UPDATED 10/13/16 to state Odinaff has been in circulation since early-2016, not 2006.
A trojan is taking a number of cues from the notorious Carbanak malware to target financial organizations and users of the SWIFT banking network.
The malware, known as Odinaff, makes contact with its victims a number of ways.
Sometimes Odinaff is distributed via password-protected RAR archive files.
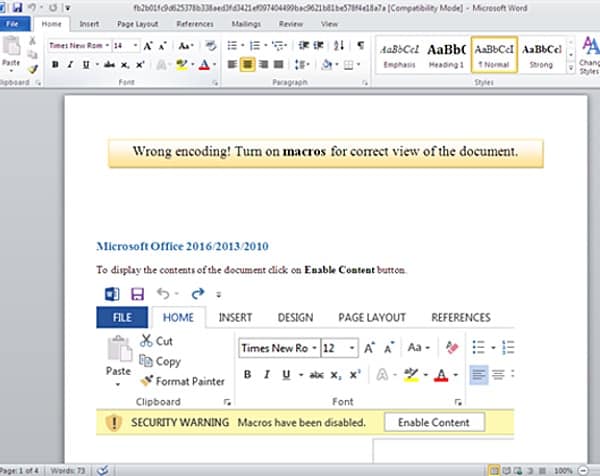
Sometimes it is spread through Word documents containing malicious macros, which I would hope you would have gone ahead and disabled by now.
Then there are other times where Odinaff uses neither method, as Symantec explains:
“Trojan.Odinaff has also been seen to be distributed through botnets, where the Trojan is pushed out to computers already infected with other malware, such as Andromeda (Downloader.Dromedan) and Snifula (Trojan.Snifula). In the case of Andromeda, this was bundled as a Trojanized installer for AmmyyAdmin, a legitimate remote administration tool. The Trojanized installer was downloaded from the official website, which has been targeted repeatedly in recent times to spread a number of different malware families.”
Upon successful installation, Odinaff leverages a cocktail of lightweight hacking tools like Mimikatz and legitimate utilities like PowerShell to traverse networks and identify important computers. From there, it calls upon other malware to complete its dirty work.
Since January 2016, the malware has targeted the United States above any other country.

Most of those campaigns have attacked financial organizations.

 That might explain why Symantec has found evidence Odinaff has targeted users of SWIFT, a global banking network which attackers abused to steal tens of millions of dollars from the Bangladesh Bank, a bank in Ukraine, and other financial institutions.
That might explain why Symantec has found evidence Odinaff has targeted users of SWIFT, a global banking network which attackers abused to steal tens of millions of dollars from the Bangladesh Bank, a bank in Ukraine, and other financial institutions.
It might also shed light on why Odinaff is in some ways connected to Carbanak, a notorious banking malware which cost banks hundreds of millions of dollars in February 2015.
Specifically, Odinaff uses three command and control (C&C) IP addresses that Carbanak has employed in some of its campaigns, and it pushes out Batle, a memory-based malware frequently leveraged by Carbanak that enables attack campaigns to maintain a low profile.
In light of what Odinaff’s packing, Symantec says malware authors aren’t messing around when it comes to targeting financial organizations:
“The discovery of Odinaff indicates that banks are at a growing risk of attack. Over the past number of years, cybercriminals have begun to display a deep understanding of the internal financial systems used by banks. They have learned that banks employ a diverse range of systems and have invested time in finding out how they work and how employees operate them. When coupled with the high level of technical expertise available to some groups, these groups now pose a significant threat to any organization they target.”
That’s why companies and users alike should disable macros by default, avoid clicking on suspicious links and email attachments, and maintain an up-to-date anti-virus solution on their computers.