Hacked roadside billboards are in the news again, so it felt like a good time to take a look back on some of the more notable incidents that have caught the media’s attention in the past…
January 2009
No, you don’t have to worry about a botnet bombarding you. It’s zombies in Austin, Texas, you have to watch out for.

“ZOMBIES AHEAD”
May 2012
Practical jokers meddled with a a road sign to warn drivers of an invasion from Skaro’s much-feared tin pepperpots:
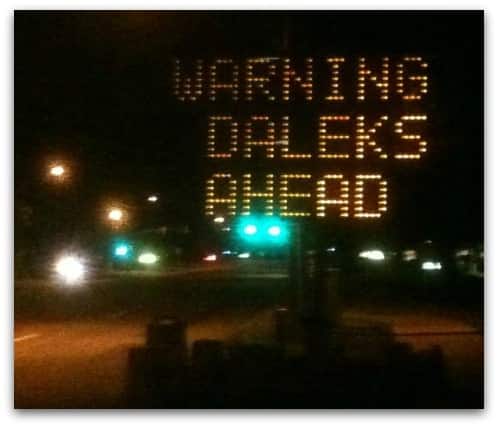
“WARNING DALEKS AHEAD”
January 2015
It’s a new year, but mischief-makers have quickly forgotten their resolution not to f**k around with road signs.
Need a New Year resolution, maybe? "Read a f'n book" says #DTLA electronic street sign pic.twitter.com/3iJhOsDg3X
— Daina Beth Solomon (@dainabethcita) January 9, 2015
At least they’re encouraging literacy…
May 2015
Hackers remotely attacked an electronic billboard display to show the obscene Goatse image (Don’t Google it. If you don’t know what Goatse is, consider yourself lucky. You’ve been warned.) to motorists and passers-by in the affluent uptown Buckhead district of Atlanta.

August 2017
Naughty Welsh hackers meddled with a billboard on Cardiff’s main shopping street, to display swastikas, far-right images, and Big Brother.

As Carole Theriault discussed on an episode of the “Smashing Security” podcast, the hackers seized control of the digital advertising display after stealing its TeamViewer login credentials and locking out its genuine operator.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
In the first few minutes of the podcast, Maria, who's our special guest, her audio is slightly defective. Please bear with it. We had some technical problems.
We even had a power cut during the course of the recording. Her bad audio only lasts maybe 3 or 4 minutes, and after that, everything should be good.
And we still think it's worth putting out. So bear with it and enjoy the show.
Sign up for the free daily threat intelligence update at recordedfuture.com/intel. That's recordedfuture.com/intel.
Hello, Carole, how are you?
Welcome to the show.
Thank you for joining, because I know you have recently had a baby, so you're not getting a lot of sleep these days, are you?
Happened the day I was in the hospital. It was amazing. So, oh wow, the nurses were going, I think something happened and I'm gonna have to change all my passwords again.
And they're wheeling in my baby in the bassinet and I'm going, oh my God, I can't get away from this anywhere.
And I agree with Carole, we need more women on this show. In fact, we've had shamefully few. Well, obviously there's been you, Carole.
My story this week is, well, let me start off by saying this. What do you think is a security researcher's biggest nightmare? What do you think would really terrify them?
But Carole, you have put your finger on it.
Because a senior threat analyst at Mandiant, which is of course a division of security firm FireEye, was hacked in what appears to have been a revenge attack.
Now, I'm not gonna name him because he's probably embarrassed enough as it is and is worried that his future career prospects are scorched.
But he was targeted by hackers as part of a campaign which they're calling #leaktheanalyst. And a bunch of hackers who call themselves Hey Maria, you're a bit geeky.
You'll be able to handle this. 31337.
Anyway, they took information from this Israeli researcher And they made it available for anyone to download from the net.
It's still available to download, including his email archive, megabytes and megabytes of that, passwords, contacts database, details of private communications with potential recruiters.
Slightly awkward, isn't it? Cloud drives, his calendar.
And if you were the hacker who was being analyzed by this analyst, that may be useful.
Furthermore, you may be able to find communications as they claim to have done about some of their clients and the situations that they found themselves in.
They even managed to track the poor guy's location because his, I said poor guy, he really was, because he had a Microsoft Surface and it was being geotracked.
And so they were able to pinpoint where in Israel he was from day to day.
