
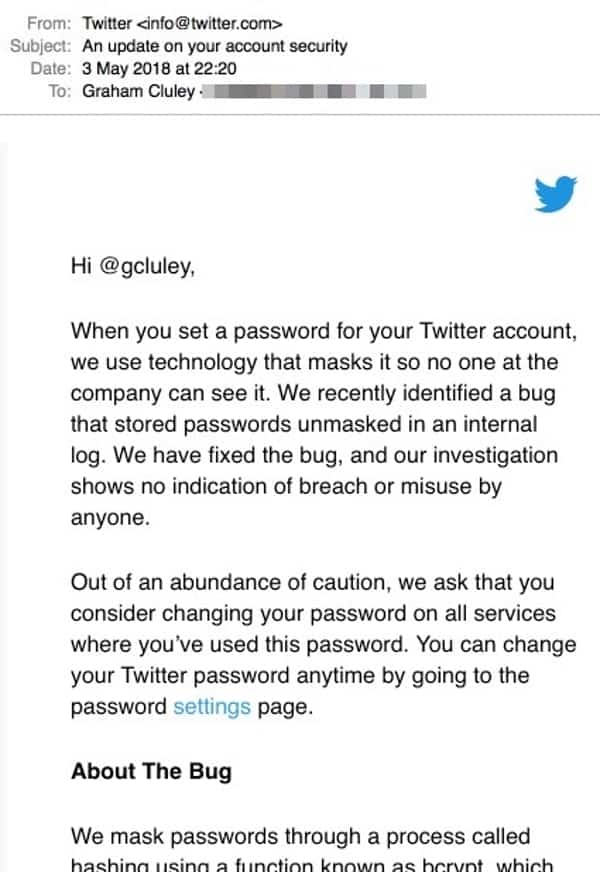
Twitter users should have received the following notification from the site by now:
When you set a password for your Twitter account, we use technology that masks it so no one at the company can see it. We recently identified a bug that stored passwords unmasked in an internal log. We have fixed the bug, and our investigation shows no indication of breach or misuse by anyone.
Out of an abundance of caution, we ask that you consider changing your password on all services where you’ve used this password. You can change your Twitter password anytime by going to the password settings page.
About The Bug
We mask passwords through a process called hashing using a function known as bcrypt, which replaces the actual password with a random set of numbers and letters that are stored in Twitter’s system. This allows our systems to validate your account credentials without revealing your password. This is an industry standard.
Due to a bug, passwords were written to an internal log before completing the hashing process. We found this error ourselves, removed the passwords, and are implementing plans to prevent this bug from happening again.
Some important things to note:
1. The sky is not falling. There is no indication that anyone managed to access or misuse the file containing plaintext passwords of Twitter users. In the big friendly words of Douglas Adams, “Don’t panic!”
2. Furthermore, even if someone had managed to access the passwords, your account would still have been protected if you had Twitter’s additional layer of two-step verification (known as Login Verification on Twitter) enabled. Here is our guide on how to enable Twitter Login Verification.
3. When I heard about this issue late last night, I didn’t let it ruin my sleep. I waited until I got up this morning and then changed my password. I already had Login Verification enabled because, well… I’m sensible.
4. If you were using your Twitter password elsewhere on the web, you should give each of those other online accounts new passwords too. This isn’t because there’s a high risk that the Twitter passwords have been exposed to bad guys, but simply because what you are doing is unsafe.
Reusing passwords is a really bad idea, and just makes life easy for online criminals.
5.Yesterday was World Password Day. I actually believe every day should be World Password Day, but I find it warming that it was the same day that Twitter told its users to sort out their passwords.
If you want to be serious about password security, you should get yourself a decent password manager. And if you want to learn more about the benefits of password mangers, and password-related security issues, be sure to listen to our “Smashing Security” podcast on the topic.
6. Twitter has been very open and public about something which, frankly, probably isn’t a huge concern. They could have just fixed the problem and swept it under the carpet, and avoided any potential embarrassment. But they did the responsible thing instead.
My hope is that with GDPR around the corner, we will see more tech companies adopt this approach and do what’s in the best interests of their users’ privacy rather than their brand.
Ultimately, websites will enhance their reputation by being upfront and honest when something goes wrong, rather than hiding it.




It is laudable that while Facebook and Uber Technologies are facing serious charges of Data security, Twitter came to the forefront and urged its 330 Million users to change their password. Twitter’s response was very professional as theoretically they could have just hidden the incident but rather they confessed that due to a glitch, user’s password was stored in a readable text to its internal computer system instead of disguising it by the process called hashing.
I agree with you that Twitter is highly professional in being transparent to its users. However, I do not understand how a Twitter internal vulnerability can be compared to data security (maybe data sharing) at different or similar companies. It is one thing to keep your user credentials safe and another what a company does with its user's data; no?