Cross-site scripting (XSS) flaws are amongst the most commonly encountered security flaws found on websites, opening up opportunities for malicious hackers to hijack customer accounts, change users’ settings and phish login credentials.
Unfortunately, it only requires a single web developer to make a mistake to open up opportunities which online criminals can exploit to launch potentially dangerous attacks.
And, although you would like to think that some of the world’s busiest websites would have trained their staff to avoid making the code blunders which can lead to an XSS attack, time and time again we hear of high profile vulnerabilities being found in familiar places.
For instance, in the last week or so a white hat hacker called Brute Logic has uncovered a serious XSS vulnerability on Amazon.com.
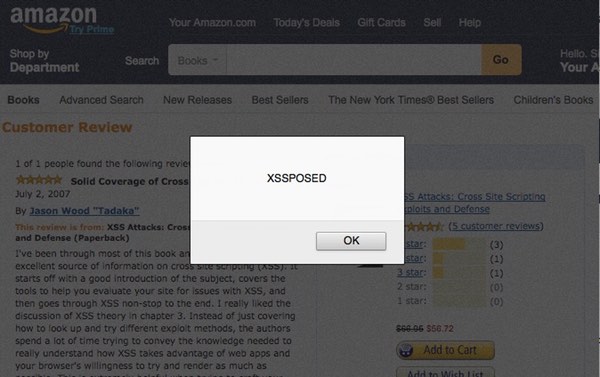
Fortunately, Brute Logic chose to do nothing more with the flaw than show how he could display the word “XSSPOSED” in a dialog box by giving an innocent party a carefully-crafted Amazon.com URL.
However, the same flaw could easily have been abused to redirect web browsers to a phishing page, compromise Amazon accounts, or to serve up content designed to infect visiting computers with a drive-by malware attack.
Perhaps worryingly, Brute Logic says that he did not inform Amazon of the serious security flaw. His reason? Amazon doesn’t pay a bug bounty and vulnerability researchers don’t believe they should be doing the work of Amazon’s security team for nothing.
As the researcher told Beta News, he doesn’t feel he has a responsibility to inform a website before sharing information to the rest of the world:
“I think this is a site/service problem. We are forcing the websites to be secure and their owners to stay tuned to what is happening in our hacking community. It is their fault to not take security seriously. We do.”
Personally, it’s a point of view I’m not comfortable with. I believe that we all have a responsibility as internet citizens to work together to plug holes and not expose innocent users to risk, and I would much prefer if vulnerability researchers worked with software vendors and website owners to get problems fixed promptly and safely.
However, at the same time, I can understand Brute Logic’s frustration considering that Amazon doesn’t appear to offer any kind of reward for those researchers who put hours of effort into finding flaws that the company’s own security team should have uncovered.
Maybe after this incident Amazon would be wise to introduce a reward program, as so many other companies are doing.
Meanwhile, Brute Logic hasn’t been resting on his laurels.
As IT Pro Portal reports, the researcher has since found a serious XSS flaw on scores of British newspaper websites, run by the Johnston Press media group and visited by millions of users every month.
BruteLogic found that sites including the Worthing Herald were at risk from the XSS flaw, which could redirect visiting computers to malicious websites or attempt to phish their login details.
The bug hunter explained the seriousness of the problem to IT Pro Portal:
“The vulnerability is still unpatched putting worthingherald.co.uk users, visitors and administrators at risk of being compromised by malicious hackers. Theft of cookies, personal data, authentication credentials and browser history are probably the less dangerous consequences of XSS attacks.”
“XSS attacks are becoming more and more sophisticated these days and are being used in pair with spear phishing, social engineering and drive-by attacks.”
If you work as a web developer, make sure that you are clued-up about XSS vulnerabilities and how to mitigate against them. Otherwise it could be your company next which is making the headlines for all the wrong reasons, and putting your users at risk.