And to add insult to injury, the hackers even defaced their victim's LinkedIn page, replacing his picture with a photograph of a hairy bottom.
What they wrote was, asshole fucked up analyst at fucked up Mandiant.
And so the bad guys, they posted up on Pastebin and they provided a link where you could download all of this data, which they'd grabbed in the screenshots and the evidence that the accounts had been compromised.
And they posted their little manifesto. And they said, for a long time, we, the— get ready, Maria— 31337 hackers—
In the #leaktheanalyst operation, we say, fuck the consequence. Let's track them on Facebook, LinkedIn, Twitter, etc.
If during your stealth operation you pwned an analyst, target him and leak his personal and professional data.
But there were certain—
If they want to cause embarrassment, if they want to give this guy some pain and get him in trouble, you probably would have done that as well, wouldn't you?
Certainly from the geo data where they were tracking his lovely old Microsoft Surface, it does appear that that may go back some time.
I don't know if that's an archive which is available to anyone, you know, whenever they log in, but it does appear that there was some old information in there.
The obvious danger is, has client data been compromised? FireEye have issued a statement.
They've told Gizmodo, "We're aware of the report." So they basically confirmed that the hack has happened.
"We're investigating, we've taken steps to limit exposure, but there's currently no evidence that any corporate systems at the company have been compromised." They say, "Customer data, keeping that secure is a top priority.
And to date, they've only confirmed the exposure of business documents related to two separate customers in Israel." One imagines one of those is the IDF.
And they've addressed the situation with those customers directly. That's an awkward phone call to make, isn't it? Oh yeah, we might have doxxed—
I think none of us can imagine that just because of our jobs or our roles or the fact that we're working in security 24/7, that somehow we couldn't be targeted.
The truth is that everyone makes mistakes.
I remember years and years ago, I was working at a security company and they were holding an antivirus conference and experts from all around the world were bringing in their presentation from rival firms.
And one of these guys gave me a floppy disk there, that's dated me.
And he said, "Here's my presentation." I said, "Thank you very much." I shoved it in my computer 'cause it was my job to collate everyone's presentation.
And the antivirus on my computer went zoop, zoop, zoop because it contained a virus on the floppy disk.
And the truth is that he'd been using exactly the same computer to analyze viruses as he'd been using to write his presentation. And, you know, so people make mistakes.
And it does appear that this particular guy may have been reusing passwords.
It's possible that his password leaked out from the old LinkedIn data breach, but also that he had a formula for passwords.
You know how sometimes people think, well, you know, I will have different passwords, but what I'll have is I'll have a sort of base word, a base password, and then I'll add on the first two letters of the domain or something like that.
That's what the video is.
As you were saying, with all the passwords we need nowadays, there's no way you can make that even sane. So yes, please.
You don't have to use a cloud-based password manager though. You can use a local one.
Some of the passwords have the word fire in them. You think, seriously, guy, you know, are you doing this?
But hey, all security researchers out there, make sure that you're practicing what you preach.
And I think that's, you know, that's a fairly likely probability you won't be targeted if you're just— but, you know, in this industry and with this LeakTheAnalyst operation, I wonder what your advice would be, Graham, for other analysts out there?
Are you saying literally just make sure your passwords are good and strong and unique?
All the variety— we'll link to a past podcast in the show notes. Oh my word, we've got a lot of show links today, haven't we?
But we'll put some of those things in where you can learn some of the techniques which you can use to harden the security, to better protect yourself from these kind of attacks.
Ultimately, I'm afraid it's your brain, isn't it?
It's your mouse finger which might be clicking or making a mistake, or it's your decision as to whether you are going to choose a strong password or a weak one.
And I think some people think, oh, because I'm a bit nerdy, somehow I don't have to worry so much as my auntie Jean.
I mean, not to be completely tinfoil hatty, but you know, it's having worked at security companies before, you know, even the marketing intern can be a target.
And you know, definitely people who are high visibility targets like an analyst know that they really need to practice what they preach. But that goes all the way down, doesn't it?
So as many of us have heard, and no doubt many of our listeners would know, Flash is finally going to kick the bucket.
Adobe announced in 2020, since supposedly is expiration date for the much maligned plugin and video player and interactive thingamajigger.
However, I mean, what else do you want to call Flash? Attack vector. There is an ongoing effort from at least one web developer on GitHub to keep Flash alive. Why?
And that is the reaction of many people around the internet.
