryptomining *without* their explicit permission.
@SGgrc @QbixApps Calendar 2 for Mac (from the App Store) launched a cryptocurrency miner without my permission. Then it ate 200% CPU until I found it and killed it. I didn't expect a miner infection from an App Store vendor. Wow. It runs the xmr-stak Monero miner.
— Fred Laxton (@fredonline) March 12, 2018
Security researcher Patrick Wardle analysed the app, and also managed to grab a screenshot of some of the poor reviews it was receiving on the Mac App store.
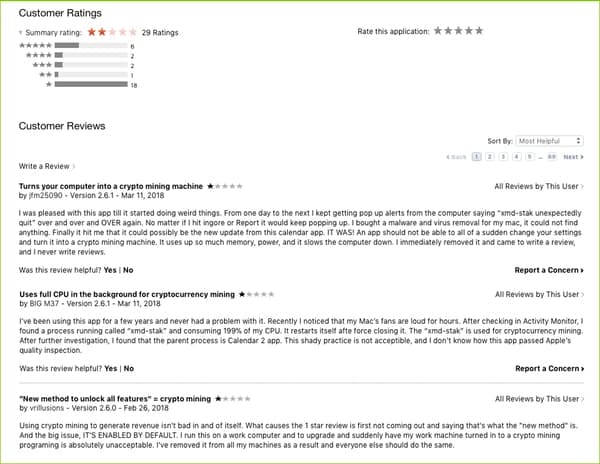
“This shady practice is not acceptable, and I don’t know how this app passed Apple’s quality inspection.”
“An app should not be able to all of a sudden change your settings and turn it into a cryptomining machine. It uses up so much memory, power and it slows the computer down. I immediately removed it and came to write a review, and i never write reviews.”
Okay, so this would be bad enough. But what’s worse is that the buggy cryptomining version of Calendar 2 was distributed via Apple’s Mac App Store, a marketplace that you expect to be safer than third-party sites because developers have to jump through some many hoops to have their apps approved.
The appearance of a cryptomining app in the official Mac App Store either suggests that Apple is allowing in apps that are open about cryptomining, or that Apple missed it.
And if Apple missed it, what other apps might be secretly harbouring malicious code in the Mac App Store?
If the complaining users are to be believed, the app may have been opening about its cryptomining but a bug meant that the cryptomining occurred even when users declined to participate.
 The app has now been pulled from the Mac App Store, and developer Qbix has blamed the problem on a “perfect storm” of bugs that meant it didn’t work as intended.
The app has now been pulled from the Mac App Store, and developer Qbix has blamed the problem on a “perfect storm” of bugs that meant it didn’t work as intended.
As Ars Technica reports, Qbix thought their app would “only” use 10-20% of a Mac’s computer power, depending on whether it was plugged in or not… but actually used much more.
Qbix has decided that it will submit a new version of its app to the Mac App Store, which doesn’t include the third-party cryptomining code, and has said it had decided to “get out of the mining business.”
A good decision by them, I think. But meanwhile Apple probably needs to wake itself up to the growing interest in cryptomining within apps, and decide what it wants to do about it. At the time of writing Apple has declined to comment on whether Qbix broke any rules.
You can hear more about this incident on an edition of the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Hello, hello, and welcome to another episode of Smashing Security, episode number soixante-neuf. My name is Graham Cluley.
And I really would like an independent organization like yourself to take a look at them and give us your feedback. Are they fair? That kind of thing. How does that sound to you?
So he seems bigoted against bigotry, but I don't know what bigotry he's referring to.
So it might have been a few people. I mean, it's possible. I mean, a few episodes ago, you spoke about gun control. It can't have been that though.
I mean, everyone's sort of sensible about that, aren't they?
I mean, from what it sounds like, all you've been doing is venting strong opinions. Surely that's what podcasts are for.
If you listen to a podcast and then you're shocked that there's strong opinions on it, then maybe you should be listening to something different.
Again, it seems to be United States. His username is Not a Bonehead Like You. I don't mean you, John. I think that's just sort of generic you. Subject title: Worst Podcast in History.
Wow.
I think it's it as in it rather than IT, because it's not capitalised.
There's probably a board scheme that's giving that out that he's using.
For instance, John, no pressure, but people will be judging you on your performance today. Get into detail.
Maybe give us a timestamp of what in particular upset you, and then we can fix it in the future.
LastPass Enterprise simplifies password management for companies of every size with the right tools to secure your business with centralized control of employee passwords and applications.
But LastPass isn't just for enterprises. It's an equally great solution for business teams, families, and single users.
Go to smashingsecurity.com/lastpass smashingsecurity.com/lastpass to see why LastPass is the trusted enterprise password manager of over 33,000 businesses.
But, you know, there are advantages to subscription models. Obviously things can be kept up to date, vulnerabilities are addressed very quickly.
