The developers of the notorious Carbanak banking trojan have added a new JavaScript backdoor to their tool set.
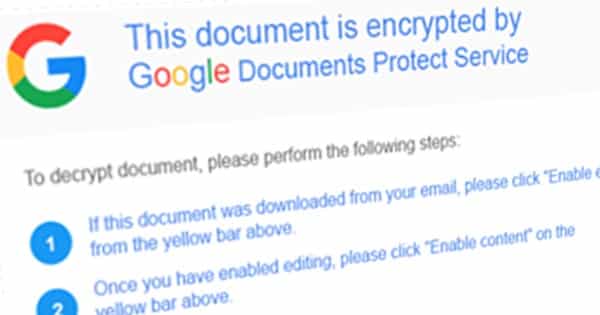
The new threat, dubbed “Bateleur”, appears to be targeting chain restaurants based in the United States. It arrives via malicious spam sent from either an Outlook.com or Gmail account that purports to contain a previously discussed check as its attachment. That document claims to be encrypted by “Outlook.com Protect Service” or “Google Protect Service”.
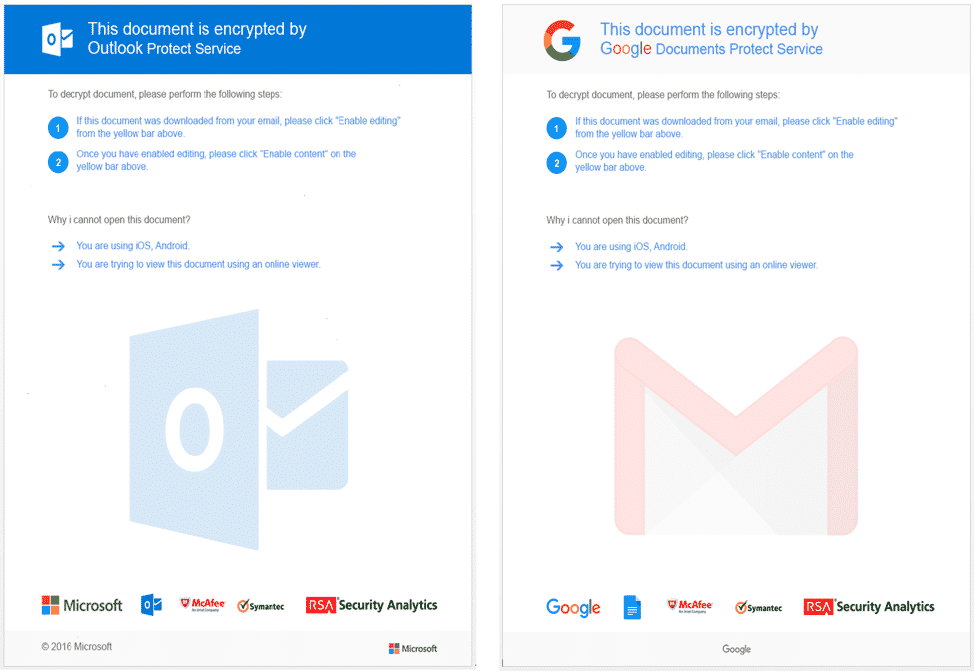
In reality, it contains malicious macros that access the delimited obfuscated JavaScript payload from the caption “UserForm1.Label1.Caption”. The macros then save the JScript content as “debug.txt” to the user’s temporary folder before executing a series of commands.
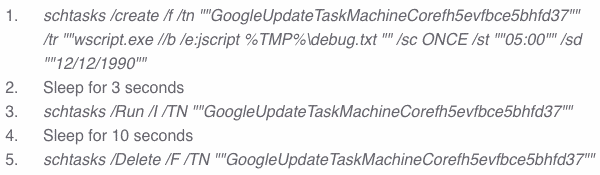
Proofpoint’s Matthew Mesa and Darien Huss detail what this sequence of events produces:
“The macro creates a scheduled task whose purpose is to execute debug.txt as a JavaScript. The macro then sleeps for 3 seconds, after which it runs the scheduled task. Finally, the macro sleeps for 10 seconds then deletes the malicious scheduled task. The combined effect of these commands is to run Bateleur on the infected system in a roundabout manner in an attempt to evade detection.
After achieving persistence by creating a scheduled task, Bateleur can access information about the infected machine, take screenshots, steal passwords, and load EXEs and DLLs. In order to evade detection, it can even detect Virtualbox, VMware, and others as well as check its script and compare it to a deny-list including terms such as “malware” and “Desktop.”
At this point, Proofpoint’s researchers think Bateleur originates from Carbanak/FIN7, the same APT responsible for Odinaff and other malware. They base their attribution on some key pieces of evidence, like similar email messages used to deliver both Bateleur and another backdoor called “GGLDR” as well as both campaigns’ use of a Meterpreter downloader script called “Tinymet”.

Notwithstanding its expanding toolset, Carbanak relies on well-known attack vectors to deliver Bateleur, GGLDR, and other threats.
Organizations should therefore take this opportunity to begin educating their employees about phishing emails if they don’t already do so. They should also consider investing in email security solutions as additional layers of protection against social engineering attacks.