Don't know how, but that's the beauty of open source. You never know what will come up after you go open source. Hooray. All right.
So the reaction of much of the security community is paraphrased beautifully by Carole's reaction. Please just let Flash die already. It is due to die in 2020.
That's not nearly soon enough, but let's make this happen.
And just in case people want some stats from a lovely Gizmodo article quoting, I believe, our sponsor Recorded Future, they ranked Adobe Flash Player as the most frequently exploited product in 2015, comprising 8 of the top 10 vulns leveraged by exploit kits and noted the existence of over 100 exploit kits and known vulns.
So yeah, it's a problem.
I worked with a lot of the guys on Metasploit, which is a very wonderful open source project.
And I've seen firsthand how wonderful the open source community is and what amazing things they can do. But open source is of course a double-edged sword.
You open up that source code to the world and there's a real possibility that a lot of people are not going to be working out of the goodness of their heart to fix Flash.
And they're just going to go to town and find all sorts of problems that they couldn't find before.
So we're going to have an even more vulnerable Flash, if that is even a thing that you can imagine. It is quite a target.
I think that does make some sense that people should be able to research this information and see how it was working.
And so all the hackers and the bad guys, the malicious hackers, can spend lots of time and continue spending lots of time exploiting Flash, but the rest of us agree not to ever use it.
Because the danger of closing down Flash is that the bad guys will then put all of their attentions on exploiting something we are using.
But if we just keep it there and they don't hear that we're not actually using it, yeah, because they're all idiots.
However, as the petition says, you never know what could come up after you go open source, exclamation point. And I mean, okay, fair enough.
It could become more secure with more eyeballs on it.
In theory, that is possible, but you know, open source projects are not always necessarily known for continuing after a certain point, you know, having a lot of support.
People tend to drop them. And I don't know how interesting this is as a problem for a lot of people.
I mean, Flash has been around for forever, but that said, what do we do when Flash goes away? What do you do with all those Homestar Runner videos?
And it's not just videos, I should say. It's really the interactive content, the stuff you click on, because videos are not really the problem. It's the interactive stuff.
And there are a lot of people who've attempted to solve this problem, basically making interactive videos from early 2000s workable.
But since the Flash backend is closed, you can't really do much with it. So there really hasn't been a good solution and there's really no viable alternative right now.
So that is actually a legitimate issue if there's stuff that you want to still use once Flash goes away.
That's completely zapped because that's obviously the most common attack vector, but maybe there could be an open source desktop player instead.
And so if you had something which you really wanted to run to check it out, you still could, but the exposure is greatly reduced.
And you know, and that way we don't lose all that ephemera from the early 2000s, really.
There's a few bad apples out there, but I think, you know, you don't know what'll come up and it could be amazing. They could actually make it much, much more secure and usable.
However, I mean, as I said, I kind of go back and forth on this one because I can see their point of view.
But one thing I'm thinking is that what's going to happen if we open source Flash is we're going to have kind of a shambling zombie form of Flash after 2020.
And people are going to go, well, okay, so Flash isn't officially supported anymore, but there's an open source version.
So I'm not going to actually get rid of it on my website because technically there's a viable option. When really we need to be telling people, stop using it.
For the love of God, why are you still doing this?
But the exposure is reduced in the browser, which is the primary attack vector.
I don't think anyone's really fighting for that. I mean, maybe they are, but I certainly am not. That certainly won't mitigate the issue.
Because that was probably what's causing the big delay in them being wiped out.
So that has done a lot for killing Flash more than anything else. I doubt that those are Flash-based.
I'm sure there are in some corners of the world, but I imagine many of them have moved to HTML5 or other options.
I mean, do we still see the mortgage ads with the dancing person where you punch the number? I mean, that sounds like 10 years ago.
But I mean, there are other problems with ads that we could probably do 50 shows on that alone.
So today, Wednesday, the day of recording, we've seen reports of a giant billboard in Wales' capital, Cardiff, its main shopping street. It's been hacked.
So the billboard seems to have been accessed by a hacker via remote control, and then they took control of the screen to display rather shocking images to the shoppers of Cardiff.
There's not a lot of info right now that's just come out at the time of recording, but a message posted by an anonymous user on the community site 4chan— okay, I'm putting little marks around community site 4chan.
Earlier today I was walking to work and looked up at a giant 300-foot TV screen on the side of the building. That's what he says. 300 feet. I think—
I noticed that TeamViewer was running in the background and I took a photo of the username and password. I just tried remote controlling it and it worked!