You know, you can pay a monthly fee to get the new features as they're developed and you don't have to pay a huge amount if a major new version comes out.
And of course it helps support developers as well. It means, rather than you just having paid them in 2005, they're continuing to get support from you.
So I actually think it's reasonable to do as long as the fee isn't too big.
Not everyone loves them though, which is understandable because people are so used now to 99 cents apps on your phone.
And that's why a developer called Cubix has made a change in its calendar app, a rather popular Mac calendar app imaginatively called Calendar 2.
You know, a bit like, I don't know, Back to the Future 2 or something like that. And it recently shipped a new version of software with a new feature.
Rather than paying a flat fee of $17.99 or your 99 cents per month subscription to gain access to all of the app's advanced features, you can all get those advanced features for free.
Yes, for free. Hooray!
And what it does is it says, look, if you want all of our advanced features for free rather than paying up, you can choose this, which is to unobtrusively generate cryptocurrency in the background.
And it's one of the ways in which Apple has managed to keep malicious attackers off iPhones and iPads. And mostly it's worked really well.
Basically developers have to jump through lots of hoops to get their smartphones vetted and out there for the audience.
It's really super because it automatically updates. It's one-click install. It's easy. It's one place.
And the idea is that Apple has vetted it and it will lead you to believe that it is safer as a result.
You know, what is their official policy on that? Are they — if that's all right with them, then it'd be good to know that, right? Or did Apple miss this app?
Because in this particular case, it tells you it's going to do it. It gives you the option to say no, thank you. But according to some of the users, it did it anyway.
There is a guy called Fred Laxton who installed the app and insists he did not choose to do the crypto mining, to opt into that.
The app has been pulled from the App Store, but not before security researcher Patrick Wardle managed to grab a screenshot of some of the bad reviews it was getting in the App Store.
So JFM25090 said, I was pleased with this app till it started doing weird things. Kept on popping up alerts over and over again. I kept on hitting ignore report.
It just kept on popping up. And an app should not be allowed to make a sudden change to your settings and turn into crypto money machines.
I immediately reviewed it and came to write a review and I never write reviews.
Because this kind of behavior is not something that you see very often in the Apple Store apps.
I don't know how this app passed Apple's quality inspection. So not ideal by any means.
'Cause it seems to me like a pretty reasonable way of making money out of software.
If you're trying to defeat this horrible thing we've got into where everybody wants everything to be free, you know, there's a lot of worse choices you could make.
You know, you could be bundling all kinds of crapware with your software that you're trying to monetize.
You could be hijacking people's search settings to point them to somewhere else to make a few pennies. But this one seems reasonable.
I'm presuming they have a policy of saying, well, you can do this if you're upfront about it.
How come they didn't spot that it actually did it even when people thought they hadn't enabled that feature? 'Cause it does appear there's a bug.
The developer Cubix has blamed the problem on a perfect storm of bugs that didn't work as planned.
You know, there are some apps which do use a huge amount of resources perfectly legitimately.
Like you, John, I think maybe crypto mining is okay if it's public and if it's definitely agreed to. The problem is that there were bugs.
Qubix told Ars Technica it's supposed to have only used between 10% and 20% of a Mac's computing power, depending on whether it was plugged in or not.
But it actually used much larger amounts and they were using third-party crypto mining code, which they hadn't viewed. They didn't know about service chains.
And so they didn't really have visibility on exactly how it was going to work. And it seems that it was doing too much. So they've ripped out the app for now.
They're going to put out a new version, which doesn't include it, but I suppose our message to Mac users and other computer users out there about their apps is take heed and developers, make sure you don't ship buggy crypto mining code.
Apple are saying, God, I don't know how we missed it. Our big question is Apple, are you gonna be allowing this in your apps or not?
It's unclear what its rules are regarding this and it allowed this app to go through, which has upset its users. Okay, okay, calm down.
Well, only because the press and others, you know, caused it because— all right, look, hey, Carole, if this app has got many thousands of users, right, what would happen if it was an app which was being used by millions and millions of people?
If this kind of thing can leak through, what other malicious activity could potentially leak through? That's what we need to worry about. You're just a bleeding heart, aren't you?
So for those who aren't down with the terminology, air gapping is a pretty common thing in keeping computers secure.
It's basically a step up from firewalling if you want to keep your machine safe, but you need it to be connected to the internet, you use a firewall.
If you want it to be really safe and you're not too worried about it being connected to the internet, then you have it air-gapped, which basically means unplugged.
It's not connected to any network.
It's something you use when you, if you have like a production room where you're making your software and you make sure that only stuff that you absolutely trust goes into that room, you would maybe burn it to a CD and you scan the CD before you put it in any of the machines in the air-gapped room.
