
Uh-oh. This is pretty worrying.
According to a Wired report, sensitive details about the New York Stock Exchange’s network was left unprotected on a public server visible for anyone in the world to view.
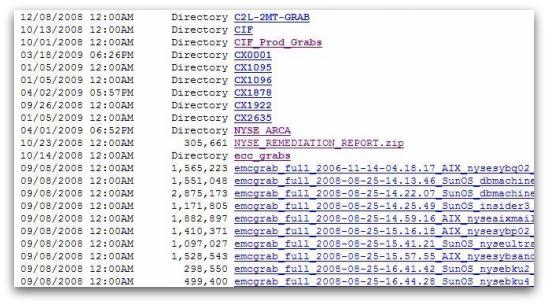
Information, including the names of servers, IP addresses, log histories, hardware and software details, and configuration information was all found on a public FTP server maintained by EMC. The data even included details of which patches had not yet been installed on the NYSE network.
The worry is that a hacker could use the sensitive information to piece together details of the stock exchange’s network architecture, and use it to pinpoint where vulnerabilities might lie.
For their part, EMC has been keen to debunk the security problem. Wired quotes a spokesman as saying that they have discussed the situation with the NYSE, adding “We’re confident that the information exchanged on our FTP site is not sensitive and will have no impact on NYSE Euronext systems or its customers.”
Let’s hope that no harm has come from this, and that hackers were not able to use the information to their advantage. Since Wired blew the whistle on this security slip-up, EMC has moved the data to a more secure location. Fortunately there is no suggestion that any of the information would have allowed hackers to get unauthorised access to the NYSE’s trading network.
But this incident does underline an all-too-common problem – human error meaning that potentially sensitive information about a client was not being properly secured behind even the simplest defences such as a password.
Of course, EMC should be no stranger to the importance of computer security. In 2006 the company purchased well-known computer security firm RSA Security.


