
Cross-site scripting (XSS) vulnerabilities are almost certainly the most prevalent security bugs found on websites today, and can be exploited by malicious hackers to hijack accounts, steal cookies, change users settings and conduct phishing attacks.
So, you would like to think that experienced web developers working on some of the world’s biggest websites would be aware of the threat, and build their code securely to prevent attackers launching a potentially dangerous attack. You would like to think that, wouldn’t you?
Unfortunately, it just takes one programmer to drop the ball, and not properly sanitize web input, to allow an XSS attack to flourish on your website.
This week, bug hunters claim to have found an XSS flaw in the popular travel website TripAdvisor, for instance, potentially allowing page content to be modified and opening opportunities for attackers to steal user credentials and post false reviews.

According to the report, a form used by TripAdvisor users to set up an “Air Watch” alert to be informed when flight prices drop can be subverted by entering carefully-crafted executable script, instead of the names of airports.
Meanwhile, controversial taxi-hire app Uber could find itself the subject of more damaging headlines after it was discovered that visitors to its website might be at risk of having their cookies, personal information, authentication credentials and browser history stolen courtesy of an XSS vulnerability.
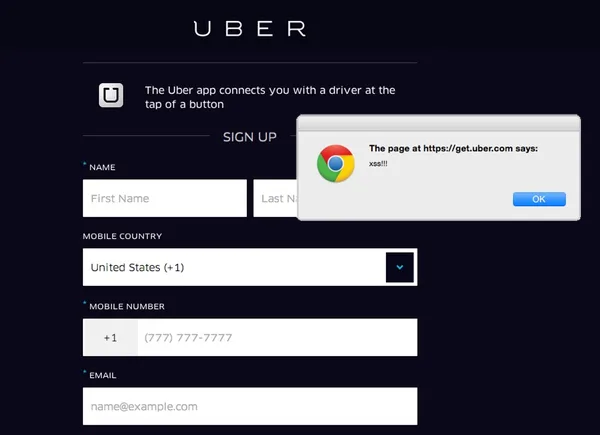
In both cases, forms on the websites have failed to sufficiently sanitize, or filter out, input. And this opens opportunities for mischief-makers and criminals to strike.
If big names like Uber and TripAdvisor can suffer from XSS vulnerabilities on their sites, it’s no wonder that such problems are also so commonly found on the websites of less well known companies too.
And one thing is clear—as consumers, we can’t put much faith in the “security seals” that many offer in the hope that it reassures us that their websites are safe and secure.
Earlier this month, researchers showed that users would be unwise to put too much trust in the security seals shown by many websites, as the automated scanners behind such certifications often do a bad job of uncovering vulnerabilities that a determined hacker would discover in a short time: SQL injection vulnerabilities, XSS flaws and cross-site request forgery (CSRF).
Is it any wonder then that more and more organizations are waking up to the fact that it may not just be advantageous to teach their developers about secure coding practices, but also to call in penetration testers to put a service through its paces before it suffers a breach.
After all, isn’t it better for you to find the XSS vulnerability on your website than a stranger with perhaps malicious intent?