And obviously in TV and movie shows, you often see that the bad guys will send a USB to the cops and the cops will plug it into their computer to see the secret files that have been stolen.
And then they say, oh no, we've infected the entire FBI network. And then obviously in real life, they would do that on an air-gapped machine.
They would just take it to a safe machine that wasn't connected to their network and have a look at whatever mysterious stuff they had to be sure it was safe.
And Jean Reno is up there with the rope, isn't he? And he's beginning to sweat and all the rest of it. And he sees a rat. Oh, I hate rats, he goes.
And Thom Cruise swoops down and all— it's terribly exciting.
They've been working on this stuff for quite a while now. So early attacks against air gaps, at least 5 years old.
So you could make noises on the air gap side, and then you could detect those noises on the other side and you could use those to send signals between two computers.
So making the machine warm up and cool down at predictable rates so that the pattern can be converted into a signature.
So this is using ultrasonic so people can't hear it, which is important because obviously if your highly secure machine suddenly starts making weird noises, you'd be a little concerned.
But it also doesn't require a microphone.
So what they've done is basically they've taken speakers and using the computer that those speakers are connected to, reversed the way they work.
So rather than turning electronic signal into sound vibrations, they're taking sound vibrations and turning it back into electronic signal to go into the computer.
They've got a cute little video on YouTube with a— they've set up these two computers and they've sent an image of a little panda from one machine to the other, just using the sound coming from the two machines.
Actually, the main thing about this is that it's two-way.
So you have on either side, you're jumping the air gap using these two sets of speakers to communicate between the two machines. Now, there are some problems with this, obviously.
You need to actually be in control of the machine on the air gap network in the first place. So you still need Thom Cruise to abseil down with his USB and stick it in.
Which makes it kind of pointless. But obviously it's not, if you want to grab something off the machine, you can just do it at that point.
But if you want something more long-term, then you can get in, get the infection in place and have it sit there and send messages backwards and forwards.
My idea, it's ultrasonics, right? Get a chihuahua. Every office needs a chihuahua.
Say, oh, I've just spotted a panda has been sent or something like that.
Aside from the fact that China suffers from a lot of polluted waters, ground, and air, it might be spurred on by speculations that they want to be world leader in the electrical car business, which is booming.
Specifically, China's already stronghold on what its 1.4 billion citizens can access and say does seem to be tightening, both in real life and online.
So let me introduce you guys to the concept of a citizen score, and I wonder what you guys are going to make of it, whether you think something similar might ever happen in less overtly controlled places like Europe or America.
So back in 2014, the State Council of China published a document outlining the construction of a social credit system.
According to Wired, the principal question asked in the doc is this: what if there was a national trust score that rated the kind of citizen you were?
Now, 4 years on, this document is much more than a pipe dream. China's social credit system, quote unquote, is looking to launch in a few years' time, in 2020.
So the gist seems to be this: how you behave on popular social media sites—so what you say, show, and share—will contribute to your social credit score.
In other words, can China authorities monitor so much behavior that they can accurately assign a holistic value to a specific individual?
Not so complimentary this.
And sites like Google, Facebook, YouTube, Twitter, these are all really strongly controlled in China. But they have an alternative, the replacement social site called WeChat.
And WeChat is seriously popular. We're talking 902 million daily users, and about 38 billion messages are sent on the platform every day. This is according to The Verge.
So on WeChat, you play games, you book meetings, you make video calls, you pay bills, you access bank accounts, you find out local hangouts, you book doctor appointments, you file police reports, you hail cabs.
You're hearing me, right? You do everything through this site.
And more interestingly, WeChat will soon issue virtual ID cards, which individuals will use in lieu of their physical state-issued ID card.
So this kind of suggests to me that maybe people don't have a lot of choice about using WeChat.
Hey, would they let us have that missing G in our name, which Twitter won't let us have?
Probably not allowed. 0 out of 100.
Now, there are not a lot of details on how this is going to work exactly, but since there's so much information being put on these sites, I think it's fair for us to speculate maybe, right?
So let me give you a few scenarios. So if you were online on a social site, told someone to fuck off, would that mean that you'd lose points? Would that be considered socially rude?
What if you hearted a picture of a political leader?
I don't even know if you would know what your score is. Do you get to watch the score?
But tie this announcement with this news that came out today at a border near Beijing.
Chinese authorities are currently testing out the use of smart glasses to identify through facial recognition who's naughty and who's nice.
So these are AI-powered glasses made by LLVision, and they pick up facial features and car registration plates and then match them in real time with databases of suspects, right?
If you want a picture of the future, imagine a boot stamping on your human face forever.
A lot of sites have that already. So you can see the reviewers and it says whether they're a regular or they're a newbie or things like that.
And it's basically just an extension of that.
There were obviously quite a few, Google, especially Google, Facebook, big foreign services tend to be blocked on local systems.