What should I use this for considering that it's probably unattended all night long?
I think last May, Liverpool One shopping center has a screen, it got hacked, and it was hacked with a rather helpful message saying, "We suggest you improve your Smashing Security.
Sincerely, your friendly neighborhood hackers."
And in March, Mexico City digital board located near one of the busy roads showed porn for a few minutes. And probably the worst one was the 2015 Atlanta billboard.
Remember, it was in a really swanky neighborhood in Atlanta, and it displayed goatse.
Now TeamViewer, for those who don't know, is a tool that allows people to remotely access computers and desktops and allows for file sharing and all these things.
And they're used to, in some cases, to display messages on, you know, people use them when they're doing presentations to share screens.
But people also use them for these big digital screens.
So TeamViewer, many of us in the industry would say, it's been designed to be easy to use, not necessarily very strongly secure.
And there is a great article that I found from, and it was published last year, but it was published from How to Geek.
And it has loads and loads of little tips on how you can make your TeamViewer instance much more secure.
Now, a few big ones that we can share is make sure you exit TeamViewer when it's not in use. Don't just leave it hanging around, you know, turned on but silent.
Use obviously strong passwords, and there is gonna be a link in the show notes for how to do that, right, Graham? Sure thing.
Turn on two-factor authentication for TeamViewer, and I was just talking to my other half, and he didn't even know that two-factor authentication existed for TeamViewer.
That may be something that's less known.
But just as a little reminder, let's do that because we're going to be relying on digital screens much more. I mean, I think the end of the poster is near, right?
Yeah, I mean, do you know how to hack those? You literally just walk up to them and open the panel in the back with a flathead screwdriver, and there you go. That's how you get out.
Maybe there should be a way for TeamViewer to self-time out on some sort of application like this.
So yeah, I mean, I'm not saying TeamViewer is responsible for all these things, but these remote access tools need to be properly configured in order to try and stem the flow of attacks like this because they seem to be growing.
You know, it's quite fun for a young hacker to be able to hack something that's so, you know.
They look on the web, they look on the dark web, they peruse the internet in its darkest corners, and they work out what are the new emerging threats and vulnerabilities from the world of hacking and cybersecurity.
And then they bundle it all up, they wrap it up in a beautiful ribbon and send it to you in a free email.
And thanks to Recorded Future for supporting the show. Smashing, and welcome back to the show. And in this segment, we are going to choose our picks of the week.
Yes, our pick of the week could be a funny story, a book we've read, a TV show, movie, record, an app.
And their latest episode, which we'll link to in the show notes, is all about tech support scammers.
Now, when I saw it was about tech support scammers, I thought, okay, they're going to do the usual thing where a scammer calls them up and they keep them on the phone for ages and it gets more and more ridiculous.
But no, they've been rather more inventive than that. It's almost brilliant. It's a great episode.
You know, it's like they're calling up regularly for chats and—
And it ends on something of a cliffhanger, which will make you want to tune in, I think, to the next episode, which hasn't been released at the time of recording, but I'm looking forward to it to find out what happens next.
But I would recommend it.
Because I heard you guys talking about the Red Pill documentary a few weeks ago, and I'm just, Graham loved that one.
But the documentary called Tickled, which is all about, quote, competitive endurance tickling, is, as the tagline says, not what you think.
And Carole and Graham, you both have seen it, I believe, so you can back me up on this.
And I forced them to watch it that night just because I thought it was that good.
And it's kind of dark and sad, and there's really no conclusion to the main documentary, which is a little frustrating because you're, you're dark and sad maybe, but also I sort of, you know, curl up on a Friday night with a bowl of popcorn.
Basically, when they started airing the Tickle documentary at film festivals, a lot of the guys in the documentary started showing up and real-life trolling these events. Yes.
And it's all this drama and it's kind of— so yeah, if the Tickle documentary is not enough for you, which it's, you know, it might not be, you know, if as fascinating as it is, go watch The Tickle King afterwards.
Back to back, it's awesome. Really fascinating. And yeah, great, great watch.
Now, the reason I wanted to use this, the reason I to bring this, I was talking about screens earlier, so this is all about screens as well.
And what they've done is they've developed a clock that is actually a kind of digital screen, but it represents a human face.