But as a foreigner, I had a phone so I could just use my 3G connection to go anywhere I wanted.
That's obviously something that most internet-savvy people are doing to try and bypass all these blocks that are put up to sites like Google, Facebook, etc.
China is actively, however, cracking down on the use of VPNs.
And according to the BBC, Beijing ordered its state-owned ISPs, which you were probably connected to— China Mobile, China Unicom, and China Telecom— to block access to unauthorized VPNs.
And you just can't help but wonder if there's lots more VPNs coming on the market only to try to make sure that they're not listed on the list of VPNs that might be blocked.
The government's also even demanded that shopping websites like Alibaba remove references to VPNs on their site. So basically, don't sell them, don't talk about it, hush hush.
No, I'm not saying— what I am saying though is if they begin scoring people based on their social media activity and whether they've said something which might be considered anti-government, for instance, it might be tempting to install some kind of little bot or something which does automatically like or heart or retweet or re-WeChat or whatever the phrase is, people in power inside the Chinese authorities and show that you're a model citizen and then just occasionally pepper what you really think.
LastPass simplifies password management for companies of every size, but it isn't just for enterprises. It's equally a great solution for business teams, families, and single users.
Learn more at smashingsecurity.com/lastpass.
It could be a funny story, a book they've read, a TV show, a movie, a record, an app, a website, a podcast, whatever. Doesn't have to be security-related necessarily. Shouldn't be.
And my pick of the week this week is, have either of you mastered the Rubik's Cube? John, you seem like the sort of person who would have whiled away your—
Because there are a couple of dudes, Ben Katz and Jared DiCarlo, and they have built a robot that can solve a mixed-up, messed-up Rubik's Cube in world record time, smashing the previous record.
They can make it 0.25 seconds.
And they got a couple of webcams to view the cube from different angles.
They really explain exactly what they're doing in that 30 seconds.
And you're wondering why, how I know that, right?
I'm going to the site.
So finances of the big tech firms and users of different social media sites and all kind of matched against each other and put into perspective.
There's a great one Carole, you're gonna love this one. I think this was in the last few days, I think.
Apparently you have a 56% chance of a deciduous tree compared to 53% chance of a conifer tree.
I think you'll enjoy the little painting we're going to do, and I hope you take the time to paint along, or you pull up your easy chair and just relax with us.
I thought today we'd just—
Well, it's watching Bob Ross videos and working out what kind of trees he's just drawn.
And the other thing that I wanted to mention this week, because this is what made me think of it this week, they recently put out a thing called their Digital Economy Compass 2018.
Which is basically a bunch of their standard infographics put together in a kind of massive— I think it's 220 pages or something.
Just hundreds of little graphs and charts all about the digital economy. It's fascinating.
So he basically put the video on a YouTube channel and set it as private and then was going to show the group.
And he was asked to access the channel from the computer connected to the display or the presentation screen. You with me?
And while he's doing all this, we are looking at his Up Next section of his YouTube channel with recommendations of videos on display.
And many of these were what we would call NSFW, if you know what I mean. And I kind of felt for the guy, right?
So anyway, fast forward to a few days ago, I'm scanning Reddit's No Stupid Questions sub and see this question from handle Absar.
Is there a way to stop certain video suggestions on YouTube?
I watched 3 flat earth videos so I could have a good laugh, and now 90% of the recommended videos are from flat tarts, quote unquote.
So let me summarize the advice for you. First, on YouTube, go to history, delete any recent videos that you don't want recommended to you in the future.
Start with big hitters like over a million views because they really skew your recommendations. Yeah, I didn't know that either.
Second, in your Up Next section, if you see the videos that are lined up in your Up Next sessions, right beside them you can see a column of three dots right next to your recommendations.
If you click on that, choose Not Interested from that list and select Tell Us Why and tell them I don't want recommendations based on this video.
Third, consider watching videos with over a million views in some form of private browser because they have such an impact on recommendations they provide you.
If you'd rather watch a video that has lots of views that you don't want to recommend to you in future, do it in a private browsing session.
And four, only like videos that you're actually interested, which seems pretty easy, right? That's a duh option, but I'm sure lots of people don't think that way.
So if you do like a video, say yes, give me more of this please. All right, and there you go. So thank you very much, Trilicon.
And now many, many presenters around the world who have to open up YouTube on a display can clean up. I mean, the best way to do it is have two accounts.
I'd say have a business account, a personal account. That's the way I'd handle it personally. But there you go. Cool.
We are on Facebook in the Smashing Security podcast group. We've got a store, smashingsecurity.com/store.
And oh, the other thing I need to do is, John, thank you very much for joining us on the show today.
If people want to know more about you and AMTSO, how should they get in touch with you?
It really does help new listeners discover the show, and you can check out past episodes at smashingsecurity.com.