Basically, the way that that face is looking or moving its mouth is supposed to indicate what time—
So basically, say for example it was 10 to 2, you would have to have your left eye kind of facing upwards and left and your right eye facing upwards and right. Right?
And how do you do that? So they took— they have 3 different face clocks which you can choose from that are available.
And then they did movies of the faces moving their eyes in, you know, around the clock face. And then they of course mirrored two together to try and get the difference.
No, it's just, you know, sometimes just come on. However, I have to say, I would people to go look at it just to see if they actually can tell the time quickly.
So I think there's, there's a game in here, right? Just stop the video and say what time is it?
It's a bit like, you know those paintings in haunted houses where they follow you, the eyes follow you, Scooby-Doo style.
So the 1, 2, 3, 4, 5, and it kind of chugs along on a cog and it turns. And as it goes, you can tell what time it is.
That was very exciting. But we've made it to the end. Thank you so much, Maria, for joining us.
Whether it's good feedback or negative feedback, we don't care. Just 5 stars, 5 stars.
Go to www.smashingsecurity.com and you can follow us on Twitter @smashingsecurity, no G on Twitter.
September 2019
It’s not all zombies and porn, sometimes road sign hackers can comment on topical political news stories.
Oh those naughty roadsign hackers… https://t.co/FaXdGm4uOB
— Graham Cluley ???? @ (@gcluley) September 27, 2019
“IMPEACH THE BASTARD”
September 2019
And, back to porn again…
Drivers on the interstate in Auburn Hills, Michigan, were greeted by an eyebrow-raising sight: a pornographic movie featuring adult actresses Xev Bellringer and Princess Leia (with a possible bit part played by an unidentified gentleman).
I'm flattered, but keep your eyes on the road and both hands on the steering wheel! Get off at the next exit, if you must ;) https://t.co/gcfOU8q7Ik
— xev_bellringer (@xev_bellringer) September 30, 2019
Police posted video footage of two suspects breaking into a shed containing the computer which was controlling the billboard.
We discussed the whole sordid affair with the type of gravitas it rightly deserves on an episode of the “Smashing Security” podcast.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Billboard boobs, face forensics, and Alexa Ransomware Gets Way Too Personal with Carole Theriault and Graham Cluley. Hello, hello, and welcome to Smashing Security episode 148.
My name is Graham Cluley.
Now on today's show, Graham gives us an SFW look at a porn incident along an American highway.
Maria muses on the latest in the deepfake, cheapfake space, and I'll investigate whether Amazon really is finally taking our privacy concerns seriously.
All this and loads more coming up on this episode of Smashing Security.
But it was also the year when a dangerous and pernicious ad campaign appeared on roadside billboards, putting drivers in peril.
There was a famous advert of Eva Herzigova looking down at her, and it was accompanied by the words—
There he was reclining as though he was having a sandwich. I don't know where he kept his cheese and pickle, but there he was enjoying himself.
I have been looking these up in the UK and elsewhere, which means I looked it up in the UK and assumed elsewhere as well. Your advert can be banned.
But of course, ads have moved on in the last, I don't know, 25, 30 years, haven't they?
You know, the old days of spaffing some wallpaper paste up on a billboard and slapping up the advert, they've long gone by because it's now all digital ads.
And some of them are video ads as well, and video images alongside the roads, which seems to me like a crazy situation.
Anyway, so the police in Auburn Hills Michigan, began to receive phone calls from motorists because they were calling to say that an electronic billboard on the interstate was displaying a rather unorthodox video.
Now, this video was—
Anyway, now you won't be surprised to hear that this video was somewhat distracting, but what surprises me is that some of the drivers who saw this, they responded by instantly leaping into action.
And 7 Action News reporter Jen Schanz, she spoke to the driver who took that video.
I kind of seen that billboard always having, you know, the user going through the desktop and making sure the proper billboards are up.
So it's one of those digital things that's easy to get hacked.
So the newspapers and the internet sites, they got hold of these videos of the footage that had been played for about 20 minutes.
And as Motherboard reports, the porn aficionados on Reddit—
Now, I've done a little bit of research into these two. I've done some Googling.
I love that.
And she said, "It is my sincere hope that this will open a larger public discussion regarding the safety of electronic billboards." Bravo.
I think there was some concerned there could have been people messing around with their stick shifts. Anyway, the thing is that this is all, of course, quite serious.
They have got some CCTV footage of two people breaking into a shed under the billboard, hacking into the computer, putting porn onto the digital billboard.
Apparently it was a 3-foot by 3-foot shack hidden behind some shrubbery. So they went behind the bushes and uploaded the video there.
I don't know when the film came out.
Quite often, the computers running these billboards or road signs are very poorly secured. And they're poorly secured in terms of physical security as well.
They may not even be locked up.
Signs have been hacked, display messages "zombie invasion," "the Daleks are coming," "impeach the bastard," I saw over the weekend.
I'm not sure this latest porn film was big or clever either. I don't know how big or— well, I don't— Anyway, so there you go. Princess Leia.
I think just keep your eyes on the road, right? And why do we have these kind of adverts on the roadside anyway? It seems terribly, terribly distracting.
But I just remember when I brought it up, it was like, hey, this brand new thing called deepfakes, they're using it to fix Carrie Fisher's face on the latest movie posthumously.
And, you know, it's wild that this technology exists somewhere in the ether and maybe one day we'll be using it for more nefarious purposes. But that's surely a long, long way away.
And I'm laughing because I kind of can't believe it, how in such a short amount of time we went from that brand new implausibility to holy shit, it's a real, very easy thing to do and it's an actual problem already.
Nobody really cared yet. So we're already there a year and a half later. So I guess what I just wanted to talk about for this segment was an update to all of this.
So in that year and a half, we are already at the point where organizations and companies are stepping up and saying this is a huge problem for us and our platforms already.
So for one example, multiple companies and organizations formed the Deepfakes Detection Challenge. Which is actually starting this month, October 2019.
And here's their mission statement. And again, remember, this is in response to a problem that started a year and a half ago.
When new forms of misinformation emerge, we need new efforts to combat them.
New technologies deepfakes, where realistic AI-generated videos show real people doing and saying fictional things, are a huge technical challenge.
Deepfake technologies are rapidly evolving and are getting incredibly hard to detect.
Adversaries creating fake content and the platforms finding it are competing in something comparable to a high-stakes, fast-moving chess game.
No single organization can— Yeah, I thought you'd be interested. No single organization can solve this on their own. Now Graham's really into it.
That's why we are working together on an ongoing initiative. So who are these companies?
And in fact, Facebook is on its own ponying up a mere $10 million towards this project.
So I don't know if that means they're actually taking it all that seriously because that seems a drop in the bucket for Facebook.
So they just came out with this new custom dataset of faces and face swaps that they made in this project called FaceForensics++.
And they actually put it on GitHub, so you can poke around a little bit.
Google basically hired a bunch of actors and with the actors' knowing consent, they made a bunch of face swaps with these actors using four popular deepfake makers, which is Deepfakes, Face2Face, FaceSwap, and Neural Textures.
So we've got four of these makers, again, year and a half, can't believe it.
And so they did the face swapping with these actors that they paid and they swapped them onto over 1,000 videos that they easily sourced on YouTube.
And then the idea was that they just made this brand new dataset so they could help reverse engineer how deepfakes are made and smarten up their own AI so they can better detect deepfakes.
So, right, yeah.
I mean, the ethical issues aside, right, about why deepfakes are a problem — hopefully that's obvious — but when they're gonna have all these credibility issues where you're gonna have fake videos running rampant on all their platforms.
If they can't detect it, people are gonna go, I can't trust anything that's on YouTube or Facebook, so I'm logging off. Which actually might be great.
It seems maybe they thought it was gonna be a niche hobbyist thing, or maybe just relegated to the world of porn, and who cares about that?
But then we saw just a few months ago, some deepfakes that an artist made of Mark Zuckerberg announcing his plans for world domination.
And then there was another one of supposedly drunken slurring Nancy Pelosi, and that one went viral on Facebook, yeah.
And I don't know if it was Nancy Pelosi or the Zuck video that was just too much egg on their face, but.
Nancy Pelosi — I'm sure she's okay, something needs to be done. You know, Obama was hit with it, I'm sure Trump has, right?
But the problem with these consortiums is it can— it sounds good that you're creating one and you're working on this, but the proof's in the pudding.
It's what actually gets agreed and pushed out, right, as a standard that is important.
And that sometimes can take consortiums years to get, you know, to agree and to decide on the wording.
It's a lawyer's nightmare or field day, depending on what kind of lawyer you are.
These orgs are, if they're trying to get in front of this problem, they have to move extremely quickly.
And yes, I was just reading a story last night about the proliferation of child pornography and how platforms like Facebook are completely failing at taking the stuff down in a prompt way.
So I'm thinking if they can't even prioritize child abuse images, how on earth are they going to get ahead of things like deepfakes?
I mean, and it's not going to be just big names that are going to get affected.
I mean, people are talking about revenge porn videos being made, people being angry at their ex-boyfriend or girlfriend making a deepfake of them on porn videos.
It could potentially affect anyone. I'm actually honestly shocked that deepfakes haven't come up yet in the current US election, impeachment, etc., etc., a whole news cycle.
And this is funny because last year Amazon actually made zero mentions of privacy features during its 80-minute unveiling. At the same event.
Actually, I seem to remember privacy was discussed pretty seriously when Bezos was papped stepping out on the then Miss Bezos.
Anyway, according to CNET, within the first 5 minutes of Amazon's product launch event, hardware chief David Limp— Odd name.
Now, he also said, this Amazon head of hardware during this launch event, privacy, so this is quoting, privacy is absolutely foundational everything we do in and around Alexa.
From now on, I'm going to call it Al, right, just because otherwise the beeping is going to get annoying in the piece.
Okay, so there's a new auto-delete feature letting the users of Al's voice recordings, letting them delete voice recordings on a rolling 3-month or 18-month basis.
Now Recode reports that Amazon will not give you the option to automatically delete your voice data.
Amazon also announced that users can now ask the speaker, "blah blah, tell me what you heard," or "Al, why did you do that?" And these queries are meant to increase transparency.
I can't help but wonder though, some of the answers must be just like, "because," or "don't worry your pretty little head about it," or something to that effect, because what are they going to explain the ins and outs of every reason?
And Apple, you might remember when we talked about a few weeks ago, actually have done it the other way around, so turning it off by default and then you turn it on and they hope you will.
Now, Amazon's two new Echo Show smart displays, right? They introduced even privacy shutters on their cameras. You know, that thing that you can buy for 50p?
So let me show you the new Amazon gizmos and services that are on offer. So number one, an Alexa-enabled eyewear called Echo Frames.
Now these glasses pair with your Android phone and can read out notification, make calls, play audio.
Do you feel like we've been here before with some other, you know, big tech giant?
And you can play music and podcasts and you can ask Alexa for rundowns of your calendar, blah, blah, blah.
Okay, you can always obviously do some shopping, right, because that's always there.
And I'm wondering if all of these Amazon devices with all these daft speakers involved, they're just to identify the people who are utterly useless in society and aren't required actually, because they're arsing around with this kind of technology.
And it's like, oh, you're wearing one of those, are you? Thank you very much. Take the door on the left. I just, why, who, what?
I mean, how did we live? How did we live?
I bet most of us, if we left the house for 2 minutes without the phone, they might go, "Forgot my phone, even though I'm just going to the shops, I better run home and grab it." I still wipe my own ass, but I wonder in 20 years' time—
We've seen that all in the press over the last few months. How does this square with so-called personal privacy?
So it's a Wi-Fi router or router.
And the idea is that all the devices will work together to transmit data across the network, spanning large, broad geographical areas.
So for example, according to Amazon's own announcement, the company found that placing 700 devices across LA was enough to cover the entire metropolitan area of the city.
So even if you do not use Amazon wireless networks in your own home or join any of the Wi-Fi networks when you go out, the mesh network could enable Amazon to get data about the location of your devices.
According to Business Insider— and tell me, guys, because you guys are geekier than me in this area— owners of Wi-Fi networks track what devices are nearby, and even if those devices don't sign onto the network, just a smartphone can, it can detect nearby networks without signing on.
So if you've used that device to download an Amazon app or log into your Amazon account, the company could pair that MAC address with your user profile.
It helps build user profiles and it helps targeted advertisements. Right. And that's a seriously growing business for them.
I'm just trying to imagine explaining this to the general public and explaining how to opt out of something like this, if that's even possible, because I'm wrapping my mind around— I don't want that for myself.
I imagine opting out of that's going to be a pain in the ass, but how do I explain this to my mom?
So lots of people's home routers are available as a sort of mesh network.
So they sort of boast that, oh, we have 5 million hotspots up and down the UK because it's residential Wi-Fi, which you can log into. Effectively.
I've just done a search on their online map, and there are 211 BT Wi-Fi hotspots near me. I mean, within a walk of 3 minutes.
So the idea here is even if you're not connected to it, they can actually see you walk by because your phone's going, oh, there's a Wi-Fi hotspot.
So anyway, all this to say that I cannot tell you how thrilled to the gills I am about Amazon's privacy announcements. And what did the head of software development say again?
Privacy is absolutely foundational to everything we do in and around Alexa. And to your exact words, I think I'll wager to call that a big fat stinking bullshit.
Single sign-on is designed to connect employees to high-priority apps, all without needing the user to log in at every single hurdle.
Now, by combining these two services, our friends at LastPass may have just revolutionized security at the enterprise level. Learn more at lastpass.com/smashing.
How can you best provide each employee with the opportunity to upskill themselves?
Immersive Labs provides a cloud-based system, meaning it's available 24 hours a day, whenever is convenient for them to learn.
It provides hands-on experience with tools, technology, and even sandboxed malware. The platform provides story-based threat simulations.
It lets teams enhance their skills while stopping an online banking breach or the hack of industrial control systems. Lots of fun to be had there.
Check out Immersive Labs' skills development platform to drive down your organization's cyber risk while reducing training costs. Check them out at immersive-labs.com/lite.
Welcome back and you join us on our favorite part of the show, the part of the show that we like to call Pick of the Week.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish. Doesn't have to be security related necessarily.
And I was curious. I thought, I don't use Google as a search engine. I thought, I wonder what they've been capturing about me.
And I've chucked in a couple of screenshots here of what I saw for on my particular account.
And what I found was that from about a year ago, there were a number of search requests made, not using the traditional Google search engine, but using the voice-activated one.
So I think what was happening here was that maybe I was driving or traveling or something like that, and I might have gone into, maybe on my mobile phone, I might have accessed the app or something, or the site, and rather than type anything, I've actually said, "Who is the greatest chess player of all time?" Or, "Is Donald Trump the worst president in American history?" And other questions like this.
And it's not only recorded those requests, which I see at google.com/history, but it's also recorded my actual voice saying them.
And she'd ask questions like, when was Rubik's Cube invented? What's the difference between red lights and blue lights on an ambulance?
Anyway, I was a bit surprised by this because I thought I'd mostly been living a Google-free life, and somehow these have been recorded from over 18 months ago.
Now obviously I can zap them so I think I did this recently.
But it's on— it's also available for Steam on the PC and Mac, so you don't have to be a Switch player. So basically it's super fun. It's very easy.
Very young children can play it, and you can honk and steal things. Yeah, you basically can just go around honking at people, which is just super fun.
But you can go around and steal things and, you know, just wreak asshole goose havoc everywhere, and it's just— it's super funny.
That would be my— that would be my recommend— listen!
It started up, and they think around 1840, and it's a kind of humorous slang that was used by Cockneys who live in East End of London.
And it was probably first used as a kind of language to disguise what was being said so that passersby wouldn't know.
So, for example, if you didn't want your customers to know that you were going to lower your prices in 10 minutes, you could say it in Cockney rhyming slang.
So the second word— there's always normally two words involved— and the second word rhymes with the word you want to use.
And I'm also on infosec.exchange if you are a Mastodon user. And my handle is simply @maria. So I'm squatting on that one.
We're at smashingsecurity.com/reddit, or just search on Reddit for Smashing Security and you'll find us.
And thank you to all the people that listen to us and view us or support us on Patreon. We love you. Everything you do is magic.
And of course, check us out on smashingsecurity.com for past episodes, sponsorship details, and info on how to get in touch with us.
Although lists like this can be amusing, we shouldn’t ignore that there’s a serious side to this.
Hacked electronic billboards and road signs can be a huge distraction for motorists, and it’s easy to imagine how an accident could occur which might result in a driver or pedestrian being injured… or worse.
I’m sure most of these roadside defacements are being done with mischief in mind, exploiting default passwords, a lack of multi-factor authentication, poorly-maintained systems, and sloppy security (sometimes it’s poor computer security, sometimes physical, not uncommonly it’s both).
In short, if you hack a road sign or electronic billboard you might gain the attention of the media but you’re not proving that you have done anything “clever” or “novel”. There are rarely leet hacking skills on show in such attacks, and no-one who knows anything about security is going to be remotely impressed.
Nonetheless, because you may be putting public safety at risk, don’t be surprised if law enforcement officers fail to see the funny side of your roadside prank.